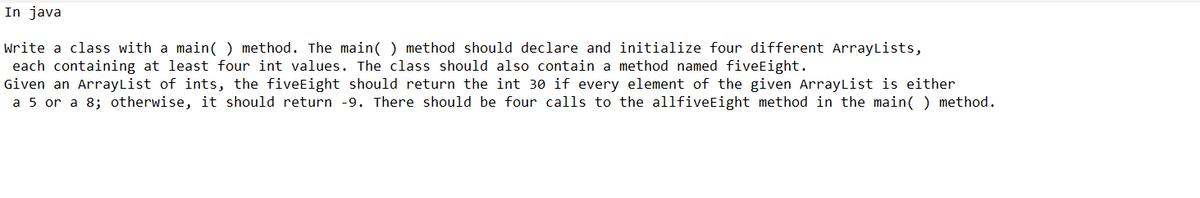
Write a class with a main() method. The main() method should declare and initialize four different ArrayLists, each containing at least four int values. The class should also contain a method named fiveEight. Given an ArrayList of ints, the fiveEight should return the int 30 if every element of the given ArrayList is either. a 5 or a 8; otherwise, it should return -9. There should be four calls to the allfiveEight method in the main() method.
Q: How can you discern between the numerous authentication alternatives and their merits and downsides…
A: This issue requires us to comprehend the various authentication techniques available for security…
Q: How would you describe a challenge-and-response authentication system such that we may better…
A: Challenge and response authentication is a set of protocols which are used to protect the services…
Q: What actions should be performed if there is a breach in a company's security?
A: In this question we have to discuss what all actions should be performed if there is a breach in…
Q: What are the most important differences between starting a data modelling project from scratch and…
A: Data Modelling Endeavours: Through the entities, connections, and data that are necessary for the…
Q: Explain how the capacity analysis reacts when a high number of processes are operating concurrently.
A: Image with Transcription Provide an explanation of how the capacity analysis responds when a large…
Q: What function do access restrictions play in the larger scheme of things in the twenty-first…
A: Hello student This is the detailed and specific theory which will be in next step Please do like
Q: As you can see in the next sentences, data modelling is of the highest importance.
A: Data Modelling: Data modelling is the technique of utilising words and symbols to describe the data…
Q: Explaining a challenge–response authentication system in your own terms is possible. What benefits…
A: System of authentication: Password-based authentication is often used in client-server systems.…
Q: "Why are authorisation lists so susceptible to unauthorised modification that they must be encrypted…
A: The answer is given in the below step
Q: Write a program using genetic algorithm for roulette wheel selection. in python
A: Question: Python code for Roulette wheel selection using genetic algorithm.
Q: Why is it of the utmost importance to guarantee that there are no data input mistakes while…
A: Data entry reevaluating has turned into an important part in smoothing out deals and showcasing data…
Q: Identify the relational keys for each table. List each relational key in a separate line. Identify…
A: Hello student
Q: What does the phrase "file handling" refer to, and why are its services necessary in the first…
A: "File Handling": File handling is the process of saving data in a C programmer in the form of…
Q: How precisely might mobile UI toolkits aid designers and developers trying to enhance the user…
A: Introduction: Adobe Photoshop is among the top 10 mobile app UI design tools. Microsoft Windows and…
Q: What do you believe occurs when you press a key on the keyboard while a software is writing a file…
A: A hardware interrupt is triggered whenever a user presses or releases a key on the keyboard, which…
Q: I am unsure of what you mean when you discuss the purposes of authentication. Determine what each…
A: The question has been answered in step2
Q: What is the conclusion on the File Integrity Monitoring Program?
A: FIM supports the security and maintenance of websites, servers, databases, and online applications.…
Q: Why do people see the Internet as the apex of information and communication technology? Is it…
A: Introduction: Communication technology is the use of technology to transport messages (information)…
Q: What is the issue statement, and what is the programme that checks file integrity used for…
A: statement: Today's world places a lot of importance on the data found in files. If this information…
Q: What role does contemporary technology play in the process of successful communication, and how is…
A: Introduction: The ability to communicate is the single most important factor in human life. A…
Q: In the case of a data security breach, what are the organization's procedures governing the sharing…
A: Answer: A data breach is a cyber attack in which sensitive, confidential or otherwise protected data…
Q: As you can see in the next sentences, data modelling is of the highest importance.
