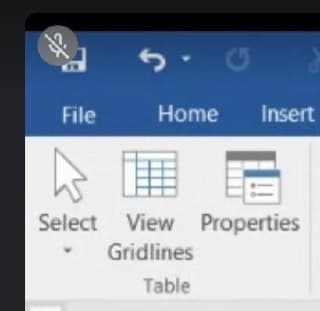
What are the commands and the implementation of a set table
Q: What exactly is a release methodology? What is the significance of version control?]
A: Introduction: Methods of release and the significance of version control The release methodology is ...
Q: In this chapter's case study, JWD Consulting used the predictive approach to build their intranet si...
A: Agile methodology is a recurring method of software development. Each repetition of a quick course t...
Q: Assume x goes to $s0, y goes to $s1, and the address of the first element in the array A goes to $s2...
A: Given that, Assume x goes to $s0, y goes to $s1, and the address of the first element in the array A...
Q: Convert the following base 3 number to its base 10 equivalent: (12001)3
A: (12001)3 To be Converted :- Equivalent Base 10 Number :- ( ? )10
Q: Create a Java program that will display the login password window. Using GUI See the pciture below ...
A: code : import javax.swing.*; import java.awt.*; import java.awt.event.*; import java.lang.Excepti...
Q: What is the best way to test memory on a Windows XP machine using the Memory Diagnostics program wit...
A: Introduction: The Memory Diagnostic tool can be used to diagnose memory-related issues or to elimina...
Q: Convert the base 10 number to its hexadecimal equivalent. Express your answer in expanded form. 946...
A: Before converting decimal ( base 10 ) to hexadecimal ( base 16) . We must know that Any remainder t...
Q: processed in a loop. The program should ‘dump’ the contents of the array before and after modificati...
A: 10. Write a program that modifies an array of 10 full words by replacing every negative value with...
Q: s the concept of registry manage
A: Sorry for that as per the bartleby guidelines we can solve only one question for you if you want to ...
Q: What exactly is computer programming? What factors should be addressed before selecting a computer p...
A: Computer programming is a method of instructing machines on what to do next. This is referred to as ...
Q: Question 3 Except where otherwise stated, any code you write in this question should be in Java. (a)...
A: Here is the detailed explanation of the solution
Q: Define the phrase "token."
A: A software token (a.k.a. soft token) is a piece of a two-factor confirmation security gadget that mi...
Q: What exactly is a named argument?
A: Named arguments also known as Keyword arguments are those values which when passed to a method / fun...
Q: What are the STL's two queue-like containers?
A: Introduction: An STL container is a grouping of items of the same kind (the elements). The elements ...
Q: Code the following using JavaScript: Create your own red-black tree and verify that binary search...
A: Here i explain it: ============================================================================== 1....
Q: CloseFile should have a description.
A: Introduction: PureBasic is designed as a revised version of BASIC by Fantaisie Software for Windows ...
Q: Write a subroutine which copies a string starting from address $1100 to a location starting from add...
A:
Q: If we think about it in terms of SQL, why can indexing cause updates and deletions to take longer?
A: Indexing: => Indexing is a data structure technique that allows you to quickly retrieve record...
Q: What are some of the main reasons he cites for the significance of good cyber defence?
A: According to the question cyber security is a important area of our global world to make secure us b...
Q: What is the difference between an output device and a dot-matrix printer?
A: Introduction: Output Devices It's an electromechanical device that accepts data from a computer and ...
Q: Computer science Explain why end-to-end testing is required and what the purpose of doing so is.
A: Introduction: The process of creating objective assessments of how well a system (device) meets, exc...
Q: Convert the following infix expression to prefix expression using stack Infix: (A+ B * C) (M * N...
A: INTRODUCTION: In the given problem statement, we are asked to convert one given expression in infix ...
Q: Explain what the "for each item in list" procedure (pictured below) does and/or why you might need t...
A: for each loop: The for-each loop is used to iterate each element in the list which means the loop wi...
Q: The following table is in 2NF. Convert it to 3NF using proper notation: Forum (ForumNum, ForumDate,...
A: Second normal form (2NF) is based on full functional dependency and the third normal form (3NF) is b...
Q: What exactly is an output device, and where does a dot-matrix printer fit in?
A: What exactly is an output device ? The output device can be any physical object that produces info...
Q: Consider a software engineering project and explain what happens if architecture is included vs what...
A: For example, if you want to build a home, you'll need an architectural plan. We had to figure out wh...
Q: What is the function of browsers?
A: Given We know about the function of browser.
Q: What are some of the main reasons he gives for having a robust cyber defence?
A: Introduction: Defending your device, software, and network from cyberattacks or threats is what cybe...
Q: Computers IMAGE PROCESS A medical image has a size of 8*8 inches. The sampling resolution in 5 cycle...
A: Below is the answer to above question. I hope this will meet your requirements.
Q: What are the memory addressing capabilities of the 20-bit address bus?
A: Introduction: the question is about the memory addressing capabilities of the 20-bit address bus
Q: Please explain what recurrence is using two distinct instances.
A: Introduction: A recurrence relation is a mathematical equation that describes a series based on a ru...
Q: Provide a list of security rules (at least 6) for a financial system that can be used/deployed in th...
A: -six security rules are 1.the european general data protection regulation(GDPR). it is a security ...
Q: An algorithm that has time complexity of O(n^2) requires 1 second to process 10 input records. Appro...
A: As per our company policy we can attempted one question at a time if you want the answer of the anot...
Q: Define a function calc_total_inches, with parameters num feet and numunches, that returns the total ...
