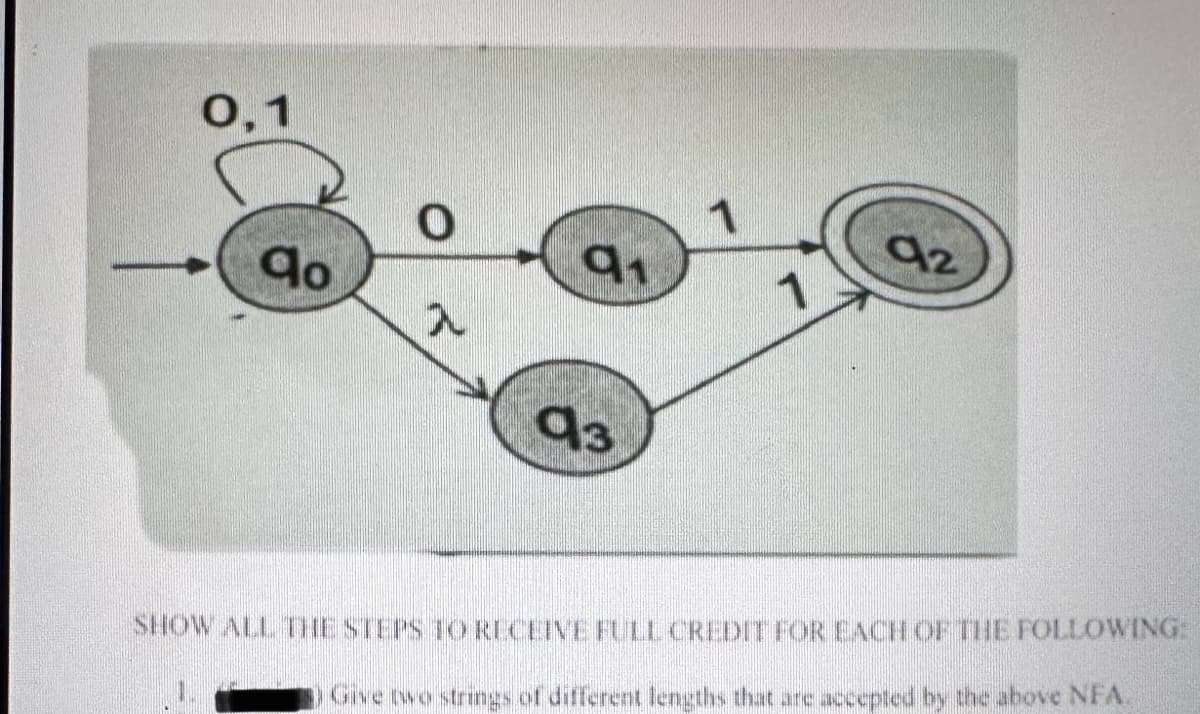
0,1 0 qo 91 入 1 93 92 SHOW ALL THE STEPS TO RECEIVE FULL CREDIT FOR EACH OF THE FOLLOWING: Give two strings of different lengths that are accepted by the above NFA.
Q: Given the following vertex set and edge set (assume bidirectional edges): V {1, 2, 3, 4, 5, 6, 7, 8,…
A: Step 1:Step 2: Step 3: Step 4:
Q: Explain how NoSQL databases can be used in business intelligence.
A: The objective of the question is to understand the application of NoSQL databases in the field of…
Q: For each of the following functions, determine whether the function is: Injective (one-to-one).…
A: A function is bijective iff it is injective as well as surjective. But given function is injective…
Q: The Code Red II worm accomplished rapid infection mainly because of its localized scanning strategy.…
A: The objective of the question is to identify the correct statements about the localized scanning…
Q: An organization is granted the block 108.153.200.40/17. The administrator wants to create 100…
A:
Q: I really need help with this one please, its really hard for me. In Java, could you use all the new…
A: Designing and implementing a Social Media Simulation in Java while incorporating multiple design…
Q: For the circuit shown below, a system of equation can be written: (Rs + R2 + RL1)I1 - RsI2 - R2I3…
A: Step 1: Step 2: Step 3:
Q: Consider a broadcast channel with N nodes and a transmission rate of R bps. Suppose the broadcast…
A: We have given,R=Transmission ratedpoll=Polling delayQ=Transmit polling roundN=NodesPolling and…
Q: Need help ! I have attached the problem! I am taking database management course.
A: Explanation:Each row in the new table represents a unique combination of student ID, student name,…
Q: College of CSIT Database Management System (IS 304) Pharmacy Prescriptions Case Study 1. Problem:…
A: Approach to solving the question: Approach to Designing the Pharmacy Prescriptions DatabaseThe…
Q: Make a Python Program that solves the attached Probability question.
A: The python program to calculate this probability is given below: import math def…
Q: The script covers all p-code binary operators (or opcodes) that may introduce data flow. true or…
A: Approach to solving the question: Script Detailed explanation: Examples: Key references: P-code,…
Q: Build a solution for the 0-1 Knapsack problem using backtracking algorithm. We have 5 items with…
A: The 0-1 Knapsack problem is a classic optimization problem where you have a set of items, each with…
Q: A sender sends binary data 101011111001110. The checksum has eight bits length, what is the checksum…
A: 1. **Splitting the data into groups of 8 bits**: The binary data provided is 101011111001110. We…
Q: Could you assist me with this question? I'm having difficulty understanding how to approach it and…
A: **Proof for 4.30**Consider the language A as described, where A is Turing-recognizable and consists…
Q: Provide the full C++ main.cpp, mystring.cpp and mystring.h. Part of the output is provided below
A: Step 1:Extraction Operator (>>): This operator reads input into a temporary non-dynamic array,…
Q: The code a programmer writes to catch a run-time error is called_____handling.
A: The objective of the question is to identify the term used to describe the code that a programmer…
Q: The script covers all p-code unary operators (or opcodes) that may introduce data flow. true or…
A: False. P-code refers to an intermediate representation of code used in compilers. Unary operators…
Q: Generate H (Hilbert Matrix) for n = 15.Compute the right-hand size vector b = Hx so that the exact…
A: The code generates a 15x15 Hilbert matrix, constructs the right-hand side vector `b` such that the…
Q: Don't use AI to do it.Given the modified single-cycle processor shown below, what are the values (in…
A: To determine the values of the main control signals and other processor components at 1950 ns in the…
Q: A Python Program with 10 menu choices. program could answer 1. Which states did not present data?2.…
A: I have provided the comments in the code so that you can easily…
Q: Consider the following problem: 1. You have a four-gallon jug and a three-gallon jug, neither of…
A: The water jug problem is resolved by this Prolog program by specifying the starting and end states…
Q: What is Enterprise Architecture? Is Enterprise architecture dead?
A: Is Enterprise architecture dead? Enterprise architecture is not dead and it promotes using the…
Q: Find solution to this question on memory hierarchies in computer structures (Refer to the…
A: A.) Block Offset: This is determined by the size of the cache block. Each block in the cache is 64…
Q: Consider alphabet Σ = {0,1,2,3} and language L = {w€Σ* : w = 0"1" 2" 3" for some positive m‚n € or…
A: Claim: The language L = {w ∈ Σ* : w = 0^m 1^n 2^m 3^n for some positive m, n ∈ Z} is not…
Q: Help for the question.Question 5a) For the single-cycle processor, what are the values (in binary)…
A: ## Understanding Single-Cycle Processor Behavior and Signal Decoding at a Specific TimeA…
Q: Problem 2. The multiplicative inverse of an integer x modulo N where x and N are coprime (mutually…
A: The problem at hand is to find the multiplicative inverse of an integer `x` modulo `N`, where `x`…
Q: 16. An artificial neuron is also know as a(n) _____ . A) element B) trinatron C) perceptron…
A: An artificial neuron, also known as a perceptron, is a computational model that is inspired by the…
Q: I am trying to run a jar file and I get this error. Error encrypting/decrypting file…
A: Examples: Let's explore additional examples and potential fixes for the "Invalid AES key length"…
Q: Check the screenshot to solve this question on memory hierarchies in computer structures ;
A: Step 1: 1 word = 64 bit =8 B Main memory = 8GB=1 G words Each block of…
Q: Please help me with these question. SHow all you work. Thank you 1. Prove that∀k ∈ N, 1k + 2k + · ·…
A: The first question is asking to prove that the sum of the kth powers of the first n natural numbers…
Q: A standard deck of playing cards consists of 52 cards. Each card has a rank and a suit. There are 13…
A: To find the probability of getting four cards of one suit and five cards of another suit in a hand…
Q: For the given 2-3 tree: Add node 65 Remove node 20 50 90 120 150 30 40 60 80 100 110 130 140 160 ?
