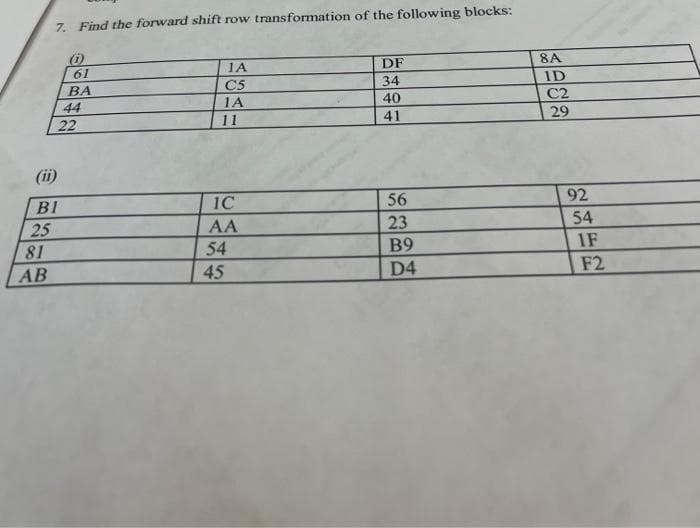
Z. Find the forward shift row transformation of the following blocks! 1A DF 8A 61 BA C5 34 ID 44 1A 40 C2 22 11 41 29 (ii) BI 1C 56 92 23 54 25 81 AA 54 45 B9 1F АВ D4 F2
Q: The use of social media by cybercriminals to disseminate malware is well documented.
A: Cybercriminals: Individuals or groups of people known as cybercriminals utilize technology to carry…
Q: void minimum (int i1, int i2) { if (i1 > n >> m; minimum (n, m); return 0;
A: Answer
Q: Are microcontrollers important in embedded applications
A: 1) Microcontrollers are designed for embedded applications, in contrast to the microprocessors used…
Q: What is the most effective method of mitigating a DDOS attack?
A: Diminish your opponent's assault surface by half. Minimize the surface area that may be attacked in…
Q: An airport has a runway for airplanes landing and taking off. When the runway is busy, airplanes…
A: Code: package Airport;import java.util.ArrayList;import java.util.LinkedList;import…
Q: What kind of firewalls are available besides those that operate on a network?
A: Given: This question enlightens you on the many types of firewalls available apart from…
Q: in the dimensional m
A: Sorry for that as per the bartleby guidelines we can solve only one question for you if you want to…
Q: 4. A function operating on positive integers is described by: { 1,ifn = 1 f(n) = f(n – 1) + 2, ifn >…
A: ALGORITHM:- 1. Take input for the value of n from the user. 2. Define a function that is…
Q: Distributed denial-of-service attacks may be carried out by a single individual.
A: No It requires multiple machines and group of people . A distributed denial-of-service (DDoS)…
Q: Is there anything more you need to do if you want your application to be useful?
A: Application performing meaningful actions: If someone wants their programme to do significant tasks,…
Q: 1. A manufacturer of scientific instruments produces thermometers that measure the freezing point of…
A: Solution:- In Excel we use the below functions for normal distribution Probability :…
Q: What can you do with a PictureBox control?
A: Lets see about PictureBox control in the next steps
Q: What are the advantages of utilizing virtual memory?
A: Introduction of the Virtual Memory: Virtual memory is section of the computer's secondary memory…
Q: What is the physical address of this instruction Source operand of MOV BL, [SI +
A: The answer is
Q: Application-layer messages are what you may call them. Is this part of the transport layer? In the…
A: A datagram is a network-related unit of transfer. A datagram possesses the following properties:…
Q: In C++ only You are given an array A of n integers as input. Also, you are given two integers, I and…
A: As per the requirement program is developed. Algorithm: Step 1: Write the main() method Step 2:…
Q: Question 1. Consider the below Verilog Code. Answer the corresponding questions. module…
A:
Q: Determine the order of trasversal for the nodes using the ff methods for the figure: DFS, inorder…
A: DFS: Inorder Traversal: Inorder Traversal is that the one the foremost used variant of DFS(Depth…
Q: "Pointers are known to have issues with dangling and wild pointers." With the use of appropriate…
A: A dangling pointer points to a memory location that has been removed (or released). Dangling…
Q: There are several reasons why the transport layer needs packetizing from the network layer. The…
A: The network's layer: The network layer of the OSI architecture is the layer that enables the host to…
Q: Create a C++ program that include the Fees to be paid The book was returned on time (Yes/No) If…
A: As per the requirement program is developed. Note: The book was returned on time (Yes/No) If yes,…
Q: What are the program's similarities and differences?
A: Project and programme similarities It’s good for project and programme managers to understand the…
Q: f(x) = |x| %3D AREA absolute, CODE EXPORT main ALIGN ENTRY main PROC
A: AREA absolute, CODE EXPORT _main ALIGN ENTRY _main PROC LDR r0, =0xF00FFABC ; input for which…
Q: What is the primary difference between operating systems on a mainframe and those on a laptop? What…
A: Start: One of the most important software programmes for managing and controlling computing devices…
Q: Explain what the word "firewall" implies in the context of network security, as well as how it is…
A: Firewall: A firewall is a network security device that monitors and filters incoming and outgoing…
Q: In what ways might a What is the function of a firewall, and how can it be put to use in your…
A: A Firewall is one type of network security device that monitors and filters incoming and outgoing…
Q: What is the physical address of this instruction Source operand of MOV BL, [SI +
A: The answer is
Q: Explain how Google Dorks works and what it's used for in the first place
A: Google Docs is a free web-based tool that allows users to create, edit, and save documents and…
Q: Describe network architectures, including topologies and strategies.
A: Given: The general design of a computer network is known as network architecture, while network…
Q: 36 95 Figure 1
A: According to answering policy we can answer only 1st question. Please resubmit remaining questions
Q: Assume you're a systems analyst working on a comprehensive test plan. Describe the testing…
A: System Analyst: A system analyst is someone who gathers and organizes data regarding software. The…
Q: Based on Big Data in Healthcare - Personal Healthcare: 1. Provide the opportunities in Personal…
A: Healthcare is the maintenance of health via diagnosis, treatment, prevention and physical therapy…
Q: In C#, what is a Collection? Explain the many sorts of collections.
A: Introduction: Collections are, in fact, modifiable. Mutables are just data that will not change once…
Q: Explain the differences between analog, digital, and hybrid computers.
A: There are three different sorts of computers, each with its capabilities. They're distinguished by…
Q: What were the three options available to GE for building the hardware and software capabilities…
A: An object's hardware capabilities specify the hardware requirements of the platform on which the…
Q: Using C Language, correct the following program and provide the correct final output: #include…
A: We are commenting what went wrong:- Syntax error:---> #include<stdio.h>…
Q: A) Give a one sentence description of the primary purpose of the Transport layer. B) Give a one…
A:
Q: Security engineering methods will be used to examine this DDoS attempt.
A: Security engineering: Security engineering is the act of integrating security measures into an…
Q: What are the advantages of utilizing virtual memory?
A: The Virtual Memory's Inception: To generate the appearance of a huge Main memory, the computer's…
Q: Java is an object-oriented programming language. Objects are known to exist in the real world. As a…
A: Object-Oriented Programming is a paradigm for programming in which objects represent everything. An…
Q: Give an argument supporting the statement that modularity is the most important principle in…
A: Modularity in software engineering refers to the degree to which a software/Web application can be…
Q: What are the different kinds of firewalls and how are they used?
A: Solution for the computers or devices that are connected Firewalls that filter packetsGateways at…
Q: What is the purpose of assembly language?
A: Given: Assembly language is now mostly used to manipulate direct hardware, get access to specific…
Q: Write a Scheme function mycount mylist myvar that counts the number of times myvar appears in the…
A: Please refer below code and output: Language used is python: def mycountmylist(lst,myvar): c=0…
Q: Collision domains broadcast domains is a Cisco switch command that can be used to debug VLAN trunk…
A: In order to see if your VLANs and your peers' work together, type "display interface trunk." It…
Q: What is a network topology, and how is it defined?
A: Physical or logical layout of a network: Network topology describes how a network's connections and…
Q: Demonstrate how a botnet was created and how it was used in a DDoS attack.in how botnets are built…
A: A distributed denial of service attack is attacked by the attackers which tries to avert allowable…
Q: String literals are included in what?
A: String literals : A "string literal" is a character sequence from the source character set…
Q: Problem Statement iven a list_of_strings (which are all lowercase letters), define and implement a…
A: Code: # Function to get minimum count of common character in all the strings in the listdef…
Q: What is a botnet and how can it be used in a DDoS attack?
A: Ans: The term botnet is called for “robot network”, which refers to a group of robot machines…
Step by step
Solved in 2 steps with 1 images

- Computer Science 1. Suppose that we have a 128-bit AES system: • 128-bit AES key; 2B7E151628AED2A6ABF7158809CF4F3C (in hexadecimal notation) • Plaintext: 3243F6A8885A308D313198A2E0370734 (in hexadecimal notation) a) What is the key for the first round in the 10-round AES? (Hint: W0 - W3) b) Construct the key schedule arising from the above key for second rounds c) What is the cyphertext of the above plaintext after one round? d) What is the cyphertext of the above plaintext after the second round?Perform the following operations (without converting to base 10). Show your work. a. 258 + 638b. 0x7BE3 + 0x45A7 c. 01012 + 10112 + 011012d. 1101002 - 0110102e. 1012 * 0112Q3 : Perform the following operation ( choose FIVE ) :-1- ( 7 – 3 ) using 2’s complement2- ( 111010 * 110011 )23- ( 572 )8 = ( ? )104- ( 111101.01101 )2 = ( ? )85- ( 56 )10 = ( ? )26- ( F9D )16 = ( ? )10
- Answer the following 4 questions with step by step explanations :1. Convert 870678(9) = x(27)2. Convert ABF(16) =x(64)3. Subtract APG(32) - 7RK(32) =4. Multiply BF(16)* AA(16) =Suppose DH contains (6B) hexadecimal, AH=(11001011)16 , CF=1, and CL contains 5, What are the values of DH AND DH,AH RCL DH, CL. Show the details of your work in the following table format. CL CF DHSubtract the followingFABC-ABCDABFD-98ACDFBC-15FF
- COH6SJ.Create a Hamming code (k, n) = (7,4) for the detection and correction of errors in word codeswhat is the first stage of R(10) if using data Eneryption Standard second stage R10 = 111001011100101111011110100001110110111101010010 K11= 001110101000101100101111110100100011101111111101 Select one: a. 11011111 01000000 11110001 11110001 01010101 01010100 10111111 b. 11011111 01000000 11110001 11110001 01010101 01011010 10101111 c. 11011111 01000000 10000001 11110001 01010101 01010100 10101111 d. 11011111 01000000 11110001 11110001 01010101 01010100 10101001 e. 11011111 01000000 11110001 11110001 01010101 01010100 10101111
- Assignment # 11. Convert 82ADh to decimal.2. Convert 11101b to decimal.3. Convert 2BD4h to decimal.4. Convert 95 to binary.5. Convert 2B3Ch to binary.6. Convert 1110101010b to hex.7. Add 3546d and 1872d.8. Add 5B39h and 7AF4h.9. Add 100101111b and 110110.10. Subtract 7283d from 9145d.11. Subtract BA94h from D26Fh.12. Subtract 0111b from 1001.13. Find one’s compliment of 5.14. Find two’s compliment of 5.15. Find two’s compliment of the two’s compliment of 5.16. In many applications, it saves time to memorize the conversions among small binary, decimal, and hex numbers. Fill in the blanks in the following table:Binary Decimal Hex_____ 9 _____1010 _____ __________ _____ D_____ 12 _____1110 _____ __________ _____ B 17. Convert the following binary and hex numbers to decimal:a. 1110b. 100101011101c. 46Ahd. FAE2Ch18. Convert the following numbers:a. 1001011 to hexb. 1001010110101110 to hexc. A2Ch to binaryd. B34Dh to binary19. Perform the following additions:a. 100101b + 10111bb. 100111101b…Explain what the following MIPS code does: (do not explain each line but explain what these two lines of codes do together) li $v0, 5syscallPlese using LZ77 encoding with a search window size of 8 and look ahead buffer of 4, encode the sequence abbdacdbbbbabba. Write down the output triples. Assume we will use <EOF> to indicate the end of the sequence.

