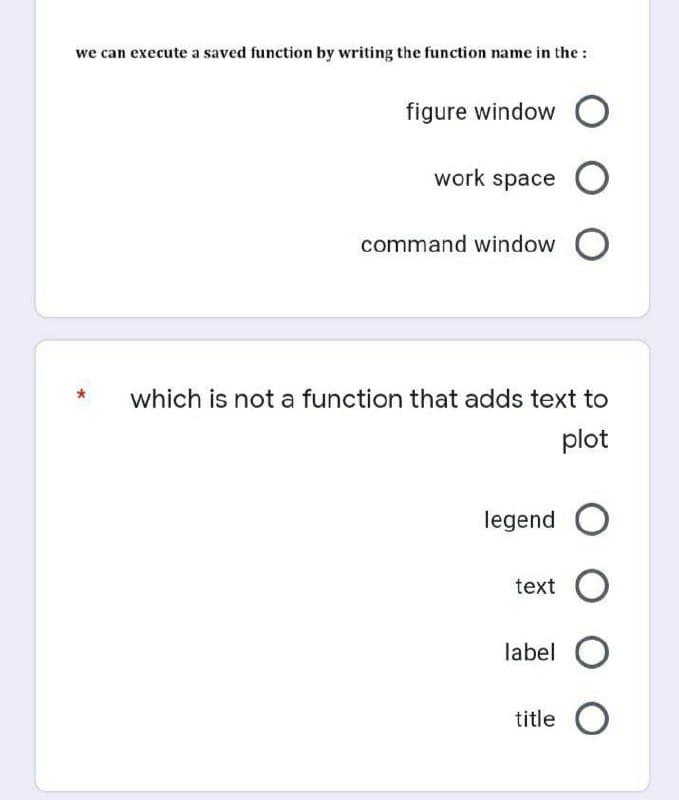
we can execute a saved function by writing the function name in the : figure window O work space O command window O which is not a function that adds text to plot legend O text O label O title O
Q: Terry assigns to client 1, Carle assigns to client 3, Mc Clymonds assigns to client 2, the optimal…
A: Answer - Terry assign to client 1, carle assigns to client 3, Mc clymonds assigns to client 2, the…
Q: a network OSI layer that is responsible for .authentication and authorization application layer…
A: Let us see the answer below,
Q: In term of security, which network .protocol is better
A: Given question is - in term of security, which network protocol is better Answer for the same with…
Q: Are there any benefits to using pure functions, and if so, how?
A: Given: An important benefit of pure works is that they don't have any negative side effects. When…
Q: What impact has the use of ICT had on our society today?
A: Introduction: The broad use of information and communication technologies has had a profound impact…
Q: If someone tried to get into your computer, where would you look?
A: Windows Task Manager: Windows Task Manager, you may see whether any programmes have been started on…
Q: What is the most important differences between connectionless communication and connectionoriented…
A: Introduction: Communication: Communication is the process of exchanging data from one source to…
Q: 10. To move content of register to another in 8086, write as following. MOV AH, BL OMOV AX, BX MOV…
A: The MOV instruction in 8086 can be: MOV reg , reg MOV mem , reg MOV reg , mem MOV reg, immediate MOV…
Q: The daily demand for interior paint cannot exceed that for exterior paint by more than 1 ton. Also,…
A: When the isoprofit line becomes parallel to either constraint 1 or the constraint 2 , then the…
Q: Why are foreign keys so important to a database's integrity? Is there a specific rationale for this…
A: Introduction: You are able to declare that a file in one table is connected to a list in another…
Q: Are you familiar with the concepts of top-down design? Is that the case? Discuss at least one…
A: Yes, our strategy has been from the top down. A top-down design is a process of breaking a system…
Q: What is type casting? Explain implicit and explicit type conversion with example.
A: Type casting or type-conversion is the process of converting one data type to another. If you wish…
Q: Do research on the iOS and Android Operating system. From that research, share the similarities and…
A: Similarities 1. Simple Application Installation It is exceptionally simple to introduce an…
Q: What are some of the most prevalent methods of system development? Each method's key advantages and…
A: Some methods of system developments are: 1) Agile Development Method When adding new functionality,…
Q: Are there any other factors that developers should keep in mind?
A: Software developer: Developers is an expert who develops, designs and builds software. Software…
Q: when the DHCP lease expires or .approaches expiration * the device stay on its same IP address for…
A: 1) IP addresses that are dynamically allocated by a DHCP server to connected devices on network. 2)…
Q: IP address routing prefix of .(255.255.255.192) can be written as /25 O /26 O /27 O /28 O
A: IP address routing prefix of (255.255.255.192) can be written as /26.(255.255.255.192)
Q: Tablet and mobile phone use in the office has to be discussed.
A: Introduction: Electronic gadgets are parts for controlling the progression of electrical flows with…
Q: Define the instance and local variables.
A: A variable is a name given to a memory area. It is the essential unit of capacity in a program.…
Q: Please explain why user-defined functions are preferable than pre-defined ones in the context of…
A: User-defined functions : User-defined functions are a kind of function that may be used inside the…
Q: Useful when you need to identify yourself but don't want to use a credit card or an ATM. The…
A: Several steps are taken to safeguard your safety at the ATM. The following are precautions to take…
Q: Write out a function that prints out all the permutations of a string. For example, abc would give…
A:
Q: What kind of long-term effects does a data breach have on the security provided by the cloud? In…
A: Introduction Here are some of the repercussions of a data breach on cloud security: The loss of…
Q: Computer Science A summary report on robotic sweeper. please help to write. 150- 400 words
A: Answer: Robotic Vacuum Cleaner Or robotic sweeper is a machine or a little plate to be exact, which…
Q: What are your options for keeping your social media accounts private?
A: What is the social media platform? Social media is a computer-based technology. In this technology,…
Q: Is there anything you'd want to say about Windows 10?
A: Given: Windows 10 is an operating system developed by Microsoft for use on personal computers,…
Q: 1. Find the answer on the given sets below corresponding the operations (union, intersection and…
A: Given: U={1,2,3,4,5,6} A={1,2,3} B={2,3,4} C={1,5} Deduction from the given info: A'={4,5,6}…
Q: Explain the importance of firewalls in maintaining the safety and privacy of a network. As a company…
A: What is a firewall? A firewall is a security tool that can be either software or hardware-based on a…
Q: Imagine that you have been given the responsibility of serving as the JAD session's facilitator. If…
A: Introduction: Session leader for the Joint Anti-Doping Agency As a JAD session leader, you're solely…
Q: Write a Little Man program that determines if the number entered by a user is an odd or even…
A: To write the above program following logic will be used: If the number when divided by 2 leaves any…
Q: A very successful cinema director named "Chef" decided to solve the problem. When a customer wants…
A: Algorithm: Firstly we will take input for the number of test cases. After that we will take the…
Q: To what degree is it feasible to define a digital signature, and if this is the case, how does the…
A: Given: Digital signatures are electronic "fingerprints" that securely connect a signer with a…
Q: te the differences between Class and Interface with example in ja
A: Introduction: Below the differences between Class and Interface with example in java
Q: firewalls are critical for network security and cybersecurity, thus it's important to understand…
A: Let's start by asking, "Why firewall: I have a computer, and it works well. I'm doing a fantastic…
Q: LAB: Number pattern Write a recursive function called print_num_pattern() to output the following…
A: Python code with given test case and output in detail below.
Q: Explain how firewalls can keep your business safe. What are the advantages and disadvantages of…
A: The pros and cons of using hardware and software firewalls, software tools, and the most effective…
Q: .one of the routing table contents port numbers O interfaces O
A: routing table: In a computer network, a route table, or the basis of route information, is a table…
Q: Investigate the ways in which gaining data via observation and through the inspection of documents…
A: The Answer is in given below steps
Q: Privacy is a broad term, but what do you mean by that? Does it truly make a difference?? And what…
A: Internet access should be restricted will not be very helpful as the attackers and other crackers…
Q: There are a lot of benefits that come with using pure functions.
A: Introduction: The following are some of the benefits of pure functions:
Q: Describe the critical steps that a company may take to improve data quality.
A: Answer is given below. 1). Focus on Your Most Important Data First Not all data is created…
Q: What do you think the future of AI will be? Justify your response?
A: Introduction Artificial intelligence today is properly known as narrow AI, in that it is designed…
Q: What are the most important tasks that an operating system must do on your behalf computer?
A: The above question is answered in step 2 :-
Q: In today's world, what role does information security management play?
A: In today's enterprises, information security is viewed as a realm of specialists who install and…
Q: What will be the output of the following code? A=100; if(A>99) clear A; end A is first stored and…
A: A=100; This statement adds variable A and its value to the workspace if(A>99) clear A;…
Q: * The role of MTA forwards the emails into mailboxes O transfer the Email across the network to the…
A: A message transfer agent ( in short MTA), often known as a mail transfer agent/ mail relay is a…
Q: Which of the following statements shows the result of executing the following line in the editor…
A: abs() function returns the absolute value of a number.
Q: To begin, let's talk about Windows Services.
A: Definition: Microsoft Windows services, formerly known as NT services, enable you to create…
Q: Write a Little Computer Man program that determines if the number entered by a user is an odd or…
A: Process: A number is even if it is perfectly divisible by 2. When the number is divided by 2, we use…
Q: How would you define computer, hardware, memory, and read-only memory (ROM)? What are the…
A: Computer: A computer is an electronic device that stores and processes data, usually in a binary…
Step by step
Solved in 4 steps

- In the code below, why is it that the displayName() module cannot print the person’s name?Start Call getInput() Call displayName()StopModule getInput() Declare String name Display "Enter your name: " Input nameEnd ModuleModule displayName() Display "Your name is: " + nameEnd ModuleWrite an application that determines whether the first two files are located in the same folder as the third one. If the files are in the same folder display All files are in the same folder, otherwise display Files are not in the same folder. Test the program when the files are in the same folder and when they are not.def menu():print("[1] Load Shapes")print("[2]Exit the program")print("[3] Add shapes")print("[4] Save shapes")option = int(input("Enter your option:"))while option != 0:if option > 4:print("Error:please enter a valid number.")break I'd like to add some error handling in here so that if a user types in a letter it prints a message saying "please only enter numbers, no letters"
- In C# language using Microsoft Visual Studio in Windows Forms App (.NET Framework) A slot machine is a gambling device that the user inserts money into and then pulls a lever (or presses a button). The slot machine then displays a set of random images. If two or more of the images match, the user wins an amount of money, which the slot machine dispenses back to the user. Design a program that simulates a slot machine. When the program runs, it should do the following: Ask the user to enter the amount of money he or she wants to insert into the slot machine. Create an application that simulates a slot machine. The application should let the user enter into a TextBox the amount of money he or she is inserting into the machine. When the user clicks the Spin button, the application should display three randomly selected symbols. (Slot machines traditionally display fruit symbols.For each of the following exercises, you may choose to write a console-based or GUI application, or both. Write a program named TestScoreList that accepts eight int values representing student test scores. Display each of the values along with a message that indicates how far it is from the average.For each of the following exercises, you may choose to write a console-based or GUI application, or both. Write a program for The Carefree Resort named ResortPrices that prompts the user to enter the number of days for a resort stay. Then display the price per night and the total price. Nightly rates are $200 for one or two nights; $180 for three or four nights; $160 for five, six, or seven nights; and $145 for eight nights or more.
- Most of the memory locations declared in an application should be class-level variables. a. True b. FalseA(n) _____________ is generated when a user interacts with a GUI object. a. error b. occasion c. method d. eventLook at this program: int main(){ int x = 4; displayMessage(); return 0;}void displayMessage(){ for(int x = 1; x <= 100; x++) cout << "I love computer science" << endl;} What will the output be? Answers: Nothing. It won't compile because you can't define the variable x inside a loop heading. Nothing. It won't compile because the displayMessage function is being called before it has been defined "I love computer science" 100 times "I love computer science" Nothing. It won't compile because you can't call a void metho
- The other half is in the photos Read the paint program below carefully and complete the source code paint.cpp by: 1. write function “myInit” of your own where you must a) setup viewport, b)set clear color to black and clear window, and c) setup matrix mode and viewing 2. Create your right menu containing the following submenus and main entries: a) color menu with eight entries “Red”, “Green”, “Blue”, “Cyan”, “Magenta”, “Yellow”, “White”, and “Black” b) pixel menu with two entries “Increase pixel size” and “Decrease pixel size” c) fill menu with two entries “Fill on” and “Fill off” d) two main entries “clear” and “quit” 3. Compile and run the program. Your complete program must be able to draw line segments, rectangles, triangles, pixels with specified color. It must also be able to accept keyboard input and display the text on the screen when work in text mode. /* paint.cpp */ #define LINE 1 #define RECTANGLE 2 #define TRIANGLE 3 #define POINTS 4 #define TEXT 5 #include…3. The following program loads and displays an image. Complete the draw_border function to draw a black border around the image. Don’t change the size of the image - draw 5 black lines across the top and bottom and 5 black lines down the left and right sides of the image. Do not change the main function. import image def draw_border(pic):'''Returns an image with a black border around it'''pass #You can leave this or remove it#Your code here to draw a black border around the image def main():'''Controls the program'''fname = "https://runestone.academy/runestone/static/instructorguide/_static/arch.jpg"img = image.Image(fname)width = img.getWidth()height = img.getHeight()win = image.ImageWin(width, height)draw_border(img)img.draw(win) main() #Run the programA slot machine is a gambling device that the user inserts money into and then pulls a lever (or presses a button). The slot machine then displays a set of random images. If two or more of the images match, the user wins an amount of money that the slot machine dispenses back to the user. Create a program that simulates a slot machine. When the program runs, it should do the following: • Asks the user to enter the amount of money he or she wants to enter into the slot machine. Instead of displaying images, the program will randomly select a word from the following list: Cherries, Oranges, Plums, Bells, Melons, Bars To select a word, the program can generate a random number in the range of 0 through 5. If the number is 0, the selected word is Cherries; if the number is 1, the selected word is Oranges; and so forth. The program should randomly select a word from this list three times and display all three of the words. • If none of the randomly selected words match, the program will…







