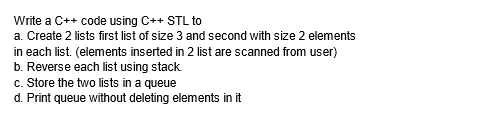
Write a C++ code using C++ STL to a. Create 2 lists first list of size 3 and second with size 2 elements in each list. (elements inserted in 2 list are scanned from user) b. Reverse each list using stack. c. Store the two lists in a queue d. Print queue without deleting elements in it
Q: Problem. Create a truth table for the expression pv ( q vr), by filling in the indicated columns one…
A: Truth Table : A truth table shows how the truth or falsity of a compound statement depends on the…
Q: I need help in this question of Data Structure and Algorithm Is n2=o(n2)? I need some detailed…
A: Answer of n2=o(n2) is:
Q: What would occur if the referential integrity of a database were What are the most common mistakes…
A: Referential integrity: Referential integrity is the relationship between tables. Each table in a…
Q: Describe many ways for acquiring meeting control. What justification is there for this?
A: The acquisition strategy is a complete, integrated plan that covers the business, technical, product…
Q: How can I prevent being a victim of phishing?
A: 1. Stay Up-to-Date on Phishing Techniques - New phishing scams are always being created. If you…
Q: Finally, what is the ultimate purpose of artificial intelligence? Provide a list of the major topics…
A: Early academics created algorithms: That emulated people's step-by-step problem-solving and…
Q: Program Requirements: Write a Java program that will 1. Ask the user to type in a sentence, using a…
A: Java : Sun Microsystems initially introduced Java, a programming language and computing platform, in…
Q: In that case, could you offer an illustration of what you mean by operating environment?
A: It is important to note that the first version of Microsoft Windows, Windows 1.0, was not a whole…
Q: How important is it to be acquainted with the compiler?
A: Introduction: Compilers convert programmes from one language to another.Compilers create machine…
Q: Is it necessary to emphasize the relevance of data backup and cloud storage in corporate…
A: Information is vital; after all, it describes everything from individual identities to financial…
Q: How does MVC fit into the broader web application framework? Which of the following are advantages…
A: An architectural design pattern called Model-View-Controller (MVC) divides an application into three…
Q: How does MVC fit into the broader web application framework? Which of the following are advantages…
A: Introduction Model, View, and Controller: Model, View, and Controller (MVC) is an architectural…
Q: What is the Search for Extraterrestrial Intelligence (SETI) and how can the distributed computing…
A: Definition: Search for Extraterrestrial Intelligence, or SETI, is what it stands for. SETI is…
Q: What roles do the leader and the follower play in the process of leadership?
A: Answer : Good leaders make us feel safe because we trust good leaders and believe that they would…
Q: What is Unpacked BCD Format?
A: Lets see the solution.
Q: ion does a foreign key play in preserving database integrity? What evidence do you hav
A: Introduction: A foreign key relationship declares that an index in one table is related to an index…
Q: Define XLAT instruction used in 8086.
A: In 8086, 8 general purpose registers exist such as - AX (AH, AL) - Accumulator BX (BH, BL) - Used…
Q: What does it mean to "debug" an application?
A: Explanation:- //Debugging: Debugging is process of tracking and eliminating an existent or…
Q: Operating system abstraction has several benefits. What are the most significant ones?
A: Solution: An software facilitates communication between the user and therefore the hardware.The…
Q: As a result of the brilliance of modern computers, Describe how computers have grown so prevalent in…
A: Computers are potent for several reasons. They work with astonishing speed, consistency, and…
Q: What does it mean to "debug" an application?
A: The above question that is what does mean by debug an application is answered below step.
Q: 3. (A5)16+ (10111)2 = (xxxx)g 4. (753) + (3AF)16 (10110)2 = (xxxx) 10 --- -
A: Octal, Hexadecimal to Binary Use below table to convert octal to binary. Hexadecimal Octal…
Q: The microkernel of the operating system is based on what philosophy? Has this technique supplanted…
A: Introduction: The microkernel operating system reduces the kernel to process communication and IO…
Q: Because modern computers are so powerful, this is the case. Exist reasonable explanations for the…
A: Computers have been powerful since their introduction, but they are now ubiquitous. We can find…
Q: How exactly does virtualization function within the context of cloud computing?
A: Introduction: A variety of services are delivered via the Internet through cloud computing as…
Q: What governance challenges must be addressed throughout the transition from on-premises servers to…
A: Introduction: Governance challenges: Identification and authentication: The types of users and, as a…
Q: This is the result of today's very powerful computers. Why has the use of computers in education…
A: Answer is
Q: What governance factors should be taken into account while shifting from on-premises servers to an…
A: Answer: The infrastructure of the charity information is maintained by the charity administration…
Q: Exists a substantial drawback to a two-tier architecture? How can a client–server design with many…
A: Two-tier architecture: It is based in client server architecture. Direct communication takes place…
Q: What governance factors should be taken into account while shifting from on-premises servers to an…
A: IaaS stands for Infrastructure as a service and is a type of cloud computing. It is this service in…
Q: What governance factors should be taken into account while shifting from on-premises servers to an…
A: Introduction: The cause the board utilizes the sending model as an infrastructure as a software…
Q: What governance factors should be considered while shifting from on-premises servers to an laaS…
A: What governance considerations should be made when shifting from on-premise servers to an IaaS…
Q: What fundamental idea governs the development of the microkernel of an operating system? What is the…
A: Microkernel OS is predicated on lowering the kernel to only essential process communication and IO…
Q: Flynn's taxonomy
A: Michael J. Flynn proposed Flynn's taxonomy, a classification of computer architectures, in 1966 and…
Q: What is the Search for Extraterrestrial Intelligence (SETI) and how can the distributed computing…
A: Introduction distributed Computing: Multiple software system elements running on several machines…
Q: Define XLAT instruction used in 8086.
A: XLAT − Used to translate a byte in AL using a table in the memory.
Q: Which part of a client/server architecture is responsible for storage?
A: The client-server architecture, architecture of a computer network in which many clients request and…
Q: What software category do compilers and editors belong under?
A: System software is required to manage computer resources and facilitate application program…
Q: es to the adopti
A: Solution - In the given question, we have to specify the obstacles to the adoption of IoT.
Q: Can those with mental or physical disabilities benefit from the internet? What new technologies are…
A: Internet has something or other for everyone in this world when talked about in terms of resources.
Q: How do user applications and system services interact inside a microkernel architecture? Please use…
A: Introduction: In a microkernel design, how do system services and user applications communicate with…
Q: What are the benefits of providing and configuring servers automatically? Which of the following are…
A: given - What benefits do servers that are provisioned and configured automatically offer? What…
Q: Is HTML in any way distinctive?
A: The answer of the question is given below
Q: nemy Assassin's Creed, armed with many guns. Your goal is to destroy as s as possible. The battle…
A: the java code is an given below :
Q: What is the degree of a vertex having 2 edges, where one of the edges is a loop? 04 O 3 O 2 01 X
A: Degree is the number of edges related to a graph
Q: Describe the fundamental methods involved in segmentation. What distinguishes it from paging? What…
A: Segments are used to split a procedure. Segments are the parts of a programme that are broken down…
Q: What governance challenges must be addressed throughout the transition from on-premises servers to…
A: The answer to the question is given below:
Q: Problem. Create a truth table for the expression (p ^ -q) v (-q ^ -r), by filling in the indicated…
A: A truth table is a table or chart used to illustrate and determine the truth value of propositions…
Q: How do you feel about the similarities between network sniffing and wiretapping? What makes them…
A: Sniffing refers to the process of capturing data from a network and continuing to monitor that data…
Q: What are the pros and downsides of global connection in cloud computing?
A: The question has been answered in step2
Step by step
Solved in 3 steps with 4 images

- Write a program in c++ and make sure it works, that reads a list of students (first names only) from a file. It is possible for the names to be in unsorted order in the file but they have to be placed in sorted order within the linked list.The program should use a doubly linked list.Each node in the doubly linked list should have the student’s name, a pointer to the next student, and a pointer to the previous student. Here is a sample visual. The head points to the beginning of the list. The tail points to the end of the list. When inserting consider all the following conditions:if(!head){ //no other nodes}else if (strcmp(data, head->name)<0){ //smaller than head}else if (strcmp(data, tail->name)>0){ //larger than tail}else{ //somewhere in the middle} When deleting a student consider all the following conditions:student may be at the head, the tail or in the middleBelow, you will find a sample of what the file looks like. Notice the names are in…Write a program where 2 linked lists have ben create and now the main task is to merge the linked lists and display the merged list. For example, merging lists {1, 2, 3} and {7, 13, 1} should yield {1, 7, 2, 13, 3, 1} Note: the above mentioned task is to be performed using doubly linked list and in C++Question : Write a program to remove duplicates from a doubly linked list. e.g (1,2,3,4,5,2) (you will remove the 2nd duplicate) and then swap two data items in a doubly linked list. swap address of node 2 with node 4.
- write a c++ code that will do the adding a node to a doubly-linked list in the three cases (insert a node at the beginning-middle-end). A separate function is required for each case.python programming Write a function that will insert a new value into the middle of a Linked List. INPUT: The head of the Linked List, the value to insert OUTPUT: Nothing is output RETURNED: Nothing is returnedQuestion : Write a c++ program which creates a Linked List having maximum sum out of two Sorted Linked Lists. Use this : LinkedList finalMaxSumList(LinkedList List1, LinkedList List2); For eg: You have two sorted linked lists, create a linked list that contains data with maximum sum. The resulting list with maximum sum will contain nodes with data from both input sorted lists. While creating the resulting list with maximum sum, we may switch to the other input list only at the point of intersection (which mean the two nodes with the same value in the lists). You are only allowed to use O(1) extra space. Note: You have to returned Linked List which contain finalMaxSumList and you are not allowed to change in data type and prototype of the Function. Input:List1 = 1->3->30->90->120->240->511List2 = 0->3->12->32->90->125->240->249 Returned LinkedList: Following is resulting linked list out of two sorted listsResultingList =…
- Task:implement a function that reverses a list of elements by pushing them onto a stack in one order and writing them back to the list in reversed order P.S:Answer must be in pythonIn C++, how do I read a file with numbers Such as 1,2 3,4 5,6 and place it into a linked list with x,y values Without stringstream or sstream and vectorsfor C++ how do you cosntruct a stack using a linked list?
- Write a program in c++ to remove duplication if exists in the linked list. Write 2 separate functions to perform search and other to perform the duplication removal. Note: the above mentioned task is to be performed using singly linked list and in c++In SML write a function posLL to count a number of positive values in an int list list. One function only. posLL[nil,[~2,3], [5], [~7,11]] > 3Which of the following statement is not true about the doubly linked list? A. We can traverse in both the directions. B. It requires extra space C. Implementation of doubly linked list is easier than the singly linked list D. It stores the addresses of the next and the previous node

