Bayes rule is given as: P(AIB) = P(BIA) P(A)/P(B) Consider a party where male and not male guest arrive with their choice of dress color. Some pink and others are not. Following is the data about observations of guests and their color choices: Pink notPink Man 5 35 notMan 20 40 Using this data find the probability: P(Pink Man). Show your calculations and the result
Bayes rule is given as: P(AIB) = P(BIA) P(A)/P(B) Consider a party where male and not male guest arrive with their choice of dress color. Some pink and others are not. Following is the data about observations of guests and their color choices: Pink notPink Man 5 35 notMan 20 40 Using this data find the probability: P(Pink Man). Show your calculations and the result
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter17: Markov Chains
Section17.7: Work-force Planning Models
Problem 9P
Related questions
Question
ANSWER THESE 2 QUESTIONS PLEASE
BUSINESS INTELLIGENCE
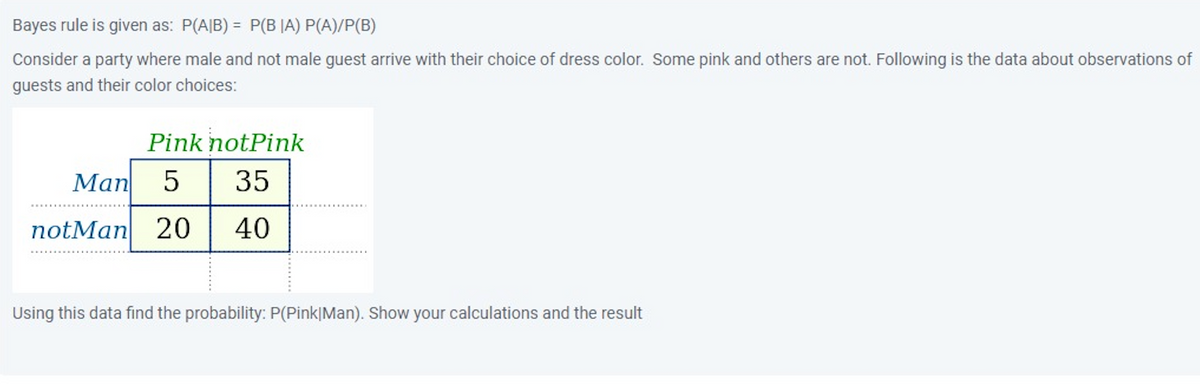
Transcribed Image Text:Bayes rule is given as: P(AIB) = P(BIA) P(A)/P(B)
Consider a party where male and not male guest arrive with their choice of dress color. Some pink and others are not. Following is the data about observations of
guests and their color choices:
Pink notPink
Man 5 35
notMan 20 40
Using this data find the probability: P(Pink Man). Show your calculations and the result
![Following is the association rules found for the Epub data which provides document download information for a library. Using this data choose two rules which are
most important (indicate rule numbers) and explain the reasons for your selection.
confidence lift
<dbl>
Ihs
rhs
support
<chr> <chr> <chr> <dbl>
<dbl>
leverage
<dbl>
[1] {doc_506} => (doc_507) 0.001207960 0.6551724303.094320.001203974
[2] {doc_507}=> (doc_506) 0.001207960 0.5588235303.09432 0.001203974
[3] (doc_4bf} => (doc_4ac) 0.001080806 0.5000000 77.102940.001066788
[4] {doc_6e9} => (doc_6e8) 0.001207960 0.6785714333.53906 0.001204338
[5] {doc_6e8} => (doc_6e9} 0.001207960 0.5937500 333.53906 0.001204338
[6] {doc_6e9} => (doc_6e7) 0.001271537 0.7142857 321.00000 0.001267575
[7] {doc_6e7}=> (doc_6e9} 0.001271537 0.5714286321.000000.001267575
[8] {doc_6e8} => (doc_6e7) 0.001335113 0.6562500 294.918750.001330586
[9] {doc_6e7}=> (doc_6e8) 0.001335113 0.6000000 294.91875 0.001330586
[10] {doc_87c} => (doc_882) 0.001335113 0.6000000 171.58909 0.001327333
[11] {doc_6e8, doc_6e9}=> {doc_6e7} 0.001080806 0.8947368 402.094740.001078118
[12] {doc_6e7, doc_6e9}=> {doc_6e8) 0.001080806 0.8500000 417.80156 0.001078219
[13] {doc_6e7, doc_6e8}=> {doc_6e9} 0.001080806 0.8095238 454.75000 0.001078429](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2F45f971c9-9efa-4eff-b81c-67b011a8da8a%2F3ab27121-d1c3-4e10-9034-5b94bb598a32%2F3g27b9f_processed.png&w=3840&q=75)
Transcribed Image Text:Following is the association rules found for the Epub data which provides document download information for a library. Using this data choose two rules which are
most important (indicate rule numbers) and explain the reasons for your selection.
confidence lift
<dbl>
Ihs
rhs
support
<chr> <chr> <chr> <dbl>
<dbl>
leverage
<dbl>
[1] {doc_506} => (doc_507) 0.001207960 0.6551724303.094320.001203974
[2] {doc_507}=> (doc_506) 0.001207960 0.5588235303.09432 0.001203974
[3] (doc_4bf} => (doc_4ac) 0.001080806 0.5000000 77.102940.001066788
[4] {doc_6e9} => (doc_6e8) 0.001207960 0.6785714333.53906 0.001204338
[5] {doc_6e8} => (doc_6e9} 0.001207960 0.5937500 333.53906 0.001204338
[6] {doc_6e9} => (doc_6e7) 0.001271537 0.7142857 321.00000 0.001267575
[7] {doc_6e7}=> (doc_6e9} 0.001271537 0.5714286321.000000.001267575
[8] {doc_6e8} => (doc_6e7) 0.001335113 0.6562500 294.918750.001330586
[9] {doc_6e7}=> (doc_6e8) 0.001335113 0.6000000 294.91875 0.001330586
[10] {doc_87c} => (doc_882) 0.001335113 0.6000000 171.58909 0.001327333
[11] {doc_6e8, doc_6e9}=> {doc_6e7} 0.001080806 0.8947368 402.094740.001078118
[12] {doc_6e7, doc_6e9}=> {doc_6e8) 0.001080806 0.8500000 417.80156 0.001078219
[13] {doc_6e7, doc_6e8}=> {doc_6e9} 0.001080806 0.8095238 454.75000 0.001078429
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole