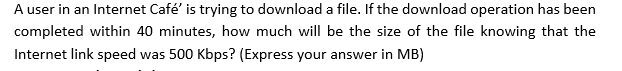
A user in an Internet Café' is trying to download a file. If the download operation has been completed within 40 minutes, how much will be the size of the file knowing that the Internet link speed was 500 Kbps? (Express your answer in MB)
Q: UDP-based application to send data reliably?
A: ANSWER: UDP (User Datagram Protocol): UDP utilizes a straightforward transmission model that does…
Q: DO NOT COPY FROM OTHER WEBSITES Upvote guarenteed for a correct and detailed answer. Thank you!!!
A:
Q: You download a file of size 180 Gbyte in one hour. What is the average goodput (the useful…
A: Solution: As per Bartleby we can answer only one question's at a time so, if you need remaining…
Q: 6. Given the IP address 153.36.147.82 and assuming 4 bit subnetting, answer the following questions.
A: 153.36.147.82 = 10011001 00100100 10010011 01010010 Ans A) 153 belongs to Class B. Class B mask :…
Q: A client sends a 128-byte request to a server located 100 km away over a 1-gigabit optical fiber.…
A: I have provided a solution in step 2.
Q: Consider the LFSR represented by the polynomial x* + x* + x² + x + 1. What are the tap bits of the…
A: To Find: The tap bits of the given LFSR represented by the polynomial, x4 + x3 + x2 + x+ 1.
Q: In SMTP, a non-ASCII message of 1000 bytes is encoded with base64. a. How many bytes are in the…
A: Given:- The size if non-ASCII message = 1000 bytes 1 byte = 8 bits The…
Q: Which of the following statements is/are correct? I. The fragmentation is applicable for data in the…
A: Defined the correct statements from the given statements
Q: Q 1. (a) Data are transmitted over a particular Ethernet network in blocks of 1500 bytes. How many…
A: Actually, 1 byte = 8 bits.
Q: Suppose Ethernet physical addresses are chosen at random (using true random bits). (a) What is the…
A: Introduction: Apply the birthday problem to decide the probability of two addresses in the network…
Q: Which layer of the ISO/OSI Reference Model would be responsible for encryption or compression during…
A: Given: Which tier of the ISO/OSI Reference Model would be responsible for delivering this service if…
Q: Which of the following doesn't correspond to the network layer data plane function? A Dropping a…
A: Computation or population of forwarding table is done by control plane hence The correct answer is D…
Q: -Which of these are valid and which are invalid to assign to hosts. List the reason for each.…
A: 192.168.238.255/24 -> invalid because .255 belongs to the broadcast IP address, it cannot…
Q: Suppose Ethernet physical addresses are chosen at random (using true random bits). (a) What is the…
A:
Q: Suppose Ethernet physical addresses are chosen at random (using true random bits). (a) What is the…
A: * As far bartleby guidelines, I answer first-sub question (a) in the multiple sub questions in that…
Q: Forwarded Suppose Host A wants to send a large file to Host B. The path from Host A to Host B has…
A: a) Consider givend data:R1 =3 Mbps, R2 = 2 Mbps, and R3 = 1 Mbps The throughput for the file…
Q: Assume that a client can use UDP to obtain a file from a distant server at a known address. The…
A: Intro UDP : The transport layer protocol User Datagram Protocol (UDP) is a connection-less-oriented…
Q: !!!! R3 What is the maximum end-to-end throughput achieved by each session, assuming both sessions…
A: It is defined as how much data can be transferred from source to destination within a given…
Q: on is m, then the sequen
A: Solution - According to Bartleby policy, I can only answer first three questions (i.e 9,10 and 11).…
Q: Find the physical address in memory if IP = 1234h, and CS = 1000h
A: given, IP= 1234h CS=1000h formula to find physical address in memory- Physical address = base…
Q: 1. Suppose Host A wants to send a large file to Host B. The path from Host A to Host B has three…
A: Here i have prepared written solution as follows:
Q: (and two switches) between A and B, and the links are uncongested (that is, no queuing delays). Host…
A:
Q: If a communications session needed encryption or compression, which layer of the ISO/OSI Reference…
A: Introduction: ISO/OSI is an abbreviation for international standard organization/open system…
Q: It is feasible to transmit a sequence of packets from one host to another using the same path…
A: Start: Delays in transmission, processing, and propagation are all constant. The time it takes to…
Q: If a communications session were to employ encryption or compression, which layer of the ISO/OSI…
A: To be determine: If a communications session were to employ encryption or compression, which layer…
Q: 47. Which of the following is not associated with the session layer ? a. Dialog control b. Token…
A: Given: Which of the following is not associated with the session layer ? a. Dialog control b.…
Q: SO/OSI Reference Model would be responsible for encryption or compression during a communication…
A: SUMMARY OSI Reference ModelSession- The fifth layer of the OSI model, which is responsible for the…
Q: 78. Each LAN type has its own strategy in the sending of a. Bits b. Bytes c. Data d. Frames
A: please see the next step for answer.
