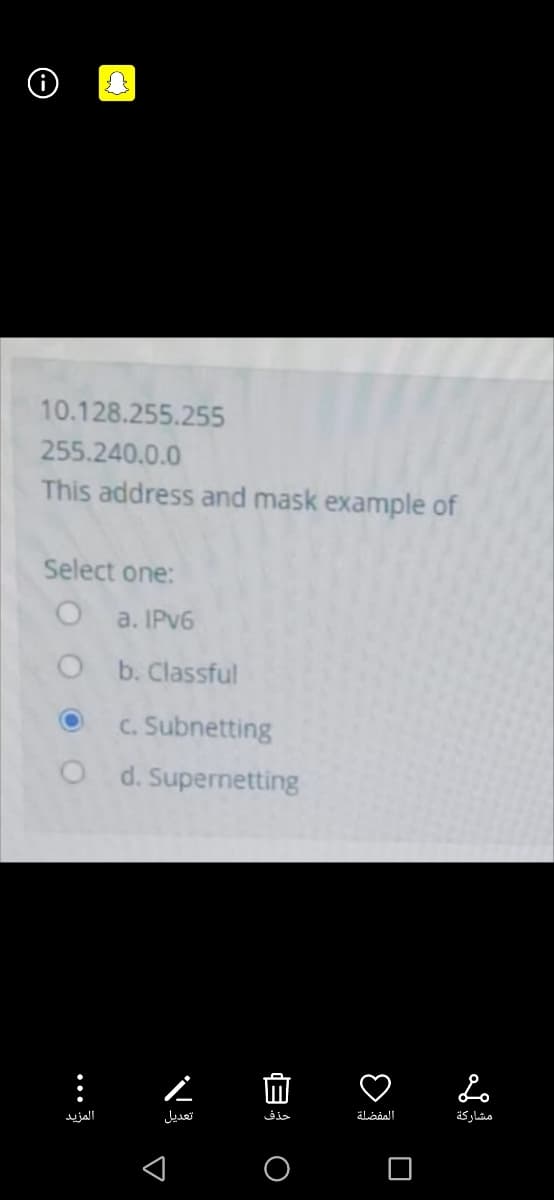
10.128.255.255 255.240.0.0 This address and mask example of
Q: 7- A ROM device has 18 address lines and 8 data lines. What is the byte capacity and storage…
A: Byte Capacity 18 address lines means address range will be 0 to 218 - 1 = 0 to 262143 8 data lines…
Q: A computer provides a virtual memory space of 248 bytes. The computer has 16 GiB of physical memory.…
A: Given, Size of virtual address space = 2 48 Bytes Then, Number of bits used to represent virtual…
Q: How many memory locations does the following memory have? 0
A: Each unit of memory location is 1byte. Now, 3MB = 3145728 bytes. Therefore, 3MB - 1byte = 3145727…
Q: Suppose we define a service routine starting at memory location x4000. This routine reads in a…
A: Given code .ORIG X4000 ; starting address of program ST R7,Save R7 ; save R7 with value 0000…
Q: Virtual Address S ry with page siz size is 4 bytes ar ago the numbo
A:
Q: Which of the following is incorrect with respect to memory management? O The user program deals with…
A: The following statements are true: The user program deals with logical addresses; it never sees the…
Q: Is it permissible to use a virtual address?
A: Introduction: You cannot register a corporation using your virtual address. It's a legal need to…
Q: has 1 G byte of Ram and it has 64 G byte of virtual memory. The page size is 4 K bytes. Disk size is…
A: the solution is an given below :
Q: Problem 6. Nowadays the virtual address is much larger (64 bits) than the physical address space…
A: Answer is given below-
Q: Page size is 4 bytes, page number is 3, frame number is 2, and offset is 8. What is the frame…
A: Solution:
Q: 10. Device fragmentation refers to device that has different OS and API. PART B 1. For Tablet X,…
A: “Since you have posted a question with multiple sub-parts, we will solve first three subparts for…
Q: What does a MAC address look like?
A: What does a MAC address look like?
Q: An address space in the memory map starts at address Ox40000000 and ends at address O×40000FFE. What…
A: Given Starting address = 40000000 Ending address = 40000FFE 40000FFE : 1073745918(decimal number)…
Q: estion 2 A 16-bit computer implementing paging has 16 bit logical addresses and 12 bit physical…
A:
Q: There are “record-once” versions of compact disk and digital video disk, which can be written only…
A: Task :- Choose the correct option for given question.
Q: True or false? Virtual memory uses software to simulate missing blocks of memory
A: Explanation: Virtual Memory: • When there is multiple program, wants to run in the RAM at the same…
Q: Give 10 differences of MAC and Windows
A:
Q: ENTRY :load r6 with 5 (i.e., XX) :load r7 with the contents of location P1²! just a dummy…
A: Hey there, I am writing the required solution of the above stated question.Please do find the…
Q: ithout using LXI command how you will transfer one byte from memory location whose address is 11H to…
A: According to the question we need to answer that without using LXI command how you will transfer one…
Q: Computer Science This question is about paging-based virtual memory A computer has a virtual-momory…
A: In a given computer Virtual - memory size = 250MB Size of Primary Memory = 325 KB = 219 B Page -…
Q: What's the difference between, say, sequential access devices and random access devices?
A: Sequential access and random access are two ways in which data is read or written from say a file to…
Q: A certain computer provides its users with a virtual-memory space of 232 bytes. The computer has 218…
A: Given Virtual address 11123456
Q: 353. Logical Address space can be larger than physical address space. a. True b. False c. May be d.…
A: Asked: . Logical Address space can be larger than physical address space. a. True b. False…
Q: 32 Which of the following ranks highest (smallest, most expensive, fastest access, most frequently…
A: Which of the following ranks highest in the memory hierarchy? a)Cache L3 b)Cache L1 c)CD-ROM…
Q: An address space in the memory map starts at address Ox84000000 and ends at address O×8400FFFF.What…
A: Here in this question we have given address of starting and ending in memory map..and we have asked…
Q: Demonstrate the following Unix/Linux commands in the lab or your personal computer and paste the…
A: Hey there, I am writing the required solution based on the above given question. Please do find the…
Q: Which is wrong about virtual memory: o Swapping when there is no hit in main memory o A page fault…
A: Which is wrong about virtual memory: o Swapping when there is no hit in main memory o A page…
Q: onsider a computer system with a 24-bit logical address and a 28-bit physical address. Let's pretend…
A: The 24 bit logical address would be divided as 2nd level PT 1st level PT page offset
Q: The time required to access a page in primary memory is 15 ns. The average time required to access a…
A: The answer is
Q: On some operating system, the LA is 24 bits, the page size is 1024 bytes. If the page table entry is…
A: Here we have given LA=24 bit Page size=1024 byte Page table entry =3 byte So to calculate page…
Q: How many bits are required for addressing (i.e. what is the size, in bits, of an address)? 30 bits O…
A: Given word size = 32 bit Total opcodes =66 Total registers =64 Total size of byte addressable memory…
Q: write APL for read byte from input port at address BOOOH and then output byte AAH at address B2H *…
A: Program Address HEX Codes Labels Mnemonics Comments F000 21, 00, 80 LXI H,8000H Load…
Q: True or false? Overlays are an obsolete technique used when system memories were very small and are…
A: Overlays : + Overlays denotes the process of inserting a block of computer code or other data into…
Q: What's the difference between a reserved and a private address?
A: Introduction to address An address always points to a host/node/server or it can represent a whole…
Q: Is there any difference between MAC address and hardware address?
A: The question is to know if there difference between MAC and hardware address.
Q: onsider a virtual memory system that can address a total of 32 bytes. You have unlimited hard disk…
A: Given the size of each page, it is known that the size of each page is same as the size of each…
Q: أذكر 3 تطبيقات ميدانية مختلفة للهياكل المنفصلة في علوم الكمبيوتر؟ بالنسبة لشريط الأدوات ، اضغط على
A: Discrete structures is an integral part of computer science.
Q: a) How many bits are in a virtual address? b) How many bits are in a physical address? c) What…
A:
Q: Which part of the MPU generates the physical address? boot program BIU ALU…
A: CORRECT OPTION: Which part of the MPU generates the physical address? BIU EXPLANATION: BIU stands…
Q: Define boot partition
A: Answer: A Windows boot partition is the partition that holds the necessary files for the Windows…
Q: Q6 Hack memory-mapped I/O Fill the blanks The base RAM address for the Hack Screen memory map is…
A: The base RAM address for the Hack Screen memory map is 16384. The function pixel_clear (row, col)…
Q: With and without using LXI command how you will transfer one byte from memory location whose address…
A: According to the question we need to answer that with and without using LXI command how you will…
Q: Q3) A address space is specified by 34 bit and corresponding memory space by 23 bit. 1- How many…
A: Given Data :Address space specified by 24 bitsMemory space specified by 16 bits Need to calculate…
Q: What is a virtual address, and how does it become a physical address
A: Virtual address is logical address and it is created by CPU that doesn't exist in real. It is…
Q: (MAC) In the MAC address table, MAC addresses are stored in a dynamic RAM. Assume the table was 8000…
A: Time Required for Memory Access Memory Access Time is the time required to identify and retrieve a…
Q: 38 Computer Science VMware's term for assigning a group of users to a role is "granting a ____".…
A: Answer :
Step by step
Solved in 2 steps

- Make 17 subnet of 145.68.69.0/24.And give all the information like broadcast address , range..etc. 2 subnet of size 9 . 5 subnet of size 67 7 subnet of size 59 3 subnet of size 91. I will award u 20 dislikes, do not copy paste. Better for u to leave it. Skip it.2.1 Bob and Alice are classmates who are studying at university of Limpopo doing their final year studies in Computer Science.Due to the ongoing pandemic of covid 19, lectures are virtual.However they have choosen not to attend virtual class but download class recordings.Discuss the process of getting the videos to play on their media player after downloding. In your explanation include all the protocols involved.1-In a network based on the bus topology, the bus is a non-shareable resource for which the machines must compete in order to transmit messages. How is deadlock controlled in this context? 2-Using 32-bit Internet addresses was originally thought to provide ample room for expansion, but that conjecture is not proving to be accurate. IPV6 uses 128-bit addressing. Will that prove to be adequate? Justify your answer’ (for example, you might compare the number of possible addresses to the population of the world).
- ) s ®%74 I, 10.100.100.1is a valid host address * QO Yes O No -4 0 G 9:09 Which is not true about Class C addresses (select more than answer) * the first byte between 192 - 224 the number of hosts is less than subnets Many addresses are wasted the address space is 53687191 address the first byte starts with 110 Map the following addresses to its right class * 192.168.6.7 128.0.10.10 127.0.100.100 O O 'O 190.0.255.255 is a Class B special address * QO True Q False Back Next Never submit passwords through Google Forms, O O © O @) @ This form was created Inside of Alnukhba University College. Report Abuse Google FGiven a Class C subnet Mask 255.255.255.192. what will be the subnet address and host number for a machine with IP address 197.1.2.67. Select one: a. second subnet and host 2 b. Third subnet and host number 3 c. second subnet and host 4 d. First subnet and host number 3 e. None f. Second subnet and host number 359- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method What will be the subnet mask of Subnet D? Select one: a. 255.255.255.192 b. 255.255.255.248 c. 255.255.192.192 d. 255.255.192.0 e. 255.255.128.255
- Write aprogram to find the ip dotted decimal notation conversion from decimal to binary,octal and hexadecimal and vice versa also find the result of NOT and AND operation of ipv4 adresses. a. 114.34.2.8 Find the result of each operation: a. NOT (22.14.70.34) Find the result of each operation: a. (22.14.70.34) AND (255.255.0.0) ALso develop a program to find classes of ip adress and first and last address,subnet mask also. Develop in javaConsider the following page address stream: 2 1 4 3 5 3 2 4 5 2 1 2 4 3 1 Which of the following causes the most page faults to occur on a machine with 3 frames? Scheme that causes the most faults: a) First in First out b) LRU and FIFO are the same number of faults c) FIFO and Opitimal are the same number of faults d) All have the same number of faults e) Least Recently Used f) No faults occurs g) LRU and Optimal are the same number of faults h) Optimal NUMBER OF FAULTS CAUSED: a)56- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the subnet mask of Subnet C? Select one: A. 255.255.128.255 B. 255.255.192.0 C. 255.255.255.240 D. 255.255.255.192 E. 255.255.255.128
- Computer Science To answer this question, you may need to write a small program. Consider the following case: current cwnd value is 1000 bytes and 1 MSS is 10 bytes (=1 TCP packet carries 10 bytes of payload). With the basic formula, after 1 RTT, the congestion window would be updated to 1010 bytes (1000 + 10). What would be the value of window if ACK clocking is used? It would be a non-integer number, so give value including only two digits after comma7.1 In IEEE 802.11, open system authentication is accomplished via a simple two-way communication. The client requests authentication, which includes the station ID, which is provided by the server (typically the MAC address). A successful or unsuccessful authentication response from the AP/router is received in response to the previous request from the client. For instance, if the client's MAC address has been expressly omitted from the AP/router setup, a failure may occur.a. What are the advantages of using this kind of authentication scheme?b. What are the security flaws in this authentication method and how may they be mitigated?21.) Consider the following configuration. Computer “A” IP address: 172.16.100.100 Subnet mask: 255.255.0.0 Computer “B” IP address: 172.16.200.200 Subnet mask: /16 What should be done to allow these computers to send and receive data to and from each other? A.) Nothing needs to be changed. B.) Delete the subnet mask from each computer. C.) A router must be configured and placed between the two computers. D.) Remove the hub between the two computers and replace it with a switch.











