Assign an IP address to yours PCs using the details listed on the visual topology diagram shown above. The PC should be fitted with two network adapters check with the instructor if you are unsure which network adapter should be configured. You are expected to use (FastEthernet)
Assign an IP address to yours PCs using the details listed on the visual topology diagram shown above. The PC should be fitted with two network adapters check with the instructor if you are unsure which network adapter should be configured. You are expected to use (FastEthernet)
A+ Guide To It Technical Support
10th Edition
ISBN:9780357108291
Author:ANDREWS, Jean.
Publisher:ANDREWS, Jean.
Chapter9: Supporting Mobile Devices
Section: Chapter Questions
Problem 17TC
Related questions
Question
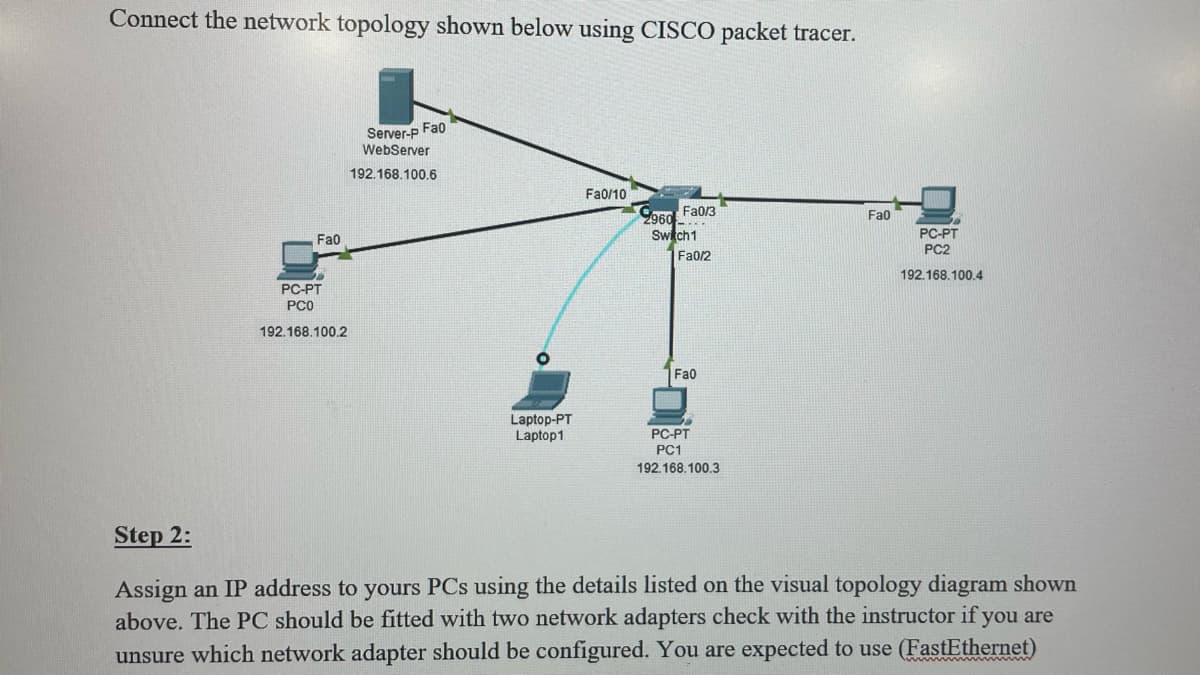
Transcribed Image Text:Connect the network topology shown below using CISCO packet tracer.
Server-p Fa0
WebServer
Fa0/10
2960 Fa0/3
Fa0
Switch1
Fa0/2
Fa0
192.168.100.6
Fa0
PC-PT
PC2
192.168.100.4
PC-PT
PC0
192.168.100.2
Laptop-PT
Laptop1
PC-PT
PC1
192.168.100.3
Step 2:
Assign an IP address to yours PCs using the details listed on the visual topology diagram shown
above. The PC should be fitted with two network adapters check with the instructor if you are
unsure which network adapter should be configured. You are expected to use (FastEthernet)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

A+ Guide to Hardware (Standalone Book) (MindTap C…
Computer Science
ISBN:
9781305266452
Author:
Jean Andrews
Publisher:
Cengage Learning

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

A+ Guide to Hardware (Standalone Book) (MindTap C…
Computer Science
ISBN:
9781305266452
Author:
Jean Andrews
Publisher:
Cengage Learning