A: Data modeling is a method used to characterize and coordinate your business processes. It permits…
Q: Consider a situation that necessitates the handling of login credentials and make intelligent…
A: Passwords should be hashed To store sensitive user information, such as the user's password,…
Q: What degree of security do different authentication techniques provide?
A: Introduction Authentication is the process of figuring out if someone or something is honest or not.…
Q: What are the advantages and disadvantages of contemporary communication technologies? Explain this…
A: Introduction: Communication technology has the advantage of facilitating effective communication.…
Q: Explain how technological advancements have made it simpler for workers to interact inside…
A: Introduction: Internal communication refers to an organization's deliberate efforts to inform and…
Q: Please include examples for each of the three fundamental file management approaches.
A: Give examples for each of the three main file management strategies. Ordinary files, usually called…
Q: Describe and demonstrate the three fundamental file management techniques.
A: Introduction: File management is the process of overseeing a system that effectively manages…
Q: In the case of a data security breach, what are the organization's procedures governing the sharing…
A: statement: An outline is a thorough plan of action or comprehensive schedule of events. Every time…
Q: Regarding effective communication, what role does modern technology play, and how is it utilised?
A: Let's see how modern technology played an important role in communication.
Q: What role does contemporary technology play in the process of successful communication, and how is…
A: Answer: You can see the average elementary age child with their head buried in their smartphone,…
Q: What are the benefits and possible disadvantages of caching disc write operations?
A: In this question we need to explain advantages and disadvantages of caching disc write operations.
Q: What type of reaction does the capacity analysis get when many processes are occurring…
A: Introduction: The surface area of your disc, where your data is stored, is split into circular…
Q: What is the precise purpose of the canvas element in HTML5?
A: Canvas element in HTML 5 are used to draw graphics via scripting. They can be used to draw…
Q: Write the appropriate algorithm for each mathematical problem 1. X = (a+b) - c 2. Get the…
A: In this question we need to write algorithm for the mathematical problems. Algorithm:- An algorithm…
Q: How does information technology contribute to the day-to-day operations of organisations, especially…
A: The answer for the above mentioned question is given in the below steps for your reference.
Q: How does information technology influence the communication procedures of modern businesses?
A: The Acronym Stands For "Information Technology: Information technology, abbreviated as IT, refers to…
Q: What are the aims and goals of the File Integrity Monitoring programme
A: Answer:
Q: What can we do with the aid of authentication? Here, we will examine the pros and downsides of…
A: You've probably heard about the advantages of two-factor authentication. Requiring more than just a…
Q: What is the precise purpose of the canvas element in HTML5?
A: <canvas> element in HTML 5 is used to draw graphics on a web page.
Q: What criteria are necessary for monitoring the integrity of the files?
A: The FIM program identifies, analyses, and reports anomalous file modifications. Monitoring file…
Q: Walk me through the three most prevalent methods for organising my files and demonstrate how they…
A: Synchronization is the synchronisation of events in order for a system to work in harmony. The…
Q: The usage of digital communication has overtaken the use of both face-to-face and voice-to-voice…
A: Every company undertakes a specific project and develops it based on the criteria. The project…
Q: Conduct research on user authentication as a form of access control and compose a report on your…
A: Start: Security mechanisms are used to enforce the layers of assurance between a system's security…
Q: Create a fictitious situation involving login management and explain it in full. Determine different…
A: Introduction: Next, we'll explore popular authentication methods and show how to utilise them for…
Q: Programming Language: C++ A) Create a program which shows dynamic memory allocation of an array. B)…
A: A dynamic array's memory is allocated at runtime thus it's size can be modified, that's how it is…
Q: CS-related domains Are there two sorts of Internet services given by apps? Uniqueness separates…
A: The following is a list of the some of the most popular internet services: Communication Services…
Q: ubject Topic: Logic Formulation using Flowchart and Pseudocode Problem: Looping Create a program…
A: Introduction: Step 1: Start Step 2: declare variables int b, n; Step 3: assign initial values to…
Q: How many distinct methods exist to access files? What are the pros and downsides of using them?
