Write a Python function that takes in three parameters - an adjacency matrix of a simple directed graph, a start node, and an end node; and returns "True" if there is a way to get from the start node to the end node using the provided edges.
Write a Python function that takes in three parameters - an adjacency matrix of a simple directed graph, a start node, and an end node; and returns "True" if there is a way to get from the start node to the end node using the provided edges.
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter5: Repetition Statements
Section5.5: A Closer Look: Loop Programming Techniques
Problem 12E: (Program) Write a program that tests the effectiveness of the rand() library function. Start by...
Related questions
Question
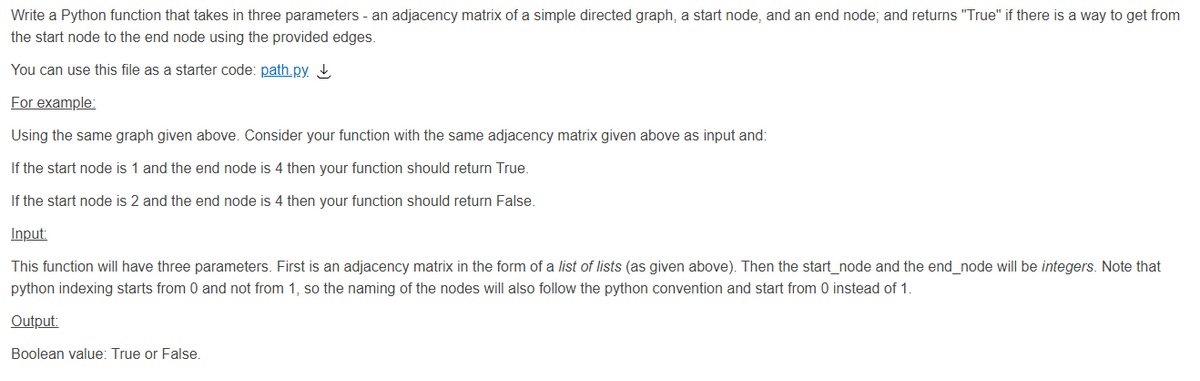
Transcribed Image Text:Write a Python function that takes in three parameters - an adjacency matrix of a simple directed graph, a start node, and an end node; and returns "True" if there is a way to get from
the start node to the end node using the provided edges.
You can use this file as a starter code: path.py ↓
For example:
Using the same graph given above. Consider your function with the same adjacency matrix given above as input and:
If the start node is 1 and the end node is 4 then your function should return True.
If the start node is 2 and the end node is 4 then your function should return False.
Input:
This function will have three parameters. First is an adjacency matrix in the form of a list of lists (as given above). Then the start_node and the end_node will be integers. Note that
python indexing starts from 0 and not from 1, so the naming of the nodes will also follow the python convention and start from 0 instead of 1.
Output:
Boolean value: True or False.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning