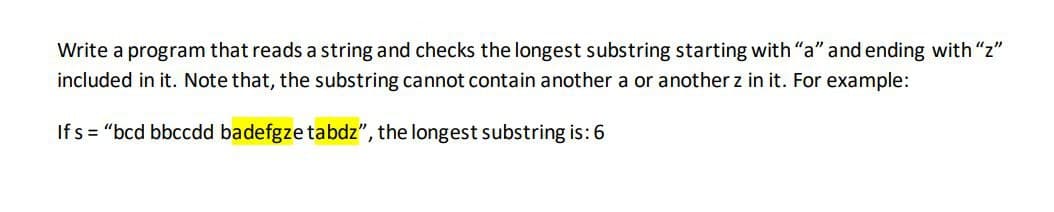
Write a program that reads a string and checks the longest substring starting with "a" and ending with "z" included in it. Note that, the substring cannot contain another a or another z in it. For example: Ifs="bcd bbccdd badefgze tabdz", the longest substring is: 6
Q: To add a menu to a menu bar, use _______. Question 18 options: menuBar.add(menu)…
A: The menu bar which refers to the part of a browser or application window that are usually present…
Q: To create a JavaFx label with the specified text, use __________. Question 11 options: new…
A: Label is included with the JavaFX package. Label is a non-editable text control used to display a…
Q: When I use the above code it is giving me a syntax error for the line rows +=1
A: Given num_rows and num_cols, print a list of all seats in a theater. Rows are numbered, columns…
Q: What strategies are available to improve data privacy?
A: The struggle to protect our personal information is a difficult one. To make matters worse, there…
Q: Analyze the following code. import javafx.application.Application; import javafx.event.ActionEvent;…
A: I have analysed given code and as per the analysis correct option is given below:-
Q: Social networking platforms are popular (such as Facebook and Twitter). Determine why people choose…
A: Individuals prefer digital social networks due the following reasons:1. Introverts find it easy to…
Q: earn to d
A: The provided C code is done as per your requirements. "Screenshot of the program code" for better…
Q: To place a node in the left region of a BorderPane p, use ___________. Question 4 options:…
A: To place a node in the left region of a BorderPane p, use p.setLeft(node); p.setLeft(node) it…
Q: To handle the key pressed event on a pane p, register the handler with p using ______. Question…
A: Given that, there is a pane p and to handle the key pressed event on a pane p, we need to register…
Q: Explain why deploying software as a service can reduce the IT support costs for a company. What…
A: Explain why deploying software as a service can reduce the IT support costs for a company. What…
Q: What alternatives are there to enhance data privacy?
A: The techniques for data privacy will be covered in the section that follows: Data is incredibly…
Q: Describe the user support processes, such as user education and help desks.
A: The question is describe the user support processes, such as user education and help desks.
Q: Compile the PLC program Compile the PLC program using Ladder logic on Codesys or Logix Pro for the…
A: A Programmable logic controller which refers to the PLC. It is the programmable controllers in the…
Q: Q. Give an Example of Italic H1 heading HTML?
A: Given Question is asking for a html code to show H1 heading in italic. Code for this question is in…
Q: A software manager is in charge of the development of a safety-critical software system, which is…
A: The answer is written in step 2.
Q: Use the Kruskal's algorithm to find the MST of the graph shown below. Show all steps. (73 2 e 1 -10-…
A: Defined the MST of the given graph using Kruskal's algorithm
Q: The purpose of this assignment is to learn to develop multi-process programs. You are expected to…
A: Assignment 3 in C: Unix shell with redirects and pipes The purpose of this assignment is to learn to…
Q: A common unit of measure for failure rates of electronic components is the Failure unIT (FIT),…
A: ANSWER:-
Q: What are events in jQuery and JavaScript? Could you provide some instances of events? What does the…
A: Events in JavaScript and jQuery, how to handle such events, and their significance in interactive…
Q: If the following statement were used in a Java program, it would cause something to be written to…
A: The given section of code is a snip of java programming. The first statement is a…
Q: Why is the insertion sort faster than the sorted group? Indicate only one cause.
A: Insertion sort is a method of sorting that is more effective on fewer elements than it is on bigger…
Q: (a) Calculate the software size in terms of use case points. Please show your works and state your…
A: Use Case Point is a technique of software estimation to find the size of software by some method for…
Q: Keep track of any databases that could include your personal information. How often and for how long…
A: The question has been answered in step2
Q: What options are available to enhance data privacy?
A: Given: What other approaches are available for enhancing the confidentiality of data? In the next…
Q: What is machine language?
A: Machine language is also know as macnine code it includes the binary digits (0s and 1s),…
Q: Which of the studied data structures in this course would be the most appropriate choice for the…
A: The answer of the question is given below:
Q: fere a few examples of sites with targeted content. Why do they fall within ocused-content portal…
A: Summary An online business gate can replicate the look and sense of your business and give you…
Q: This section offers a broad perspective on the development of computing throughout history.
A: It is possible to trace the evolution: of computers all the way back to the creation of the abacus,…
Q: node.getStylesheets.add("style.css");
A: the question of answer is option D - node.getStylesheets.add("style.css");
Q: Please list the three C++ classes that may be used to build output streams.
A: In the given question there are three output stream classes in c++. They are ostream, ofstream and…
Q: of incorrectly transmitting a single bit. Let w = 1010001 which is transmitted over the channel. Let…
A: The answer is
Q: Compare the roles played by programmers, systems analysts, information systems managers, the CIO,…
A: The question is to compare the roles played by programmers, systems analysts, information systems…
Q: Determine and describe two of the operating system effects that virtualization is expected to have.
A: Given: Virtualisation on the operating systems Based on the operating system Virtualisation on the…
Q: Consider the communication network in figure 1. E 2 B F 4 Figura 1: Graph representing a data…
A:
Q: Compile a list of social media's mental health risks. Is there a risk of Internet addiction?
A: During the past decade, online social networking has caused profound changes in the way people…
Q: List reasons why your engagement as an information system user is vital during the system…
A: Introduction: To relate the concepts of user engagement and change, provide four reasons why your…
Q: For the 8-bit word 00111001, the check bits stored with it would be 0111. Suppose when the word is…
A: Introduction So in this given question, we are asked What is the data word that was read from…
Q: How are data read from a magnetic disk?
A:
Q: What options are available to enhance data privacy?
A: Data privacy is also called information privacy, is the aspect of information technology that deals…
Q: Suppose an 8-bit data word stored in memory is 11000010. Using the Hamming algorithm, determine what…
A: Check bit 8(C8) calculated by values in bit numbers: 12, 11, 10 and 9 Check bit 4 (C4) calculated…
Q: Give an example of a situation in which multicast addresses might be beneficial.
A: The Internet Protocol supports the ability to have one device send a message to a set of recipients.…
Q: Delete 88 from the B-tree of order 5 of Figure 11-40. Show the resulting tree.
A: Accordion to the information given:- We have to Delete 88 from the B-tree of order 5
Q: 1. In each row, four items are given: function to which runtime is proportional, original input…
A: According to the information given:- We have to find out new runtime on the basis of instruction…
Q: 3. One can build a circuit which consists of a hierarchy of logic gates which take a series of 2"…
A: 3. AND GATE: Outputs a 1 if both bits are 1, outputs 0 otherwise. // C program implementing the…
Q: a. Find the number of bits for the main memory address. ANSWER: b. How many blocks are there in a…
A: Here in this question we have given Main memory capacity= 4GB Block size = 32 B Cache size = 64 kB.…
Q: What are events in jQuery and JavaScript? Could you provide some instances of events? What does the…
A: Events in JavaScript and jQuery, how to handle such events, and their significance in interactive…
Q: Describe the role that LSI chips typically play in a contemporary personal computer.
A: Personal Computer: A personal computer (PC) is a multifunctional a microcomputer that is…
Q: ribe what a "firewall" is in terms of network security and how network top
A: Introduction: Firewalls are important because they have a great impact on modern security techniques…
Q: Explain the differences between the internet, intranet, and extranet
A: Internet This is the global network of computers available to anybody who knows their Internet…
Q: If the four numbers 00, 01, 10, and 11 are coded as shown below, what is the Hamming Distance of…
A:
Step by step
Solved in 4 steps with 2 images

- Write a program that reads a character and a string (an entire line, which may include spaces or tabs), and outputs the number of times the character appears in the string. Hint: use getline(cin, mystring) to read the entire line including spaces. Use mystring.length() to know how many characters. But to avoid a glitch when getline gets an empty string following a cin, do the following sequence: cin >> mychar; /* get character. cin leaves the newline in the input buffer*/ cin.ignore(80,'\n'); /* remove newline from the buffer, which getline would see as empty line*/ cout << "Enter a string: "; //prompt for string getline(cin, mystring); Example program run (the user types only the word "Monday" and the letter "a"): Enter character to count: a Enter a string: Monday count = 1 Example program run: Enter character to count: a Enter a string: Today is Monday count = 2 Example program run: Enter character to count: b Enter a string: Today is Monday count = 0 #include…write a program that allows the input of a string from the user and prints the longest word in that string and its length. If there are multiple words with the same maximum length you must print the first one only.Write a program which reads string and rewrite it in alphabetical order. For example, the word STRING should be written as GINRST.
- Write a program that reads a text (string) and prints the letter that starts the most number ofwords in that stringWrite a program that reads in a string containing three words separated by commasand then outputs that string with each word in a different line.Write a program which takes a string from the user and replaces all occurrences of ‘b’ with ‘$’.
- Write a program that takes a string and swap the first character and the last character of that string.Write a program that gets a string containing a person’s first, middle, and last names, and then display their first, middle, and last initials. For example, if the user enters John William Smith the program should display J. W. S.write a program that inputs a string and checks if it is a palindrome. Use a functiion.****
- Write a program that takes a string and creates a new string made of first two characters and last two characters from the given stringWrite a program that accepts as input a sentence in which all of the words are run together but the first character of each word is uppercase. Convert the sentence to a string in which the words are separated by spaces and only the first word starts with an uppercase letter. For example the string “StopAndSmellTheRoses.” would be converted to “Stop and smell the roses.”Write a regular expression in python that checks if a string in python has a length of exactly seven letters and starts with two zeroes and contains at least 3 consecutive 1s

