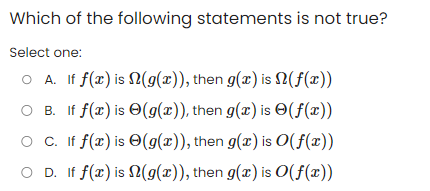
Which of the following statements is not true? Select one: O A. If f(x) is O B. If f(x) is OC. If f(x) is OD. If f(x) is (g(x)), then g(x) is (f(x)) (g(x)), then g(x) is (f(x)) (g(x)), then g(x) is O(f(x)) (g(x)), then g(x) is O(f(x))
Q: Could you please provide us your own words to define the notion of a challenge-and-response…
A: Answer: Introduction A challenge-response authentication system (CRAS), also known as a two-step…
Q: Objective: To be able to create a script file of matrix addition, matrix multiplication and Matrix…
A: 1. Input the number of rows and columns for the first and second matrices.2. Input the elements of…
Q: The economies and businesses that depend on globalization and information technology today may find…
A: Information on the potential risks that globalization and information technology may pose to…
Q: If you had a list of every component that makes up the kernel of a typical operating system, how…
A: The kernel of a typical operating system is responsible for managing the computer's resources and…
Q: what is the use of profiler decorator?
A: We have to write about the use of a profiler decorator. Decorator: In Python, a decorator is a…
Q: The One-Lane Bridge. Cars coming from the north and the south arrive at a one- lane bridge. Cars…
A: let us see the answer:- Introduction:- (a) Global Invariant: At any point in time, there can only be…
Q: Provide an example of a hypothetical situation requiring the management of logins. Develop a range…
A: Provide an illustration of a hypothetical login management scenario. List several distinct…
Q: Examples may be used to define a real-time operating system. What distinguishes this operating…
A: In this question we have to understand real time operating system with an example. What…
Q: The following concepts for operating system microkernel architecture may be summed up: What…
A: The microkernel operating system is an alternative to the conventional kernel-based method, which is…
Q: Could you please provide us your own words to define the notion of a challenge-and-response…
A: What is an authentication: Authentication is the process of verifying the identity of a user or…
Q: What are the primary distinctions between operating systems that support real-time and those that do…
A: Introduction: In this section, we are asked to describe what the primary distinctions are between…
Q: Computer science and technology How would you define "software"?
A: In this question we need to define the term software.
Q: How far has technology evolved in the last several decades, and what are some of the many sorts of…
A: The level of creativity brought about by technology: If new ideas are not implemented, the world has…
Q: Think about the potential uses and advantages of technology in your own l
A: Introduction: Technology has become an integral part of our lives, and it has transformed the way we…
Q: What is the underlying idea of Sequential Quadratic Programming, how is it applied, and where is it…
A: Introduction: Sequential Quadratic Programming (SQP) is a numerical optimization technique that is…
Q: Please describe, in your own words, what happened as a direct consequence of the previously…
A: A data violation is a cyber attack that involves illegal access to and disclosure of sensitive,…
Q: Question 4# Read the following algorithm: Algorithm for converting a fraction a into binary with p…
A: Solution: Given, Method: Initialise: j = 1, b1, b2,...,bp = 0 Loop: if j=p+ 1 stop. x = 2x If j…
Q: Answer the given question with a proper explanation and step-by-step solution. In C# Write and…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: Let's discuss the social and ethical repercussions of using and misusing information technology.
A: The following are examples of potential social and ethical repercussions of utilizing and…
Q: Explain the steps involved in a thorough software structure examination, and provide concrete…
A: Discuss software structure review using examples. In the early phases of the Software Development…
Q: How may cloud computing help your company? Is using the cloud secure? What are the dangers and…
A: Q How may cloud computing help your company? Cloud computing can help a company in a number of…
Q: Provide examples of the goals that are meant to be attained at each phase of the traditional system…
A: Here is your solution -
Q: It's essential to recognize four project components that will support the use of software…
A: Introduction: there are four aspects of a project that make it more likely that software engineering…
Q: There are numerous distinct models that may be used in software development, and each model may be…
A: Answer is
Q: You should keep track of the technology that has become crucial in your life. Think about the…
A: Almost every aspect of life now depends on technology. Technology is used by humans so often that…
Q: When someone uses the phrase "multimedia software," what does it truly mean?
A: Multimedia: It is the visual representation created by combining animation, graphics, video, still…
Q: I need help fixing my function for bool DelOddCopEven(Node*& headPtr). When I run my code it pass…
A: Below is the complete solution with explanation in detail for the given question about fixing the…
Q: 4.16 Atomic Broadcast. Assume one producer process and n consumer processes share a buffer. The…
A: The problem involves a single producer process and n consumer processes sharing a buffer. The…
Q: Provide a brief description of the stakeholders involved in the system's development and give two…
A: Given: Describe the stakeholders involved in the construction of a system and provide two examples.…
Q: ons for the requirement of continuous event simulation are
A: Answer:- Four justifications of the critical nature of continuous event simulation: Risk-free…
Q: With the computing power available in today's computers, this is certainly not out of the question.…
A: Computers have been significant since their inception, but they are now ubiquitous; as a consequence…
Q: Since technology advances at such a fast pace, ongoing adaptability is essential. Find and describe…
A: Applications of AI are vast, from customer service and marketing to healthcare and finance. Recent…
Q: Think about the potential uses and advantages of technology in your own life, as well as how it can…
A: Given: How can you use technology to improve yourself, your community, your relationships with…
Q: 3) Disassmble the following code with gcc compiler using -01 optimisation. Comment on the…
A: Here's the disassembled code with -O1 optimization: set_row: movq %rdx, %rax leaq…
Q: w how many bits belong to the host portion of the address ii.show the last usable host address in t
A: i. Converting the IP address and subnet mask to binary notation: IP address: 192.168.200.10 =…
Q: For which of the following is the set S equal to {(a, b)|a, b nonnegative integers }? Select one: O…
A: The solution is given below for the above given question:
Q: Define a function called exact change that takes the total change amount in cents and calculates the…
A: The above question is solved using python.
