Which of the following is not applicable for File Server? O a. The clients use Microsoft edge to access the web pages O b. The server also runs an email server. O c. The clients send requests to servers' software. O d. The client network devices have file access.
Which of the following is not applicable for File Server? O a. The clients use Microsoft edge to access the web pages O b. The server also runs an email server. O c. The clients send requests to servers' software. O d. The client network devices have file access.
Chapter6: Linux Server Deployment
Section: Chapter Questions
Problem 15RQ
Related questions
Question
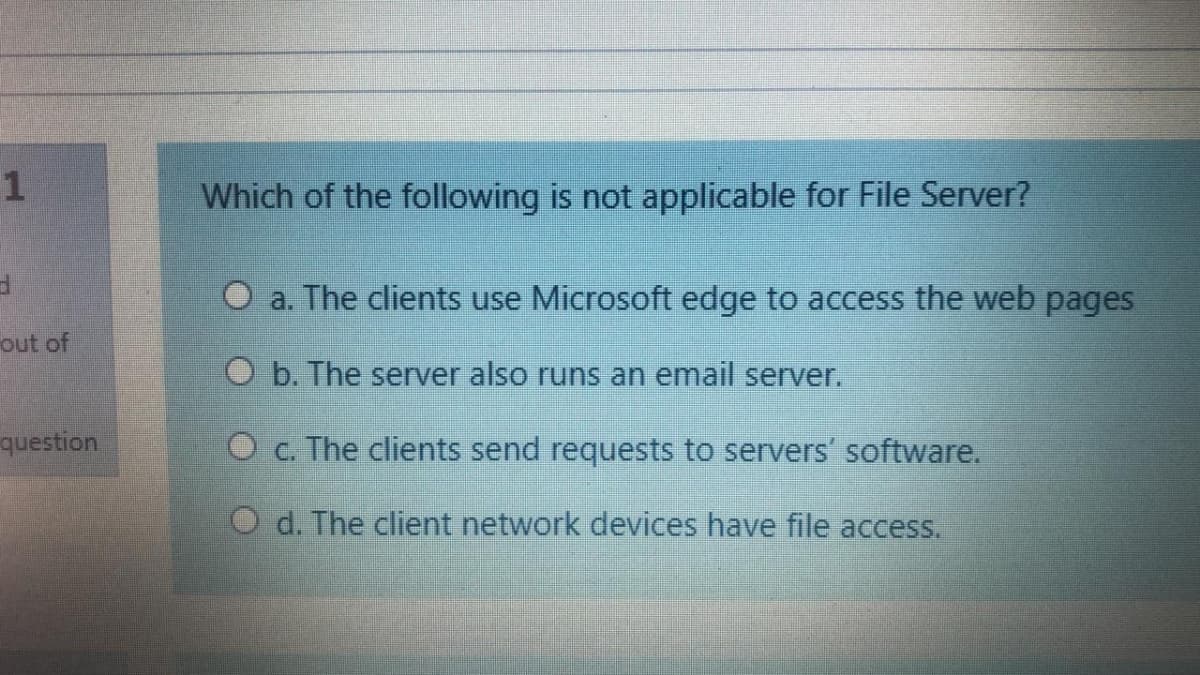
Transcribed Image Text:Which of the following is not applicable for File Server?
O a. The clients use Microsoft edge to access the web pages
out of
O b. The server also runs an email server.
question
O c. The clients send requests to servers' software.
O d. The client network devices have file access.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,