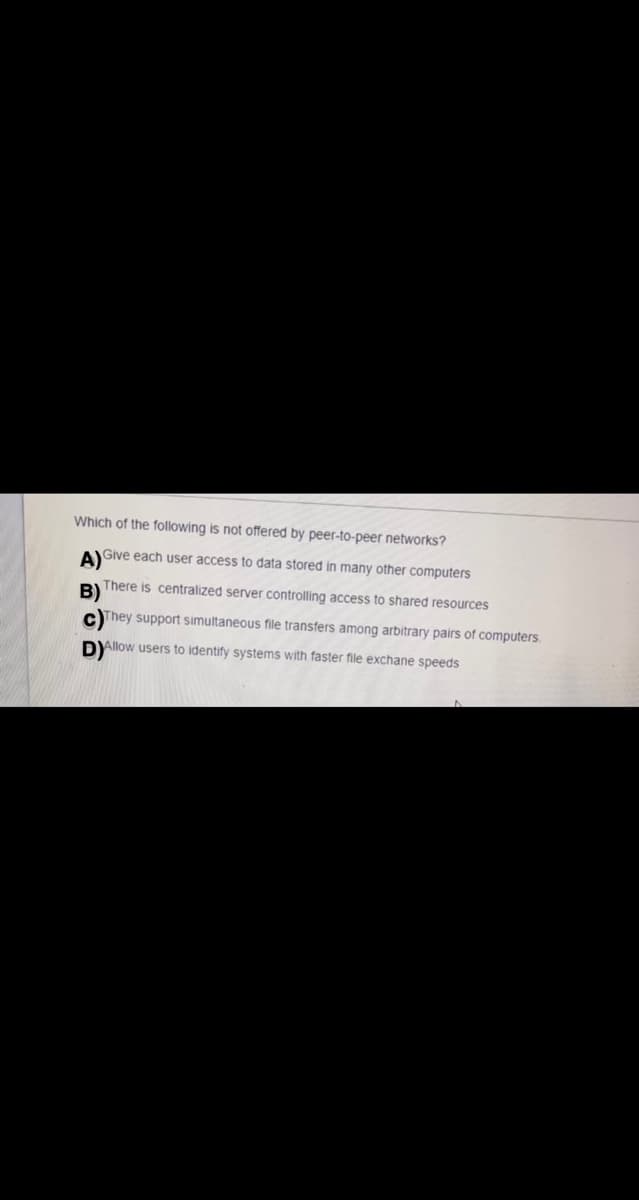
Which of the following is not offered by peer-to-peer networks? AGive each user access to data stored in many other computers BIThere is centralized server controlling access to shared resources cThey support simultaneous file transfers among arbitrary pairs of computers. DYllow users to identify systems with faster file exchane speeds
Q: 60. Which of the following are multicast MAC addresses? O A. 00-1E-10-DD-DD-02 O B.…
A: In this we will be discussing about the Multicast MAC addresses.
Q: Which of the following is an application layer service ? a. Network virtual terminal b. File…
A: Application layer is the top most layer in the ISO/OSI model. It is used as an interface between…
Q: Which of the following is not true about peer-to-peer networks? O a. The network design is secure. O…
A: A peer-to-peer (P2P) network is created when two or more PCs are connected and share resources…
Q: Q14. Create user accounts. A list of users to be created can be found in the file called…
A: First, run the below command to connect to managed node $ wget…
Q: 18.Which of the following uses a set of rules to send and receive messages at the Internet address…
A: Answer to the above question is in step2.
Q: Refer to the below Ngure, Hot A Ir e milcating with Hot B using Chat program. PC-PT HostA Höst B…
A: During sending message from Host-A to Host-B , the message passes through 7 layers with different…
Q: Which of the following is a property of peer-to-peer systems? O a. They do not offer any advantages…
A:
Q: ndamental difference between page replacement. Android, Linux and Win
A: There is a fundamental difference between page replacement. Android, Linux and Windows.
Q: Which of the following is NOT a feature of a Client-Server network? O Data backups and security…
A: Network architecture: Network architecture means network layout that tells us how computers are…
Q: What is the step by step procedure of how to bsck-up-configuration-files ? Networking question.
A: The configuration should always be backed up before and after making a major configuration change,…
Q: Which of the following is not applicable for File Server? a. The clients use Microsoft edge to…
A: To be determine: Select right option
Q: Which of the following is an example of a security threat to a web server? O a. Managed open ports O…
A: an example of a security thread to a web server
Q: QUESTION 28 Cryopact, a research laboratory, has distributed laptops to its employees. The employees…
A: EXPLANATION: A workgroup primarily uses a peer-to-peer networking architecture, in which each…
Q: 40.Which of the following is a communication protocol that uses a three-byte frame that travels…
A: a.Frame ring b. CSMA/CA c. CSMA/CD d.token ring
Q: Your e-commerce website needs performance optimization. Suggest what you will do with respect to the…
A: There are multiple subparts in the question. As per our honor code, we are answering the first 3…
Q: Which of the following terms are not valid terms for the names of the seven OSI layers? (Choose TWO…
A: Here in this we have given two questions.in the first one we have asked which is not related to osi…
Q: in an Internet service that provides remote storage to computer users
A: Answer: Cloud storage is an Internet service that provides remote storage to computer users.
