addElement removeMin () ; addElement addElement removeMin () ; (10) ; (5); (1) ; addElement(45);
Q: vide a quick explanation of the three requisites for an effective and efficient netwo
A: An effective and efficient network:- An effective and efficient network is one that has the capacity…
Q: How many stages are there to developing a web page? Walk me through the process and tell me why each…
A: Hello student Greetings Hope you are doing great. Thank You!!!
Q: Just what is an intrusion prevention system?
A: Intrusion detection and prevention system (IPS): Network security that recognizes and stops detected…
Q: Web developers create content management systems, websites, and other web-based applications,…
A: Web development: The main responsibility of web engineering is the website's design and…
Q: In what ways can people get in touch with one another? Provide an example of a means of…
A: Your answer is given below .
Q: To smooth out data in order to remove noise, use a. ... method. O binning
A: SOLUTION - The correct answer is " (a) binning " To smooth out data in order to remove noise, use…
Q: Assume we have 16-bit (2 bytes) 2's complement system with a 2-bit fractional. Find a decimal…
A: This question is related to computer science, specifically binary numbers and their representations.…
Q: A mobile database may be described in how many words?
A: Given: Explain in three points what a mobile database is. Answer: Physically, mobile information…
Q: When referring to the Von Neumann Cycle, what exactly are the different phases? In what ways do the…
A: Fetch Memory Instructions Conduct ALU operations by decoding instructions and fetching operands.…
Q: Where do von Neumann and Harvard differ most significantly?
A: Answer is
Q: What makes an IDS tick?
A: Intrusion Detection System "IDS" A surveillance system that detects suspicious activity and…
Q: Provide an example of both a local area network and a wide area network, and explain how they vary.
A: Your answer is given below.
Q: Draw and simulate the logic diagrams of (8*3) encoder using NAND gates only.
A: 8:3 encoder: An 8:3 encoder is a digital circuit that takes 8 input signals (A through H) and…
Q: Can we expect any benefits from asynchronously launching our programmes? Where do the flaws lie in…
A: Asynchronous programming is a parallel programming method where little pieces of codes/programs run…
Q: This is due of the incredible capability of modern computers. How did schools come to rely so much…
A: Answer is
Q: EXCEL Use the autofill deature to fill the range B3:E3 with a series of labels for the four quaters…
A: step-by-step instructions on how to use the autofill feature to create a series of labels for the…
Q: hat is the meaning of binary translation? How and when did this become
A: Binary translation is the process of converting executable code from one instruction set to another.…
Q: When added to a web browser, how do add-on extensions function technically
A: A browser extension is a small software module for customizing a web browser. Browsers typically…
Q: In contrast to software engineers, who design programmes for operating systems, web developers focus…
A: Introduction: Web developers and software engineers differ most in their jobs. Web developers…
Q: To what extent does the use of a foreign key ensure database consistency? Is there a particular…
A: Foreign key: A relational database foreign key links data from two relations. It links two relations…
Q: Discuss how important it is to follow a well-integrated change control approach while working on…
A: We must emphasize the value of an effective change control procedure on IT projects. The following…
Q: Reason being, technological progress in computers. It is unclear how long it will take to establish…
A: From their inception, computers have proved dependable, yet they are now pervasive; we could…
Q: What is the definition of the Internet?
A: SOLUTION - What is the definition of the Internet? The Internet is a global network of…
Q: What part does intrusion detection and prevention play in network and cyber security?
A: A network intrusion detection system (NIDS) is crucial for network security since it can identify…
Q: Why and how do we use the Python programming language?Why and how do we use the Python programming…
A: The programming language is the formal computer language that consists of instructions or set of the…
Q: There is a catastrophic flaw in the traditional client-server architecture. Is the answer to…
A: Introduction: The traditional client-server architecture has been the backbone of most computing…
Q: Could you please explain why formal methods should be used while creating software for the medical…
A: Definition: While making decisions, the non-Formal approach to software development frequently polls…
Q: keepass (tool)s used to examine and
A: KeePass is an open-source password manager that provides a secure and convenient way to store and…
Q: Explain what you mean by the word "web application."
A: A Web application (Web app) is an application program that is stored on a remote server and…
Q: Describe the pros and cons of using solid-state secondary storage devices as opposed to magnetic…
A: Introduction: Data is stored on a disc using magnetic storage, a type of storage medium. In terms…
Q: We have two 4-bit registers A, B available, each with the standard “Load" input. When "Load" is at…
A: To design the data path for this case, we need to use a combination of logic gates and multiplexers.…
Q: The number of stages in designing a website? Explain the significance of each stage.
A: Web development creates a website for the Internet or an intranet. Web developers usually imply…
Q: How will you prevent the four most frequent causes of database failures?
A: Introduction: Database failures can have severe consequences for businesses and organizations,…
Q: Outline the Internet of Things' many moving parts (IoT).
A: The IoT has two main parts. Object you want to smarten Connectivity embedded system. A sophisticated…
Q: In cell D14, enter a formula using the MEDIAN function to calculate the median value in range…
A: Introduction: In data analysis, it's common to need to find the middle value of a set of numbers.…
Q: C++ Do not use file .txt just use cin Write a program that declares a struct to store the data of…
A: Define a struct FootballPlayer to store the data of a football player, with fields for the player's…
Q: Asynchronous programming approaches provide what advantages? Are there any kind of internet-based…
A: Hello student Greetings Hope you are doing great. Thank You!!!
Q: Write down some short thoughts on what you know about active and passive changes.
A: What is modification system: A modification system is a process or set of processes for making…
Q: how many (3)/(4) centimeteres cubes do you need to create a cube with an edge length of 12…
A: What is cube: A cube is a three-dimensional shape with six square faces of equal size that meet at…
Q: I was wondering if there were any case studies of how virtual servers were utilised in the classroom
A: Virtual work areas are PCs you access and use over the web. Since the working framework isn't being…
Q: Design the following 3-bit up counter: Count: 000, 001, 011, 101, 111, 010, 100, 000, 001, 101, ...…
A: Answer the above question are as follows
Q: There are many individuals that utilise programming languages to create applications for the web.…
A: Introduction: Programming languages are an essential tool for building applications for the web.…
Q: , up to four authors, publisher, ISBN, price, and number of copies in stock. To keep track of the…
A: The class definition includes private member variables for the title, authors, publisher, ISBN,…
Q: Provide an example to support your answer. Both Arduino Uno and Raspberry Pi are used in the…
A: Raspberry are inexpensive single-board computers that may usage in a variety of contexts and…
Q: To what extent does a typical Web app differ from others?
A: What is program: 1. A program is a set of instructions that performs a specific task when executed…
Q: complete the function RollSpecificNumber() that takes in three parameters: a GVDie object, an…
A: Let's write the answer in detail. Here's a possible implementation of the RollSpecificNumber()…
Q: Summarize the three conditions that must be met by a network for it to function optimally.
A: A network is a collection of interconnected computers that allow for the sharing of data and…
Q: Do you find it easier to operate and manage Linux or Windows virtual memory, and why?
A: Dear Student, The detailed answer to your question with required explanation is given below -
Q: You need to be aware of the most pressing issues related to the company's IT infrastructure and how…
A: Introduction: Managing an information requirements organisation, in contrast, involves management…
Q: Where do fat-client and thin-client architectures diverge?
A: Introduction: In a thin client paradigm, the presentation layer is introduced on the network, while…
- Starting with an empty minheap, draw the heap after each of the following operations
please see attached image.
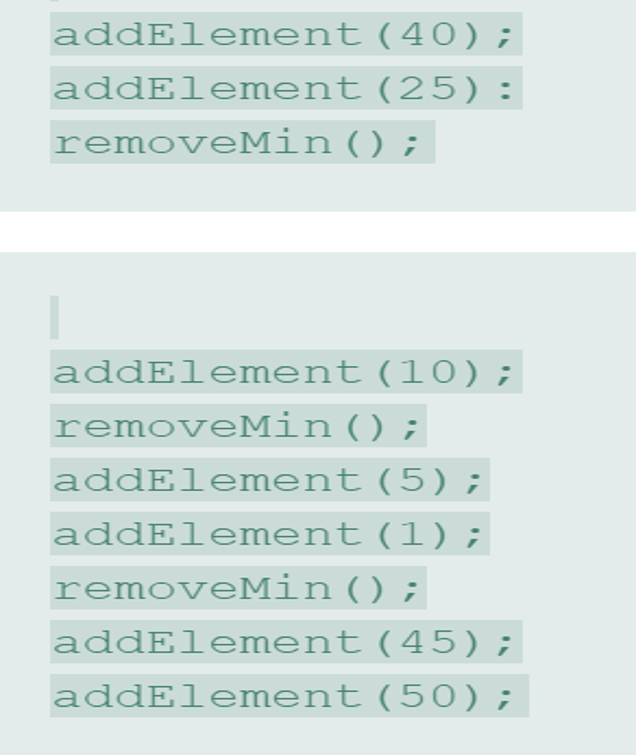
Step by step
Solved in 2 steps with 10 images

- Course: Data Structure and Algorithims Language: Java Kindly make the program in 2 hours. Task is well explained. You have to make the proogram properly in Java: Restriction: Prototype cannot be change you have to make program by using given prototype. TAsk: Create a class Node having two data members int data; Node next; Write the parametrized constructor of the class Node which contain one parameter int value assign this value to data and assign next to null Create class LinkList having one data members of type Node. Node head Write the following function in the LinkList class publicvoidinsertAtLast(int data);//this function add node at the end of the list publicvoid insertAthead(int data);//this function add node at the head of the list publicvoid deleteNode(int key);//this function find a node containing "key" and delete it publicvoid printLinkList();//this function print all the values in the Linklist public LinkListmergeList(LinkList l1,LinkList l2);// this function…complete all the implementation of the member functions listed in the class interface for the following header file. #ifndef _LINKEDSTACK#define _LINKEDSTACK #includeusing namespace std;templateclass LinkedStack{private:Node *top; Node *getCurrentTop() { return top; }public: Stack(); bool isEmpty(); bool push(ItemType newItem); bool pop(); ItemType peek(); void clean(); bool display();};#endifPart 2. Library Class Implement a class, Library, as described in the class diagram below. Library must implement the Comparable interface. The compareTo() method must compare the branch names and only the branch names. The comparison must be case insensitive. The equals() method must compare the branch names and only the branch names. The comparison must be case insensitive. Be sure to test the equals() and compareTo() methods before proceeding. Library - state: String - branch: String - city: String - zip: String - county: String - int squareFeet: int - int hoursOpen: int - int weeksOpen: int + Library(state: String, branch: String, city: String, zip: String, county: String, squareFeet: int, hoursOpen: int, weeksOpen: int) + getState(): String + getBranch(): String + getCity(): String + getZip(): String + getCounty(): String + getSquareFeet(): int + getHoursOpen(): int + getWeeksOpen(): int + setState(state: String): void + setBranch(branch: String):void +…
- The terms "primary," "candidate," and "superkey" need to be defined.Java/Data Structures: The Java Class Library implementation of the interface list return null when an index is out of range. True or FalseUsing the following UML, define the interface using Java programming language. <> DynamicList + capacity : int //initialized to 10 + add(int index, Object o): boolean + remove(int index): boolean
- Static analyzer write code c++ create your static analyzer tool thatreads your code as a text. Then, it analyzes it based on the below checklist. The checklist: - Do the attributes (e.g., data type and size) of each parameter match theattributes of each corresponding argument?SKELETON CODE IS PROVIDED ALONG WITH C AND H FILES. #include <stdio.h> #include <stdlib.h> #include <string.h> #include <stdbool.h> #include "node.h" #include "stack_functions.h" #define NUM_VERTICES 10 /** This function takes a pointer to the adjacency matrix of a Graph and the size of this matrix as arguments and prints the matrix */ void print_graph(int * graph, int size); /** This function takes a pointer to the adjacency matrix of a Graph, the size of this matrix, the source and dest node numbers along with the weight or cost of the edge and fills the adjacency matrix accordingly. */ void add_edge(int * graph, int size, int src, int dst, int cost); /** This function takes a pointer to the adjacency matrix of a graph, the size of this matrix, source and destination vertex numbers as inputs and prints out the path from the source vertex to the destination vertex. It also prints the total cost of this…java program: University of Bahrain College of Information Technology Department of Computer Science Second Semester, 2020-2021 ITCS214 / ITCS215 / ITCS216 (Data Structures) Assignment 3 Implement generic class ArrayStack as discussed in the lectures having following methods: constructor, push, pop, peek, isEmpty, copy constructor, reallocate (private method). Also add following methods to this class: size: returns number of elements in the stack. contains: Search an element in the stack. If found returns true, else returns false. clear: Deletes all elements of the stack and make it empty stack. Implement generic class ArrayQueue as discussed in the lectures having following methods: constructor, copy constructor, offer, poll, peek, isEmpty, reallocate(private), iterator. Inner class Iter that implements interface Iterator having methods: constructor, hasNext, next. Also add following methods to the ArrayQueue class: size: returns number of elements in the queue. contains: Search…

