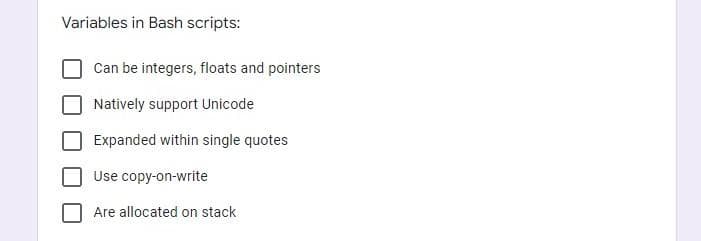
Variables in Bash scripts: Can be integers, floats and pointers Natively support Unicode Expanded within single quotes Use copy-on-write Are allocated on stack
Q: What was the "Analytical Engine" and how did it work?
A: Analytical Engine: According to popular belief, the analytical engine is a machine that was…
Q: 2. Create a program that will compute for your grade. Use LBYEC2A Grading system. Lab Activities:…
A: If else statements need to be used to print grades and total grade has to be calculated using given…
Q: What is meant by online analytical processing is the processing of data in real time?
A: INTRODUCTION: Here we need to define online analytical processing is the processing of data in…
Q: When you say "IOP," what exactly do you mean? Make use of a flow graphic to explain the idea of…
A: An input-output processor (IOP) is a processor with direct memory access capability. In this, the…
Q: What exactly is the difference between system and user space?
A: System space: User space is a Linux concept that provides a block or set of virtual addresses to…
Q: How is software versioned? Explain the versioning information and protocols utilized in an online…
A: In fact, the information provided is versioned software systems. The following has been provided:…
Q: Does "define system model" really mean "define the model of the system"? Considerations for…
A: Model of the System: The phrase system model is used in a wide range of disciplines, applications,…
Q: In this lesson, we'll talk about an application life cycle management environment and give two…
A: Given: The programmers use the design specifications (programming requirements) to code, test,…
Q: at are two reasons why layered protocols are used? Give
A: Justification for the Use of Layered Protocols Layered protocols are primarily utilised in…
Q: You provide a significant explanation to support your solution to the question, "What is the…
A: Start: A distributed transaction is a sequence of data activities that spans two or more data…
Q: Given the code segment below, what is the value that is passed to func() given the function call?…
A: aData+2 is passed as parameter and the requirement is to find out the value that is passed to the…
Q: In terms of email, what can be done to improve the process? Give clear instances of what you mean.
A: The technique helped in email communication: Email communication is a fundamental instrument for…
Q: Provide a brief description of 4GLs.
A: Answer
Q: When compared to other sorts of models, what exactly is a system model? While developing fundamental…
A: The Answer is in given below steps
Q: What are the risks and ramifications of working with a disjointed data system?
A: Introduction: Here we are required to explain what are the risk and ramifications of working with a…
Q: Give examples of two different types of application lifecycle management environments (ALMs).
A: The answer for the given question is as follows.
Q: What precisely is a system model? What factors should be considered while developing the first…
A: Given: The problem is that people don't grasp system modelling and the aspects that should be…
Q: All are examples of data bound controls EXCEPT Select one: O a. list boxes b. picture boxes c.…
A: Let's see the solution in the next steps
Q: Explain the special purpose and general purpose register of 8051 microcontroller in detail. Analyze…
A: General Purpose Register of 8051 Microcontroller General purpose registers are the registers which…
Q: Because of the fast advancement of technology, the nature of cyberspace contact is changing swiftly.…
A: Definition: The term "cyberspace" refers to a global network that links millions of digital devices.…
Q: Decode the number using the given private key. Decode the number M = 15 using the private key d = 53…
A: Given: Private key = 53 n = 77 Message M = 15 Let the decode number be x To decode this using the…
Q: What causes it to be difficult to detect passive assaults while being much more difficult to resist…
A: Introduction: Aggression in children is influenced by instinct, hormone imbalance, genetics,…
Q: Are you aware that there are two alternative methods for terminating processes and breaking…
A: A process could be terminated if it tries to use a resource that it is not allowed to. For example -…
Q: We receive automated updates of software over the Internet. How important is it to keep up with the…
A: Software Update: A software update (also known as a software patch) is a short piece of program code…
Q: Discuss the various design strategies employed in the creation of various operating systems.
A: A primer on OS design approaches The design process entails establishing a conceptual view of the…
Q: a. How many subnets are there in this network? b. What are the first valid host and last valid host…
A: The answer is
Q: 1. What is the possible output if this recursive function run if x is 5 and y is 2. static int…
A: We need to find the output when fun1 is called with x=5, y=2. ***As per the guidelines, only 1st…
Q: Is there a particular ETL tool that you prefer above the rest?
