A password is considered strong if the below conditions are all met: • It has at least 6 characters and at most 20 characters. • It contains at least one lowercase letter, at least one uppercase letter, and at least one digit. • It does not contain three repeating characters in a row (Le., "...aaa..." is weak, but "..aa..a..." is strong, assuming other conditions are met). Given a string password, return the minimum number of steps required to make password strong. if password is already strong, return e. In one step, you can: • Insert one character to password, • Delete one character from password, or • Replace one character of password with another character. Example 1: Input: password - Output: 5
A password is considered strong if the below conditions are all met: • It has at least 6 characters and at most 20 characters. • It contains at least one lowercase letter, at least one uppercase letter, and at least one digit. • It does not contain three repeating characters in a row (Le., "...aaa..." is weak, but "..aa..a..." is strong, assuming other conditions are met). Given a string password, return the minimum number of steps required to make password strong. if password is already strong, return e. In one step, you can: • Insert one character to password, • Delete one character from password, or • Replace one character of password with another character. Example 1: Input: password - Output: 5
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter19: Probabilistic Dynamic Programming
Section19.4: Further Examples Of Probabilistic Dynamic Programming Formulations
Problem 7P
Related questions
Question
Computer Engineering Lab
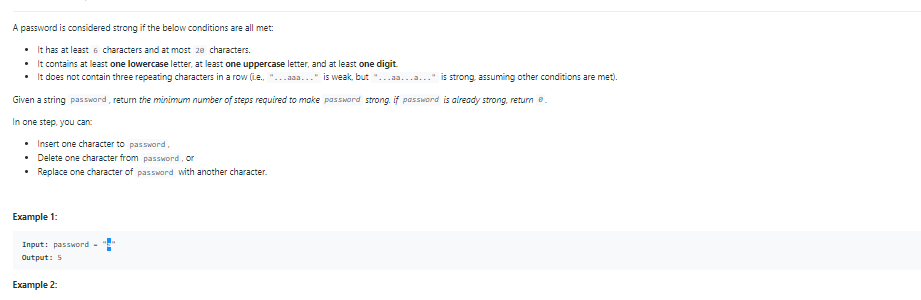
Transcribed Image Text:A password is considered strong if the below conditions are all met:
• It has at least 6 characters and at most 2e characters.
• It contains at least one lowercase letter, at least one uppercase letter, and at least one digit
• It does not contain three repeating characters in a row (Le. "...aaa..." is weak, but
is strong, assuming other conditions are met).
Given a string password, retum the minimum number of steps required to make password strong. if password is aiready strong, return e.
In one step, you can:
• Insert one character to password,
• Delete one character from password, or
• Replace one character of passMard with another character.
Example 1:
Input: pasSword -
Output: 5
Example 2:
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole