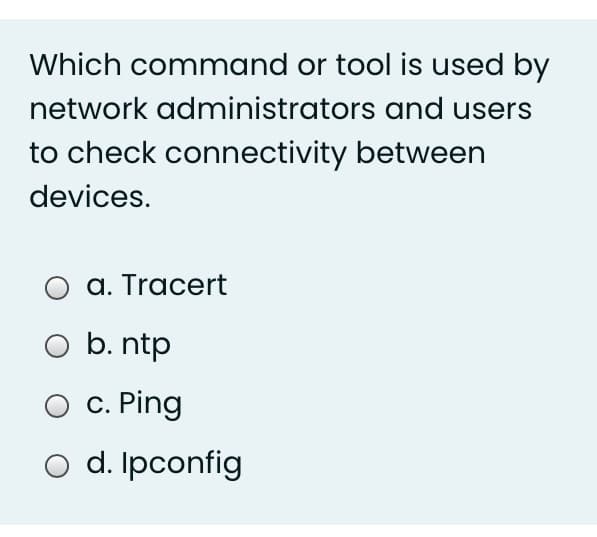
Which command or tool is used by network administrators and users to check connectivity between devices.
Q: when the DHCP lease expires or .approaches expiration * the device stay on its same IP address for…
A: 1) IP addresses that are dynamically allocated by a DHCP server to connected devices on network. 2)…
Q: QUESTION 1 000 O Desktop PC Wireless Switch Laptop Router Figure 3 A network administrator is…
A: The network administrator is connected with the Desktop Pc and the Laptop with the use of the…
Q: Assign an IP address to yours PCs using the details listed on the visual topology diagram shown…
A:
Q: Reliable data transfer guarantees that The data will not overflow the receiver's buffer OA OB. The…
A: Data transfer is any information that is transferred from one location to another through some…
Q: As network administrator, you must construct a new network for newly installed workstations. Your…
A: Topology refers to the physical organization of network equipment such as PCs, routers, hub…
Q: Using VIM, create a script that will attempt to ping all devices on your network and create a list…
A: Ping each IP address in the subnet to monitor the number of existing ad-hoc clients on a wireless…
Q: Which device monitors inbound and outbound network connections in order to identify suspicious…
A: HIDS
Q: Using Packet tracer create a WAN with four departments on different VLANs, ALL the departments…
A: Using Packet tracer create a WAN with four departments on different VLANs, ALL the…
Q: 4. Show the following commands: (a) Show the command that allows you to view all of the user…
A: Note: as per company guidelines we are supposed to answers only one question at a time. please…
Q: When is the right time to plan a network update?
A: Following are reasons behind network update 1)Expand storage capability 2)Add connect heavy devices…
Q: Network Administrator you are install a new computer lab for 30 computers, write down the basic…
A: here have to determine how to build computer lab.
Q: ______________________allows devices on one network to communicate with devices on another network?
A: Given To know about the devices enables devices on one network to connect with those on another
Q: Which of the following sentences reflects the main function of the network tap installed between two…
A: Answer : The main function of the network tap installed between two networks:
Q: The type of route that should be used on a border router to enable all devices inside the…
A: I have given an answer in step 2.
Q: As a network administrator, you are to set up a network system for a small company having about 20…
A: Introduction As a network administrator, you are to set up a network system for a small company…
Q: Set up a wireless router with three PCs and two laptops, and configure the SSID name and password of…
A: This problem is going to be solved by a tool named Cisco Packet Tracer.
Q: Which connection type, wifi or wired, do you prefer? Establish it.
A: Introduction: In response to your inquiry, The Internet is one of the enigmatic technologies that we…
Q: 1- Write the commands to change Your IP Address via CMD.
A: A set of numbers that uniquely identify a device and provide data about its location is known as an…
Q: Which of the following term best refers to a meeting point where multiple ISPS can peer together,…
A:
Q: Once the scan is complete write a short paper detailing the process you performed to run this scan…
A: Following are the advantages of running an Advanced IP Scanner : --> Enabling advanced IP…
Q: Set up a wireless router with three PCs and two laptops, and configure the SSID name and password of…
A: We will configure the the given configurations in Cisco Packet Tracer.
Q: Connections made between ATM service providers switches creates what type communication channe
A: The services provided by ATM networks are those which provide delivery of the subscriber sessions to…
Q: An IP address must always be used by the server on your network as a host that delivers a service.…
A: An IP address is a one of a kind address that recognizes a gadget on the internet or a nearby…
Q: What is the purpose of resetting network settings?
A: Introduction: Said, Reset Network Settings is a method of resetting all network settings to their…
Q: Question 22 Select the appropriate response A cable customer has reported slow access times when…
A: Question 22 : Option d) tracert At each hop, tracert makes three attempts to reach the router and…
Q: When should you schedule a network update, and how long should it take?
A: Introduction: The time frame in which the network evolved.
Q: using GNS3 Configure valid IP addresses for all hosts and ensure that all devices can communicate…
A:
Q: Problem Statement A network engineer in his office situated in Beijing China was trying to connect a…
A: router is the device that connects the Internet with a server
Q: How mac address and IP address can be helpful to secure your device on a network or how can be it…
A: Why need a Mac address: The pros/benefits of MAC address use are as follows: It offers a safe way…
Q: How can network administrators filter, examine, and detect various kinds of traffic? One method is…
A: Network Access Control: The act of keeping unauthorised users and devices out of a private network…
Q: how machine must be configured to join the network before you can utilize the User State Technology…
A: A restricted network is where NAP sends a computer that needs remediation services or to block…
Q: Your home network consisting of 1 desktop computer, 1 wireless laptop, 1 network printer, 1 wireless…
A: Step 1 Given that, the network consists of total 3 hosts and 1 router. The router is wireless and…
Q: 5 Which network device would you use in the following scenario to allow both endpoint devices to…
A: To find a network device that allows both endpoint devices to communicate with each other. The…
Q: A technician is setting up a new corporate wireless network. One of the requirements for the network…
A: A technician is setting up a new corporate wireless network. One of the requirements for the network…
Q: the ping and traceroute commands. If you were experiencing difficulties in connecting to a remote…
A: the ping and traceroute commands
Q: 50.Which transmission mode is used to send a video or radio signal in a TV transmission over your…
A: Given: 50.Which transmission mode is used to send a video or radio signal in a TV transmission over…
Q: A collection of skills and experiences enable a network administrator to understand her network and…
A: Troubleshooting the network as an administrator can easily collect information regarding the problem…
Q: A network engineer will use the show cdp neighbour command on a number of network devices when…
A: Introduction: Show CDP neighbor command: Datalink(layer 2) layer protocol Help to view all directly…
Q: please answer only the 2nd part. Thanks Demonstrate your ability to configure a switch. Your tasks…
A: Answer: This is question is from Computer Network we have answered in handwritten format.
Q: (a) Find the minimum bandwidth for an ASK signal transmitting at 7000 bps. The transmission mode is…
A: a. In ASK (Amplitude Shift Keying) relationship between baud rate and bandwidth is: BW = (1+d) * Nd…
Q: When should a network update be scheduled and for how long
A: We know that network is a medium which is used for communication among devices or can be used for…
Q: Which of the following best describes creating standard configurations for device classifications?…
A: best describes creating standard configurations for device classification
Q: Subject : System and Network Administration Solve the Question : Qusetion : You are the network…
A: Network administrators are responsible for maintaining the computer networks and for solving…
Q: Assume you're the networkadmin at ABC. Suddenly, end-users complained that they could only…
A: When several default gateways are used, IP traffic is routed to the next gateway in the backup list…
Q: In this activity, you will Deploy Network Services. First is open a sample file, locate and deploy…
A: The steps to perform the deploy network services activity are shown below. Step 1: Open the packet…
Q: If a client device (such as a Windows laptop) were present in a location where it is known that a…
A: Introduction to a wireless network Wireless networks are computer networks that communicate without…
Q: Q3/ You are a network administrator and you need to subnet your network into five subnetworks…
A: Here we find subnet mask for given question:…
Step by step
Solved in 2 steps

- Which of the following are not part of connectivity reports? VM that connects to billing database. CPU Usage Ports accessible through a firewall. User logins.Which of the following are graphical remote administration technologies? (Choose allthat apply.)a. telnetb. ssh -Xc. sshd. VNCQUESTION 20 Which of the following is a command-line utility that can be used to display, change, add, and delete network configuration settings on a computer, including basic and advanced settings? a. hostname b. nslookup c. netsh d. netstat
- .Which of the following are the primary functions of all organizations? Enable GingerCannot connect to Ginger Check your internet connectionor reload the browserDisable in this text fieldRephraseRephrase current sentenceEdit in Ginger×What service in Windows Server 2016 authenticates remote users and computers to the Windows domain and its corporate network resources? a. Active Directory b. Group Policy c. DirectAccess d. RAS (Remote Access Service)Do not copy from other websites Correct and detailed answer. Thank you! Q1 : What happens if IP Address of host cannot be determined? Select one: a. The system exit with UnknownHostException is thrown b. IOException is thrown c. Temporary IP Address is assigned d. knownHostException is thrown
- 83. Which of the following is not the Networking Devices? a. Gateways b. Linux c. Routers d. FirewallsYou are working as a security adviser on a project that tries to upgrade a legacy network. During a project meeting you were asked to give your opinion on below Devices/Technologies and the appropriate use in the context of Information Security: # Switch Vs. Hub to connect local devices. (2 marks) # Using a Firewall Vs. IDS (1.5 marks) # Using Telnet to remotely login to machines. (2 marks) # Using SFTP Vs. Cloud Services (DropBox, GDrive) to share content. (2 marks)One of your coworkers downloaded several, very large video files for a special project she’s working on for a new client. When you run your network monitor later this afternoon, what list will your coworker’s computer likely show up on? a. Top talkers b. Top listeners c. Giants d. Jabbers
- Which component uses port mirroring to collect information from domain controllers and DNS servers? Group of answer choices Advanced Threat Analytics Center Honeytoken Gateway ATA Lightweight Gateway ATA GatewayWhich of the following is not a problem that could be caused by disabling STP in a switched network? a. Broadcast storm b. MAC spoofing c. Duplicate packets d. Switching table instabilityWhich of the following commands can be used to scan the available ports on computerswithin your organization?a. tracerouteb. tracertc. nmapd. sudo