A: ETL-Extract, Transform, and Load to database man ETL becomes a multi-purpose programming technique…
Q: Is there a significant difference between asynchronous, synchronous, and isochronous connections,…
A: Explanation: Asynchronous Connection:-\sData is exchanged from one end to the other in…
Q: Write a sentinel loop in java that read numbers from the console until the user typed -1 and then…
A:
Q: Public key cryptography is an example of an asymmetric encryption method with numerous benefits over…
A: Asymmetric cryptography, often known as public key cryptography, is a method of encrypting and…
Q: 7)There are many situations in logic design in which simplification of logic expression is possible…
A: The NOR gate is a digital logic gate that implements logical NOR - it behaves according to the truth…
Q: What is a cryptographic hash function (CFH), and how does it work??
A: Cryptographic hash function: It's a mathematical function that turns a message's arbitrary length…
Q: Write PHP script to display the square and cubes of 1 to 10 numbers
A: Intro PHP script to display the squares and cubes of the numbers 1 to 10. PHP script is starts from…
Q: The Goal Seek function in Microsoft Excel may be shown by creating a spreadsheet.
A: Seek a goal: When only the source knows the correct input value, goal searching is the way of…
Q: Give an explanation of the function a repository plays in the creation of systems.
A: REPOSITORY: A repository is a centralized area where all of the data and information is kept safe…
Q: In a three level memory hierarchy, the access time of cache, main and virtual memory is 5…
A: We are going to find out average access time of memory when hierarchical access memory organization…
Q: 10)The Memory Data Register (MDR) is designed such that it _. a. is logically connected to all…
A: To find the Memory Data Register (MDR) is designed such that it ____________.
Q: How are deep learning methods used to Arduino? How might this approach be utilized to teach flight…
A: Deep Learning: Deep Learning is a more sophisticated machine learning technique that is modelled…
Q: What are the types of testing techniques predominantly used ? Select one: a. Partition based,…
A: To find what are the types of testing techniques predominantly used.
Q: The integration of three fundamental technologies provides system architectural security in the…
A: Active Metering: Active metering works by allowing designers to lock and remotely disable individual…
Q: In your own words, explain what you mean by the term "system model". In the process of constructing…
A: Introduction: Information flows between modules are represented as impacts or flows in the systems…
Q: List and briefly describe the steps that a computer or operating system will go through in the event…
A: TLB(Translation Lookaside Buffer ): A translation lookaside buffer (TLB) is memory cache that…
Q: 4. 780107 _8
A:
Q: Why use hyperlinks instead of keyboard shortcuts to browse around your presentation?
A: The hyperlink is described as a connection between two locations in a text document that is…
Q: It's important to know what what is meant by "system model." Considerations for constructing basic…
A: Introduction: The informal flow of information between modules is represented as influences or flows…
Q: Packages for Speech Recognition in Python are listed below.
A: According to the question the speech recognition is that machine of ability to listen the spoken…
Q: Create a function in Javascript that takes two numbers as arguments (num, length) and returns an…
A: JavaScript Code for above : // required function for abovefunction ReqdFunction(num, length) {…
Q: Which one of the following requirements is the MOST important for an access control system?…
A: Introduction: An access control system allows or restricts access to a building, a room or another…
Q: t reads the data of the dates and stock volumes into two separate lists. Output: The program must…
A: First, create the input file "data.txt" and then use the code below:
Step by step
Solved in 2 steps

- Language: Python Goal: implement decryption in the attached code block import argparse import os import time import sys import string # Handle command-line arguments parser = argparse.ArgumentParser() parser.add_argument("-d", "--decrypt", help='Decrypt a file', required=False) parser.add_argument("-e", "--encrypt", help='Encrypt a file', required=False) parser.add_argument("-o", "--outfile", help='Output file', required=False) args = parser.parse_args() encrypting = True try: ciphertext = open(args.decrypt, "rb").read() try: plaintext = open(args.encrypt, "rb").read() print("You can't specify both -e and -d") exit(1) except Exception: encrypting = False except Exception: try: plaintext = open(args.encrypt, "rb").read() except Exception: print("Input file error (did you specify -e or -d?)") exit(1) def lrot(n, d): return ((n << d) & 0xff) | (n >> (8 - d)) if encrypting: #…The questions should be solved using Linux Bash Scripting. In the file there should be solution code and one/two screenshot for running of program. Student id and names should be written inside the file. The assignment should be sent as PDF. Upload Link: https://forms.office.com/r/JfpSa2dDi8 Question 1. Read "n" and generate following pattern according to givennas below. Ex: for given value forn:4\[ \begin{array}{l} 1 \\ 23 \\ 456 \\ 78910 \end{array} \]Implement a password cracker using C++ Source code must be well documented (comments). You will be provided with an unsalted hashed password file that contains password hashes for different users. Also, you will be provided with a dictionary file(in clear text) containing the most common passwords. You should implement the offline dictionary attack by trying SHA1 and SHA2 algorithms. Also, your program should brute force all possible alphanumeric(only small cases) passwords from 1 to 4 characters using SHA1 and SHA2 algorithms against all hashed passwords left from the offline dictionary attack (if any).