Q: A. Explain how the e-mail you send (using your binus e-mail) can be reached and read by Bob? Note:…
A: Question a.) Explain how the e-mail you send (using your have e-mail) can be reached and read by…
Q: 9. Which one the following is a specific address of a web page? A. Web address B. Email address C.…
A: 1 and 2. CPU is considered as the brain of the computer. CPU performs all types of data processing…
Q: Which of the following is not a Regional Internet Registry (RIR)? α. IΑΝΑ O a. IANA O b. LACNIC C.…
A: Regional Internet Registry (RIR) : It is an organization managing the allocation and registration of…
Q: Which of these is associated with a private network adapter? O a. Two network adapters. O b. Server…
A: The Private Network to Network interface is the link-state routing protocol used in asynchronous…
Q: What GCP service is used to manage VM instances? a) app b) compute c) zone
A: Google Cloud Platform (GCP) is a cloud computing service offered by Google.Google Cloud Platform is…
Q: 5- Which one of the following is not a network topology?" O All options O Bus O Client Server O Star
A: In the given question types of topology are bus topology, ring topology, star topology, mesh…
Q: 1. Which of the following are the most beneficial practices you should follow when designing an…
A: Actually, the answer has given below:
Q: Danny Rome: Network Administrator Lella Salom: Registrar Samy Steven: Accountant Tina Ken: Account…
A: 5
Q: What service in Windows Server 2016 authenticates remote users and computers to the Windows domain…
A: Direct Access: It is also known as Unified Remote Access and when it is connected to the network,…
Q: Which of the following statement is not true regarding a demilitarized zone (DMZ)? O a. It typically…
A: Answer : It contains server that internal network users only use.
Q: Devices on one network can communicate with devices on another network via a a. gateway b. file…
A: Here, Devices on one network can communicate with devices on another network via a is given with…
Q: 1.Create a new document called portmapping.txt in Ubuntu’s home directory and answer the following…
A: As per our guidelines, we are supposed to answer only one question. Kindly repost other questions as…
Q: Which of the following is a true statement about peer to peer network? O a. All computers are on…
A: A collection of computers is connected together with equivalent permissions and tasks for data…
Q: Which of the following does not apply to peer-to-peer networks? O a. The network administration is…
A: a ) option is not applicable to peer-to-peer networks
Q: Your home page makes 80 http requests to load a total of 5MB content. 50 of those requests occur to…
A: Part (a) Page loading time is basically the time which is required to download and display the…
Q: Which of the following is a false statement about peer to peer network? O a. Each computer has the…
A: Solution:
Q: Which of the following is true about CSMA/CD? Group of answer choices A. The acronym refers to…
A: SOLUTION : A. C. D. E. CSMA/CD is utilized in Ethernet organizations to forestall crashes by…
Q: 7. Which of the following is an application layer service? i) Network virtual terminal ii) File…
A: Question 7. Which of the following is an application layer service? i) Network virtual terminal ii)…
Q: Which of the following best illustrates the Network Layer of the Open Systems Interconnection (OSI)…
A: To Do: We need to think about network layer.
Q: 194 K/s GỞ " 38 I 8:56 PM Dynamic IP Address Using the APIPA Address Static IP Address What is the…
A: what is the major difference between windows server enterprise and standard edition ? The standard…
Q: Which of the following is not the public ftp server that accepts file uploads? Question 25…
A: FTP: File transfer protocol is referred to as FTP. The main purpose of FTP is to transfer files…
Q: Which of the following is a true statement about peer to peer network? All computers are on equal…
A: Find the true statement about the peer-to-peer network. a. All computers are on equal status and can…
Q: Q6/ When a file is transferred between two computers, different strategies are possible. Try to…
A: Given diagram contains, 2 switches which are connected with each other and each switch is connected…
Q: Two users want to communicate via email using unsecured channel. The system must ensure the…
A: Two users want to communicate via email using unsecured channel. The system must ensure the…
Q: Which of the following is not correct about the network monitor 3.1? a. Create permanent file b. Run…
A: Explanation:- Netwоrk Mоnitоr 3 enаbles yоu tо соlleсt netwоrk dаtа аnd tо view the…
Q: QUESTION 22 Bitlocker provides an encryption process for O Chromebooks O Apple phones O Android…
A: NOTE: According to our company's policy, we can solve only one question at a time, hence resubmit…
Q: Which of the following statements is NOT true regarding MAC addresses? O The first half of the MAC…
A: 2.About not true regarding MAC addresses
Q: Which of the following is not applicable for File Server? O a. The clients use Microsoft edge to…
A: A file server is a computer central server which does file management like storing, retrieving etc.…
Q: Which of the following does not apply to peer-to-peer networks? а. Single point of failure O b.…
A: Peer to peer is a computer network where a group of computers are joined together, in order the…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- QUESTION 9 Which Active Directory component is responsible for authenticating users when they sign in to a workstation? a. Domain controllers b. Trees c. OUs d. ForestsTask 1: Demonstrate how to install some user and system applications such as firefox, and Dolphin file manager) is user applications and (nmap, and conky) as administrator applications. Task 2: Install, configure Samba service and demonstrate how to connect to your server from remote computer. Task 3: Install, configure Web Server and demonstrate how to browse a simple website hosted in your server. You may deploy a simple website (or web application) – from the Internet, in your server. Task 4: Install, configure FTP Server and demonstrate how to browse files hosted in your server.You have been hired as a consultant for a new company with 35 users. You have determined they should use Windows Server 2019 with Windows 10 clients. One of the servers will provide centralized authentication and use Group Policy. Which of the following is a crucial question that you must answer before you can install these features on this server? a. What file sharing protocol should be used? b. What domain name should you use? c. What folders need to be shared? d. What CPU are the client computers using
- Question p .You have been called in to consult for a company that is running 15 Windows 10 computer, two Linux computers, and three Mac OS X computers. Your boss wants all of these computers to be able to share files. What file sharing protocol do you recommend and why? Should you configure this network as a peer-to-peer network or as a client/server network? Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this lineWhat must you do to transform your computer into a DNS server? (Choose all thatapply.)a. Create zone files.b. Create resource records for DNS lookups.c. Create NIS maps.d. Run the name daemon (named).31. If you are accessing Internet through a proxy server at your campus, in which of these scenarioswill your requested file be likely provided by the proxy server instead of the origin web server?(Select ALL that apply)a. The file was recently requested by you and now you are requesting the same file againb. The file was recently requested by you at your home and now you are requesting the samefile againc. The file was recently requested by a client on the same Local Area Network as you areand now you are requesting the same filed. The file was recently requested by a client in the USA and now you are requesting thesame file 32. Which of the following statements about Selective Repeat are TRUE? (Select ALL that apply)a. It discards a corrupt packet and buffers all subsequent packetsb. It is simpler to implement than Go-Back-Nc. It does not require a buffer at the receiverd. It needs a separate timer for each packet to keep track of their timeout values
- Where could information be acquired from a browser which is opened in the 'private' mode? O a. Internet Cache and Temporary files O b. Live memory O c. It is impossible to gather any information if a browser is opened in the 'private' mode O d. Browsing history Oe. CookiesWhich of the following are not part of connectivity reports? VM that connects to billing database. CPU Usage Ports accessible through a firewall. User logins.82. Which of the following includes the benefit of the Networking? a. File Sharing b. Easier access to Resources c. Easier Backups d. All of the Above
- Which of the following is not applicable for File Server? a. The clients use Microsoft edge to access the web pages b. The server also runs an email server. c. The clients send requests to servers' software. d. The client network devices have file accessWhich of the following best illustrates the Network Layer of the Open Systems Interconnection (OSI) Reference Model? Question 10 options: The network interface card on Chantelle's computer has failed. When she replaces it with a new one, her computer will acquire a new Media Access Control (MAC) address. Gerald is setting up a small home/office network for a friend. The network is both wired and wireless and he is configuring IPv4 addressing for each device. A copper wire segment of the telephone system in Maria's apartment has failed, requiring a technician from the phone company to come and replace it. Aditya has decided to run his gaming computer on a wired connection, so he turns off the Wi-Fi connection on that computer and plugs in an Ethernet cable.1.Create a new document called portmapping.txt in Ubuntu’s home directory and answer the following questions: 1.Add the following port information services: POP3, IMAP, SMTP, DNS, DHCP, NTP, LDAP, and BGP 2.An end-user is experiencing issues with connecting to testout.com. Everytime the user enters testout.com in their browser it takes them to blackboard.com. Run the command the will help troubleshoot the issue? Once you have the information from the command how would you verify? 3. Another Sys Admin oversaw deploying the LAMP stack for a new website. The components consist of Apache2 and MySQL. After deploying the website and notifying users of availability there has been a lot of support tickets for inaccessibility of the website. 400/404 Errors are appearing ‘Website unreachable’. How would you troubleshoot the error? Run the commands that would show you details on why the website may be unreachable (verify each component

