
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN: 9780133594140
Author: James Kurose, Keith Ross
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Question
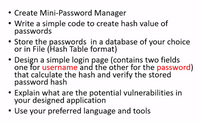
Transcribed Image Text:Create Mini-Password Manager
• Write a simple code to create hash value of
passwords
• Store the passwords in a dațabase of your choice
or in File (Hash Table format)
Design a simple login page (contains two fields
one for username and the other for the password)
that calculate the hash and verify the stored
password hash
Explain what are the potential vulnerabilities in
your designed application
• Use your preferred language and tools
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps

Knowledge Booster
Similar questions
- The encryption of the database's data has two advantages.arrow_forwardData redundancy is when the same data is stored in numerous places in a database. This redundancy may cause data to become __________, which occurs when multiple copies of the same data no longer share the same value. What is the underline word?arrow_forwardEvery data file has a ------- that says about the way the data is stored. Records File structure Database Fieldsarrow_forward
- How dangerous is it to copy a database off a server?arrow_forwardTrue or False: Data warehousing involves consolidating data from various sources into a single repository.arrow_forwardCS 386 Project: Overview Project Synopsis: This group project will require your group to design and implement your own enciphering algorithm. Your team's algorithm must combine the two operations, substitution and permutation/transposition, into your unique encryption algorithm. Your encryption algorithm must include multiple rounds of the two operations. You program must be able to encrypt and decrypt messages. Your team will need to give your algorithm a name that is unique to your encryption technique. Your group mayarrow_forward
- When a password has to be kept in a file, why is hashing preferable than encryption?What is the purpose of and how does a password file work?arrow_forwardRAID-capable storage reduces the need for Oracle database backups in today's environment.Written material is preferred over scrawled information since handwriting is more difficult to decipher.arrow_forwardDatabase question You want to be warned automatically when more than 100 sessions are opened with your database instance.Identify the action that would help you achieve this. a) Set the TRACE_ENABLED parameter to TRUE b) Set the threshold for the Current Logons Count metric c) Set the LOG_CHECKPOINT_TO_ALERT parameter to TRUE d) Set the SESSIONS_PER_USER limit in the profiles used by usersarrow_forward
- When a password is saved in a file, why is hashing preferable over encryption? What are the purposes and methods of a password file?arrow_forwardWhy is hashing a password saved in a file preferable to encryption? What exactly does a password file serve?arrow_forwardFalse or True An programme interacts directly with a database, updating, removing, and adding records.arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY

Computer Networking: A Top-Down Approach (7th Edi...
Computer Engineering
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:PEARSON

Computer Organization and Design MIPS Edition, Fi...
Computer Engineering
ISBN:9780124077263
Author:David A. Patterson, John L. Hennessy
Publisher:Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:9781337569330
Author:Jill West, Tamara Dean, Jean Andrews
Publisher:Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:9781337093422
Author:Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:9780133750423
Author:VENIT, Stewart
Publisher:Pearson Education

Sc Business Data Communications and Networking, T...
Computer Engineering
ISBN:9781119368830
Author:FITZGERALD
Publisher:WILEY