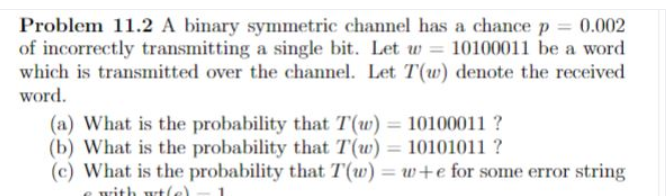
which is transmitted over the channel. Let T(w) denote the received word.
Q: You should include examples of both physical and schematic representations to show that you can tell…
A: Let us know about the model first. A model is an abstraction of reality or a representation of a…
Q: It is important to note the benefits and drawbacks of both circuit switch networks and packet switch…
A: Let's discuss what benefits and cons are offered for both network switching Techniques, i.e. Packet…
Q: Is the idea behind this "Employee Management System" sound or not?
A: "A distributed system called an employee management system was created to preserve personnel…
Q: What does "application security" mean?
A: If we talk about definition then Application security is the process of developing, adding, and…
Q: Does choosing "good enough" quality in software development offer any advantages or disadvantages?
A: The benefits of creating software that is "good enough quality" are listed below. A state of…
Q: When and why should you use a throw statement instead of a throws clause?
A: Introduction: The ‘throw’ keyword is utilized only when we need to throw an exception and are…
Q: Operating systems that aren't interrupted function better than ones that are interrupt-driven most…
A: Introduction : In my experience, a "System interrupt" is a special term that denoted that something…
Q: What benefits and drawbacks come with software of "good enough" quality?
A: "Software" collects instructions, data, or computer programs to make machines run and complete…
Q: Use structured language when explaining non-systems analysis procedures. Language structure might be…
A: Given: We have to discuss use structured language when explaining non-system analysis procedures.…
Q: important to note the benefits and drawbacks of both circuit switch networks and packet switch…
A: Please find the answer below :
Q: Consider the following program specification: Write a program that will prompt the user for 10…
A: here in this question we have asked yo write a program which take an array of 10 number ranging from…
Q: Why is software engineering essential in the creation of software applications? What is it?
A: Introduction: Applications software like data set developers, accounting sheets, internet browsers,…
Q: Talk about non-systems analytical procedures using structured language.
A: The answer is:-
Q: Is it feasible to define the terms coupling and cohesion in the context of object-oriented…
A: It is a method for analyzing and developing a system that employs an object-oriented programming…
Q: Define each layer of the OSI model and explain its function.
A: Define each layer of the OSI model and explain its function.
Q: Object-oriented design must be employed whenever it makes logical to do so. The usage of structured…
A: OOD (object-oriented design): Objects, as the name indicates, are utilised in programming.…
Q: When should distributed database systems employ data replication to address data fragmentation if it…
A: Replication in computing involves the exchange of data to ensure consistency across redundant…
Q: When and how was the abacus first employed?
A: The abacus, sometimes known as the "World's First Computing System," was used to do calculations…
Q: Describe the fundamentals of machine language. What's more, why can't electronic devices understand…
A: A computer can understand machine language, which is a low-level language composed of binary digits…
Q: Exactly what tasks do operating systems primarily serve to perform?
A: We will explore the most vital responsibilities an operating system must fulfill. We shall explore…
Q: Please provide a definition of security service.
A: A capability that supports one, or many, of the security goals. Examples of security services are…
Q: e of prototypes in the process to provide an overview of object-oriented ana
A: Introduction: The process of creating a model of a system is known as prototyping. Prototypes are…
Q: How does Ubuntu Server stack up against other server OSes?
A: The biggest competitor of ubuntu server is windows server. Windows is a popular operating system…
Q: There might be debate about how a company deploys Windows Server 2012.
A: There might be debate about how a company deploys Windows Server 2012 answer in below step.
Q: The next semester, enrol in a course that teaches a programming language. How does one decide which…
A: Languages used in Computers A programming language is a unique computer language designed to…
Q: Based on concrete instances, which operating system is quicker, interrupt-driven or not?
A: Solution: The CPU must always be informed when a peripheral has finished the work it was given, and…
Q: Why are records so important to a successful criminal investigation? List the absolute minimum…
A: Given: The Importance of Documenting Criminal InvestigationsNotes, sketches, photos, and maybe even…
Q: Describe the fundamentals of machine language. What's more, why can't electronic devices understand…
A: Fundamentals al Machine Language. Machine Language is a low…
Q: If effective interaction with the computer is feasible, why is programming required? There are…
A: Programming: The Swift programming language is an example of a high-level programming language that…
Q: y it matters more that object function takes precedence over constraints in linear progra
A: Introduction: Linear programming is a technique for optimising operations that have constraints. The…
Q: What does "interdependence" entail in relation to other concepts used to describe systems?
A: The question has been answered in step2
Q: What does the Ubuntu operating system mean in terms of a server operating system?
