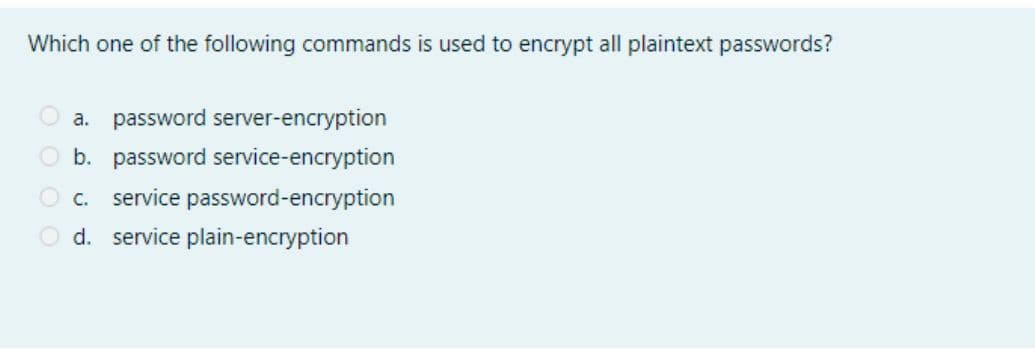
Which one of the following commands is used to encrypt all plaintext passwords? a. password server-encryption O b. password service-encryption O c. service password-encryption O d. service plain-encryption
Q: Which of the following is NOT a functionality that encryption algorithms can provide? Lütfen birini…
A: Answer : - Option (E) is correct . i,e. None of the above is correct option . Explaination :- A…
Q: Which of the following core requirement for the Reference Monitor (RM) is NOT true: O a.…
A: The Reference Monitor system is a secure, always used and fully testable module which controls all…
Q: True or False?
A: Given statement is true.
Q: Which of the following assertions is false: There are two keys used for encryption and decryption in…
A: Start: One key was used for encryption and another for decryption in public key cryptography.Two…
Q: Which one of the following mathematical notation represents the symmetric key decryption process? Oa…
A: Symmetric key decryption consists of a shared key between the sender and the receiver. Before the…
Q: Your colleague sent to you a message which is encrypted using a Playfair cipher, with key…
A: Playfair cipher is a symmetric encryption technique which is also known as playfair square. Steps to…
Q: Which of the following operations replaces plaintext characters with different ciphertext…
A: 1) Substitution cipher is a method of cryptography which converts standard plaintext into…
Q: 1. Which of the following public key cryptosystem application can be used by RSA? O a. Key exchange…
A: RSA: It is a public key cryptosystem used for secure data transmission. It is asymmetric…
Q: 5. Which of the following application is not one of the public key encryption categories? a. Digital…
A: Cryptography: Cryptography is the process of securing a message or information by encrypting it…
Q: which of the following ciphers is more secure O a. DES cipher O b. 2DES O C. double Affine cipher O…
A: In cryptography, security is most important things otherwise data will no longer safe.
Q: Which of these sentences are TRUE (select all that apply). NOTE: MAC is Message Authentication Code…
A: Message Authentication Code(MAC) A message authentication code in cryptography is a short piece of…
Q: Which of the following are a requirement for a secure One-Time Pad? Lütfen birini seçin: O A. The…
A: Requirements for the one time pad will be: The key must be truly random. The key must be at least as…
Q: Which of the following modes of Symmetric Key Block Ciphers is relatively less secure compared to…
A: 1.electronics code book is not more secure in symmetric key block cipher compare to other In…
Q: Which of the following security features is put into place to ensure correct authorization?…
A: Authentication: The authentication process identified the user who wants to access the network…
Q: Which encryption algorithm is used in SecurityPlus Lab 12 when creating the TrueCrypt volume?…
A: TrueCrypt supports different ciphers like - AES, Serpent, Twofish etc. and then different…
Q: A user enters a logon name and a password to gain network access. Choose the best description to…
A: Multi-factor Authentication (MFA) is an authentication method that requires the user to provide two…
Q: 5. Which of the following application is not one of the public key encryption categories? a. Digital…
A: Applications of public key encryption: ✓Encryption /decryption: The sender encrypts a message with…
Q: True or False? The following set of commands configure SSH to accept a username of cisco with a…
A: The following set of commands configures SSH to accept a username of cisco with a password cisco…
Q: Based on your understanding which of the following statements describes the verbose failure messages…
A: The design always depends on providing security to the user. So the design fault include using a…
Q: gr33n@pple
A: passwords is considered as the best among the suggested password for a user named: Khalid Ali? a.…
Q: key combination the receiver should apply to break the encrypted message for authentication in…
A: key combination the receiver should apply to break the encrypted message for authentication in…
Q: In which of the following modes, the command "ip address 10.10.10.10 255.0.0.0" can be executed? O…
A: In Interface mode the command ip address 10.10.10.10 255.0.0.0 can be executed. so the correct…
Q: and read it?
A: Symmetric key cryptography is used to encrypt individual files which can be accessed by ones who…
Q: Which of the following is the most important principle that ensures secured use of a public key…
A: The most important principle that ensures secured use of a public key algorithm
Q: Which of below should NEVER be used for sending passwords or other sensitive information Select one:…
A: Everyone can see the information provided from a form using the GET method, as all variable names…
Q: 4. What is the cipher command used to encrypt? a. Files but not directories b. Directories but not…
A: Your answer is given below with an explanation.
