
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
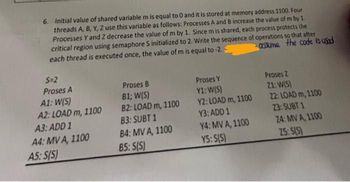
Transcribed Image Text:6. Initial value of shared variable m is equal to 0 and it is stored at memory address 1100. Four
threads A, B, Y, Z use this variable as follows: Processes A and B increase the value of m by 1.
Processes Y and Z decrease the value of m by 1. Since m is shared, each process protects the
critical region using semaphore S initialized to 2. Write the sequence of operations so that after
each thread is executed once, the value of m is equal to -2.3
assume the code is used
S=2
Proses A
A1: W(S)
A2: LOAD m, 1100
A3: ADD 1
A4: MV A, 1100
A5: S(S)
Proses B
B1; W(S)
B2: LOAD m, 1100
83: SUBT 1
B4: MV A, 1100
85: S(S)
Proses Y
Y1: W(S)
Y2: LOAD m, 1100
Y3: ADD 1
Y4: MV A, 1100
Y5: S(S)
Proses 2
21: W(S)
22: LOAD m, 1100
23: SUBT 1
24: MV A, 1100
25: S(S)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps

Knowledge Booster
Similar questions
- yyhhjjarrow_forwardTwo threads inside the same process are compared to two independent processes. How do you know when is the right time to act?arrow_forwardIn Python code: Put the thread_function on a thread. Put 3 threads into a queue and run the threads. import queuequeue = queue.Queue def thread_function(name): print("Thread %s: starting", name) time.sleep(2) print("Thread %s: finishing", name) # start threads by passing function to Thread constructorfrom pprint import pprintimport threadingimport time def threadfunc(*t): print(">>>>",*t) time.sleep(1) print('[',*t,']') time.sleep(2) print("<<<<",*t) arg1 = ("AAAAAAAA")threadA = threading.Thread(target=threadfunc,args=arg1)threadA.start() arg2 = ("BBBBBBBB")threadB = threading.Thread(target=threadfunc,args=arg2)threadB.start() arg3 = ("CCCCCCCC")threadC = threading.Thread(target=threadfunc,args=arg3)threadC.start() threadA.join()threadB.join()threadC.join() # multiple threadsimport threadingimport time tnames = ('AAAAAAAA','BBBBBBBB','CCCCCCCC')count = len(tnames)threadlist = []count = 3 def threadfunc(*t):…arrow_forward
- Which is an example of statement-level concurrency? the manufacturer states that there are multiple processors on achip, but there is actually only one instructions are fetched form memory while previous instructions run a loop the performs the same operation on 500 array elements is split into five threads that perform the operation on 100 array elements each five threads that with loops that perform the same operations on 100 elements each from the same array are combined into one threadarrow_forwardWhich of the following components of program state are shared across threads in a multi-threaded process? (a) Register values (b) Heap memory (c) Global variables (d) Stack memoryarrow_forwardOCCURS WHEN MULTIPLE PROCESSES OR THREADS READ AND WRITE DATA ITEMS SO THAT THE FINAL RESULT DEPENDS ON THE ORDER OF EXECUTION OF INSTRUCTIONS IN THE MULTIPLE PROCESSES, Select one: a.COMPETING PROCESSES b.CRITICAL SECTION c.MUTUAL EXCLUSION d.RACE CONDITIONarrow_forward
- Developing a program using two threads instead of one doubles the program performance (e.g., it will run in 10 ms instead of 20) True Falsearrow_forwardA condition variable is an object able to the calling thread until notified to resume. block terminate start mutexarrow_forwardThink about a problem that might arise when the operating system of a computer employs many threads to do the same operation.arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education