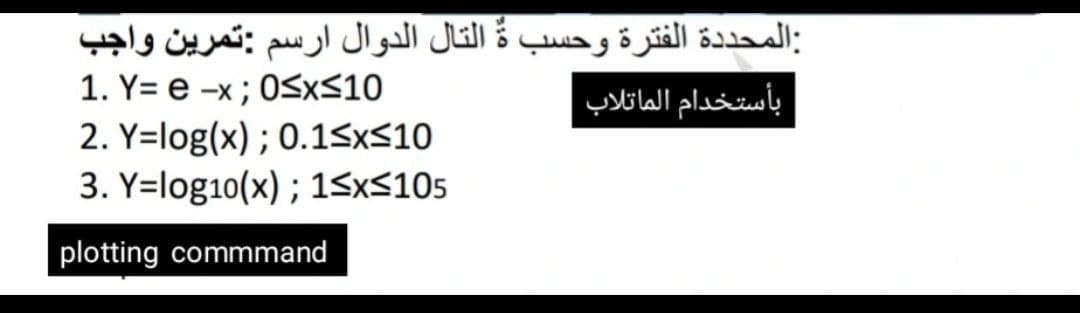
-x; OSXS: Y=log(x) : 0.15
Q: When should the tester stop testing the * ?software When all the bugs are found When they have enoug...
A: Q) When should the tester stop testing the software? Answer: D) They should never stop testing Expl...
Q: Datapath should be defined.
A: Introduction: A data path is a collection of functional units that conduct data processing tasks, su...
Q: The computer communication system is made up of six components, which are as follows: Write brief co...
A: Communication implies sending, getting and handling of data between at least two gadgets. An assortm...
Q: Describe the many types of computing applications and the characteristics of each.
A: An application, often known as an application program or application software, is a computer softwar...
Q: What exactly is a lock? What is the necessity for them in relation to database management systems? W...
A: Lock guarantees for special use of data objects in current activity. It first accesses the data obje...
Q: What are the difficulties that a simultaneous multithreading architecture must handle in an operatin...
A: Simultaneous multithreading (SMT) is a method that uses hardware multithreading to improve the overa...
Q: Question1: define two lists of numbers (arrays) and ask the user to give the size of each, and then ...
A: First check whether the lengths are same or not Then every element in both the arrays and check whet...
Q: Using this image, explain how you would use this configuration for an email system to a new cloud cu...
A: explain how you would use this configuration for an email system to a new cloud customer or the exec...
Q: An summary of the systems design phase should be provided.
A: System design bridges the gap between the issue domain and the current system, This phase focuses on...
Q: Explain why the ability to respond in real time is a crucial differentiator between embedded systems...
A: Introduction: An embedded system is one that is embedded inside another system, normally performs a ...
Q: Explain briefly with the aid of examples the uses and importance of the following technologies i.Ar...
A:
Q: Why is it important to categorized Network based on their size?
A: We are going to understand why we have categorised Network based on their sizes like LAN,MAN,WAN etc...
Q: Which one of the following is a proposition/statement? a. Six is an odd integer. b. Divide 12 by 2 t...
A: Given: Which one of the following is a proposition/statement? a. Six is an odd integer. ...
Q: Distinguish the reasons why distributed software systems are more complex than centralized software ...
A: Difference between the distributed software system and centralized software system - Distribute...
Q: of the following productions is allowed in a CFG in Greibach Normal Form? А— ВаС
A: GNF answer should be only one terminal (small letters) followed by any no of non terminal(capital le...
Q: Find the condition numb infinity norm. 3 5 A = 2 6
A: Lets see the solution.
Q: 1- Write a MIPS assembly program that stores the values in consecutive successive words in the data ...
A: - Memory organization The purpose of the memory is to store batch bands, and bring them (processor f...
Q: How can I find out which thread models my operating system (Windows 7) uses (one-one, one-many, or m...
A: Introduction : There are four basic thread models : Single Thread Model at the user level: Model fo...
Q: ARDUINO LANGUAGE We have two push buttons and three LEDs (Red, Green and Blue). When the user pre...
A: Arduino language is a language based on C/C++ that makes easy to make program or write code. It is d...
Q: Write a program in Matlab that can read 33 numbers Then it prints the numbers that are divisible by ...
A: MATLAB CODE: a=33; disp('Given number is divided by 5' + a); number = 1; while number<=a if mo...
Q: a) What is Cyclic Redundancy Check (CRC) and how it works? b) Generate hamming code for the message ...
A: I have answered this question in step 2.
Q: Privacy in the context of information security is a difficult concept to comprehend.
A: Introduction: The term "privacy" in information security refers to protecting user information. It a...
