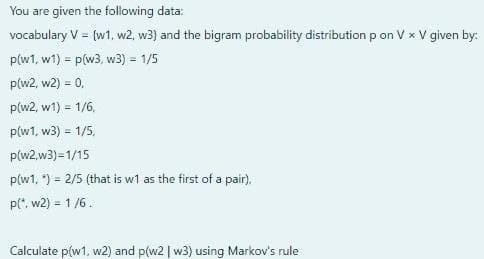
You are given the following data: vocabulary V (w1, w2, w3) and the bigram probability distribution p on V x V given b p(w1, w1) = p(w3, w3) = 1/5 p(w2, w2) = 0, p(w2, w1) = 1/6, p(w1, w3) = 1/5, p(w2,w3)=1/15 p(w1. ) 2/5 (that is w1 as the first of a pair). p(", w2) = 1 /6. Calculate p(w1, w2) and p(w2 | w3) using Markov's rule
Q: To fully define a variable one needs to mention not only its ‘type’ but also its ‘other properties’....
A: Answer: Variables Variable is a memory location which is used to store a value. The types of valu...
Q: [p → (¬h → c)] ∧ (p → ¬h) ⊧ p → c
A:
Q: What is a correct syntax to output "Hello World" in Python? print("Hello World") echo("Hello World")...
A: In python, For printing, print(" ") is used For commenting, # is used
Q: 1. Write a Java program that prints the sum, product, difference, and quotient of two numbers. Examp...
A: I have provided JAVA CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOTS---
Q: 1. Name the four assumption of a criminal profile. 2. What is a cyber nomad? 3. What is multifactor ...
A: *As for company norms and guidelines we are providing first three sub parts of the given question so...
Q: nput variables and what do their binary values represent? 2.)What are the output variabl...
A: The Digital Comparator is another very useful combinational logic circuit used to compare the value ...
Q: Given the following data, what is the result of the operation on it? If an instruction is illegal or...
A: Given the following data, what is the result of the operation on it? If an instruction is illegal or...
Q: Identify and describe the four key components of an information system.
A: Introduction: Here we are required to describe the four key components of an information system.
Q: Effects of overspeeding to driver, traffic enforcer and people around you Please create a Use cas...
A: Use Case Diagram given below:-
Q: Which of the following policy settings are not supported by Local Group Policy on Windows 10? (Choos...
A: in Folder redirection , You must be a member of the Domain Administrators security group, the Enter...
Q: Please don't copy *Python Pseudocode: read the question good and please answer the question and do n...
A: Solution: arrow_forward Forward pass To train a neural network, there are 2 passes (phases): Forward...
Q: Using R programming - Dataset contains around 65k+ traffic-related violation records and display 10 ...
A: Libraries Used :- PandasMatplotlibSeabornmissingno
Q: Suppose that Motorola uses the normal distribution to determine the probability of defects and the n...
A: Solution is given below:-
Q: I am stuck on this Problem.. Theory Of Computation.. Write pseudocode for an algorithm relies on R...
A: Ans: Introduction to Computational Theory Automata theory (also known as Theory Of Computing) is a t...
Q: Convert the binary number 11000101.101 to decimal format
A: As given, we need to convert the given binary number 11000101.101 to decimal format. I have provided...
Q: . (a) Is 2 드 {2, 4, 6}? (b) Is {3} E {1, 3, 5}?
A: When subset symbol is used. Check for {} symbol for each element except variables. When belongs to s...
Q: # your code here def multiply_numbers(a,b,c): # Called function receive three values from the callin...
A:
Q: Create a program that will ask the user how much they would like to tip.
A: using System; using System.Collections.Generic; namespace App { class Program { stat...
Q: Define the term "union" All operators, as well as the Union.
A:
Q: Given the context-free grammar G below: S → aSb|bSa[SS|A Give derivations for the strings ababab, ba...
A:
Q: There are two integer data values in locations num1 and num2. Create these two variables in an assem...
A: the program is an given below :
Q: 6. In PHP language, write a program to input a string from the user and print every character of the...
A: Write a PHP program to input a string from the user and print every character of the string in the o...
Q: 1. If a node x is the inorder successor of node y then node x must appear in y's subtree. (In Binary...
A: inorder traversal means traversal through left root right.
Q: what is the big O version of 5N^2 + N^2 + 1000?
A: Solution:
Q: 3. Farhan must pay a bill to a shopkeeper. The shopkeeper doesn't have any change, so Farhan must ha...
A: Given :- Farhan must pay a bill to a shopkeeper. the shopkeeper doesn't have any change, so Farhan m...
Q: What are the three primary roles of database administration?
A: Introduction: Maintenance is handled by Database Administrators, which involves monitoring servers, ...
Q: 58a2b+62c5+1 even or odd?
A: Your answer is given below with an explanation.
Q: Create a program that will accept numbers from 1-20 and determine if the entered number is odd or ev...
A: Find the required code in C and output:
Q: The above would be used via: proof by counterexample proof by exhaustion proof by ...
A: The negation is: ∃x in D such that P(x) ∧ ~Q(x)
Q: Activity 1: Display Images Design a GUI Application as shown below Display Images O X Camel Cat Lion...
A: Please make sure you place your files are in the correct folder. If using eclipse, the file should b...
Q: n the code template below, you are given three classes
A: Solutio Code
Q: 3. Explain the following MIPS addressing modes with the use examples (instructions): a) Register ...
A: Given :- 3. Explain the following MIPS addressing modes with the use examples (instructions): a) Reg...
Q: ). Has there been an addition to the MD series? If so, what is the name of the hashing algorithm?|
A: SUMMARY: - Hence, we discussed all the points
Q: 1. Write a program that reads a Celsius degree in a double value from the console, then converts it ...
A: As per the requirement program is completed. Algorithm: Step 1: Write the main() method Step 2: Usin...
Q: to decimal for
A: Given Binary Number: 1011101 Multiply each digit of the binary integer by the power of two that co...
Q: 2. Microsoft SQL server, how to copy 1 table from database1 and paste in database2, Each server is...
A: So , There is simple trick that you are able to copy one table from database1 and paste it on databa...
Q: There are multiple ways to prevent from this spyware. There are some that should always keep in mind...
A: Auditing is a mechanism, which is used to record the actions whatever happens on a computer system. ...
Q: Question 5 Analyze the following code: Number[] numberArray new Integer[2]: numberArray[0] - new Dou...
A: The correct answer is
Q: loud: A rapidly growing company has outgrown its computing e nvironment and needs to upgrade. The ch...
A: Cloud: A rapidly growing company has outgrown its computing e nvironment and needs to upgrade. The c...
Q: What is the output of the following program segment? * c = putchar (c); putchar (F(c)); putchar (c);...
A: As per the requirement program is executed in c language. If we execute the same program as it is we...
Q: In this program you will use a nested loop to generate the following outputs: $ ./a.out 1 22 333 444...
A: Hello student Greetings Hope you are doing great. Thank You!!!
Q: Question 1: Random Number Generator for Mark Six Lottery (A 6 out of 49 lotto game, 7 numbers are dr...
A: Random number generator using HTML,CSS and JavaScript.
Q: How Do Amazon Rds, Dynamodb, and Redshift Differ from Each Other
A: Introduction: How Do Amazon Rds, Dynamodb, and Redshift Differ from Each Other
Q: oefficients
A: given- Given the calculated filter coefficients h (0) = 0.25, h (- 1) = h(1) = 0.22508, h(- 2) = h(2...
Q: Investigate the challenges that information systems face via the use of technology and information r...
A: Introduction: This question discusses the difficulties that information systems face due to their re...
Q: ulating the amount needed to deposit in order to have, for instance, $5000 in the account after thre...
A: Suppose you want to deposit a certain amount of money into a savings account with a fixed annual i...
Q: In python, create a code that accepts the size of a list as an input (n). It will print out all the ...
A: INTRODUCTUON: The Answer is
Q: d. (4 – 2i) – ((-3 + 3i) + (1 + i))
A: Complex number: Complex number is a element of number system which contains real part and specific e...
Q: Write a Prolog program to print all Pythagorean triples (x, y, z) such that 1 ≤ x , y ≤ z ≤ 100. ...
A: Actually, program is an executable software that runs on a computer.
Q: Write a program that allows the user to navigate the lines of text in a file. The program should pro...
A:
Step by step
Solved in 2 steps with 2 images

- A random variable X with two-sided exponential distribution given by has moment generating function given by M X (t)= e^ t +e^ -t -2 t^ 2 . f x (x)= x+1,&-1\\ 1-x,&0<= x<=1 - 1 <= x <= 0 (a) Using M_{X}(t) or otherwise, find the mean and variance of X. (b) Use Chebychev inequality to estimate the tail probability, P(X > delta) , for delta > 0 and compare your result with the exact tail probability.Let X and Y be two binary, discrete random variables with the following joint probability mass functions. (a) Compute P(X = 0]Y = 1). (b) Show that X and Y are not statistically independent. P(X = 0, y = 1) = P(X = 1, Y = 0) = 3/8 P(X = 0, y = 0) = P(X = 1, Y = 1) = 1/8Consider values shown in the table below:i=1 (cold) i=2 (allergy) i=3 (stomach pain) p(Hi)0.60.30.1 p(E1 |Hi)0.30.80.3 p(E2 |Hi)0.60.90.0Those values represent (hypothetically) three mutually exclusive and exhaustive hypotheses for the patient’s condition. For example, H1: the patient has a cold, H2: the patient has an allergy, and H3: the patient has stomach pain with their prior probabilities, p(Hi)’s and two conditionally independent pieces of evidence (E1, patient sneezes and E2, patient coughs) which support these hypotheses to differing degrees. Therefore;a) Compute the posterior probabilities for the hypothesis if the patient sneezes. What is the conclusion that can be derived from this condition?b) Based on the answer from the previous result, as the patient coughs are now observed, compute the posterior probabilities for this condition. Explain the results.
- Given a two-category classification problem under the univariate case, where there are two training sets (one for each category) as follows: D₁ = (-3,-1,0,4} D₂ = {-2,1,2,3,6,8} Given the test example x = 5, please answer the following questions: have and a) Assume that the likelihood function of each category has certain paramétric form. Specifically, we p(x | w₁) N, 07) p(x₂)~ N(μ₂, 02). Which category should we decide on when maximum-likelihood estimation is employed to make the prediction?From 1965 to 1974, in U.S. there were M = 17, 857, 857 male livebirths and F = 16, 974, 194 female livebirths. We model the number of male livebirth as a binomial distribution with parameters size = M+F and prob = p. The following code computes the maximum likelihood estimator for p. M <- 17857857 F <- 16974194 ll <- function(p){ dbinom(M, size=M+F, prob=p, log=TRUE) } ps <- seq(0.01, 0.99, by = 0.001) ll.ps <- ll(ps) plot(ps, ll.ps, type='l') phat <- ps[which.max(ll.ps)] abline(v = phat, col='blue') Question: What can we learn from the plot?From 1965 to 1974, in U.S. there were M = 17, 857, 857 male livebirths and F = 16, 974, 194 female livebirths. We model the number of male livebirth as a binomial distribution with parameters size = M+F and prob = p. The following code computes the maximum likelihood estimator for p. M <- 17857857 F <- 16974194 ll <- function(p){ dbinom(M, size=M+F, prob=p, log=TRUE) } ps <- seq(0.01, 0.99, by = 0.001) ll.ps <- ll(ps) plot(ps, ll.ps, type='l') phat <- ps[which.max(ll.ps)] abline(v = phat, col='blue') Question: An estimator for p, denoted by pˆ, is obtained by ps[which.max(ll.ps)]. Is this the maximum likelihood estimator? Why (explain the code)?
- Give an example of a random variable X : {b, c, d, e} → N (Natural Number) with expectation 2, where each of {b, c, d, e} has equal probabilityGiven 2 patterns at 0.4 and 0.6, estimate probability density analytically using a rectangular window of width 0.3, using a triangular window of width 0.3 and using 1 nearest-neighbour.Let events A, B, C, and D be given by A = {at least 3 heads}, B = {at most 2 heads}, C = {headson the third toss}, and D = {1 head and 3 tails}. If the probability set function assigns 1/16 toeach outcome in the sample space, find (i) P(A), (ii) P(A ∩ B), (iii) P(B), (iv) P(A∩C), (v) P(D),(vi) P(A∪C), and (vii) P(B ∩ D).
- A certain cat shelter has devised a novel way of making prospective adopters choose their new pet. To remove pet owners’ biases regarding breed, age, or looks, they are led blindfolded into a room containing all the cats up for adoption and must bring home whichever they pick up. Suppose you are trying to adopt two cats, and the shelter contains a total of N cats in one of only two colors: black or orange. is it still possible to pick up two black cats with probability ½, given that there is an even number of orange cats in the room? If so, how many cats should be in the room? How many black, how many orange?Please solve the following problem. Quiz = Pass Quiz = Fail AI = Fail 0.1 0.2 AI = Pass 0.6 0.1 Mid = Pass Mid = Fail AI = Fail 0.2 0.2 AI = Pass 0.5 0.1 Suppose you have three events AI Grade, Quiz, and Mid. Here each event has two possible outcomes, either pass or fail. Additionally, given that AI Grade is observed, Quiz and Mid become independent of each other. Also, out of every 100 students, 30 students fail the AI course. Now, using the joint probability tables given, calculate P(AI Grade=Pass, Quiz=Fail, Mid=Fail).2. Given a Sample Space S = {1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 12, 13}, Event A = {1, 3, 4, 7, 9}, and Event B = {3, 7, 9, 11, 12, 13} Find the probability P(A|B). State your answer as a value with one digit after the decimal point.