A: Encryption: The server of operating system known as Ubuntu Server was developed by Canonical and…
Q: Show via examples why interrupt-driven operating systems perform better overall than…
A: Show via examples why interrupt-driven operating systems perform better overall than…
Q: When two or more individuals collaborate, what does it mean? Make a list of all the different…
A: Introduction: Collaboration is a business movement wherein individuals cooperate to accomplish a…
Q: Talk about non-systems analytical procedures using structured language.
A: Structured Languages The application of structured English is an effective approach for decision…
Q: What does testing in BC/DR planning accomplish? How many different test types are there?
A: BC/DR Preparation: Business continuity and disaster preparation aid an organisation's ability to…
Q: What does the Ubuntu operating system mean in terms of a server operating system?
A: Ubuntu is an open-source operating system (OS) based on the Debian GNU/Linux distribution. Ubuntu…
Q: Suppose that a 4M × 32 main memory is built using 128K × 8 RAM chips and memory is word addressable…
A: a. How many RAM chips are needed? 128 (4M/128K*32/8 = 128) b. How many chips would be involved…
Q: If you could provide an example of a user interacting with a system and explain the discrepancy…
A: The ease with that a user is able to comprehend the present state of a system is referred to as the…
Q: It is important to try to describe procedures that are not part of the systems analysis process,…
A: Systems Analysis: "The process of evaluating a procedure or business to define its aim and purposes…
Q: How can the training demands for an e-learning system be assessed?
A: Definition: E-learning is a method of education that relies on formalized instruction but also makes…
Q: Your Name Week 4 PA User Entry of Age Please enter your age: twenty System. FormatException: Input…
A: Answer: Algorithms: Step1: we have taken user input from the of age Step2: First we have…
Q: Global positioning system is shortened to "GSM." Why do you need a SIM card for your cell phone?
A: Given: We have to discuss Global positioning system is shortened to GSM. Why do you need a SIM…
Q: It is important to examine the relative advantages of synchronous data replication and partitioning.
A: The act of storing duplicates of similar data on other nodes is known as synchronous data…
Q: Examine the numerous applications that various kinds of businesses employ information technology…
A: Information systems' foundations: Information technology may be advantageous to any business,…
Q: The organisation of the object-oriented design approaches that are used should put more focus on…
A: Start: Object-oriented design is method of the design that encompasses the process of…
Q: The security of a virtual private network (VPN) surpasses that of public Wi-Fi (VPN). When using a…
A: According to the information given:- We have to define the security of a virtual private network…
Q: The two primary roles of an OS should be briefly explained here.
A: We need to discuss two primary roles of an operating system.
Q: A virtual private network (VPN) is the best option for protecting the perimeter of a network. Can…
A: VPN is crucial for network security, and the following are a few reasons why VPN is the best…
Q: What does "interdependence" entail in relation to other concepts used to describe systems?
A: The answer of the question is given below
Step by step
Solved in 2 steps

- The previous problem is in the picture. Suppose that I have 800 Gigabytes worth of movies on my hard drive at home, and I’d like to get them to a friend in Chicago. I could either send them over the Internet, or I could copy them to a thumb drive, drive to Chicago, and deliver them by hand. Assume that the specs for my cable connection are the same as in the previous problem, but the friend in Chicago has a cable connection which gets 25 Mbps down/5 Mbps up. Which would be faster? Show your work.Computer A is sending a 10 MByte long file to Computer B via packet-switching over two consecutive 100 Mbps links of 2000 km length each.Assume that the signal propagation speed on both links is 2 x 108 m/s.Furthermore, assume that the maximum length of a packet is 1480 bytes and that Computer A fills each packet to the max, if possible. How "long" (in meters) is one bit on link 1?**Please do C****C IS different from B** a. Compute CBC-MAC for a message of 16 bits, “8642” (in Hexa). Assume a block size of 8 bits with an IV=F1 (in hexa). For simplicity, assume the encryption to be a simple XOR of the key with the plaintext. Let the encryption key be B4 (in Hexa). (Hint: Divide the message into blocks of 8 bits each; XOR each block with the previous cipher output; then encrypt this with the key. For the first block, XOR it with IV. Details in pages 325-326 Ch.12 of the textbook) b. Suppose Alice computes the Secret prefix MAC (page 322: secret prefix MAC(x) = h(key || x)) for the message ”AM” (in ASCII) with key “G” (in ASCII) that both Alice and Bob know. The hash function that is used is h(x1x2x3)= g(g(x1 XOR x2) XOR x3 ) where each xi is a character represented as 8 bits, and g(x) is a 8-bit string that is equal to the complement of bits in x. For example, g(10110011) = 01001100. The MAC is 8 bits. (8-bit ASCII representation of the characters is given…
- 10. A disadvantage of a broadcast subnet is the capacity wasted when multiple hosts attempt to access the channel at the same time. As a simplistic example, suppose that time is divided into discrete slots, with each of the n hosts attempting to use the channel with probability p during each slot. What fraction of the slots are wasted due to collisions?Assume the following parameters for Go-Back-N a) N 3 b) Round Trip Time (RTT)10 ms c) Retransmission Timeout period 40 ms d) Segment Size: 1200 bytes. Suppose that Bob sends 7 segments, numbere1 through 7, to Alice using the Go-Back-N mechanism. Suppose that Segment 3 and Segment are lost the first time the segments are sent to Alice, but reach Alice correctly when retransmitted. Apart from the above, there were no other segment losses. What is the average throughput obtained in sending all segments (in bytes/sec)? Draw a diagram to show your work in detail. 2. Assume the following parameters for Selective Repeat: b) Round Trip Time (RTT)10 ms c) Retransmission Timeout period 40 ms d) Segment Size: 1200 bytes Suppose that Bob sends 6 segments, numbered 1 through 6, to Alice using Selective Repeat. Suppose that Segment 3 gets lost the first time Bob sends it to Alice, but reaches Alice correctly when retransmitted Apart from the above, there were no other segment losses. What is the…Q1. A series of messages is to be transferred between two computers over the Internet. The messages comprise just the characters A through H. Analysis has shown that the probability (relative frequency of occurrence) of each character is as follows: A and B= 0.25, C and D= 0.14, E,F,G, and H= 0.055 (a) By computing the entropy of the source, derive the minimum average number of bits per character.
- Computer A is sending a 100 kByte long file to Computer B via packet-switching over two consecutive 10 Mbps links of 1000 km length each.Assume that the signal propagation speed on both links is 2.5 x 108 m/s.Furthermore, assume that the maximum length of a packet is 1500 bytes and that Computer A fills each packet to the max, if possible. If transmission starts at time t=0, how long (in seconds) does it take until Computer B has received the last bit of the complete file transfer?Assume that the switch between link 1 and 2 is a "store-and-forward" switch. Furthermore, assume that processing and queuing delays are negligible and no other stations are using the links.**Please do A or C** a. Compute CBC-MAC for a message of 16 bits, “8642” (in Hexa). Assume a block size of 8 bits with an IV=F1 (in hexa). For simplicity, assume the encryption to be a simple XOR of the key with the plaintext. Let the encryption key be B4 (in Hexa). (Hint: Divide the message into blocks of 8 bits each; XOR each block with the previous cipher output; then encrypt this with the key. For the first block, XOR it with IV. Details in pages 325-326 Ch.12 of the textbook) b. Suppose Alice computes the Secret prefix MAC (page 322: secret prefix MAC(x) = h(key || x)) for the message ”AM” (in ASCII) with key “G” (in ASCII) that both Alice and Bob know. The hash function that is used is h(x1x2x3)= g(g(x1 XOR x2) XOR x3 ) where each xi is a character represented as 8 bits, and g(x) is a 8-bit string that is equal to the complement of bits in x. For example, g(10110011) = 01001100. The MAC is 8 bits. (8-bit ASCII representation of the characters is given below.) What is the…Computer A is sending a 100 kByte long file to Computer B via packet-switching over two consecutive 10 Mbps links of 1000 km length each.Assume that the signal propagation speed on both links is 2.5 x 108 m/s.Furthermore, assume that the maximum length of a packet is 1500 bytes and that Computer A fills each packet to the max, if possible. How many bytes will be contained in the last packet?
- Computer A is sending a 100 kByte long file to Computer B via packet-switching over two consecutive 10 Mbps links of 1000 km length each.Assume that the signal propagation speed on both links is 2.5 x 108 m/s.Furthermore, assume that the maximum length of a packet is 1500 bytes and that Computer A fills each packet to the max, if possible. If transmission starts at time t=0, at which time (in seconds) does the first bit arrive at the switch connecting link 1 and link 2?Computer A is sending a 10 MByte long file to Computer B via packet-switching over two consecutive 100 Mbps links of 2000 km length each.Assume that the signal propagation speed on both links is 2 x 108 m/s.Furthermore, assume that the maximum length of a packet is 1480 bytes and that Computer A fills each packet to the max, if possible. If transmission starts at time t=0, at which time (in seconds) does the first bit arrive at the switch connecting link 1 and link 2? (What is the propagation delay for link 1?)Suppose that a binary message – either 0 or 1 – must be transmitted by wire from location Ato location B. However, the data sent over the wire are subject to a channel noise disturbance,so to reduce the possibility of error, the value 2 is sent over the wire when the message is1, and the value −2 is sent when the message is 0. If X, X = {−2,2}, is the value sent atlocation A, the value received at location B, denoted as R, is given byR = X + N ,where N is the channel noise disturbance, which is independent of X. When the message isreceived at location B, the receiver decodes it according to the following rule:if R ≥.5, then conclude that message 1 was sentif R < .5, then conclude that message 0 was sentAssuming that the channel noise, N, is a unit normal random variable and that the message0 or 1 is sent with equal probability, what is the probability that we conclude that the wrongmessage was sent? This is the probability of error for this communication channel