Q: Explain how the size of the organization and the size of the program are factors that influence soft...
A: - We need to talk about how the size of an organisation and the size of the program influence softwa...
Q: write VB 6.0 program to print ali, Date and time after each 3 sec and continue until stop the timer ...
A: Answer in step 2
Q: Can you explain the importance of interrupt in microprocessor?
A: Introduction: Interrupt is a technique for temporarily stopping the execution of a programme so that...
Q: Define the MIDI protocol.
A: Introduction: MIDI is an abbreviation for Musical instrument digital interface. It is essentially a ...
Q: Distinguish the reasons why distributed software systems are more complex than centralized software ...
A: Distributed software systems are more complex than centralized software systems, which are character...
Q: How would you address the potential for misleading sharing?
A: Introduction: In frameworks with suitable, lucid stores at the size of the smallest asset block cont...
Q: data 4137 obs. of 12 variables : int 920 1170 810 940 1180 980 880 9.. : int 43 18 14 40 18 114 78 5...
A: According to the question, we have to write a code in RStudio using the lm function to perform the l...
Q: Give an example of when adaptors are typically required when systems are built by merging applicatio...
A: Necessity of adaptors in integrated framework At the point when multiple application frameworks are ...
Q: 6. How long does each of the given operations take for each of the given data structures? Write L fo...
A: Insertion at the cursor means inserting at a specific index. To insert a specific index in an array,...
Q: System software should be defined.
A: Computer software is classified into two broad categories: system software and application programme...
Q: Provide an explanation for the function of some of the components in a computer's internal memory.
A: Introduction: Internal memory is used at a start-up to store the system's data and run different typ...
Q: Create a C++ program that will check if the string or group of text is a palindrome or not. For exa...
A: PROGRAM EXPLANATION Include the header file. Define the main function. Take a string as input from ...
Q: raw a connected graph with 7 nodes and 10 edges which has no cutnode nor bridge. Find by the use of ...
A: Lets see the solution.
Q: Ving problem Read in 20 numbers, each of which islbetween 20 and 50, inclusive. As each number is re...
A: Although, below all program with output screen is shown. But, we must know that CA[20] is the change...
Q: Computer Science Please code in MatLab
A: Introduction Please code in MatLab
Q: What are the various purposes of the following categories of application software? Enterprise resou...
A: Introduction: In a nutshell, application software, or app, is software that performs specified funct...
Q: Twisted pair cable (Ethernet) has how many pairs of wires? What is the name of the port on a compute...
A: Actually, computer is a electronic device which takes input and gives output.
Q: Define the term "local wide network."
A: Locally extensive network A local network is a private computer network that is used to link compute...
Q: ysis and de
A: given - Establish a clear understanding of systems analysis and design, as well as the function of a...
Q: Which of the following problems does proof of work NOT solve? O Proof of sender' ownership of the fu...
A: One of the decentralised consensus mechanism is known as Proof of Work.
Q: You've been given the task of setting up a LAN for your workplace. a. As part of this arrangement, d...
A: Introduction: Novell's DOS, Windows, Mac, and OS/2 clients may connect to a TCP/IP network with this...
Q: Explain concurrency and then discuss four design and management considerations that arise as a resul...
A: Concurrency: Concurrency means execution of multiple processes at same time. The running processess ...
Q: ). Insert 20 into the following sorted list. Show your steps clearly. 3, 7, 21, 34, 46, 69, 88
A: # importing the moduleimport bisect # initializing the list, elementnumbers = [3, 7, 21, 34, 46, 69,...
Q: While developing a reliable transport protocol, early versions of the protocol discussed in class us...
A: RDP is a network transport protocol that was first defined in RFC 908 and modified in RFC 1151. Its ...
Q: Describe the process by which skilled interface designers carry out their jobs.
A: Introduction: Interface Design: Device Architecture and User Experience, or UX, are influenced by in...
Q: Choose a certain vertical application to look into more to begin your research. Investigate software...
A: Introduction: Horizontal word processing tools such as Microsoft Word and Corel WordPerfect are both...
Q: When an optimistic approach to concurrency control is applied, it is common for transactions to take...
A: Introduction: When an optimistic approach to concurrency control is applied, it is common for transa...
Q: Describe the security dimensions and security levels that must be taken into consideration while dev...
A: Introduction: Security signifies safety, as well as the precautions, are taken to be secure or prote...
Step by step
Solved in 2 steps with 2 images

- True or false set{(x,x2):x∈Z}canbeseeasafunctionZ→Q. set{(x2,x):x∈Z}canbeseeasafunctionZ→Q.Substitution ciphers are encryption/decryption algorithms that replace one letter or number with another. The first attested use of a substitution cipher in military affairs was by Julius Caesar, described by him in Gallic Wars (cf. Kahn pp83-84). In caesar cipher , you replace each letter by 3rd letter on. If it is out of bound (later than Z), then round to the head (letter A) and continue the shift. For example:meet me after the toga party PHHW PH DIWHU WKH WRJD SDUWB Please write a program in Java to implement the Caesar Cipher: a. Implement the encryption algorithm. Ask the user to input one all lower case normal sentence (called plaintext) using the nextLine method, and then output the encrypted text (called ciphertext). b. Implement the decryption algorithm. Ask the user to input one encrypted sentence (i.e. ciphertext) using the nextLine method, and then output the decrypted text (i.e. plaintext).Write code that prints a random number of lines between 2 and 10 lines inclusive, where each line contains a random number of 'x' characters between 5 and 20 inclusive. For example: xxxxxxx xxxxxxxxxxxxxxxxxx xxxxxxxxxxxx xxxxxx xxxxxxxxxxx xxxxxxxxxxxxxxxx
- Cell E3 has the formula “=A20+C22”; If we copy the formula from E3 to E4, which one of the following will be the formula in cell E4? a. "=A20+D22" b. "=A21+C23" c. "=A21+D23" d. "=B21+D23"HALP m + n = 2k + 2k = 4k therefore adding even numbers always gives an even number. The above is wrong because.... it doesn't consider the case when adding to odd numbers m and n are different so you cannot use 2k for both it doesn't consider what m and n are for particular values in the integers it doesn't consider the case when m is even and n is oddadd a green leaf on the right side of flower my code n = 800; A = 1.995653; B = 1.27689; C = 8; r=linspace(0,1,n); theta=linspace(-2,20*pi,n); [R,THETA]=ndgrid(r,theta); % define the number of petals we want per cycle. Roses have 3 and a bit. petalNum=3.6; x = 1 - (1/2)*((5/4)*(1 - mod(petalNum*THETA, 2*pi)/pi).^2 - 1/4).^2; phi = (pi/2)*exp(-THETA/(C*pi)); y = A*(R.^2).*(B*R - 1).^2.*sin(phi); R2 = x.*(R.*sin(phi) + y.*cos(phi)); X=R2.*sin(THETA); Y=R2.*cos(THETA); Z=x.*(R.*cos(phi)-y.*sin(phi)); % % define a red map for our rose colouring red_map=linspace(1,0.25,10)'; red_map(:,2)=0; red_map(:,3)=0; clf surf(X,Y,Z,'LineStyle','none') view([-40.50 42.00]) colormap(red_map)
- Write a program to compute sin(x) for given x. The user should supply x and a positive integer n, where sin (x) = x - x 3 /3! + x5 /5! - x 7 /7! + x9 /9! +……+x n /n!Find the values of a, b, c and d needed to solve this puzzle int a = ? int b = ? int c = ? int d = ? char expect[128] = "There are 10 kinds of people in the world: those who understand binary and those who don't"; char actual[128] = {}; strcpy(actual,expect); int location1 = 5; int location2 = 17; ((int *)actual)[location1] = 0x58585858; ((int *)actual)[location2] = 0x59595959; *(((int *)actual) + a) = b; *(((int *)actual) + c) = d; if(strncmp(expect,actual,BUFSIZE) == 0){ return; } failure("Here are hints:\n- use two ints with 4 bytes to make the message right\n- beware of endian ordering angst\n");calculate number of operations in this algorithm void my_dgemv(int n, double* A, double* x, double* y) { double alpha=1.0, beta=1.0; int lda=n, incx=1, incy=1; cblas_dgemv(CblasRowMajor, CblasNoTrans, n, n, alpha, A, lda, x, incx, beta, y, incy); }
- A binary number is to be transfromed by appending three 0's to the end of the number. For example , 11101 is transformed to 11101000. Which of the following best dewcribes the relationship between the transformed number and the original.- The transfromed number is 3 times the value of the original number- The transformed number is 4 times the value of the original number- the transformed number is 8 times the value of the original number- The transformed value is 1000 times the value of the original numberWrite a program to compute number/binary string x such that SHA256(“yourEmailAdress || x”) <= 107839786668602559178668060348078522694548577690162289924414440996864 What you should be submitting: (a) Your program (b) The number xWhich of the following sets are equal? A = {x | x^2 − 4x + 3 = 0} B = {x | x^2 − 3x + 2 = 0} C= {x | x ∈ N, x < 3} D= {x | x ∈ N, x is odd, x < 5} E= {1, 2} F = {1, 2, 1} G= {3, 1} H= {1, 1, 3}

