4. The Ackermann function is a fast-growing function that takes two nonnegative integers: m and n, and the algorithm is defined as below: A(m, n) = n + 1 if m=0 = A(m-1, 1) if n = 0 = A(m-1, A(m, n-1)), otherwise Write this function in C++ and test the function by calling it from main by using a nested loop, by varying m = 0 to 3, and inside the m loop, use another loop to vary n from 0 to 10 The program should display a table for all Ackermann numbers generated as below: m/n 0 2 3 1 4 5 6 7 8 9 0123 The inside of the table the computed A values must be displayed. 10
4. The Ackermann function is a fast-growing function that takes two nonnegative integers: m and n, and the algorithm is defined as below: A(m, n) = n + 1 if m=0 = A(m-1, 1) if n = 0 = A(m-1, A(m, n-1)), otherwise Write this function in C++ and test the function by calling it from main by using a nested loop, by varying m = 0 to 3, and inside the m loop, use another loop to vary n from 0 to 10 The program should display a table for all Ackermann numbers generated as below: m/n 0 2 3 1 4 5 6 7 8 9 0123 The inside of the table the computed A values must be displayed. 10
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter5: Repetition Statements
Section5.5: A Closer Look: Loop Programming Techniques
Problem 12E: (Program) Write a program that tests the effectiveness of the rand() library function. Start by...
Related questions
Question
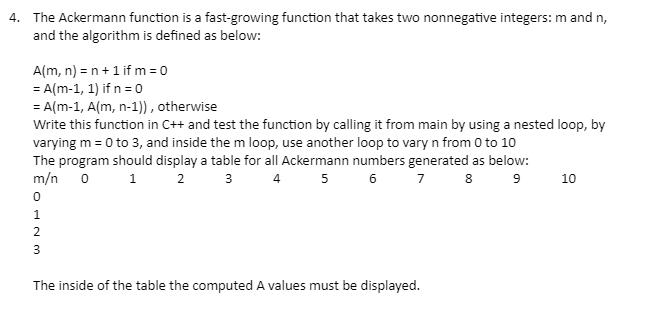
Transcribed Image Text:4. The Ackermann function is a fast-growing function that takes two nonnegative integers: m and n,
and the algorithm is defined as below:
A(m, n) = n + 1 if m=0
= A(m-1, 1) if n = 0
= A(m-1, A(m, n-1)), otherwise
Write this function in C++ and test the function by calling it from main by using a nested loop, by
varying m = 0 to 3, and inside the m loop, use another loop to vary n from 0 to 10
The program should display a table for all Ackermann numbers generated as below:
m/n 0
6 7 8 9
1 2
3
4 5
0
1
2
3
The inside of the table the computed A values must be displayed.
10
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 2 images

Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr