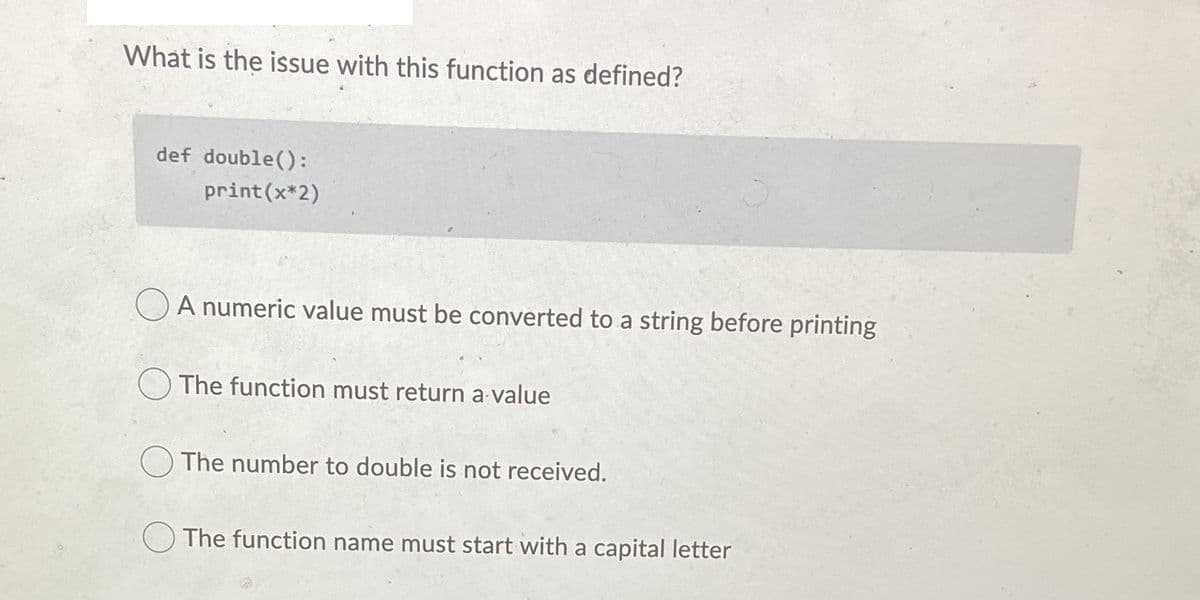
What is the issue with this function as defined? def double(): print (x*2) A numeric value must be converted to a string before printing The function must return a value The number to double is not received. The function name must start with a capital letter
Q: 1-Write a programto set (bit- 15) and clear (bit-0) thatstored in memory locations form (01F0)Hto…
A: #Code org 100h.DATANUM DW 1111H,2222H,3333H,4444H,5555H,6666H,7777H,8888H.CODEMOV AX,@DATAMOV…
Q: What exactly is the goal of artificial intelligence
A: Introduction: Artificial intelligence aims to improve people's ability to learn, think, and perceive…
Q: If you were to utilize the website provided by your bank, in what ways would each of the three…
A: Introduction: People rely on banks. Banks connect consumers with deficit and surplus assets. Net…
Q: The public key cryptography community had to face its first obstacle head-on when it came to the…
A: Introduction: Public key cryptography needs two keys, one kept secret and one made public.…
Q: When you refer to "fuzzy logic," can you perhaps explain precisely what you mean by that?
A: Definition: Fuzzy logic is a method of variable processing that allows for the processing of…
Q: It is important to compile a list of all known hazard categories and rank them according to the…
A: Definition: With URL evidence, categories threats from most commonly seen to least frequently found…
Q: What does an abstract class serve?
A: Introduction: The abstract keyword must be used to declare any class as an abstract class.
Q: The MetaData component of the architecture is the one that is considered to be the most important…
A: Definition: In response to the question The database is built on the central webpage. RDBMS…
Q: What precisely does it imply when people talk about "header-based vulnerabilities"? I'd appreciate…
A: In this section, we are needed to clarify what is meant by the term "header-based vulnerabilities"…
Q: Is there a specific factor that contributes to the severity of the threat posed by zero-day…
A: A zero-day exploit is a security flaw in a piece of software that has been identified by the…
Q: How may challenges pertaining to multi-period financial management be modeled via linear…
A: Given: How can multiperiod financial management issues be modelled using linear programming?
Q: It is extremely difficult to build a mobile network that does not require wireless technology at any…
A: Intro Wireless Technology: RF technology is a frequency in the electromagnetic spectrum linked to…
Q: What are the primary differences between backward integration and forward integration, and what…
A: Introduction: Backward integration occurs when a corporation collaborates with suppliers to get raw…
Q: In a few phrases, explain what a star schema is and how it is used in data architecture for business…
A: Intro SCHEMA DES STARS - Star schema is a mature modeling technique or methodology that is commonly…
Q: Assume a bank's database is protected using snapshot isolation database technology. Do you…
A: Intro Banks safeguard their data: Banks must first reevaluate their existing back-office and…
Q: Why isn't a data item represented in a data model?
A: It is possible to think of a data model as an abstract model that organizes and standardizes data…
Q: Although wired and wireless networks each have their own set of benefits and drawbacks, wireless…
A: Wireless Networks: A network comprised of wired connections. A wired network connects computers via…
Q: What precisely is meant by the phrase "dynamic scoping," how is it used, and how can its performance…
A: Introduction Definition: Dynamic scoping is an unusual way of looking at programming languages.…
Q: VMware has hands-on labs you can use to work with products. 1. Log on to your myvmware account. 2.…
A: Answer:
Q: Make a distinction between the general and the specialized types of requirements, both of which…
A: The following are some of the sorts of requirements for a computer-based system:- System…
Q: Using examples, define a real-time operating system. Describe how it varies from a normal operating…
A: In this issue, we will talk about real-time operating systems and how they vary from traditional…
Q: What are the most prominent differences and similarities, and how do they relate to one another,…
A: Given: Five differences between on-premises and cloud IT SECURITY solutions Datacenter security is…
Q: Explain "two-tier" and "three-tier" app architectures. Which is better for web apps? Why?
A: Given: The functionality of a multi-tiered application is segregated into discrete functional…
Q: Differentiate between a two-tier and a three-tier application design using examples. What is the…
A: Application architectures: There are many different kinds of application architectures, but the most…
Q: What do you think are the most significant factors to take into account when selecting an operating…
A: Given: Top 10 Things to Think About When Making Embedded Software 1) Product Requirement…
Q: What are the key differences between the solid-state disks (SSDs) used in laptop computers and those…
A: Given: We will learn how corporate SSDs differ from SSDs used in laptop PCs. An enterprise SSD is a…
Q: Why isn't "store-and-forward network" technology used in general communications any longer? Also,…
A: Solution: Store and forward packet-switching ensure high-quality data packet delivery. Because…
Q: Give a quick overview of one of the caching protocols available.
A: Intro What happens in a multiprocessor system is that many processes look for a copy of a common…
Q: ng characteristics between activ
A: Passive scanners accentuate monitoring network action, while active scanners are equipped for…
Q: What kind of an abbreviation should be used for the term "computer output" when it refers to data…
A: Launch: A micro form is a small version of a document, generally printed on film or paper, that is…
Q: The fundamental responsibilities of an operating system are broken down into the following…
A: Operating system: An operating system is a software programme that manages and operates computing…
Q: Determine a few of the most widely used messaging programs that are now available. Do they operate…
A: SMS: SMS Short Message Service is a text messaging service(system) available on most phones,…
Q: Why was batch processing the most common way to use a computer prior to the introduction of time…
A: Given: Batch processing is a method of the automating and processing a large number of transactions…
Q: Why parallel processing improves query speed significantly.
