Q: Why is the middle portion of 3DES a decryption rather than an encryption? What are the roles of…
A: The middle portion of 3DES, also known as Triple Data Encryption Algorithm, uses a decryption…
Q: How does MVC structure web apps? MVC offers what benefits?
A: Required: How does MVC help with web application organisation? What benefits come with using an MVC…
Q: What three characteristics are necessary for a network to serve its purpose effectively and…
A: Introduction: During this stage, production planners determine how and where items will be…
Q: Why is remote control or mission planning software the most effective way to operate a drone?
A: remote control software is a most effective way to operate a drone
Q: Register and RAM are memory types.
A: Solution to the given question, Introduction: Memory is a place where the data is stored. It…
Q: the National Commerce Bank has hired you to create web application that verifies a customer personal…
A: Introduction Validation From (HTML): A validation form in HTML is a mechanism that checks whether…
Q: This is my Test cases: "hi.txt" but the most frequent word I got is "is" instead of "Lawrence". plz…
A: Solution: The issue is that the implementation of getMostFrequentWord() method is not considering…
Q: 9 is even 7 is not odd or 9 is not even :: if 7 is odd then 9 is even b. if 7 is odd or 11 is odd…
A: Introduction: The truth table is an important tool in propositional logic because it enables us to…
Q: What do the processor unit and programme counter do in the von Neumann paradigm?
A: Introduction The processor unit and programme counter are vital components of the von Neumann…
Q: So, why database security? At least two methods to safeguard a database, right?
A: A set of practices for defending database management systems from malicious cyberattacks and…
Q: Why define separate data types for undirected graphs, directed graphs, edge-weighted undirected…
A: Data types: Data types define the type of data that can be stored and manipulated within a computer…
Q: DESTINATION San Francisco New Orleans Atlanta REG. PRICE 550.00 330.00 295.00 REDUCED SALE PRICE…
A: Code: print("DESTINATION"+" "+"REG.PRICE"+" "+"REDUCED"+" "+"SALE PRICE")l=["San…
Q: Given our 5-stage pipeline with the hardware support for forwarding and stall to deal with data…
A: (1) Data dependencies: "on $2 from Add to Lw" "on $1 from Add to And" "on $3 from Lw to And" "on $7…
Q: Create a program which will plot the “uneclipsed” area of the star as a function of time - just like…
A: Here's an example Python program that plots the "uneclipsed" area of a square planet passing in…
Q: Explain two Von Neumann-free parallel processing methods.
A: Introduction: The Von Neumann architecture has been the foundation of computer processing since the…
Q: How many 9-bits strings are possible which start from 111 or end with 11 or both.
A: Introduction String: A string is a collection of words that can comprise letters, numbers, symbols,…
Q: The functions do not return what they should
A: (define (collect-prop-variables prop) (cond ((null? prop) '()) ((not (pair? prop)) (if (eq?…
Q: What distinguishes network and application architecture?
A: The above question that is what distinguishes network and application architecture is answered below…
Q: What is an ordinary Web application?
A: An ordinary web application is a software application that is accessed through a web browser or…
Q: Explain why conventional (informal) software development methodologies will not work for medical and…
A: Introduction: Software development is the process of creating, designing, and testing software…
Q: Does a two-tier design have any significant drawbacks? How does a multi tier client-server solve…
A: Intro Client-server architecture with two levels: The Client-Server model serves as the foundation…
Q: The issue is crucial for those who create software. Moreover, what suggestions do you have for…
A: Software development: Software development is the process of creating, designing, developing, and…
Q: Just what makes UBUNTU, Kali, and Fedora Linux different from one another?
A: Introduction: An operating system (OS) is a collection of software that maintains computer hardware…
Q: Why does a foreign key protect the database? Why is this important?
A: Introduction A database constraint known as a foreign key ensures that the values stored in a column…
Q: Write a ASQ statement to return to see all of the first names in the People table. SELECT first name…
A: We need to find the correct query for getting first names in the People table. *As the table is not…
Q: Commands for the following but only as an unprivileged user - Create a new directory in /tmp/…
A: Assuming the unprivileged user has write access to /tmp/ directory, here are the commands: Create a…
Q: Your host in this example has IP address 172.16.1.1. Someone tries to send e-mail from a remote host…
A: Refer below the answer for your above asked question:
Q: The candidates will design in any core content area with the focus of the use of reading, writing,…
A: ELLs Students who struggle to learn or communicate effectively in English are known as…
Q: Why deploy and configure servers automatically? Does automation have drawbacks?
A: Reasons for using automation and it's disadvantages are given below.
Q: What would happen if the programmer replaced the displayBalance command with sac.balance instead of…
A: Class private access specifier is used to conceal data. Data from outside the class is hidden by it.…
Q: Culd you please epxlin how did you calculated this subnets? and could you please provide some source…
A: Solution: Given,
Q: Information is present in the screenshot and below. Based on that need help in solving the code for…
A: Coded using Python 3.
Q: Web design involves many distinct stages. Each step should have a detailed description of its…
A: Yes, web design typically involves several distinct stages, and it's important to have a clear…
Q: Please name and describe any eight different types of Internet of Things sensors (with a picture).
