Write code that when executed in PowerShell, will satisfy the following requirements: Complete the following command so that it displays the output indicated below.
Q: Question: Find the even multiples of any number chosen by the user in a given range – the user…
A: According to the information given:- We have to follow the instruction to get the desired outcome…
Q: . In order to avoid deadlock between threads we can use a —— object. 2. A class —— another if its…
A: Deadlock is a situation in computer programming, where two programs shares the same resources and…
Q: Create a complete ER diagram to represent the data used by a library. The library provides books to…
A: Answer
Q: Write a C/C++ program to extract the sign bit, exponent field, and the fraction field of a 32-bit…
A: Code: // include required header files#include <limits.h>#include…
Q: Explain the differences between an SSD and a magnetic disc.
A: Introduction SSD: The full form of SSD is Solid-State Drive. It is nothing but a huge storage…
Q: ments used in the Batch Proce
A: Below Name the Six (6) documents used in the Batch Processing System
Q: Do not use Swing for the console output--the console output must be displayed in the console. Write…
A:
Q: Write a c++ code that swaps two input integers using pointers. a. In the main function. b. By…
A: The function declaration would be void swap(int *, int *) ; Here when we call this function from…
Q: What would be the output of the following program?
A: Explanation: Answer is 21 Explanation It uses the concept of nested list. The elements of nested…
Q: Character devices often send data quicker than block devices. Is this statement true or false?…
A: Under unix systems there are mainly two types of devices. They are categorised as:- 1. Character…
Q: Question 1 Discuss some of the advantages of online banking. Would you prefer an online or Physical…
A: As per our guidelines we are suppose to answer one question. Kindly repost other questions as…
Q: What are the four most important roles of routers?
A: Introduction: When two or more packet-switched networks or subnetworks are linked together by a…
Q: Suppose that the circle is inscribed within the square as depicted above. If someone were to throw a…
A: Matlab Program: clcclear allclose allr=1;L=2*r;A_circ=pi*r*r;A_sq=L*L;myProbability=A_circ/A_sq
Q: As a result of our findings, we believe Flynn's taxonomy has to be raised by one level. High-level…
A: A high-level computers a PC with an undeniable level computational limit contrasted with a broadly…
Q: Which compiler phase would give you an error notice if you attempted to add an integer to a…
A: Introduction: Compiled programs written in a high-level language are converted into equivalent…
Q: DO NOT COPY PASTE FROM INTERNET Declare 6 arrays as required 10 store the students record each of…
A: Program Explanation: 1) Implement the header file. 2) Declare the integer. 3) Storing the…
Q: One lap around a standard high-school running track is exactly 0.25 miles. Define a function named…
A: Given data, One lap around a standard high-school running track is exactly 0.25 miles. Define a…
Q: Write program: prompt user to enter 2 double numbers which are the radius of 2 circles. Save values…
A:
Q: Why was an alphanumeric number system referred to as a hexadecimal number system?
A: Introduction It is known as hexadecimal to refer to the numeral system that has a base of 16. As a…
Q: Using the given diagram: 1. Give the pre-order traversal 2. Give the in-order traversal 3. Give the…
A: 1. The order of preorder traversal is Root -> left -> right Thus the preorder traversal is 1 7…
Q: Create the K-maps and then simplify for the following functions: 1) . F(x,y,z) = y′z′ + y′z + xyz′
A: The solution is F= y'+xyz'
Q: . How many step function do Rour and 2 each have in S-AES?
A: This is a cryptography question of AES Algorithm.
Q: 2. You have a 5*5 empty array. Write a C++ program to fill random values[0,100] in the array and…
A: Required:- 2. You have a 5*5 empty array. Write a C++ program to fill random values[0,100] in the…
Q: What form of data is sent to each of the following? (7-8 bit ASCII, 4-bit BCD, 8-bit binary for…
A: Answer the above questions are as follows:
Q: Initially, why was RISC architecture recommended?
A: INTRODUCTION: An Instruction Set with Fewer InstructionsA computer is a form of microprocessor…
Q: Write a simple python program which sums the integers from 1 to 10 using a for loop (and prints the…
A: We used the for loop to calculate the total of n numbers in the preceding example. First, we took a…
Q: A command-line interface or a graphical user interface? Why?
A: ANSWER:-
Q: 7. Write a C/C++ program that reads in a sequence of positive integers and prints out their BCD…
A: Code: #include <iostream>//include the header files #include <queue>//include the header…
Q: puter Science Show the runtime stack and activations for the following recursive function. by…
A: Given : public static void printCharsReverse(String str) { if (str == null || str.equals(""))…
Q: Given symbols and their frequencies of occurrence in some a) Determine and draw the Huffman Tree,…
A: Answer
Q: 4. Write program to evaluate the following polynomial function: f(x) = 2x³ + 5x² – 7x - 9 Prompt…
A: Input : Input x Output : Polynomial value in the given form.
Q: Task 3 Using the state space graph given below, OPEN and CLOSED lists, to demonstrate the…
A: -Hill-climbing algorithm is a local search algorithm . -It moves continuously upward until the best…
Q: Assume you have a method (shown below) inside the single linked list class, what does this method…
A: Ans: Assume a method inside the single linked list class , This method is doing that private E…
Q: 10. A 2.0 dBm signal is sent into a 1 × 10 tree coupler. What's the output signal strength from this…
A: Answer
Q: Once distinct software modules have been written and tested, they must be combined and tested as a…
A: Given that After writing and testing individual software modules, they must be combined and tested…
Q: Which features of Azure Domain are particularly useful? Beyond Microsoft, there are several more…
A: Introduction: Azure Active Directory (Azure AD) is a cloud-based identity and access management…
Q: Which of the following Big O notations is equivalent to 0(734-N+8N2+100N6)? O N? ON
A: answer is
Q: The virtual machine monitor (VMM) or hypervisor is a software layer that sits underneath the guest…
A: Hypervisors: Segmentation is accomplished by a bit of software known as a hypervisor. It hides the…
Q: 6. Consider the following code segment. Assume that index1 is a number between 1 and…
A: Let us see the answer below,
Q: What are the advantages and disadvantages of UML?
A: UML stands for Unified Modeling Language and it is a general purpose modeling language. UML is used…
Q: 7. A code segment is intended to transform the list utensils so that the last element of the list is…
A: The given question asks for to remove last element of the list and inset the removed element at 1st…
Q: What value does mystery(12345678) return? public String mystery(int n) { String soln = “”; while…
A: The correct option is option b which is "2468".
Q: are underlined. Give an expression in SQL for each of the following queries. Student(studentID,…
A: 1) SELECT full_name, school_name FROM Student NATURAL JOIN School WHERE age>=10 AND age<=15
Q: For each order id, calculate the total of the Order. The total of an order is the sum of the prices…
A: For each order id, calculate the total of the Order. The total of an order is the sum of the prices…
Q: Discuss the advantages and disadvantages of the delta modulation compared to PCM.
A: Answer
Q: Embedded systems often rely on watchdog clocks for several reasons.
A: The watchdog timer is critical in embedded systems: The watchdog timer (WDT) is a component of the…
Q: 10. The following code segment is intended to remove all duplicate elements in the list myList. The…
A: We are given a code's logic which is suppose to remove duplicates from the given list. But this…
Q: Create a program that declares variable to hold number of eggs of a chicken. Your program will…
A: import java.util.*;public class Main { public static void main(String[] args) { Scanner scan =…
Q: If building a new system architecture to serve the new service presents any obstacles, would cloud…
A: EXPLANATION: Organizations encounter the following challenges while creating their infrastructures:…
Q: Convert the following expression from infix to postfix. A * C + D – K / 3 * 10
A: answer is
This seems to be a straight forward powershell problem but I can't figure it what goes after format-table for this question.
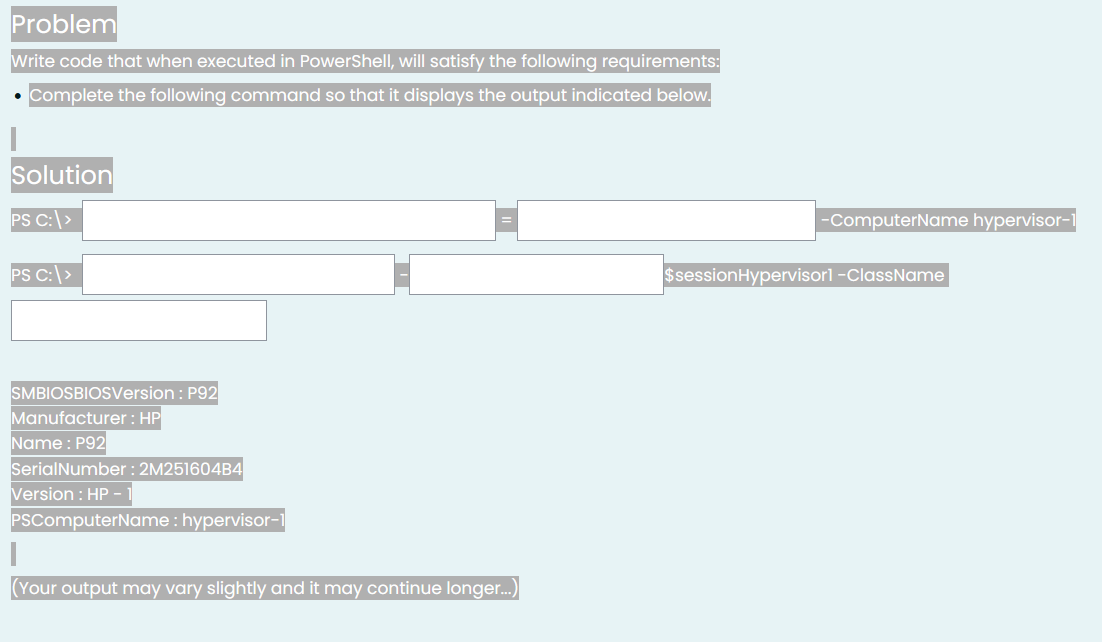
Step by step
Solved in 2 steps with 1 images

- Please answer properly with output screenshot must Where is the error in this code? from telethon.sync import TelegramClientfrom telethon.tl.functions.messages import GetDialogsRequestfrom telethon.tl.types import InputPeerEmptyimport os, sysimport configparserimport csvimport time re="\033[1;31m"gr="\033[1;32m"cy="\033[1;36m" def banner():os.system('clear')print("ok") cpass = configparser.RawConfigParser()cpass.read('config.data') try: api_id = cpass['cred']['id'] api_hash = cpass['cred']['hash'] phone = cpass['cred']['phone'] client = TelegramClient(phone, api_id, api_hash)except KeyError: os.system('clear') banner() print(re+"[!] run python3 setup.py first !!\n") sys.exit(1) client.connect()if not client.is_user_authorized(): client.send_code_request(phone) os.system('clear') banner() client.sign_in(phone, input(gr+'[+] Enter the code: '+re))os.system('clear')banner()chats = []last_date = Nonechunk_size = 200groups=[]result =…Below is cache.py. Make sure the code works properly and is plagarism free. Make sure to show the screenshot of the output with the screenshot of the code being tested as plagarism free. cache.py import socketimport sys def handle_client(client_socket): while True: command = client_socket.recv(1024).decode() if not command: break if command == 'quit': break elif command == 'put': receive_file(client_socket) elif command == 'get': send_file(client_socket) else: print("Invalid command.") break client_socket.close() def receive_file(client_socket): pass def send_file(client_socket): pass def main(): if len(sys.argv) != 4: print("Usage: cache.py <port> <server_ip> <server_port> <transport_protocol>") return port, server_ip, server_port, transport_protocol = int(sys.argv[1]), sys.argv[2], int(sys.argv[3]), sys.argv[4]…The Cupid matchmaking Service maintains two files - one for the male clients and another for female clients. Each file contains a client ID, last name, first name, and address. Each file is in client ID order. Use the provided pseudocode to write a C++ application that merges the two files into one file containing a list of all clients, maintaining ID member order. // Pseudocode Project8// Start// Declarations// InputFile inFile1;// InputFile inFile2;// OutputFile outFile1;// num mClientNumber, fClientNumber// string mClientName, fClientName// bool atLeastOneFileNotAtEnd = true// bool inFile1Written = false// bool inFile2Written = false// output "File merge processing starting"// open inFile1 "MaleClients.rtf"// open inFile2 "FemaleClients.rtf"// open outFile1 "MergedClients.rtf"// read mClientNumber and mClientName from inFile1// read fClientNumber and fClientName from inFile2// while ( atLeastOneFileNotAtEnd == true )// if (inFile1 is EOF)// if (inFile2Written == false)// output…
- This exercise is will require you to write a C program that is able to run Linux commands from theprogram when executed. The program should be able to perform the following operations:1. Take a Linux command as an input from the user using scanf in C.2. This command should be a valid Linux command3. The program should use execvp(char *command, char *params[]) function to run this Linux commandand produce and output on the console.4. The screenshot below shows the expected output of the program:Instructions:• Write the C program in any editor of your choice. • Use execvp(char *command, char *params[]) function to run the commandsa) Create a system call int sys_wolfie(void *buf, uint size), which copies an ASCII art image of Wolfie to a user-supplied buffer, provided that the buffer is large enough. You are welcome to use an ASCII art generator, or draw your own by hand. If the buffer is too small, or not valid, return a negative value. If the call succeeds, return the number of bytes copied. B) Write a user-level application, called wolfietest.c, that gets the Wolfie image from the kernel, and prints it to the console. When the OS runs, your program's binary should be included in fs.img and listed if someone runs ls at the xv6 shell's command prompt. Language in CBelow is server.py. Make sure the code works properly and is plagarism free. Make sure to show the screenshot of the output with the screenshot of the code being tested as plagarism free. server.py import socketimport sys def handle_client(client_socket): while True: command = client_socket.recv(1024).decode() if not command: break if command == 'quit': break elif command == 'put': receive_file(client_socket) elif command == 'get': send_file(client_socket) else: print("Invalid command.") break client_socket.close() def receive_file(client_socket): pass def send_file(client_socket): pass def main(): if len(sys.argv) != 3: print("Usage: server.py <port> <transport_protocol>") return try: port, transport_protocol = int(sys.argv[1]), sys.argv[2] except ValueError: print("Invalid port number.") return…
- if the user click on create account or on login with empty text info (without entering the desired info like name and DOB before clicking on create account for example ) the program crashes, can you figure out why and fix it import tkinter as tkfrom datetime import datetime, timedeltaclass ATM: def __init__(self): self.accounts = {} def create_account(self): # Get user inputs first_name = first_name_entry.get() last_name = last_name_entry.get() dob = dob_entry.get() address = address_entry.get() debit_card = debit_card_entry.get() while len(debit_card) != 16 or not debit_card.isdigit(): debit_card = input("Invalid debit card number. Enter debit card number (16 digits): ") pin = pin_entry.get() while len(pin) != 4 or not pin.isdigit(): pin = input("Invalid pin. Enter 4-digit pin: ") # Create account and update GUI self.accounts[debit_card] = {"first_name":…Below is a sequence of shell commands that we typed into a bash terminal window on a Linux machine and some of the output that was produced. Your job is to write the output produced by the commands in the sequence. The commands are executed consecutively and changes made by one command may affect the output produced by later commands. First Create a Directory and Rename as Name_AridNo like (Ali_18-Arid-102) and then execute the following commands and show output. Shell > pwd /home/me/test > ls -F hw1 hw1.bak tmp/ > bash > touch it > cd tmp > ls –F justme.txt > echo “Dear Ali” > diary > cat ‘Name_AridNo’ /etc/hosts > pwdIn Chapter 11, you created the most recent version of the MarshallsRevenue program, which prompts the user for customer data for scheduled mural painting. Now, save all the entered data to a file that is closed when data entry is complete and then reopened and read in, allowing the user to view lists of customer orders for mural types.
- I have a code (class Server). I need help to fix error in another class. These are 2 seperated files. import socketimport pandas as pdimport sqlite3class Server:def __init__(self, portnumber):self.port = portnumberself.s = socket.socket()self.host = socket.gethostname()self.s.bind((self.host, self.port))self.s.listen(5)print('Server listening....')def __enter__(self):return selfdef __exit__(self, exc_type, exc_val, exc_tb):self.close()def serve(self):while True:conn, addr = self.s.accept()print('Got connection from', addr)query = conn.recv(1024).decode()print('Server received query:', query)# Process the SQL query and retrieve datadata = self.process_query(query)# Send the data back to the clientconn.sendall(data.to_msgpack())print('Sent data:', data)conn.close()def process_query(self, query):# Connect to the SQLDatabase and execute the queryconnection = sqlite3.connect('data.db')data = pd.read_sql_query(query, connection)connection.close()return datadef close(self):self.s.close()# Run…Please identify the correct statement(s) for the following code snippet from the script: while inst_iter.hasNext() and not monitor.isCancelled(): ins = inst_iter.next() addr = ins.getAddress() pcodeList = ins.getPcode() for pcode in pcodeList: if pcode.getOpcode() == PcodeOp.FLOAT_DIV or pcode.getOpcode() == PcodeOp.INT_DIV: print("Address: {}, Inst: {}, Pcode: {}".format(addr, ins, pcode)) addrSet.add(addr) Question 1 options: It saves the address of the disassembled instruction that introduces division. This snippet uses refined/high p-code. This snippet uses raw p-code. It uses p-code opcode to identify the division operator. It uses the mnemonic string of a disassembled instruction to identify the division operator. It saves the sequence number of the p-code instruction that introduces division.Please write the program and explain-line-by-line. Thank you! A shell interface gives the user a prompt, after which the next command is entered. The example below illustrates the prompt osh> and the user's next command: cat prog.c. (This command displays the file prog.c on the terminal using the UNIX cat command.) osh>cat prog.c One technique for implementing a shell interface is to have the parent process first read what the user enters on the command line (in this case, cat prog.c) and then create a separate child process that performs the command. Unless otherwise specified, the parent process waits for the child to exit before continuing. This is similar in functionality to the new process creation illustrated in Figure 3.9. However, UNIX shells typically also allow the child process to run in the background, or concurrently. To accomplish this, we add an ampersand (&) at the end of the command. Thus, if we rewrite the above command as osh>cat prog.c & the…