A: Intro When we process information in parallel, we take in numerous forms of communication…
Q: Q:find the actual address for the following instruction assume X=38 and R index=DCE8 hex LOAD X(Ri),…
A: Given: X = 38 R index = DCE8 hex LOAD X(Ri) ,A
Q: mming build interconn
A: Introduction: DP is an algorithmic procedure for solving an enhancement issue by dividing it into…
Q: Why does it make more sense to hash a file that contains user passwords as opposed to encrypting…
A: Definition: Hashed passwords are safer to keep since they are compared to y, and if y = h(x), the…
Q: Is it true that there are things called Windows Services, and if so, how do such things work? Is it…
A: Given: Services are an important feature of the Microsoft Windows operating system because they…
Q: Insert the value 27 into the AVL tree below and draw the resulting AVL tree. 20 30 SO BS
A: Intro to AVL tree: AVL is a binary search tree(a binary tree where every node value is greater than…
Q: When you refer to "fuzzy logic," can you perhaps explain precisely what you mean by that?
A: Introduction: A method for the processing of variables known as fuzzy logic enables the processing…
Q: Remove all errors from the C++ program given below asap. #include using namespace std; int main(){…
A: The given program has 3 errors: Missing Semicolon after the variable initialization. Missed to…
Q: What is the purpose of an abstract class
A: Introduction Abstract class: The abstract keyword must be used to turn any class into an…
Q: Would it be beneficial to have a working grasp of Boolean logic and Venn diagrams in day-to-day…
A: Boolean logic and the Venn diagram have practical applications: George Boole was a mathematician who…
Q: When it refers about "memory leaks," what exactly does dynamic memory allocation mean to refer to?
A: Given: The technique of allocating memory space while an application is being executed or while it…
Q: What are your opinions on the need for many addressing modes in a computer?
A: Introduction: The term addressing modes refers to the way in which the operand of an instruction is…
Q: 'Rabenstein code was used to send a message with 4 information bits, you receive 100110001, if
A: The answer is
Q: of linear programming to the process of making financia
A: Introduction: Linear programming is used by financial institutions to decide the mix of financial…
Q: What are some of the benefits of cloud computing? What are the risks and challenges associated with…
A: Note: This is a multipart-based problem. As per company guidelines, only the first three parts are…
Q: It's important to note that doing a search using keywords on the internet and conducting a search…
A: Conducting in-depth research on keywords enables you to ensure that you are using the same terms as…
Q: What factors make cybercrime appealing to specific individuals?
A: There will be several motivations for every cybercrime. Some people may have good intentions toward…
Python
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

- Mark the following statements as true or false: a. To use a predefined function in a program, you need to know only the name of the function and how to use it. (1) b. A value-returning function returns only one value. (2, 3) c. Parameters allow you to use different values each time the function is called. (2, 7, 9) d. When a return statement executes in a user-defined function, the function immediately exits. (3, 4) e. A value-returning function returns only integer values. (4) f. A variable name cannot be passed to a value parameter. (3, 6) g. If a C++ function does not use parameters, parentheses around the empty parameter list are still required. (2, 3, 6) h. In C + + , the names of the corresponding formal and actual parameters must be the same. (3, 4, 6) i. A function that changes the value of a reference parameter also changes the value of the actual parameter. (7) j. Whenever the value of a reference parameter changes, the value of the actual parameter changes. (7) k. In C++, function definitions can be nested; that is, the definition of one function can be enclosed in the body of another function. (9) l. Using global variables in a program is a better programming style than using local variables, because extra variables can be avoided. (10) m. In a program, global constants are as dangerous as global variables. (10) n. The memory for a static variable remains allocated between function calls. (11)(Numerical) Write a program that tests the effectiveness of the rand() library function. Start by initializing 10 counters to 0, and then generate a large number of pseudorandom integers between 0 and 9. Each time a 0 occurs, increment the variable you have designated as the zero counter; when a 1 occurs, increment the counter variable that’s keeping count of the 1s that occur; and so on. Finally, display the number of 0s, 1s, 2s, and so on that occurred and the percentage of the time they occurred.Write a isPalindrome Function Write a function isPalindrome($str) that returns true if the parameter string is a palindrome (a palindrome is a word or sentence that reads the same forward and backward at the character level). You should ignore non-letter characters when determining if the string is a palindrome. Thus, isPalindrome("A man, a plan, a canal, Panama!") should return true.
- Write and test a function that removes the leading and trailing spaces from a string. The function has two parameters. The first parameter is the address of the original string. The second parameter is the address of a string that is almost a copy of the original string. The difference between the strings is that the first string may have leading or trailing spaces and the second string will not have leading or trailing spaces. Use the function Str_length to compute the length of the original stringdef truth_value(integer): """Convert an integer into a truth value.""" # Convert 0 into False and all other integers, # including 1, into True if integer == 0: truth_value = False else: truth_value = True return truth_value Now, write a function that goes in the opposite direction of the truth_value() function. This new function should convert a truth value into an integer. In particular, True should be converted into 1 and False into 0. Name the new function integer_0_or_1(). All you need to include below is your definition of the function integer_0_or_1(). It will be tested automatically against relevant inputs. So include your function and nothing more.Write and test the “digit” function:Function Prototype: int digit(int n,int k)This function returns the kth digit of the positive integer n. For example, if n is the integer 29,415, then the call digit(n,0) would return the digit 2, and the call digit(n,2) would return the digit 4.
- Write a function which will take 2 arguments. They are: Sentence position Your first task is to take these arguments as user input and pass these values to the function parameters. Your second task is to implement the function and remove the characters at the index number which is divisible by the position (Avoid the index number 0 as it will always be divisible by the position, so no need to remove the index 0 character). Finally, add the removed characters at the end of the new string. Return the value and then finally, print the new string at the function call. ===================================================== Input:"I love programming."3Function call:function_name("I love programming.", 3)Output:I lveprgrmmngo oai. ============================================== Input:"Python is easy to learn. I love python."6Function call:function_name("Python is easy to learn. I love python.", 6)Output:Pythonis eay to earn.I lov pythn. sl eoPlease fill the blanks for C. /*getchar VS scanf*/ #include<stdio.h> #define length 70 //Putting all function headers to top __1__ print_scanf(); __2__ print_getchar(); int main() { //print 2 sentences using getchar() for(int i = 0; i < 2; i++) { print_getchar(); } //print 2 sentences using scanf() for(int i = 0; i < 2; i++) { print_scanf(); } return 0; } //Function to print using getchar void print_getchar() { __3__ str[__4__]; //create a string called str with length defined above printf("Enter your sentence for getchar:"); int i = 0; while(1) //run forever,unless there's a break or return { /*save user's input to curChar since we need to check 2 cases: Case 1. if the inputted character is a letter we save curChar to our string (array of char) Case 2. if it's a new line character.…Write a function that counts and returns the number of vowels in the string. (For the purposes of this exercise, we are talking about the standard 5 vowels -- A, E, I, O, U). Write a function that counts and returns the number of consonants in the string. Write a function that converts the string to all lowercase. Write a function that converts the string to all uppercase. Write the following functions. Each of these functions should have a single parameter -- accepting a c-style string as an argument. The function should only do what is specified (note that none of these functions do any output to the screen). Your functions should use const in the prototype wherever it is appropriate: Write the main function that offers a menu and allows the user to test the functions you have implemented. Program C++, must use c- style
- (Format an integer) Write a function with the following header to format the inte- ger with the specified width. def format(number, width): The function returns a string for the number with prefix 0s. The size of the string is the width. For example, format(34, 4) returns "0034" and format(34, 5) returns "00034". If the number is longer than the width, the function returns the string representation for the number. For example, format(34, 1) returns "34". Write a test program that prompts the user to enter a number and its width and dis- plays a string returned from invoking format(number, width). Here is a sample run:Playing with Functions: Write a Javascript program to check if the argument passed to any function is a function type or not. I.e. Create a function check which takes a argument and check if that argument is a function or not.Write a function argument_count that accepts an integer i, followed by any number of additional arguments. The function should returnTrue if the value given to i is equal to the number of arguments that follows it, and should return False otherwise.