A: INTRODUCTION: The Internet is a global network that links billions of computers worldwide to one…
Q: Please give me the proper answer with step by step solution Qns:Java question Implement a method…
A: Your Java Program is given below as you required with output.
Q: How does MVC structure web apps? What are MVC framework benefits?
A: What is MVC ? --> MVC stands for the three words Model - View - Controller . Each of this word…
Q: the question does not involve 27/46. we have to solve as if we don't know that answer yet.
A: In this question we will solve the given equation to find out the value of w? Given equation is:…
Q: Dynamic Programming Backward Recursion Approach
A: Dynamic Programming: Dynamic programming is a technique used to solve complex optimization problems…
Q: Computer networking skills? explain computer network types
A: Introduction: In today's digital age, computer networking is an essential skill for many…
Q: Architecture benefits? Let's compare a project without and with architecture. Will it affect the…
A: Introduction Architecture: In software engineering, architecture refers to the fundamental structure…
Q: What's a pattern in architecture? Compare these three architectures.
A: Introduction In this question we are asked about the pattern in architecture and Compare three…
Q: What does the phrase "data leaking" really mean?
A: Data leakage: Data leakage is simply the unlawful transfer of data-related information outside of a…
Q: Matrices provide a convenient mechanism to manage large amounts of data. Ordinary matrix…
A: Algorithm: Initialize a new matrix C with dimensions rows(A) x cols(B) to store the result of the…
Q: As the administrator, StormWind Studios is under your direction and supervision. IPAM is now going…
A: IPAM DNS and DHCP, which provide services to assign and resolve IP addresses of machines in a…
Q: How does auto-provisioning and configuration help servers? Automated systems' drawbacks?
A: Auto-provisioning and configuration can help servers in several ways: Efficiency:…
Q: The Issue: You're writing a graphics filter that runs each image through a filter. Each pixel is…
A: Arithmetic with fixed points.Fixed point arithmetic allows you to perform computations with real…
Q: What is your opinion of DMP, and will these devices assist or hinder mobile device investigations?…
A: A DMP (Data Management Platform) is a technology platform that collects and manages large amounts of…
Q: A. In one of his cases, Sherlock Holmes was confronted with the following message: Cz sio wuh vlyue…
A: A. The message appears to be encrypted using a simple substitution cipher, where each letter in the…
Q: Suppose the computer has finished all the steps needed to make a software ready to run. Describe in…
A: A program is run by the CPU using an execute cycle. It retrieves each instruction one at a time.…
Q: Provide the instruction type, assembly language instruction, and hexadecimal representation of the…
A: Refer below the answer for your above asked question:
Translate to respective boolean expressions and create its overall truth table.
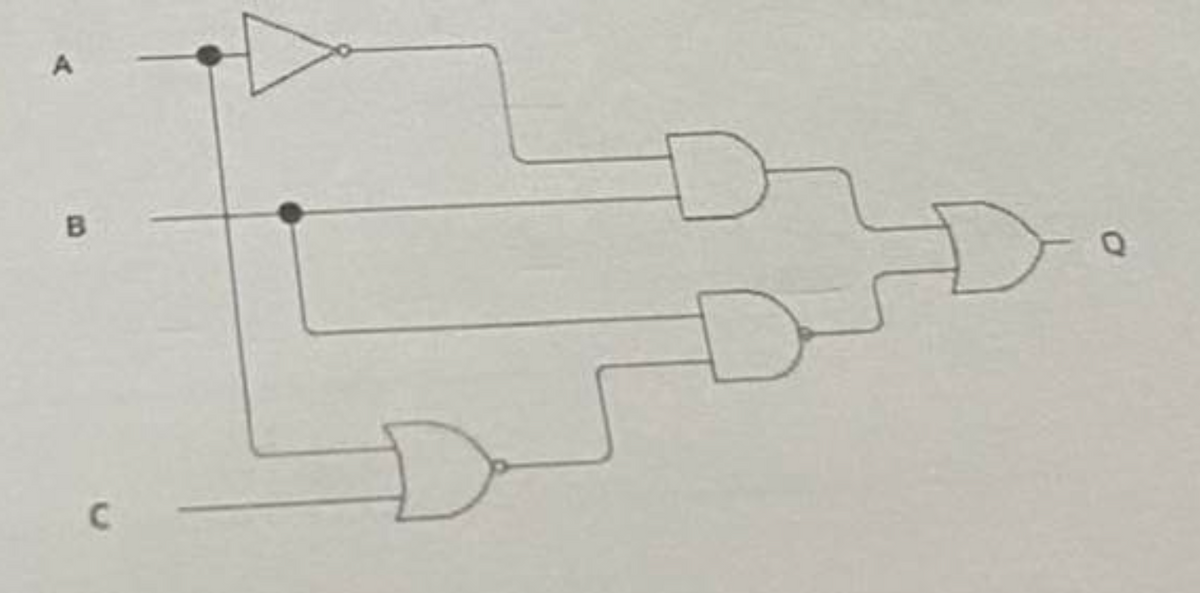
Step by step
Solved in 2 steps