Q: Which of the following cipher uses two keys to encrypt data? a) substitution cipher b)…
A: The keys used in Encryption are of two types and are as follows: Public Key Private Key
Q: Which of the following passwords meets the password requirements? Select one: O a. @#$)*&^% O b. A…
A: A password is a collection of guidelines meant to improve computer security by persuading users to…
Q: In which of these attack scenarios is the attacker most powerful? Ciphertext only attacks Known…
A: Please find the answer below ;
Q: For your online PayPal account, you must create a password. Which of these passwords is the LEAST…
A: Least secure password
Q: Which of the following passwords is the most secure? 87654321 changeme p63lmhZ passwOrd
A: Please find the solution below:
Q: Which encryption benchmark ensures data is not modified after it’s transmitted and before it’s…
A: Answer 2. Integrity is the right Option Explaination: Data integrity guarantees that the data…
Q: With which command can I get awk to output the home directories of the top 20 users, their login…
A: overview: A command is a precise instruction from a user to the operating system or an application…
Q: Which of the following malware aims to encrypt all the data on the machine and ask a victim to…
A: Encryption is technique to encode data using some key.
Q: Which of the following symmetric key encryption ciphers provides the strongest protections O DES AES…
A: Given:
Q: Which of the following encryption method uses the same key to encrypt and decrypt the data? O Data…
A: Given we know that encryption method uses the same key to encrypt and decrypt the data…
Q: Which of the following true regarding OTP? O a. It is a Poly-alphabetic cryptosystem O b. It is an…
A: answer is given in step2.
Q: In which of the following authentication methods the user needs to enter a registered username and…
A: Username/Password Authentication Method : Every time you've signed up for a website, you've likely…
Q: The passwords in the given output are encrypted. Which command have been used to encrypt all…
A: Option 1-service password-encryption command to encrypt all passwords in the config file to prevent…
Q: What is the correct command to encrypt plain text passwords? O a. Ping O b. show running-config O c.…
A: The answer is given in step 2.
Q: Which of the following operations do not achieve non-repudiation? a. Encryption using hybrid…
A: MAC do not achieve the non-repudiation. option d is the correct answer.
Q: What is the definition of a reverse shell? When an attacker receives a shell prompt from a remote…
A: let's see the correct answer of the question
Q: Which of the following is not a characteristic of a weak password? O a. Using a common dictionary…
A: Lets see the solution.
Q: Which of the following mechanisms offers slowest performance compared to others? O a Digitally…
A: Since all the options are considered with message sending and receiving. All the processes take…
Step by step
Solved in 2 steps

- Which of the following operations do not achieve non-repudiation? a.Encryption using hybrid cryptosystems b.Digitally signing a message digest c.Digitally signing a complete message d.MACWhich of the following assertions is false: There are two keys used for encryption and decryption in public-key cryptography. O Unencrypted data is the same as plain text. None of the above choices ring true. The terms encryption and cipher text are not interchangeable.Which encryption benchmark ensures data is not modified after it’s transmitted and before it’s received? a. Confidentiality b. Integrity c. Availability d. Symmetric
- Which security mechanism(s) are provided in each of the following cases? A school demands student identification and a password to let students log into the school server. A school server disconnects a student if she is logged into the system for more than two hours. A professor refuses to send students their grades by e-mail unless they provide student identification they were preassigned by the professor. A bank requires the customer’s signature for a withdrawal.When sending a large file, which method uses less encryption operations, cypher block chaining or cypher feedback mode?And which one is much more effective?You are the administrator for your company network. You and a colleague are discussing the key archive store. The key archive stores which of the following information? Group of answer choices The public key and private key only The public key, private key, and supported cryptographic algorithms only The subject name, public key, private key, and supported cryptographic algorithms The public key only
- What is the output of the following command? Get-DnsServerTrustAnchor –name secure.practicelabs.com –computername PLABDC01 Updates the trust points created earlier on the PLABDC01 Creates a new trust point on the PLABDC01 Refreshes the trust point on all DNS servers Creates a new trust point on all DNS servers from PLABDC01MCQ: Which of the following is an example for user to host authentication? a. Encryption keys b. Digital certificate c. Username & Password d. Hash algorithmWhich encryption method encrypts individual files so that only the owner and other users who have been authorized can decrypt the file and read it?
- Which of the following statements about cookies is true? a. Cookies were originally intended to facilitate advertising on web. b. Cookies allow websites to off load the storage of information about visitors. c. Cookies always contain encrypted data d. Cookies are text files and never contain encrypted data. e. None of the above is true.a. Which of the following can be used for both encryption and digital signatures? 3DES AES RSA MD5 b. Digital Signatures provide which of the following? Confidentiality Authorization Integrity Authentication Availability c. The difference between a hash and a digital signature is: Hashes are used to verify message authenticity, digital signatures are used to verify message integrity. Hashes are used to verify message integrity and authenticity, digital signatures are used to verify message authenticity only. Hashes are used to verify the message integrity only, digital signatures are used to verify message authenticity and message integrity. There is no functional difference. d.Which asymmetric algorithm is used for establishing a shared key?A.Elliptic CurveB. PGPC. Diffie-HellmanD. RSA e.What is used to create a message digest that will be attached to data at rest or in transit? Asymmetric algorithm Symmetric algorithm Encryption Hashing Non-repudiation Authentication…Which of the following is a good practice ? A. Give full permission for remote transferringB. Grant read only permissionC. Grant limited permission to specified accountD. Give both read and write permission but not execute.