- Make a new DevC++ project named “yourID_InitialsofYourName_P9_Q3”. Writeyour own two-dimensional array library which contains a function for eachoperation listed below. Your functions have to make use of pointers. In the file“main.c” under this project, test all functions.a. Enter the elements of an arrayb. Print the elements of an arrayc. Print the mth, nth element of an array (c programming with explanation/DONT USE Dynamic Memory Allocation )create a python program Problem StatementImplement all the functions of a dictionary (ADT) using hashing.Data: • Set of (key, value) pairs. Keys are mapped to values. Keys must be comparable. Keys must be unique.Standard Operations: • Insert(key, value) • Find(key), • Delete(key) This is the example output of the program. ====== CPE 204L Dictionary =====[1] : Insert Word[2] : Find Word[3] : Delete Word[4] : Exit============================Enter your choice : 1Enter word: prettyEnter meaning: beautifulPretty is successfully inserted into dictionary====== CPE 204L Dictionary =====[1] : Insert Word[2] : Find Word[3] : Delete Word[4] : Exit============================Enter your choice : 1Enter word: prettyEnter meaning: beautifulDuplicate Word! Pretty is not successfully inserted into dictionary.====== CPE 204L Dictionary =====[1] : Insert Word[2] : Find Word[3] : Delete Word[4] : Exit============================Enter your choice : 2Enter word: prettyWord is Present in…CS) Please write this code in the C language. Also, be clear you need only implement the sort algorithm and save the file with the name "srtheap.c". Please do not copy and paste from other similar questions.
- 92. In external hashing for files of disk, the pointers which contain record position and block address within the block are classified as a. position pointers b. address pointers c. block pointers d. record pointersplease code in pythonthe below code has alot of errors .. please make it error free import numpy as np import randomimport sys import osfrom datetime import datetimeimport string import subprocess from subprocess import callfrom subprocess import check_output if len(sys.argv) < 3: print('Usage: maintest.py Nm Ns R \n') exit() Ns = sys.argv[1] #sort size R = sys.argv[2] #number of repetitions w = open('BubbleSortResult.txt', 'w')#BubbleSort1: No Split Input = np.random.rand(Ns) Itmp = list (Input) def sort (numbers): sorted = False while not sorted: sorted = True for i in range (len (numbers)-1): if numbers [1] > numbers [i + 1]: sorted = False numbers [i + 1], numbers [i] = numbers[i], numbers [ i + 1]Te = datetime. now () for i in range (R): #Run R-time Itmp = list (Input) # Get fresh Input #print (Itmp) sort (Itmp) # This is in-place sort. Input will be altered. Te = datetime. now () - Te Totalus…23. Pointers are useful in a. Traversing a linked list b. Pointing mistakes in input data c. Locating a particular sector of a magnetic disk d. All of the above
- 2. For the code below, draw a picture of the program stack when the function partition() is called the 2nd time. # extracted from suquant's reply at # https://stackoverflow.com/questions/18262306/quicksort-with-python def partition(array, begin, end): pivot = begin for i in range(begin+1, end+1): if array[i] <= array[begin]: pivot += 1 array[i], array[pivot] = array[pivot], array[i] array[pivot], array[begin] = array[begin], array[pivot] return pivot def quicksort(array, begin, end): if begin >= end: return pivot = partition(array, begin, end) quicksort(array, begin, pivot-1) quicksort(array, pivot+1, end) # added calling code if __name__ == "__main__": mylist = [8, 2, 17, 4, 12] quicksort(mylist, 0, 4)Python, input file has the following structure (number, then animal each on a line): 4Cows5Camels1Peacock3Whales4Lions2Scorpions Two output files are required:first output_file: sort by (dictionary) key but those sharing the same key should be listed on the same line with a ";" separated 1: Peacock2: Scorpions3: Whales4: Cows; lions ------------------------------> separated by ';' because they share the same key 45: Camels second output_file:Only values are sorted as follows and written to file: CamelsCowsLions PeacockScorpionsWhales Thank youLinux general memory layout includes stack, heap, data, and code. stack memory relations stores local variables heap: dynamic memory for programmer to allocate data: stores global variables, separated into initialized and uninitialized code: stores the code being executed Use the following code to answer the questions that follow #include <stdio.h> #include <stdlib.h> int x; int main(int argc, char *argv[]) { int y=3 printf(": %p\n", main); int* z = malloc(100e6); printf("location of stack: %p\n", &y); return 0; } Where are the possible memory addresses of the above variables? Address Location x y main z *z

