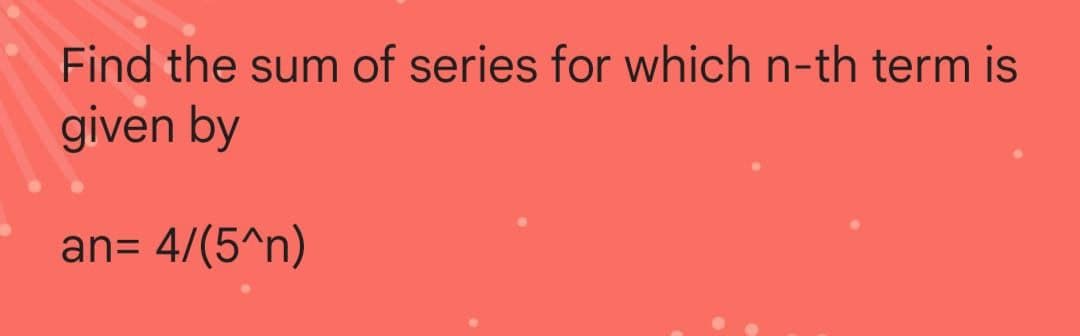
Find the sum of series for which n-th term is given by an= 4/(5^n)
Q: The following is a list of five typical network topologies. Which one do you think you can most…
A: Introduction: Describe five distinct kinds of network topologies. Which do you believe is the most…
Q: What exactly is booting?
A: Introduction: When a computer is first turned on, it goes through a predetermined sequence of tasks…
Q: Given the variable: double num=35.4689; Write a printf statement that will print the variable num in…
A: Answer:
Q: Consider the kind of wireless connection you'd want to use, WAN. What distinguishes this choice from…
A: The current scenario here is to explain briefly about wireless connection, types of wireless…
Q: ) Construct the state diagram for a nondeterministic Turing machine whose language is the set of…
A: Given data, Language L = Set of strings that contain a sub string 'u' satisfying the conditions that…
Q: What do you know about wireless security? Discuss and evaluate your thoughts.
A: Examine and discuss your knowledge of wireless security. ANSWER: Unauthorized access to devices or…
Q: What data type in C# should I use in 1/2
A: Answer: C # is a tightly typed language. It means we have to declare the variance that reflects the…
Q: What are the potential drawbacks of developing using tests first?
A: The Answer is in step2
Q: Q. implement a python program to short array [64, 34, 25, 12, 22,11,98] using merge sort.
A:
Q: Who establishes Internet standards?
A: Introduction: A specification of a technology or method for use on the Internet is an example of…
Q: Programming and user contexts may be shown by using examples.
A: The solution to the given question is: INTRODUCTION A programming environment is a combination of…
Q: The terms "task tracker" and "job tracker" are both used in the workplace. Could you perhaps give a…
A: Introduction: In Hadoop, two separate trackers are used: Task managerJob tracking software
Q: Why we need Gradle in Android
A: You were probably using Eclipse for your programming before Android Studio, and you didn't know how…
Q: Explain what Artificial Intelligence is in terms of how it acts logically.
A: Given: Define Artificial Intelligence in terms of sensible behaviour. Answer: The capacity to think…
Q: Compute the output frequency, fout for the sequential circuit given in Fig. Q2(b)(i). Assume a 48…
A: Below I have provided the handwritten solution to the given question
Q: Process A Arrival Time 0 2 C 6 D 8 Schedule the execution of the processes in the table based on the…
A: Note:- Dear student, As per our guidelines, we can answer your first question. FCFS First Come…
Q: i. Describe and illustrate the organization of a hard disk. (Hint: Include platters. tracks and…
A: i) Describe and illustrate the organization of a hard disk, A hard disk is a fixed unit containing…
Q: Are there any resources that may be saved by switching to a cloud computing platform? Describe the…
A: Introduction WHAT RESOURCES WOULD BE FREED UP WITH A CLOUD COMPUTING-BASED SYSTEM? Cloud computing…
Q: What precisely is voting technology, and why is it so crucial? What are the implications for…
A: The word "voting technology": Simply refers to the equipment or procedure for collecting and…
Q: What kinds of computations are most likely to be performed solely by AI managed by humans? What do…
A: Introduction: AI computation has no bounds. However, with inside the sensation of human controlled…
Q: When it comes to server operating systems, how would you define CentOS, and how is it different from…
A: CentOS is an open-source distribution platform for Linux. Many refer to it as a copy of Red Hat…
Q: Computer Science What type of memory management algorithm does Windows use?
A: The complete solution is given below:-
Q: No, the network was easy to set up for the whole firm. Describe the problems and the potential…
A: Company-wide network: An intranet is a company-wide network that is accessible only to employees and…
Q: What could get in the way of third-party programmes for open architecture platforms like Windows and…
A: Introduction: When third-party developed apps become a commodity, one of these interferes with their…
Q: List and briefly describe the various parts of a typical operating system kernel.
A: Required: Give a brief description and list of each component of a typical operating system kernel.…
Q: SQL language
A: Introduction SQL or structured Query Language that is basically a kind of a language that defines…
Q: Are there any specific features of Ubuntu Server that make it stand out from the rest of the Server…
A: Ubuntu is the operating system that is based on Linux. It's designed for PCs, cellphones, and…
Q: Please list and briefly explain the components of a typical operating system's kernel.
A: NOTE :- Below i explain the answer in my own words by which you understand it well. The Linux…
Q: 3- Implement onContextItemSelected(). When the user selects a menu item, the system calls this…
A: It is defined as a floating menu that appears when the user performs a long-click on an element. It…
Q: When it comes to information security, what are the distinctions between the top-down and bottom-up…
A: Information security enables organisations to protect digital/analog information. Information…
Q: computer science - What are external and internal types?
A: Introduction: Sorting is a strategy for organising data in a certain way.
Q: Share some citation guidelines with us. Plagiarism has serious repercussions.
A: Students who engage in plagiarism or any other form of academic dishonesty risk significant…
Q: Is it feasible to build a single protocol that can manage all of the difficulties that might arise…
A: Single protocol include all the functionalities which can be performed by a single protocol only.
Q: It is imperative that the topic of network security be addressed. Is there a difference between big…
A: This same integrity, confidentiality, and accessibility of computer networks and data are protected…
Q: Since the 1950s, the Turing Test has been used to measure the intelligence of computers. If you had…
A: Turing Test: The Turing Test is a straightforward way for determining whether or not a computer can…
Q: How can data in use be compromised? Why would an attacker target it then rather than in transit or…
A: Answer :- Data in use is data that is being processed by a computer or other device. An attacker can…
Q: What are the benefits of creating "connection points" across different networks? How do they factor…
A: Connection points: The attachment points are connected by a route, which is a path on a graph. It…
Q: y favorite number is " + 7L what is the correct data type that t
A: Given: + 7L
Q: In terms of server operating systems, how would you describe CentOS, and how does it differ from…
A: Introduction: CentOS is equipped with several very outstanding security features, such as a potent…
Q: What are the THREE most significant advantages that the Microsoft Excel system has brought to your…
A: There is online access: Excel is part of the Office 365 Productivity Suite, so company owners and…
Q: The benefits and disadvantages of weighted graphs against adjacency lists should be compared.
A: Introduction: One possible drawback of the adjacency-list format is that there is no faster method…
Q: Describe the DHCP lease idea. How do you go about getting it? What's the goal of all of this? Is…
A: DSCP lease time: Computers assess whether a lease reservation is needed. This includes whether a…
Q: five quality objectives we outlined earlier?
A: solution in below step
Q: Q. implement a python program to short array [64, 34,25,12,22,11,98] using merge sort.
A: It is required to write a python program to sort the given array using merge sort. Merge sort uses…
Q: What role do databases play in three-tier apps?
A: Intro Three-tier application: The most common client-server design in relational database…
Q: What exactly does it imply when it's referred to as the "session state" in HTTP
A: SESSION STATE OF HTTP: Session state, in the context of . NET,…
Q: Consider the following MATLAB code: a=1; while a<=6 a=3*a-1; end How many times the loop repeats?…
A: Given a=1 The condition of the while loop is a<=6 1<=6 (condition true) So, the code inside…
Q: Flat files and folders are often mistaken for databases on computers by the general public. You can…
A: A flat file is a database that is stored in a file. It might be either a plain text or a binary…
Q: What exactly are encapsulation and de-encapsulation?How does it function in a network?
A: Introduction: One of the core concepts behind OOP is called encapsulation (object-oriented…
Q: Explain the steps needed in changing the context.
A: Introduction: Context switching is used to save the context or state of a process so that it may be…
Step by step
Solved in 4 steps with 2 images

- Find the order of growth for the following function ((n^3) − (60n^2) − 5)(nlog(n) + 3^n )Show that StartFraction d Over dx EndFraction (ln kx)equalsStartFraction d Over dx EndFraction ln x, given that xgreater than 0 and kgreater than 0 is a real number.Given an array A of n distinct positive integers and an integer B, find the number of unordered pairs of indices(i and j) such that i != j and that A[i] + A[j] > B using an algorithim in time nlogn. Prove that the algorithm you have is in time nlogn
- Generate the graph of f(xk) vs k where k is the iteration number and xk is the current estimate of x at iteration k. This graph should convey the decreasing nature of function values.Solve this recurrence relations together with the initialconditions given. a_{n+2} = −4a_{n+1} + 5a_n for n ≥ 0, a_0 = 2, a_1 = 8find the adjacent matrix not the adjacent list