A: Introduction: Basic file access method: File organization is simply arranging all of an employee's…
Q: What are the most common errors that might occur throughout the data modelling process?
A: Data modeling Data modeling is only the method for making or making the portrayal in a picturesque…
Step by step
Solved in 3 steps with 1 images

- A supermarket wants to reward its best customer of each day, showing the customer’s name on a screen in the supermarket. For that purpose, the store keeps an ArrayList.Create a class customer having id, name, gender, and bill provide appropriate getters/setters and constructors also provide toString method.In the Store class, make an ArrayList of customers, store name, and address implement methods public void addSale(Customer c) that will add customers to the arraylist.public void RemoveCustomer(int id);public void UpdateCustomerRecord(int Id);public displayAll();public String nameOfBestCustomer() to record the sale and return the name of the customer with the largest sale. public ArrayList nameOfBestCustomers(int topN) so that it displays the top customers, that is, the topN customers with the largest sales, where topN is a value that the user of the program supplies. Write a program that prompts following menu and ============================================…Given a base Plant class and a derived Flower class, complete main() to create an ArrayList called myGarden. The ArrayList should be able to store objects that belong to the Plant class or the Flower class. Create a method called printArrayList(), that uses the printInfo() methods defined in the respective classes and prints each element in myGarden. The program should read plants or flowers from input (ending with -1), add each Plant or Flower to the myGarden ArrayList, and output each element in myGarden using the printInfo() method. Ex. If the input is: plant Spirea 10 flower Hydrangea 30 false lilac flower Rose 6 false white plant Mint 4 -1 the output is: Plant 1 Information: Plant name: Spirea Cost: 10 Plant 2 Information: Plant name: Hydrangea Cost: 30 Annual: false Color of flowers: lilac Plant 3 Information: Plant name: Rose Cost: 6 Annual: false Color of flowers: white Plant 4 Information: Plant name: Mint Cost: 4 import java.util.Scanner;import java.util.ArrayList;import…Write a main method, in which you should have an Arralylist of students, in which you should include every student. You should have a PhD student named Joe Smith. In addition, you should create an Undergraduate student object for each of your team members (setting their names). If you’re only one person doing the assignment, then you should just create one undergraduate object. For each undergraduate student, you should add add two courses (COIS 2240 and COIS 1020). Loop over the arraylist of students, print their names, if the student is an undergraduate student, print their courses.
- In java A supermarket wants to reward its best customer of each day, showing the customer’s name on a screen in the supermarket. For that purpose, the store keeps an ArrayList.Create a class customer having id, name, gender, and bill provide appropriate getters/setters and constructors also provide toString method.In the Store class, make an ArrayList of customers, store name, and address implement methods public void addSale(Customer c) that will add customers to the arraylist.public void RemoveCustomer(int id);public void UpdateCustomerRecord(int Id);public displayAll();public String nameOfBestCustomer() to record the sale and return the name of the customer with the largest sale. public ArrayList nameOfBestCustomers(int topN) so that it displays the top customers, that is, the topN customers with the largest sales, where topN is a value that the user of the program supplies. Write a program that prompts following menu and ============================================…Need help writing the method: getWaitlistedIDs() – returns an array of type int[], namely the ids of students in the waitlist. public int[] getWaitlistedIDs() { // insert solution here and modify the return statement return null; } For context public class Course { public String code; public int capacity; public SLinkedList<Student>[] studentTable; public int size; public SLinkedList<Student> waitlist; public Course(String code) { this.code = code; this.studentTable = new SLinkedList[10]; this.size = 0; this.waitlist = new SLinkedList<Student>(); this.capacity = 10; } public Course(String code, int capacity) { this.code = code; this.studentTable = new SLinkedList[capacity]; this.size = 0; this.waitlist = new SLinkedList<>(); this.capacity = capacity; }In java Write a method public static ArrayList<Integer> append(ArrayList<Integer> a, ArrayList<Integer> b) that appends one array list after another. Ex: a = 1 2 3 4 5, b = 6 7 8 9 10 then append returns 1 2 3 4 5 6 7 8 9 10
- The printRightToLeft method is intended to print the elements in the ArrayList words in reverse order. For example, if words contains ["jelly bean", "jukebox", "jewelry"], the method should produce the following output. jewelry jukebox jelly bean The method is shown below. public static void printRightToLeft(ArrayList<String> words) { if (words.size() > 0) { System.out.println(words.get(words.size() - 1)); /* missing code */ } } Which of the following can be used to replace /* missing code */ so that the printRightToLeft method works as intended? words.remove(0); printRightToLeft(words); words.remove(0); printRightToLeft(words); words.remove(words.size()); printRightToLeft(words); words.remove(words.size()); printRightToLeft(words); words.remove(words.size() - 1); printRightToLeft(words); words.remove(words.size() - 1); printRightToLeft(words); printRightToLeft(words); words.remove(0); printRightToLeft(words); words.remove(0);…In java, Write a method void popMult(int k) for the ArrayBoundedStack class which will pop k items from this. Throw a StackUnderflowException and don't pop anything if there are fewer than k items on this. This is a method of the ArrayBoundedStack class. DO NOT USE ANY OTHER METHODS OF THE ARRAYBOUNDEDSTACK CLASS.java Create a static method that: is called repeatAll returns ArrayList of Booleans takes in a single parameter - an ArrayList of Booleans This method should modify its ArrayList parameter by repeating its ArrayList values. For example, if the parameter is (true, false, false) The modified ArrayList should be (true, false, false, true, false, false) public static void main(String[] args) { Scanner in = new Scanner(System.in); int size = in.nextInt(); ArrayList<Boolean> list = new ArrayList<>(); for(int i=0; i < size; i++) { list.add(in.nextBoolean()); } System.out.println(repeatAll(list)); } }
- JAVA, PLEASE THE PROGRAM SHOULD USE THE INITIAL ARRAYLIST AND TO EDIT IT NOT TO CREATE A NEW ONE Create a class called OurArrayList and implement the following methods. Do NOT createany auxiliary memory.Include a main method and test all your methods with appropriate examples.a. Write a method called scaleByK() that takes an ArrayList of integers as aparameter and replaces every integer of value K with K copies of itself. Forexample, if the list stores the values (4, 1 , 2, 0 ,3) before the method is called, itshould store the values (4, 4, 4, 4, 1, 2, 2, 3, 3, 3) after the method finishesexecuting. Zeroes and negative numbers should be removed from the list by thismethodComplete the Course class by implementing the printRoster() method, which outputs a list of all students enrolled in a course and also the total number of students in the course. Given classes: Class Course represents a course, which contains an ArrayList of Student objects as a course roster. (Type your code in here) Class Student represents a classroom student, which has three fields: first name, last name, and GPA. (Hint: toString() returns a String representation of the Student object.) Ex: If the following students and their GPA values are added to a course: Henry Cabot with 3.5 GPABrenda Stern with 2.0 GPAJane Flynn with 3.9 GPALynda Robison with 3.2 GPA then the program output is: Henry Cabot (GPA: 3.5) Brenda Stern (GPA: 2.0) Jane Flynn (GPA: 3.9) Lynda Robison (GPA: 3.2) Students: 4 course.java import java.util.ArrayList; // Class representing a studentpublic class Course { private ArrayList<Student> roster; // Collection of Student objects public Course() {…To demonstrate working with ArrayLists, we will be working with four source files: a Dessert class, two classes that extend Dessert called IceCream and Cake, and a TestDessert class. The TestDessert class contains a main() method that declares an ArrayList to hold Dessert objects. This ArrayList is referenced by the variable named "list". Examine TestDessert's main() method and notice the four comments. You are to implement code that accomplishes the tasks described in each step. For step 1, you are to populate the ArrayList with 10 IceCream and Cake objects. These objects should be inserted into the ArrayList at random. This means each run of the program should produce an ArrayList with different proportions of IceCream and Cake objects. After this operation, the ArrayList should contain 10 total objects (IceCream and Cake objects). Display the ArrayList after the operation. For step 2, if the first and last dessert in the ArrayList are different (one is IceCream and the other is…



