
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
Draw an inheritance hierarchy representing parts of a computer system (processor, memory,
disk drive, DVD drive, printer, scanner, keyboard, mouse, etc.).
(I want the complete solution using the codes in bluej program also diagram)
bluej
java cood
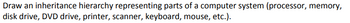
Transcribed Image Text:Draw an inheritance hierarchy representing parts of a computer system (processor, memory,
disk drive, DVD drive, printer, scanner, keyboard, mouse, etc.).
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Instead of receiving references, Java's method parameters get values as their input. In what specific ways does this manifest itself?arrow_forwardWhy does the Number Class from this slide need to be abstract?arrow_forwardDesign a class hierarchy for a simple banking system. Include classes for a Bank, Account, and Customer. Implement methods for depositing and withdrawing money, transferring funds between accounts, and checking the account balance.arrow_forward
- Create a UML class diagram of the application illustrating class hierarchy, collaboration, and the content of each class. There is only one class. There is a main method that calls four methods. I am not sure if I made the UML Class diagram correct. import java.util.Random; // import Random packageimport java.util.Scanner; // import Scanner Package public class SortArray{ // class name public static void main(String[] args) { //main method Scanner scanner = new Scanner(System.in); // creates object of the Scanner classint[] array = initializeArray(scanner); System.out.print("Array of randomly generated values: ");displayArray(array); // Prints unsorted array sortDescending(array); // sort the array in descending orderSystem.out.print("Values in desending order: ");displayArray(array); // prints the sorted array, should be in descending ordersortAscending(array); // sort the array in ascending orderSystem.out.print("Values in asending order: ");displayArray(array); // prints the…arrow_forwardPlease write the code in Java usign this UML diagram. Add Comments.arrow_forwardWrite a java program as shown in the following UML class diagram:(read the details below)arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education