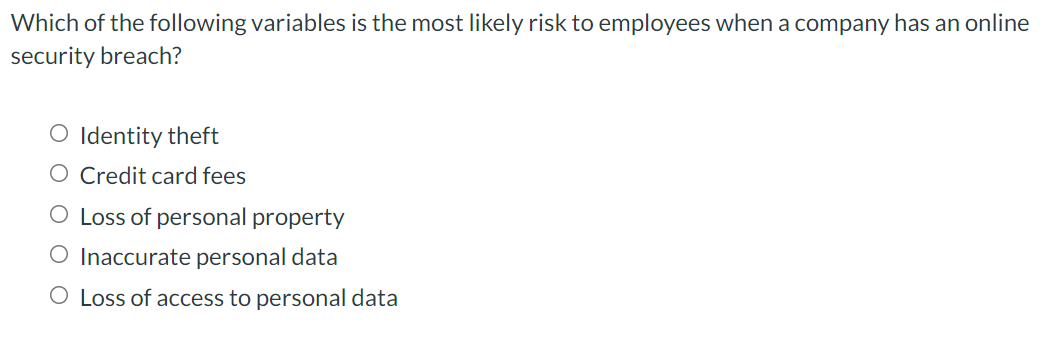
Vhich of the following variables is the most likely risk to employees when a company has an online ecurity breach? O Identity theft O Credit card fees O Loss of personal property O Inaccurate personal data O Loss of access to personal data
Q: endence (Pooled, S
A: Three forms of interdependence An organizational structure's level of connection and activity may be...
Q: Max 1A + 2B s.t. 1A S 4 1B S 3 2A + 2B = 10 A, B20 (a) Show the feasible region.
A:
Q: A student arrive in a photocopy service. There is only one photocopy operator, and the time required...
A:
Q: Woolworths is a member of the Better Cotton Initiative (BCI), a global enterprise which aims to crea...
A: Three type of buyer supplier relationship: Transactional: This type of relation exists when there a...
Q: cular iteration of the simplex method, if ther riable should be the leaving basic variable, i on mus...
A: linear programming and the simplex method
Q: 4. Determine a strategy for Wal-Mart to improve online sales. 5. Write a report to management that d...
A: A creating pattern for large numbers of these retail outlets is the way that the vast majority of th...
Q: Determine the critical path and project completion time.
A: A PERT diagram indicating the activity duration in three dimensional process which helps to calculat...
Q: Use the following information for questions 34 through 39. A $100 million portfolio consists of 35 m...
A: A Small Introduction about Management Management is the fulfillment of authoritative objectives in ...
Q: The following Level 0 MRP information is given for a personal computing system. Using a lead time o...
A: The net material requirement is the amount requiring genuine operations subsequent to allotting the ...
Q: The table below shows the demand for a particular brand of microwave oven in a department store. Mon...
A: Given-
Q: The NATO Company uses 150,000 gallons of hydrochloric acid per month. The cost of carrying the chemi...
A:
Q: Explain why satisficing exists and why someone would not require an optimal solution
A: Satisficing refers to a decision-making strategy where the main focus is on achieving satisfactory o...
Q: Define critical path.
A: Project management is the management in which different types of knowledge and skills are used to ma...
Q: This is a proposal used to explain where a business wants to go and how it expects to get there O Vi...
A: A business proposition is sent from a provider to a likely client to win a particular project. It is...
Q: Question: Describe the concept of “SUPPLY CHAIN MANAGEMENT PROCESS” With the help of Any Company Exa...
A: Production is the process of creating finished products using the raw materials and resources for fi...
Q: Apples are prepared in a process with two resources. The first resource has a capacity of 2.1 apples...
A: Process cycle time indicating the average time required to complete a unit of item. Here, we can ide...
Q: What is containerization and how does it relate to global trade?
A: The process of containerization has emerged as a major trend in the software development which acts ...
Q: The table below shows the violent crime rate in Canada between 1977 and 2004. a. Enter this data int...
A: Quadratic regression equation is of form ax2+bx+c where a should not be equal to zero.
Q: Yost-Perry Industries (YPI) manufactures a mix of affordable guitars (A, B, C) that are fabricated a...
A: Underway and project management, a bottleneck is an interaction in a chain of cycles, to such an ext...
Q: How do the international organizations such European Union, APEC, ASEAN, weigh the risks and benefit...
A: International organizations are described as institutions that consist of more than 3 members and gr...
Q: What do you think are the limitations of the flow process chart? Then suggests ways to answer these ...
A: Flowcharts have many limitations, that can be listed down as below:
Q: Problem #2- Brown Manufacturing-Modified, from textbook page #198 If the annual demand is reduced to...
A: Given:Annual demand = 8,000 unitsDaily demand=60 unitsProduction per day= 80 unitsOrdering cost=$120...
Q: Exercises - Management Accounting Concepts and Techniques for Decision Making 16. The Call Company h...
A:
Q: These constraints translate mathematically to X, 2 .2(x, + x2 + x3 + x4) x2 2 .1(x, + x2 + x3 + x4) ...
A:
Q: 1. Consider a walk time of 0.1 min, with loading and unloading time = 1.0 min and machine run time =...
A:
Q: Describe the primary methods for discharging a contract.
A: A contract is discharged by order of the court. In some cases, such as insolvency or the death of on...
Q: The National Company uses 150,000 gallons of hydrochloric acid per month. The cost of carrying the c...
A: Solution is as follows:
Q: Explain the relationship between priority versus capacity that must exist within the production plan...
A: Capacity can be understood as how much a firm can handle at a given point of time. It is quite sign...
Q: The table gives the total cost schedule for oil changes at the local Jiffy Lube. What is Jiffy Lu...
A: Given-
Q: what is the importance of human resource management in business operations?
A: Human resources management is a very important part of any organization. Without human resources man...
Q: What are the three types of models in operations management and the importance of them
A: To determine: The three types of models in operations management and the importance of them. Model: ...
Q: Explain the two common inventory estimation methods, mentioning key similarities and differences bet...
A: The main common inventory estimation methods are:- First-In, First-Out (FIFO) Last-In, First-Out (...
Q: With an overall cost of goods totaling $64,000 and sales of $181,000, what is the food cost percenta...
A: Food cost percentage is a proportionate measurement between total inventory cost and total sales. H...
Q: Two factor authentication (2FA) is when a website uses two different methods for people trying to ac...
A: Two-factor authentication often called two-factor verification or two-factor authentication 2FA is n...
Q: Red and White Pizza Pies, Inc. makes pizza pies in two (2) flavors, regular and white pizza. Each pi...
A:
Q: Managing a variety of personalities can be challenging for an employer who has a mix of Gen Y, Gen X...
A: Psychology at the workplace is very important as it helps the manager to take critical decisions at ...
Q: Bryan has been working for Habib Jewels for almost 12 years. He is well known for his skills in pre...
A: given, Bryan has been working for Habib Jewels for almost 12 years. He is well known for his skills...
Q: Consider the following actual and forecast demand levels for Big Mac hamburgers at a local McDonald'...
A: Let, Ft+1 = Forecast for friday Yt = 48.00 Ft = 77.60 α = 0.40 Thus expression for the forecast for ...
Q: i
A: A productivity measure is expressed as the ratio of output to inputs used in a production process. I...
Q: 6-45 The Hardware Warehouse is evaluating the safety stock policy for all its items, as identified b...
A: Given data Economic Order Quantity (EOQ) = 80 units Holding cost (H) = $3 Daily demand (d) = 5 uni...
Q: A supermarket is looking to implement a decision support system, however management remains unconvi...
A: As per Bartleby's guidelines, we only answer the first question in case multiple unrelated questions...
Q: what are the factors to consider in selecting a place or location for a business?
A: Location decision is the process of selecting the ideal location from different alternatives to set ...
Q: Cooperatives provide their services to their members only, hence you have to become a member to avai...
A: Cooperatives are member-possessed, member-administered organizations that operate to support their m...
Q: 1.What is Scope Verification 2. Define Scope Change Control 3. Purpose of Scope Change Control 4. E...
A: (1) Scope verification is the process of obtaining formal stakeholder acceptance of the project scop...
Q: What is the difference between tangible and intangible resources? Which do you find to be more valua...
A: An organisation requires different varieties of assets in order to successfully carry out it's produ...
Q: A type of histogram in which the categories are plotted in the descending rank order of the magnitud...
A: Project the board charts are visual portrayals of information that transform troublesome venture the...
Q: a. What are the types of lubricants ? p. What are the "golden rules" of good ubrication?
A: Generally speaking, the most widely recognized utilization of oil is to lessen impedance between two...
Q: Blair & Rosen, Inc. (BSR) is a brokerage firm that specializes in investment portfolios designed to ...
A: Note: - As we can answer only up to three subparts we will answer the first three subparts(a, b, and...
Q: Discuss why inventory is an important consideration for managers. Be sure to provide examples to ill...
A: Inventory is the raw material and finished product that the company stores and maintain for manufact...
Q: you are required to discuss the role of HR in terms of 1. recruitment and selection for operation...
A: Human resources Dept. is indeed the section/dept of an organization that is responsible for locating...
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- How are you managing your e-mails now? Are you mixing personal and school and work-related e-mails in the same account?Which of the following is a reason for organizations to employ social network analysis (SNA)? To identify subject experts and set up mechanisms to facilitate the passing of knowledge from experts to colleagues To decrease costs and improve customer service and reduce the overall investment in inventory in a supply chain To plan and record quality control activities such as product inspections, asset purchases, and material certifications To enable an organization to collect, document, assess, remediate, and attest to internal control processes and safeguardsThe local electricity company will be unable to meet demand for a week.DevastatedProvide an explanation for why business continuity measures were taken in each scenario. data from a server by a disgruntled workerThe Covid-19 containment protocols require the company to maintain a minimal workforce for many months.Firefighters flooded servers and other IT equipment while putting out an office fire.After hours, a crucial server farm was broken into.
- Due to a power plant shutdown, the nation will be without electricity for the next week.DevastatedProvide an explanation for why it was necessary to implement business continuity solutions in each instance.To prevent the spread of Covid-19, the company must keep its workforce small for many months, according to data destroyed by a disgruntled worker.Firefighters flooded the office's computers and other IT equipment while putting out the blaze.A critical server room locked up for the night was broken into.Introduction Contemporary organizations collect, store, and transmit a tremendous amount of highly sensitive data. Despite the many benefits that information technology offers, these systems are not completely secure. Proper controls must be put in place to mitigate security risks and protect vital business information. Scenario Fullsoft, Inc. is a software development company based in New York City. Fullsoft’s software product development code is kept confidential in an effort to safeguard the company’s competitive advantage in the marketplace. Fullsoft recently experienced a malware attack; as a result, proprietary information seems to have been leaked. The company is now in the process of recovering from this breach. You are a security professional who reports into Fullsoft’s infrastructure operations team. The Chief Technology Officer asks you and your colleagues to participate in a team meeting to discuss the incident and its potential impact on the company. Tasks Prepare…Which of the following is a privacy issue? Group of answer choices What information does a person or an organization have a right to obtain, under what conditions, and with what safeguards? How can we ensure that the information will be processed properly and presented accurately to users? How should we handle illegally copying copyrighted software? What information about oneself should an individual be required to reveal to others?
- The executive team at DataX Space is working hard to make the organization a safer place for employees to work. All except which of the following actions would help improve safety? Create and implement a policy regarding emergency situations Appoint a coordinator to oversee the development and implementation of the plan Create an advisory committee to oversee safety concerns Appoint a safety specialist to enforce all safety practicesWhich of the following is the MOST relevant information to include in an information security risk report to facilitate senior management’sunderstanding of impact to the organization? Findings from recent penetration testing Status of identified key security risks Risks inherent in new security technologies Detailed assessment of the security risk profileHow a business might be negatively affected by not having functioning email software
- Computer ethics question: You lose your privacy and are fully aware of this loss of privacy as it is happening. The circumstances that led to this privacy loss were out of your control, but you don't really feel bothered or worried about having lost your privacy at all. In this scenario, your normative privacy has been lost. should take about 2-4 minutes Consider the following scenario: You lose your privacy and are fully aware of this loss of privacy as it is happening. The circumstances that led to this privacy loss were out of your control, but you don't really feel bothered or worried about having lost your privacy at all. In this scenario, your normative privacy has been lost.Answer choices: false there is not enough information to draw an informed conclusion trueA social media plan should be monitored after it has been implemented because social media campaigns can be fluid. Question 5 options: True False29 IT system quality is a crucial success factor for creating a favourable e-government environment. Select one: a. True b. False

