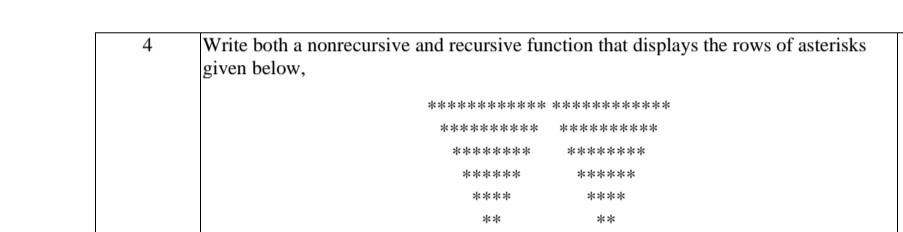
Write both a nonrecursive and recursive function that displays the rows of asterisks given below, **** **** 本**本**本 ******** ******** ****** ****** **** **** ** ** 寸
Q: Explain the purpose of templating. Additionally, the following code accepts an array and search item…
A: Introduction: A template is a blueprint or formula used to create a generic class or function in…
Q: Computer science What operating system components are always in memory
A: An operating system like the name suggests devices in the operation of the computer system i.e. it…
Q: Which of the following is the largest quantity? Select one: O a. The octal number 05272 O b. The…
A: Answer is (c). The Binary number 101010111111 Convert all the values into binary. (05272)8 =…
Q: The virtual what () member function returns defining a brief description of the error that occurred.…
A: C-string is a collection of character data type values terminated by a null('\0') character. The…
Q: A badly constructed web application for an online shopping site retains the price of each item as a…
A: According to the data, when constructing the web application of an e-commerce portal, confidential…
Q: QUESTION 5 Which of these is the definition for packages in Python? A. A set of main modules…
A: A python package is defined as a collection or folder of python modules. Modules which are related…
Q: Compare several data connection layer sliding window protocols?
A: GO-BACK-N 1. GO-BACK-n requires all retransmission of the succeeding frame along with the lost or…
Q: What will be the value of x after the following code is executed?
A: I have provided correct answer, C CODE, CODE SCREENSHOT with OUTPUT----------
Q: ng in the context a
A: Solution - In the given question, we have to tell about objective of prototyping in the context of…
Q: What three aspects are considered while making hardware purchases?
A: The Answer is in step-2.
Q: Because automation relies on knowledge information technology, what is the reason for this…
A: Introduction: Infrastructure refers to the facilities and services that a firm need. Electricity,…
Q: DHCP and APIPA are side by side. In what ways does merging these two methods make sense?
A: Introduction: The APIPA includes the configuration for looking for a DHCP server (in every five…
Q: Then how would you describe the constant emphasis on customers if that's the case?
A: Customers: Individuals and corporations that buy products and services from another company are…
Q: Why are thin clients preferred over desktop computers at a university computer lab, and how do they…
A: The above question is solved in step 2:-
Q: What are the fundamental concepts that underpin a wireless network?
A: Introduction: The data is transmitted between the source and destination devices using radio signals…
Q: Use the laws of Boolean algebra to simplify the following Boolean expressions : (a) yx[x+(xxy)] (b)…
A: Boolean algebra is an area of mathematics in which the variables' values are the truth values true…
Q: If your spreadsheet includes more than one theme, divide the columns into tables such that each…
A: Name of the spreadsheet for spreadsheet B: Headings for the COMPANY column: Officer Name, Officer…
Q: Consider the following (artificial) data set. Copy the code line by line without the > sign and run…
A:
Q: 8.10 Write the exact output.
A: A piece of code is given:
Q: What are some of the most recent technological breakthroughs in the field of information technology
A: Introduction: Some eg of Information Technology are safeguarding data and information, Building a…
Q: there anything in Facebook's policies that might have prevented the data breach
A: Answer :
Q: Provide a description of the second chance method for page replacement in the context of an LRU…
A: Algorithm: All bit reference values are set to False (Let it be the size of the max capacity of the…
Q: What are the key differences between a local-area network and a wide-area network in terms of…
A: This question explains the main distinctions between a local-area network and a wide-area network…
Q: What is the objective of prototyping in the context of software development?
A: Here, we will discuss the purpose and objectives of software engineering prototyping. The primary…
Q: My student claimed that the three fundamental page replacement algorithms (FIFO, LRU, and optimal)…
A: Page Replacement: Computers are designed with many levels of memory. As the memory's transmission…
Q: In Python 3, which functions are used to accept input from the user A. rawinput() B.…
A: The Answer is in step2
Q: What does the Ubuntu Server Operating System look like, and how does it compare to competing server…
A: Before comparing the difference between Ubuntu Server from other operating systems, let's show what…
Q: Find initial values of x and y that demonstrate that the following Hoare triples do not hold. 1) {{…
A: Answer is given below-
Q: What are the repercussions of making the wrong indexing decisions?
A: The term "poor indexing" refers to any SQL Server table configuration that has excessive,…
Q: Information technology What is the relevance of ethics in IT?
A: The significant ethical issues in data innovation are as per the following:
Q: Computer science What are SIM cards and SD cards, and why do mobile devices require them? Is it true…
A: Introduction: Computer science What are SIM cards and SD cards, and why do mobile devices require…
Q: QUESTION 2 What will be the output of the following Python code? A. error B. a b c d…
A: Python code to convert lower case to upper case
Q: What is the use of knowing how to operate a computer in the information age?
A: Answer: Computer literacy is essential because it presents extra work prospects, facilitates…
Q: Cloud security might be significantly affected by the data leak, but is this possible? Why should I…
A: Definition: Is it possible that a data breach might have a major impact on cloud security? What are…
Q: Explain briefly how you can analyze this DDoS assault using security engineering techniques…
A: How do you identify and analyze a DDoS attack? in-line examination of all packets and out-of-band…
Q: What is the property of the FIFO algorithm that you are referring to? (b) What is the name of the…
A: FIFO (FIRST IN FIRST OUT) ALGORITHM: In FIFO page replacement algorithm, operating system keeps…
Q: List and discuss the most common file properties and actions. (About the operating system)
A: File Information: It required a password to access the file. It reveals the ID of the person who…
Q: Explain how a file management system may provide access to many users to files for the purpose of…
A: GIVEN: Explain how a file management system may provide many users access to files for the purpose…
Q: Describe the information concealing principle as it applies to software design.
A: Introduction: Principles of information concealment in software design. -
Q: Make a C language code, that makes you write a sentence or paragraph and it tells you how many…
A: The code implementation in the C language is given in the steps below.
Q: Define a Turing Machine that accepts the following language: L = {w € {!,O}* | w = vw'v where v, w'…
A: The answer of this question is as follows:
Q: What are the hurdles that firms face when attempting to migrate to a cloud platform? Is there a…
A: Cloud computing platform: The 'cloud platform' is the environment that allows a software service or…
Q: What are the most effective perimeter and network protection approaches for protecting network…
A: Introduction: Firewalls are an essential part of any perimeter defence. Firewalls are made up of…
Q: Iterated and non-iterated queries, authoritative and root servers, and DNS records are all covered…
A: The Domain Name System (DNS) is known as "the phonebook" on the Internet. Domain names such as…
Q: Define a data file and provide FOUR (4) examples of a data file.
A: answer is
Q: Check to see if any penetration testing is taking place. Is data security a concern?
A: Penetration Testing: A penetration test, often called a pen test, is a legitimate simulated cyber…
Q: Do data breaches have the potential to have a significant effect on cloud security? Does anybody…
A: INITIATION: Unauthorized access to and disclosure of sensitive, confidential, or otherwise protected…
Q: Why did Cisco transition from a standalone access control system to an IP networked solution? " "
A: Internet Protocol (IP) is a form of protocol or type of rules which creates the base for routing the…
Q: Dialogue about iterative and non-iterative DNS requests, authoritative servers, root servers (if…
A: Domain Name Service The DNS, or domain name system, is the Internet's phone book. Humans typically…
Step by step
Solved in 2 steps with 2 images

- For function decToBinary, write the missing parts of the recursion case. This function should return a string that stores the binary equivalent for int variable num. Example: The binary equivalent of 13 may be found by repeatedly dividing 13 by 2. So, 13 in base 2 is represented by the string "1101". Examples: decToBinary(13) -> "1101" public String decToBinary (int num) { if (num < 2) return Integer.toString(num); else return <<Missing recursive call>> + <<Missing calculation>>;}Write a recursive function named reverseWithinBounds that has an argument that is an array of characters and two arguments that are bounds on array indices. The function should reverse the order of those entries in the array whose indices are between the two bounds (including the bounds). For example, if the array is: a[0] == 'A' a[1] == 'B' a[2] == 'C' a[3] == 'D' a[4] == 'E' and the bounds are 1 and 4, then after the function is run the array elements should be: a[0] == 'A' a[1] == 'E' a[2] == 'D' a[3] == 'C' a[4] == 'B' Embed the function in a program and test it. After you have fully debugged this function, define another function named reverseCstring that takes a single argument that is a C string and modifies the argument so that it is reversed. This function will include a call to the recursive definition you did for the first part of this project, and need not be recursive. Embed this second function in a program and test it.Write a recursive function named reverseWithinBounds that has an argument that is an array of characters and two arguments that are bounds on array indices. The function should reverse the order of those entries in the array whose indices are between the two bounds (including the bounds). For example, if the array is: a[0] == 'A' a[1] == 'B' a[2] == 'C' a[3] == 'D' a[4] == 'E' and the bounds are 1 and 4, then after the function is run the array elements should be: a[0] == 'A' a[1] == 'E' a[2] == 'D' a[3] == 'C' a[4] == 'B' Embed the function in a program and test it. After you have fully debugged this function, define another function named reverseCstring that takes a single argument that is a C string and modifies the argument so that it is reversed. This function will include a call to the recursive definition you did for the first part of this project, and need not be recursive. Embed this second function in a program and test it. Turn in only this final result (with output,…
- Write a recursive function named reverseWithinBounds that has an argument that is an array of characters and two arguments that are bounds on array indices. The function should reverse the order of those entries in the array whose indices are between the two bounds (including the bounds). For example, if the array is: a[0] == 'A' a[1] == 'B' a[2] == 'C' a[3] == 'D' a[4] == 'E' and the bounds are 1 and 4, then after the function is run the array elements should be: a[0] == 'A' a[1] == 'E' a[2] == 'D' a[3] == 'C' a[4] == 'B'write each of the functions LENGTH, WRITESTR, READSTR and CONCAT so that they operate iteratively without using recursion.Write a recursive function that, given a sequence of comparable values, returns the count of elements where the current element is less than the following ( next ) element in the given sequence. See the examples given below. def count_ordered ( seq ) : """ Input : A sequence of comparable elements Output : The number of elements that are less than the following element in the sequence Example : >>> count_ordered ( [ 1 , 2 , 3 , 4 , 5 , 6 ] ) 5 >>> count_ordered ( ( 1 , 12, 7.3 , -2,4 ) ) 2 >>> count_ordered ( 'Python' ) 2 >>> count_ordered ( [ 6 ] ) 0 >>> count_ordered ( [ ] ) 0 """ In the first example above , count_ordered ( [ 1,2,3,4,5,6 ] )the returned answer is 5 because for all the first 5 numbers the current number is less than the next number. In the second example above, count_ordered ( ( 1,12,7.3 , -2,4 ) )the…
- c++ Write a recursive function that, given two strings, returns whether the first string is asubsequence of the second. For example, given hac and cathartic, you should return true, but givenbat and table, you should return false.Below,enter code to complete implementation of a recursive function sum_all_integers(), which takes an input n and adds all intergers preceding it, up to n: add_all_integers(n):1. Write a recursive function that takes as a parameter a nonnegative integer and generates the following pattern of stars. If the nonnegative integer is 4, then the pattern generated is:********************Also, write a program that prompts the user to enter the number of lines in the pattern and uses the recursive function to generate the pattern. For example, specifying 4 as the number of lines generates the above pattern. 2. A palindrome is a string that reads the same both forward and backward. For example, the string "madam" is a palindrome. Write a program that uses a recursive function to check whether a string is a palindrome. Your program must contain a value-returning recursive function that returns true if the string is a palindrome and false otherwise. Do not use any global variables; use the appropriate parameter.
- A palindrome is a sentence that contains the same sequence of letters reading it either forwards or backwards. A classic example is '1\.ble was I, ereI saw Elba." Write a recursive function that detects whether a string is apalindrome. The basic idea is to check that the first and last letters of thestring are the same letter; if they are, then the entire string is a palindromeif everything between those letters is a palindrome.There are a couple of special cases to check for. If either the first orlast character of the string is not a letter, you can check to see if the restof the string is a palindrome with that character removed. Also, when youcompare letters, make sure that you do it in a case-insensitive way.Use your function in a program that prompts a user for a phrase andthen tells whether or not it is a palindrome. Here's another classic fortesting: '1\. man, a plan, a canal, Panama!"Question: First write a function mulByDigit :: Int -> BigInt -> BigInt which takes an integer digit and a big integer, and returns the big integer list which is the result of multiplying the big integer with the digit. You should get the following behavior: ghci> mulByDigit 9 [9,9,9,9] [8,9,9,9,1] Your implementation should not be recursive. Now, using mulByDigit, fill in the implementation of bigMul :: BigInt -> BigInt -> BigInt Again, you have to fill in implementations for f , base , args only. Once you are done, you should get the following behavior at the prompt: ghci> bigMul [9,9,9,9] [9,9,9,9] [9,9,9,8,0,0,0,1] ghci> bigMul [9,9,9,9,9] [9,9,9,9,9] [9,9,9,9,8,0,0,0,0,1] ghci> bigMul [4,3,7,2] [1,6,3,2,9] [7,1,3,9,0,3,8,8] ghci> bigMul [9,9,9,9] [0] [] Your implementation should not be recursive. Code: import Prelude hiding (replicate, sum)import Data.List (foldl') foldLeft :: (a -> b -> a) -> a -> [b] -> afoldLeft =…Write a recursive function PrintPattern2 that receives two arguments: (i) a character ch; (ii) number of lines and print the pattern.Example:PrintPattern2('*',5) will print the following pattern

