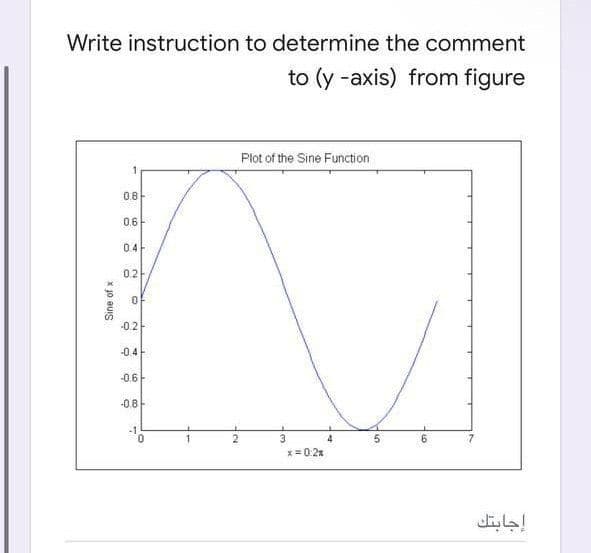
Write instruction to determine the comment to (y -axis) from figure
Q: Are operating systems partitioned in a way that's unique to each of them?
A: Introduction: Disk operating systems and file systems recognize a partition as a separate entity.…
Q: Were usability and user experience objectives split into separate categories?
A: Given: When it comes to product/design usability, a user may utilise it to fulfil a specified goal…
Q: what is SDLC's waterfall model?
A: SDLC stands for Software Development Life Cycle. The waterfall model is the first process model to…
Q: Use any system or piece of software, such as a program from Microsoft Office, to access the Help…
A: Software: To operate a computer, software is utilised. System software, utility software, and…
Q: Write a program to generate and print a two- dimensional array as rowl: 0 4 8 8 12 row2: 1 5 9. 13…
A: ALGORITHM:- 1. Declare the array of size 4*2. 2. Fill it using the nested loops. 3. Display the…
Q: Why may an application choose for UDP instead of TCP?
A: Beginning: Packet retransmission is not performed in UDP. UDP is also easier to use and quicker than…
Q: List and discuss four vulnerability intelligence sources. Which seems to be the most efficient? Why?
A: A smart card reader is the answer: Smart card readers can be used as part of an authentication…
Q: What are the computer's three most basic parts?
A: Explanation: A machine is made up of a few fundamental parts.Hardware, apps, programmers, data, and…
Q: Create a program using class that randomly adds, subtract, and multiply numbers base on the user's…
A: Find the required code in C++ given as below and sample output :
Q: Let G = (V,E,w) be a weighted directed graph. The diameter of G is the largest distance between any…
A: Given that, There is a graph G= (V,E,w) where V= vertices, E= edges and w=weights of the edges. The…
Q: What is "white box testing?" Is white box testing really necessary?
A: Start: White Box Testing: White box testing is concerned with the programing code's inherent logic…
Q: e a POWERSHELL (not shell, specifically Powershell) script program (evenodd.ps) which adds the odd…
A: Answer:- Below are the commands to do your given task. $lines = (Get-Content $filepath).split('\n')…
Q: Write quadruples from the expression : (a +b) * (c + d) – (a +b + c) and Discuss the issues in…
A: Given expression : (a+b) *(c+d) - (a+b+c) Quadruples: record structure with four fields: operation,…
Q: In-depth discussion and assessment of your wireless security expertise is provided.
A: Wireless security: In order to protect your computer and data, wireless security measures must be…
Q: Is there a variety of malware? Do worms and viruses have any differences? Infectious diseases are…
A: Definition: According to the question, a Trojan horse virus does not exist. Worms, Trojan horses,…
Q: Illustrate the strengths and the weaknesses associated with the proposed K-12 Cybersecurity…
A: Given: Illustrate the strength and weakness of K-12 Cybersecurity standards
Q: How can we begin usability engineering without first getting to know our users?
A: Explanation: Usability engineering is a field of study that focuses on improving the usability of…
Q: What's the difference between a test criteria and a test requirement in software engineering?
A: Criteria for the test: Any task in which there are no problems in the code (meaning its execution…
Q: Suppose we have two 2-dimensional arrays a and b, and consider the following C code. int a[4][4];…
A: Here we have given the cache misses wrt to array a and b. You can find the solution in step 2.
Q: Consider the main memory sıze of 128 kB, Cache sıze of 16 kB, Block size of 256 B with Byte…
A: Main memory size = 128KB = 17 bits Total number of cache block = 16KB/256 = 64 Block size = 256 B.…
Q: Simplify the function F(A,B,C,D)=A'C'D+ A'D+B'C+CD+AB'D' using Kmap. Draw the logic circuit for the…
A:
Q: microprocessor
A: answer is
Q: To guarantee that the carry flag is set, what command should be executed? the condition of…
A: Introduction: To guarantee that the carry flag is set, what command should be executed? The…
Q: How were usability and user experience metrics allocated in the review?
A: Intro The following are the usability and user experience metrics that were used in the evaluation:…
Q: Write a program, which returns the index of the minimum repeating element of the array in Jinear…
A: INTRODUCTION: Here we need to write a c++ program that returns the index of the minimum repeating…
Q: ecks whether the point is within the circle centered at (0, 0) with radius 10. For example, (4, 5)…
A: Given:
Q: is language a labeled-line system or an across-fiber pattern system?
A: is language a labeled-line system or an across-fiber pattern system?
Q: Your Windows machine launches to a blue screen with no Start screen or desktop. What is the first…
A: Introduction: Your Windows system starts up with a blue screen of death and no Start menu or…
Q: Implement single port 128×8 RAM module using VHDL with synchronous read/write operations. and Show…
A: Answer is given below-
Q: As an ATM virtual circuit, the smallest conceivable unit, it is the virtual circuit. How?
A: Introduction: In terms of ATMs, you must determine which of the following virtual circuits is the…
Q: explain why the Work Breakdown Structure is important. Is the software development lifecycle (SDLC)…
A: INTRODUCTION: Here we need to tell explain why the Work Breakdown Structure is important. Is the…
Q: Provide 2 flowcharts (1. uses for-loop and 2. uses do-while loop ) for a program that accepts a…
A: Your both flowchart 1. use for loop and 2. uses do-while loop is given below.
Q: Explain the need for diverse testing strategies at various stages of the software development life…
A: There are different strategies available for testing in software development life cycle.
Q: When it comes to performance testing, there are a number of reasons why JMeter is the tool that…
A: JMeter is a desktop application that runs entirely in Java and is used to test and evaluate overall…
Q: Many proposals have been made for a processor that can decode encrypted data and system instructions…
A: According to the information given:- We have to describe processor that can decode encrypted data…
Q: Why do bugs happen? How can a bug enter into a piece of code? Give a few instances to illustrate…
A: Bugs: Errors made by the developer during software development result in bugs. Due to the…
Q: For the sake of evaluating software maintenance, what metric should be used?
A: Software Administration: In software maintenance, there are five distinct metric types. Preventive…
Q: Carry out a comparison investigation on no less than four of the many search engines that are…
A: Introduction: Location, personalization, and algorithm differences are the key reasons for consumers…
Q: A description of the implementation of finite-state machine control is required.
A: Introduction: A finite-state machine (FSM) is a mathematical description of computing that is also…
Q: es assume that the page of proc
A: Solution - In the given question, we have to tell which is better among FIFO and LRU.
Q: When carrying out performance testing, what do you think to be the most important factors to take…
A: Performance testing is a technique for measuring the speed, responsiveness, and stability under the…
Q: a five-digit integer variable iVar. Separates it into its individual digits and print the digits…
A: Here in this question we have asked to consider a five digit integer variable iVar.and separate it…
Q: A well-known testing tool for unit testing is known as Junit. What additional kinds of testing tools…
A: Unit Testing: A unit test is a technique for testing a unit, which is the smallest amount of code…
Q: Defintion and definitions of secrecy, confidentiality, privacy, integrity and availability
A: This question explains about definitions of secrecy, confidentiality, privacy, integrity and…
Q: Write a program to generate and print a two-dimensional array as follows: rowl: 0 3 6 9 row2: 2 5 8…
A: ALGORITHM:- 1. Declare the array of size 4*2. 2. Fill it using the nested loops. 3. Display the…
Q: Put your own words to use while describing the notion of "separation of concerns." Engineers in the…
A: Separation of concerns: Separation of concerns is a software architecture design pattern and idea…
Q: Write a python function count_matches that, given two strings, counts the number of positions at…
A: Algorithm to count number of matching character in in two string Take two string as input. For…
Q: Cuánto es 2*2
A: How much is 2*2
Q: In a Big Data initiative, you might consider the use of Infrastructure as a Service (IaaS) and…
A: Infrastructure as a service (IaaS) is a kind of cloud computing service that provides the necessary…
Q: Write a program that first gets a list of integers from input and puts them into a vector. The input…
A: I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT-----------------
Step by step
Solved in 2 steps

- Implement the following pseudocode in assembly language. Use short-circuit evaluationand assume that X is a 32-bit variable.if( ebx > ecx ) OR ( ebx > val1 )X = 1elseX = 2Write a single instruction that converts an uppercase character in AL to lowercase but doesnot modify AL if it already contains a lowercase letter.Describe the implementation of the TestandSet instruction. Show how the followingalgorithm using TestandSet does not satisfy the bounded wait requirement?Shared data: boolean lock = false;Process Pi:do {while (TestAndSet(lock)) ;critical sectionlock = false;remainder section}
- what is the 8085 Assembly Language Instruction That do the follwing Call a Function conditionally on not zero result (flag Z=0)Can you tell me what the phrase "instruction pipelinelining" means? Not only should the problems with data and branches be explained, but solutions should also be given.Implement the following pseudocode in assembly language. Use short-circuit evaluationand assume that val1 and X are 32-bit variables.if( val1 > ecx ) AND ( ecx > edx )X = 1elseX = 2;
- EX2: « Explain what happens as the following sequences of instructions are executed : . MOV DL.05H . MOV AX,0A00H . MOV DS AX . MOV SI,0H . MOV CX,0FH « Again: INC SI . CMP [SI].DL . LOGCPNE Againwhat is the 8085 Assembly Language Instruction That do the follwing Call a Function conditionally on minus result (flag S=1)What is the 8085 Assembly Language Instruction That do the follwing Return from a Function Unconditionally
- what is the 8085 Assembly Language Instruction That do the follwing Call a Function UnconditionallyWhat is the value of DX after the instruction (subtraction)? DX = 35F3H BX = 7235HSUB DL, BHSelect the correct response:A.129 B. 3581C. 3581HD. 128In this implementation, each instruction is provided with its own data independently of how other instructions acquire theirs. We insert a(n): A Multiple Input/Output B The Case of Many Pieces of Information or Directions C Unique Information Only One D Several Insts From One