A: - We have to code for the total number of inches with the feet and inch as the parameters as the fun...
Q: Instructions 1. Write a console application that uses at least five (5) different methods of Math cl...
A: Code is given below :
Q: 2s complement is used to represent signed integer, especially positive integers * True False O skip ...
A: According to the question number system always help us to trace the value of machine language which ...
Q: Differentiate the Intensity transformation and Neighbourhood operations applied on a digital image w...
A: Intensity transformation and neighborhood operations are the data analyzing techniques. Intensity tr...
Q: What are the advantages of utilising containers to replace virtual machines?
A: Intro Virtual machine (also known as a virtual machine): A Virtual Machine (VM) is a registered ass...
Q: What is the distinction between static and dynamic VLANs? When, as a network designer, should we uti...
A: Intro What is the distinction between static and dynamic VLANs? When, as a network designer, should ...
Q: Describe your thoughts on artificial intelligence, technological developments, and humanoid species....
A: Research and technology have advanced so rapidly that it is no surprise that the birth and mortality...
Q: How do you use the mouse to move a control to a different spot on the form?
A: Introduction: the question is about How do you use the mouse to move a control to a different spot o...
Q: Given the following binary number in 32-bit (single precision) IEEE-754 format, the decimal value cl...
A:
Q: Suppose you have a RISC machine with a 2.7 GHz clock (i.e., the clock ticks 2.7 billion times per se...
A: Below is the correct answer to above question. I hope this will helpful for you.....
Q: Question: For each of the below three problems, draw the state diagram of a pushdown automaton. (a...
A: Context Free Grammar is a grammar which is represented as G=(V,T,P,S) Where V is set of non termin...
Q: An address in a block is given as 182.18.127.99. Find the number of addresses in the block, the Netw...
A: Below is the answer to above query. I hope this will helpful....
Q: What must you do first before deleting the programme folder containing background-running software?
A: Introduction: Before eliminating the program folder containing background applications, this must be...
Q: Write a Python function to prompt the user to enter a nucleotide sequence 5' to 3' and then print ou...
A: The required python program is provided in the next step by using the for loops and comments are wri...
Q: Give a brief description of WriteStackFrame.
A: Intro the above question is about Give a brief description of WriteStackFrame.
Q: What are the reasons Pine Valley Furniture Company could require a data warehouse?
A: Data warehouse for Pine Valley Furniture Company (PVFC) Combining the data from one or more sources ...
Q: What grouping does the rollup subclause give, and how does it vary from the CUBE subclause?
A: Introduction: The GROUP BY clause include two sub-clauses and they are: CUBE Sub-clause ROLLUP Sub...
Step by step
Solved in 2 steps

- The View tab contains commands that you can use to customize the display of items in the File Explorer window true false Quick status displays more information about the applicationtruefalsepublic void onClick(View view) {//declare variablesdouble a,b,c;//text values from x and yString S1= inputXEdit_Text.getText().toString();String S2 = inputYEdit_Text.getText().toString();a= Double.parseDouble(S1);b= Double.parseDouble(S2);//adding operation with variablesc=a+b;//c=a-b;// convert the answer to a numberString s=Double.toString(c);//display result it textViewtextView.setText(s); Please help to add math operations(-, * , / ) on JavaComplete main.cpp to invoke the TaskMenu operations: viewPendingTasks(); viewCompletedTasks(); addNewTask(); editTask(); deleteTask();
- List the components that are automatically created when you place a DataGridView control on a form.Window 1Should have a welcome message, a textbox to receive AN EXISTING ID of the user and a button to access the data base. All users ID should be saved in a data base (Don’t use access). Once the Id is verified then the program will give the user access to the main menu window.Your database should have the following columns. Use SQL/mySQL to create the database and Netbeans as the IDE.In a DataGridView control, you can format a bound column’s data using the column’s ____ property. a. DefaultCellStyle b. StyleFormat c. AutoSizeColumnsMode d. BindingNavigator
- Transcribed Image Text /* you have a sceneraio for recruting app */ In which you have two types of Record type on Position Object one is for Technical and one is non technical Record type. you have to write a SOQL query to fetch All the reocrd type of the ID of Technical Record Type. Please Run the SOQL Query on the Anonymous Window. also please attach the screenshot of the output. Apex, SalesforceAdd functionality to retrieve a car record either by ID, Model, or price range. Add menu options to retrieve a car record by a car by Id or Model name a user should be able to search by ID or by item name create only one submenu option for searching the search should not be case sensitive (for example, a user may enter sTRolleR or STROLLER); store items in all lower/upper case to expedite the search write one search function that can search by ID and name and goes through the array of structs/objects only once allow partial search; must return all matching items (for example, a user can enter "roll" to search for a "stroller"; return "rolls", "stroller"); see C++ find() function show the entire record if found or an appropriate message if not by a price range user should be able to enter the target price and the range; for exampletarget price: 5000range %: 20 20% of 5000 is 1000, display all valid car records with a price at least $4000 (5000-1000) and no more than $6000 (5000+20%)Window 1Should have a welcome message, a textbox to receive AN EXISTING ID of the user and a button to access the data base. All users ID should be saved in a data base (Don’t use access). Once the Id is verified then the program will give the user access to the main menu window.Your database should have the following columns.
- The__________ control contains buttons for moving from one record to anotherin a dataset.a. BindingNavigatorb. BindingSource c. TableAdapterd. TableAdapterManagerDescribe procedure of views saving reprogramming effort.A __________ can display an entire database table in a scrollable grid on an application’s form. a. scrollable data control b. Table control c. SmartGrid control d. DataGridView control