Q: Let X and Y be the number of 1's in the binary notation of network ID and Direct Broadcast Address…
A: Here in this question we have given an ip address and we have asked to find the no of 1s in network…
Q: What is the total average delay for receiving a message when no cache is used, i.e., the sum of LAN…
A: Given Data : Length of message , L = 7 Speed , X = 180 Mbps Message arrival rate, B = 6 messages /…
Q: Suppose Ethernet physical addresses are chosen at random (using true random bits). (a) What is the…
A: Introduction Apply the birthday problem to conclude the probability of two addresses in the network…
Q: Why do we have to multiply the offset field of an IP datagram by eight to obtain the real offset for…
A: answer is
Q: If CS= 24F6 H and IP= 634A H show: - The logical address. - The offset address. And calculate: - The…
A: solution is given below:
Q: Two keywords can be used in ACL to replace the address or the wildcard mask. O Host and some O Host…
A:
Q: B) IP address 200.172.138.62 11001000.10101100.10001010.111110 Subnet 255.255.255.240 11111111.…
A:
Q: Q3: Find the netid and the hostid of the following IP addresses. Explain the complete logic? a.…
A: Computer network: A group of computer system or computer nodes that are connected to each other and…
Q: In NAT, users in the same local network have internally the same IP addresses and they are…
A: Network address transalation basically searches the translation table based on the destination port…
Q: s] Using 5-bit sequence numbers, what is the maximum size of the send and receive windows for each…
A: Given 5- bit sequence numbers we have to find maximum size of sender window and receiver window for…
Q: A file of size 20 KiloBytes is transmitted to a destination over a 10 Megabit/s network link (1 Mega…
A: File size, L = 20Kb = 20 * 103 bytes = 20 * 103 * 8 bits = 1.6 * 105 bits Bandwidth B = 10Mbits/s =…
Q: A large number of consecutive IP address are available starting at 192.16.0.0. Suppose that four…
A: 1) For 7000 addresses => 7000/256=28 hence Hence Address range is 192.16.0.0 to 192.16.27.255/19…
Q: A user in Beirut, connected to the internet via a 2 Kbps connection retrieves a 25 Kbytes web page…
A: With non-persistent HTTP, there is one TCP connection for the page and one for each one of…
Q: TCP sessions are full-duplex, which means that data can be sent in either direction during the…
A: sender will send the data to receiver and set SYN bit on. receiver will receive the data and send…
Q: True or false? Suppose Host A is sending a large file to Host B over a TCP connection. If the…
A: The sequence number of the subsequent segment depends on the number of 8-byte characters in the…
Q: Consider the LFSR represented by the polynomial x4 + x² + x + 1. What are the tap bits of the LFSR?…
A: LFSR is a Linear Feedback Shift Register. Its input bits are usually driven by the XOR gates. In…
Q: A large population ALOHA user manages to generate 50 request/sec, including both originals and…
A: To find: To find the chance of success, probability, and the number of transmissions from the given…
Q: Write down a relationship that represents the effective end-to-end throughput that can be achieved…
A: throughput: it is the amount of data moved successfully from one place to another in a given time…
Q: Q4: Full the blank of the following sentences 1- If the destination of packets is at another system…
A: We need to answer questions related to network and LAN. ***As per the guidelines only 1st 3…
Q: In NAT, users in the same local network have internally the same IP addresses and they are…
A: Network Address Translation (NAT) is a method of representing an entire group of computers with a…
Q: When host A receives a TCP segment from host B, the values of the advertised window and the window…
A: TCP: It is used for organizing data in a way that ensures the secure transmission between the…
Step by step
Solved in 2 steps

- Suppose that R = 1 Gbps and Rc is 300 Mbps and Rs is 200 Mbps. Assuming that the servers are sending at their maximum rate possible, enter the link utilization of the shared link, whose rate is R, below. Enter your answer as a decimal, of the form 1.00 (if the utilization is 1, or 0.xx if the utilization is less than 1, rounded to the closest xx).What is the data transmission time to send a 20 GiB file over a link with a 1 Gbps line rate? You can assume there is no overhead. (Show your work)A sender and a receiver are connected by two routers as shown. The bandwidth of each link is 1,000,000 Bytes/sec and the propagation delay for each link is 0.1 msec. A file size of 1000 bytes needs to be transferred from source to destination. Calculate the total time taken to transfer the file if message switching is used. enter only the value and not any units. For example, If your answer is 10.4 msec, just enter the value 10.4.
- Calculate total time (in milliseconds) required to send a file of size of 8000 Bytes. Assume RTT (round trip time) of 80 milli second on a link with bandwidth of 0.8 x106bits /second and a packet size of 1000 Bytes where after sending each packet we must wait one RTT before sending the next packet.Skype is a well‑known VoIP system used not only for peer‑to‑peer conversations but also for audio and video conferencing involving three or more callers. Assume a video conference with a central server on Skype has N callers, and each caller generates a constant data stream at rate r bps. How many bits per second does the call initiator need to send? How many bits does each of other N‑1 callers need to send?Calculate total time (in milliseconds) required to send a file of size of 8000 Bytes. Assume RTT (round trip time) of 80 milli second on a link with bandwidth of 0.8 x106 bits /second and a packet size of 1000 Bytes where after sending each packet we must wait one RTT before sending the next packet.
- Computer A uses the Go-back-N ARQ protocol to send a 110 Mbytes file to computer B with a window size of 15. Given each frame carries 100K bytes data. How long does it take to send the whole file (the total time taken from A sending the first bit of the file until A receiving the last acknowledgment)? Given that the transmission rate of the link is 500 Mbps and the propagation time between A and B is 15ms. Assume no data or control frame is lost or damaged and ignore the overhead due to header and trailer.If we know a printer's IP address is 200.23.16.202 and subnet mask is 255.255.255.224, then, what's the network ID and host ID of this printer? Write both in the standard dot-decimal format without attaching the subnet mask. ( show the calculation)What is the efficiency if a 100-byte file is transmitted using Ethernet? A 10,000-byte file?
- Suppose Host A wants to send a large file to Host B. The path from Host A to Host B has three links, of rates R1=500 kbps, R2=2 Mbps, and R3=1 Mbps a. Assuming no other traffic in the network, what is the throughput for the file transfer? b. Suppose the file is 4 million bytes. Dividing the file size by the throughput, roughly how long will it take to transfer the file to Host B? c. Repeat (a) and (b), but now with R reduced to 100 kbps.Based on the given block data below, answer the following questions. Hint: First do Google search for ‘packet dump decode’. Then cut and paste the block of data below into the input data section. Then press decode. You will be able to find the answer from the decoding result. Hint Q6: For the payload of the application layer, look at the last few bytes in ASCII. You can use the ASCII character table to manually convert them. If you understanding the layer 4 destination port #, you understand what it is asking for. There is only one kind of information for the port #. Data block to be decoded: 00 11 bc b5 49 40 b8 8d 12 00 0d fa 08 00 45 00 00 37 99 09 00 00 ff 11 ea 9f 0a 07 03 1a 42 aa e8 41 c7 19 00 35 00 23 a3 9e 02 90 01 00 00 01 00 00 00 00 00 00 05 6d 69 74 72 65 03 6f 72 67 00 00 01 00 01 Please answer the following questions after decoded the above data block: Q1: (Layer 4) Protocol is: Q2: Source MAC address: Q3: Destination MAC address: Q4: Source IP address:…1. Suppose two hosts, A and B, are separated by 30,000 kilometers and are connected by a direct link of R = 3 Mbps. Suppose the propagation speed over the link is 2.5 x 108 meters/sec. a. Calculate the bandwidth-delay product, R _ dprop. b. Consider sending a file of 900,000 bits from Host A to Host B. Suppose the file is sent continuously as one large message. What is the maximum number of bits that will be in the link at any given time?