A:
Q: Test Analyze Tools Extensions Window Help Search (Ctrl+Q) Debug Any CPU Start File Edit View Git…
A: Based on the code snippet provided, here's a more complete version of the `CarReturn` method,…
Q: How to write verilog for a three state counter state machine and the testbench
A: To write Verilog for a three-state counter state machine and its testbench, you can follow these…
Q: Q2 The Powerball Lottery 15 Points The Powerball lottery is based on a random drawing of six balls…
A: To calculate the probability of winning $100 by matching exactly four of the first five numbers (in…
Q: 4. What does this function return? Which principle does it illustrate?
A: The result of the 'f2' function is '100'. It serves as an example of the lexical scoping concept. R…
Q: Suppose a program have 40% of its code enhanced to yield a system speedup of 4.3 times faster. What…
A: Approach to solving the question: Detailed explanation: Examples: Key references: computer science
Q: ⚫ Each prescription is exclusive to a doctor. However, each doctor may compose a large number of…
A: ### 1. Conceptual Database Design: #### Entities: 1. **Doctor**: Represents the medical…
Q: 1. Let Σ be an alphabet. Prove or disprove that for every language L over alphabet Σ, if L² = L,…
A: . Language Fundamentals:Alphabet (Σ): Imagine a set of building blocks, like {a, b} for a-b-c words.…
Q: Just want answer
A: Understanding CFG, PDAs, and Transitions: Demystifying the OptionsThis prompt delves into the…
Q: What is data defination, data dictionary and data manipulation language (SQL) and with example in…
A: Data DefinitionData definition involves specifying, structuring, and managing the creation and…
Q: Consider the graph shown in Figure 2 consisting of vertices 1, 2, .., 9. Construct a matrix with 9…
A: To construct the matrix with the distance results of Dijkstra's algorithm for each iteration, we…
Q: When using AWS Identity and Access Management (IAM), what is the recommended best practice with your…
A: let's go through each option:A. Delete your account root user access keys (Correct): This option is…
Q: In TSSST switch (where SSS stands for a three-stage space-division switch) with N=150. It is used…
A:
Q: Hello. Please answer the attached Operating Systems question and its two parts correctly and…
A: Part B: Deadlock Possibility with Two Processes and Three Identical ResourcesIn a system with two…
Q: . Given the following graph: List the vertex set List the edge set Show the adjacency list…
A: Step 1:Vertex set : { 5, 11, 2, 7, 8, 9, 10, 3} Step 2:Edge set : { (5,11), (11,2), (7,11), (7,8),…
Q: Could you assist me with this question? I'm struggling to understand how to approach it and…
A: The question asks for the number of dominoes needed to form a specific pattern. The pattern is shown…
Q: This is a lesson from applied cryptography (institute of information security)
A: Determining the Group's Order: Firstly, we must determine the Zag×23Zag×23 group's order, which is…
Q: can you help me with this:
A: To calculate the total path cost to each of the cities connected to Arad (Sibiu, Timisoara, and…
Step by step
Solved in 2 steps

- 7 Answer f,g and h you are obligated to answer 3 subparts(c) Compute the percent decline or increase in the mobile website visitors, write a formula in cell E26 and copy to cell E27. (d) In cell F26, Use the IF Function to create a formula to print "Yes" if there is cannibalization; else, the formula should print "No". Copy the formula to cell F27.Hint: If the percent increase is negative then there is cannibalization, else there is no cannibalization. Screenshot is attached below thx!!In C++, Also don’t forget to covert term and rate to month before calculating the monthly payment.
- A system administrator gives each new user a new password using 7 pieces of password he has previously determined. These parts are used as 1- “Ma +”, 2- “Ge *”, 3 - “! Se”, 4- “E? S”, 5- “As”, 6- “A3n”, 7- “E / m”. has determined. Write the function named PasswordYaz, which puts the password on the screen by randomly bringing together the desired number of pieces as much as the number of passwords, in accordance with the following main function. The function should determine random passwords according to the number of passwords sent to it and the number of pieces in each code and print them on the screen. (Be sure to use the prototype) in cplease can you check check my code? c++(turboC) #include<stdio.h>main(){int eno;char enam[20],sc,pc,s,p;float nhw,rph,gp,ot,sss,med,wtax,ins,td,np;clrscr();printf("Enter EMPLOYEE NO.:");scanf("%d",&eno);print("Enter EMPLOYEE NAME:");scanf("%s",&enam);printf("Enter STATUS CODE:");sc=getche();printf("\nEnter POSITION CODE:");pc=getche();printf("\nEnter NO. OF HRS. WORKED:");scanf("%f",&nhw);printf("\nEnter RATE PER HOUR:");scanf("%f",&rph);clrscr();gotoxy(38,2);printf("ABC Company");gotoxy(39,3);printf("Cebu City");gotoxy(35,6);printf("*** PAY SLIP ***");gotoxy(10,9);printf("EMPLOYEE NO. : %D",eno);s=toupper(sc);switch(s){case 'S' : gotoxy(50,9); printf("STATUS: Single"); break;case 'M' : gotoxy(50,9); printf("STATUS: Married"); break;case 'H' : gotoxy(10,11); printf("POSITION: Department Head"); break;case 'C' : gotoxy(10,11); printf("POSITION: Officer in Charge"); break;defualt : gotoxy(10,11);…Rewrite the following WHERE clause without the use of the IN special operator: WHERE V_STATE IN (TN, FL, GA)
- Please, write code in C++ The Nobel peace prize is awarded to persons who excel in various fields of endeavor. Currently only a handful of panel members determine and choose people who qualify for a particular award based on nomination from a wide range of disciplines’. This process of selecting the winners for the various prices have been criticized as being biased especially from the side of the panel members. The committee of experts at a general council meeting decided to automate the selection process. On a trial bases, you have been engaged to develop a system that will automatically select a nominee as the winner of the award in two categories (peace and science). Your program should have the following functionalities. a) You are to define a class named NobelAward. Your class must have two functions, one of the functions should be named AwardCategory, and the other function should be named AwardWinner. Your AwardCategory must have a string argument and return the string when…complete the following cose to calculate the average salary using the while loop in the razor page? @{ [ ] salary = {555.2,678,700,545}Use ( C++) please
- (n) Using the SUMIFS function, write a formula in cell F64 to compute Small & Spot servers' average total cost. Copy the formula down to cells F65 to F69. (o) Using the COUNTIFS function, write a formula in cell G64 to compute the total number of Small & Spot servers rented. Copy the formula down to cells G65 to G69. Screen shots attached below thank you!!Write a C++ code to check whether a string is a valid password. Password rules:A password must have at least ten characters.A password consists of only letters and digits.A password must contain at least two digits. Expected Output: 1. A password must have at least eight characters. 2. A password consists of only letters and digits. 3. A password must contain at least two digits Input a password (You are agreeing to the above Terms and Conditions.): abcd1234 Password is valid: abcd1234a. In cell H4, create a formula using the IF function that tests whether the value in the Bundled column ([@[Bundled?]]) is "Yes". b. If the value in the Bundled column is Yes, subtract 10 from the amount in the Per Month column ([@[Per Month]]). c. Otherwise, the payment is the same as the value in the Per Month column. d. If necessary, fill the formula to the range H5:H48.