Q: When it comes to using computers and other forms of technology, what are some of the benefits of…
A: The answer to the question is given below:
Q: Make a list of the advantages and disadvantages of the TCP protocol using this information.
A: The TCP protocol is a connection-oriented transport layer protocol that serves to provide end-to-end…
Q: Write 10x9x8x7 in the form nPr A.10P5 B.10P6 C.10P7 D.10P4
A: What is Computer: A computer is a digital electronic machine that can be programmed to automatically…
Q: 1. Build a systems requirement checklist for a mobile application that keeps track of the food you…
A: Systems Requirement Checklist for a Mobile Application: Output: Display daily caloric intake based…
Q: A password system uses exact 8-character of alphanumeric. To be a secure password system, any…
A: Assuming that the password is chosen randomly from all possible combinations of 8 characters that…
Q: After completing this course, you will have a much better grasp of cloud computing, social…
A: Answer: Introduction Completing a course in cloud computing and related subjects can provide…
Q: To make telephone numbers easier to remember, some companies use letters to represent their…
A: In this question we have to Implement a Java program for the telephone number easier to remember…
Q: This article explains interrupt latency and context switching time.
A: We'll go over the idea of interrupt latency and how it relates to context: When a process or event…
Q: hat specifically do you have in mind as the outcome of the authentication process when you speak…
A: The primary goal of the authentication process is to verify the identity of a user or system, to…
Q: Which of our goals could become a reality if we seek help from authentication? In this part, we'll…
A: Explanation Authentication can play a crucial role in achieving various goals, especially those…
Q: When someone uses the phrase "multimedia software," what does it truly mean?
A: Multimedia It's a kind of visual representation that combines moving visuals, still photos, sound,…
Q: We suggest raising Flynn's taxonomy by one degree. What distinguishes computers at this level from…
A: Using Flynn's taxonomy, computer architectures are grouped according to how many simultaneous…
Q: Examine the degree to which technological advancements are making moral vacations available and the…
A: The Ethical Difficulties Posed by Information Technology Changing from one dominant set of…
Step by step
Solved in 2 steps

- Which of the following statements below is self-contradiction? a. [(X→Y) ∧ X]→Yb. [(~X→Y) ∧ (~X ∧ ~Y)]→Yc. X → (X ∨ Y)d. X ∧ (~X ∧ Y) 28Given: If A AND B, then C. Given: The if-then statement's reverse is also correct. If A is True, B is True, what is C? Forward and reverse / Forward and reverse Not True or False False TrueGiven: If A AND B, then C. Given: The if-then statement's reverse isalso correct. If A is True, B is True, what is C? Forward and reverse / Forward and reverse False Not True or False True i think a true but i dont want to guess what do you think?
- Given: If A AND B, then C. Given: The if-then statement's reverse isalso correct. If A is True, B is True, what is C? Forward and reverse / Forward and reverse False True Not True or FalseIf the statements p and q are both true while statement r is false. which of the following has a false truth value?* a. If r then (p or q). b. Not (r and (not p or q)). c. (p or r) if and only if not q. d. If not (r and q) then p.Which of the following statements can be right: (1). If x = O(n4), y = O(n2), then x/y = O(n2). (2). If x = Θ(n4), y = Θ(n2), then x/y = Θ(n2). Only (1) is right. Only (2) is right. Both (1) and (2) are right. (D). Neither (1) nor (2) is right
- Given: If A AND B, then C. Given: The if-then statement's reverse is also correct. If A is True, B is True, what is C? A. Not True or False B. Forward and reverse/Forward and reverse C. False D. TrueAssign the sum of x and y to w, and increment x by 1 with ++. Use only one statement and ensure that original value of x is used in statement.A= 1011 ,, B= 1010 Q: Apply the three equations and write a simple comment ————————— Please can you check my answer, and correct it for me if it’s wrong
- Which of the following statements is true and which is false: a. C++ is same as c=c+2. b. The arithmentic operators * and / has the same priority. O a is false and b is true O a and b are false O a is true and b is false a and b are trueWhich of the following best characterizes the statements: A) If n is an odd integer, then n2 + 4n + 1 is an even integer B) If n is an integer that is evenly divisible by 3, then (n + 2)2 + 2n is an even integer 1.Only A is true 2.Only B is true 3.Both A and B are true 4.Both A and B are falseTranslate the statement into equation: When three is multiplied by one less than a number x, the result is 10 less than 5 times the number x.



