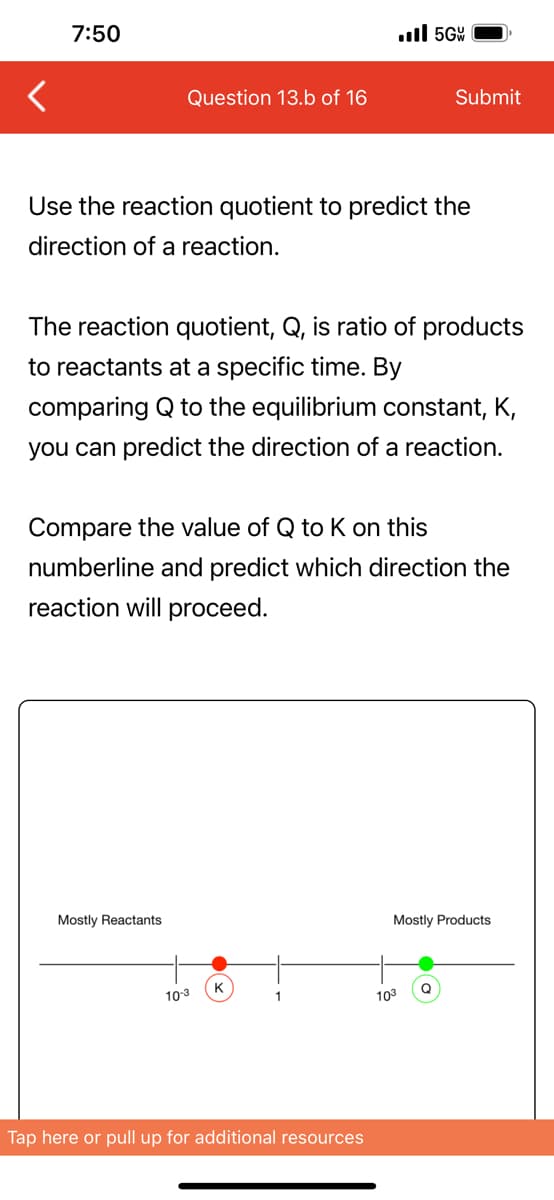
Use the reaction quotient to predict the direction of a reaction. The reaction quotient, Q, is ratio of products to reactants at a specific time. By comparing Q to the equilibrium constant, K, you can predict the direction of a reaction. Compare the value of Q to K on this numberline and predict which direction the reaction will proceed. Mostly Reactants 10-3 Mostly Products 103
Use the reaction quotient to predict the direction of a reaction. The reaction quotient, Q, is ratio of products to reactants at a specific time. By comparing Q to the equilibrium constant, K, you can predict the direction of a reaction. Compare the value of Q to K on this numberline and predict which direction the reaction will proceed. Mostly Reactants 10-3 Mostly Products 103
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter17: Markov Chains
Section17.7: Work-force Planning Models
Problem 4P
Related questions
Question
This is all the information given for this question
Transcribed Image Text:7:50
Question 13.b of 16
Use the reaction quotient to predict the
direction of a reaction.
Mostly Reactants
The reaction quotient, Q, is ratio of products
to reactants at a specific time. By
comparing Q to the equilibrium constant, K,
you can predict the direction of a reaction.
Compare the value of Q to K on this
numberline and predict which direction the
reaction will proceed.
10-3
K
.5G
1
Tap here or pull up for additional resources
Submit
103
Mostly Products
Q
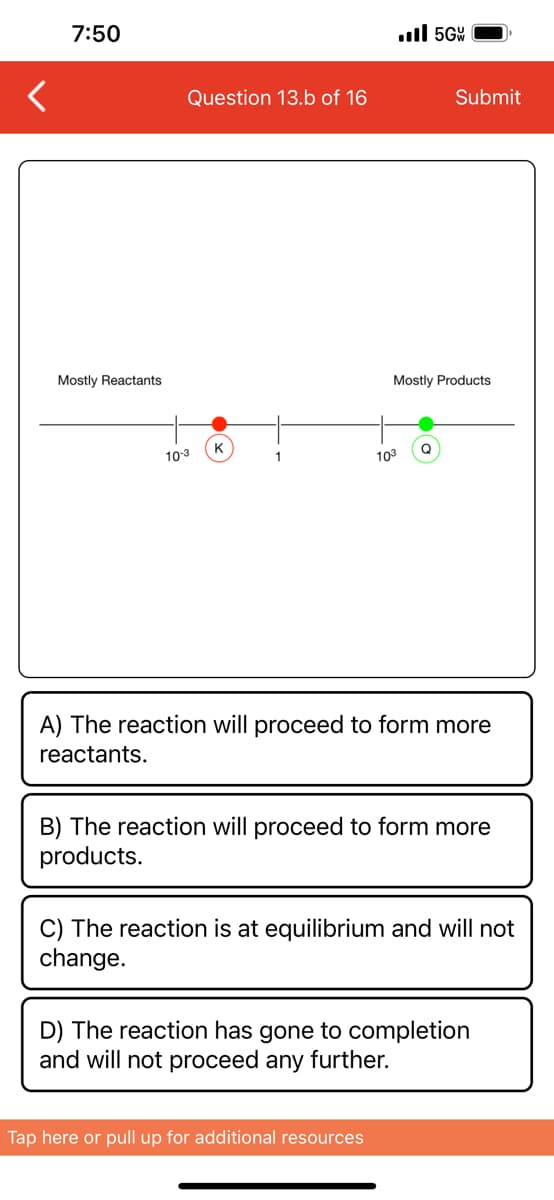
Transcribed Image Text:<
7:50
Mostly Reactants
Question 13.b of 16
10-3
K
1
.5GW
103
Mostly Products
Submit
Q
Tap here or pull up for additional resources
A) The reaction will proceed to form more
reactants.
B) The reaction will proceed to form more
products.
C) The reaction is at equilibrium and will not
change.
D) The reaction has gone to completion
and will not proceed any further.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr