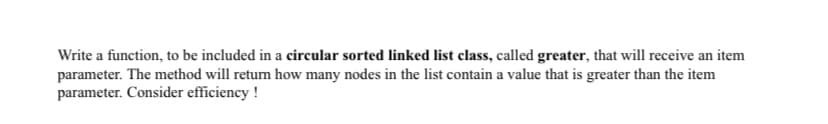
Write a function, to be included in a circular sorted linked list class, called greater, that will receive an item parameter. The method will return how many nodes in the list contain a value that is greater than the item parameter. Consider efficiency !
Q: What if a procedure didn't include the RET instruction?
A: Introduction: The RET command stands for return. This instruction appears at the conclusion of proc...
Q: what is the code that print the co2 level in Commonwealth? co2_sensors = [{"loc_id":1,"cities":{"Qu...
A: I give the code in Python along with output and code screenshot
Q: this code should be in python: ...
A: Here is the detailed explanation of the program
Q: Check each line of code and try to figure out what the errors are. Modify the code to let it run suc...
A: We are given 3 python small codes and we have to find out the errors in the statements. I will first...
Q: 3. Identify and explain the Restricted Airspace
A: Given: Recognize and describe Restricted Airspace.
Q: make a python program (please see images for instructions and sample run)
A: Python code for lotto draw game.
Q: 10. Given a list of unsorted integers, find the pair of elements that have the smallest absolute dif...
A: Coded using Python 3.
Q: Identify two widely utilised system development methodologies. Each method's pros and cons are detai...
A: Lets see what is system development methodologies: A system development methodologies are the framew...
Q: MD5 offers strong collision resistance: DTrue False
A: Q1) Answer:False MD5 is not collision-resistant. As such, MD5 is not suitable for applications lik...
Q: ProPublica Al system is related to 3. a. Recruitment b. Promotions Judiciary d. Tourism C.
A: Propublica AI At every level of the criminal justice system, they are utilised to inform choices on...
Q: ving a large amount of bandwidth? Could you please elaborate on what you mean?
A: given - What are the advantages and cons of having a large amount of bandwidth? Could you please ela...
Q: Question 11 reads a line of input, including leading and embedded spaces, and stores it in a string ...
A: As per company guidelines we are suppose to answer only 1 question. Kindly re-post other question...
Q: What are the fundamental distinctions between Dijkstra's algorithm-based link state routing principl...
A: Intro Routing - In this process the received IP packet by the router will go through the routing t...
Q: To show information about a yum package group we would type _____ and the package name. Select an a...
A: Find the answer with reason given as below :
Q: Visit the websites of three big technological companies (Microsoft, Oracle, and Cisco), as well as t...
A: Introduction : Websites dedicated to the most up-to-date information about security. Microsoft devel...
Q: In the operation of hard real-time systems, what is the most critical component to consider?
A: Find the answer given as below :
Q: Suppose your friend, Alice is trying to find all the odd numbers that are between X and Y. You want ...
A: Step-1: Start Step-2: Start a for loop i = 92 to 1092 Step-3: Check if every i is not divisible by 2...
Q: What exactly is "clocking," and why do you need to configure it?
A: It is all about defining when to read the signals and when to write. Specifying the timing of reads...
Q: Describe three (3) of these element with respect to creating, digital processing and storage in a co...
A: Introduction: In the development of computer applications, digital processing and storage are essent...
Q: This code runs only if there is an exception. except try finally els When checking valu...
A: Note: Since the question is multipart we are advised to do only first three questions. Kindly post o...
Q: Implement the following c++ operations on the singly linked List Data structure: 1) Maximum 2) Minim...
A: Your C++ program is given below as you required with an output.
Q: plications with ACL highlighting advantages and disa
A: A comparison of these applications with ACL highlighting advantages and disadvantages?
Q: Determine the many ways in which conventional email is vulnerable to denial-of-service assaults. Mak...
A: Given: Determine the many ways in which traditional email can be subjected to denial-of-service atta...
Q: What are threats? Give some
A: given - . What are threats? Give some examples.
Q: The way requests for devices are managed can be succinctly described.
A: Numerous I/O devices can be linked to a computer system. However, at any given time, only a few I/O ...
Q: Define the terms listed below. I The datapath (ii) Processor timer (iii) Clocking in many phases.
A: Given: We have to define the given term: 1) the datapath 2) processor timer 3) Clocking in many pha...
Q: write a java code to print the following grid **
A: I give the code in Java along with output and code screenshots.
Q: Exactly what is the goal of cybersecurity?
A: According to the question cyber security always work on some application or the tool to make secure ...
Q: l
A: given - Generate a corresponding IJVM assembly language program for the following Java code fragment...
Q: Define the terms Rollback and Roll forward.
A: Introduction the question is about Defining the terms Rollback and Roll forward. and here is the sol...
Q: Define/Explain the topic fully and identify the role that particular term, concept, or analysis play...
A: Part(1) A virtual private network (VPN) extends a private network across a public network, allowing...
Q: Describe scenarios in which linked lists will be useful.
A: Given: Describe scenarios in which linked lists will be useful.
Q: 1) Givern the truth table: abcd F (a) 1 no. Use K-Map to simplify the expression in SOP form and imp...
A: Here is the detailed explanation of the solution
Q: Before installing software from source you need to do what? Select an answer: Install all license ke...
A: All the options are important for installing a software.
Q: with a link at the top of it that when clicked will jump all the way to the bottom of the page. At t...
A: the code is an given below :
Q: Given the following Python code below: co2_sensors = [{"loc_id":1,"cities":{"Quezon City": {"Common...
A: Please find the answer below :
Q: Access to the internet and information technologies has widened the social class divide. Explain the...
A: Introduction : The digital gap refers to the discrepancy in access to information technology among d...
Q: What is the name of the LGPO backup?
A: Introduction: LGPO: LGPO stands for local group policy object. This is one of the tools that use a...
Q: Which data structure is necessary to convert infix notation to prefix notation?
A: Introduction Which data structure is required to convert the infix to prefix notation?
Q: Write a python program to print the larger value that is in the range 10..20 inclusive, or print 0 i...
A: The program written in Python and it takes three integer user input and check that it is in inclusiv...
Q: Following: (i) Find the product of two numbers. (ii) Find the remainder when one number is divided b...
A: As per our guidelines, we are supposed to answer only 1st three parts. Kindly repost the remaining q...
Q: 1. Briefly explain sign magnitude and two's complement representation. 2. What is the sign of 100100...
A: I'm providing the all answers of above query. I hope this will meet your requirements.
Q: Is virtual memory the same as RAM in terms of speed?
A: As far as speed is concerned, is virtual memory the same as RAM?
Q: Given this implementation of insertion sort as seen in the photo below, What is the worst-case time...
A: Find the answer with explanation given as below :
Q: How does information flow in a three-tier design?
A: Introduction: The three-tier architecture of the application is a well-structured and ordered client...
Q: Why do we talk about Predictive, Diagnostic, and Prescriptive in relation to Machine Learning?
A: Introduction: Machine learning (ML) is a subset of artificial intelligence (AI) that enables softwar...
Q: Try to input these to Python app and submit the result: from fractions import Fraction print(Fractio...
A: The python code provide the output r as, -64/1325602/5-6433713753386423/90071992547409921337719/5000...
Q: Use Java multi-threading to calculate the expression: (n!) / 2. 1. Create a method called factorial ...
A: Introduction
Q: H.W:- Find the deteminant for the following matrices: 2 3 5. B =0 -2 answer: [B| = -20 -21
A: Here is the detailed explanation of the solution
Q: Show how to convert a regular expression directly into a context-free grammar.
A: This method is not easy to grasp and may take some time to master. We'll teach you how to make regul...
Step by step
Solved in 2 steps with 1 images

- Implement a nested class DoubleNode for creating doubly-linked lists, with each node containing a reference to the item before and following it in the list (empty if no such item exists). Then, for the following jobs, implement static methods: insert at the beginning, insert at the end, remove from the beginning, remove from the end, insert before a given node, insert after a given node, and remove a given node.in java Write a method for the Linked Based List class which returns the largest item in the list. If the list is empty return null. Assume that class T is Comparable.DO NOT USE ANY OTHER METHODS OF THE LINKED BASED LIST CLASS. What is the worst case and best case complexity of the code in the previous problem? Explain your answer.Implements clone which duplicates a list. Pay attention, because if there are sublists, they must be duplicated as well. Understand the implementation of the following function, which recursively displays the ids of each node in a list def show_ids(M, level=0): k = M.first_node while k is not None: print(" "*2*level, id(k)) if (str(k.value.__class__.__name__) == str(M.__class__.__name__)): show_ids(k.value, level+1) k = k.next W=L2(Node(10, Node(L2(Node(14, Node(15, Node(L2(Node(16, Node(17))))))), Node(20, Node(30)))) )show_ids(W) Develop your solution as follows: - First copy the nodes of the current list (self) - Create a new list with the copied nodes - Loop through the nodes of the new list checking the value field - If this field is also a list (use isinstance as in the show_ids function) then it calls clone on that list and substitutes the value. Complete the code: def L4(*args,**kwargs): class L4_class(L):…
- Build doubly-linked lists using a nested class called DoubleNode, where each node includes a reference to the item before it and the item after it in the list (null if there is no such item). Then put in place static methods for inserting at the start, inserting at the end, removing from the start, removing from the finish, inserting before a given node, inserting after a given node, and removing a given node.Implement a nested class DoubleNode for building doubly-linked lists, whereeach node contains a reference to the item preceding it and the item following it in thelist (null if there is no such item). Then implement static methods for the followingtasks: insert at the beginning, insert at the end, remove from the beginning, removefrom the end, insert before a given node, insert after a given node, and remove a givennode.Implement a self-organizing list by building a single linked list of nodes and frequently and randomly retrieving data from the list. Show what happens to the list when the count, move to front, and transpose techniques are applied to the same set of frequently retrieved items.
- Suppose that you have a singly linked list with five nodes and with head reference. Then the statement head = head.next will remove the first node of the linked list? a) true b) falseImplement program to adds methods to search a linked list for a data item with aspecified key value, and to remove an item with a specified key value. These, along with insertion at the start of the list, are the same operations carried out by the LinkList Workshop applet. Write The complete linkList2.cpp program.Implement a class “LinkedList” which has two private data members head: A pointer to the Node class length: length of the linked listImplement the following private method: 1. bool InsertHead(int data); // Use InsertAt FunctionInsert at the start of the linked list. Return true2. bool InsertEnd(int data); // Use InsertAt FunctionInsert at the end of the linked list. Return true3. bool RemoveAt(int index);Remove and delete the node at position “index”. Return true if successful, otherwise, false. this in c++
- Write a method replace to be included in the class KWLinkedList (for doubly linked list) that accepts two parameters, searchItem and repItem of type E. The method searches for searchItem in the doubly linked list, if found then replace it with repItem and return true. If the searchItem is not found in the doubly linked list, then insert repItem at the end of the linked list and return false. Assume that the list is not empty. You can use ListIterator and its methods to search the searchItem in the list and replace it with repItem if found. Do not call any method of class KWLinkedList to add a new node at the end of the list. Method Heading: public boolean replace(E searchItem, E repItem) Example: searchItem: 15 repItem: 17 List (before method call): 9 10 15 20 4 5 6 List (after method call) : 9 10 17 20 4 5 6Implement a method to remove a node in the middle of a singly linked list (i.e., any node except the first and last node, not necessarily the exact middle), given only access to that node.EXAMPLElnput:the node c from the linked list a->b->c->d->e->fResult: nothing is returned, but the new linked list looks like a ->b->d->e->fExecute a program that will split a circularly linked list P with n nodes intotwo circularly linked lists P1, P2 with the first n/2 and the last n – n/2 nodes ofthe list P in them.

