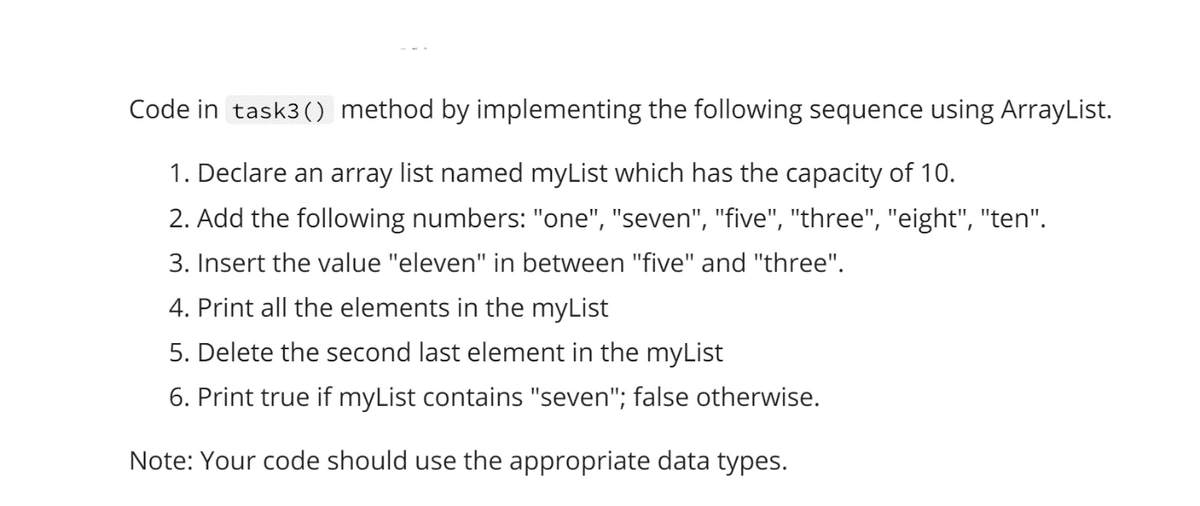
Code in task3 () method by implementing the following sequence using ArrayList. 1. Declare an array list named myList which has the capacity of 10. 2. Add the following numbers: "one", "seven", "five", "three", "eight", "ten". 3. Insert the value "eleven" in between "five" and "three". 4. Print all the elements in the myList 5. Delete the second last element in the myList 6. Print true if myList contains "seven"; false otherwise. Note: Your code should use the appropriate data types.
Q: ΡΥTHΟΝ Determine a function T(n) that relates input size n to number of runtime steps and the Big-O…
A: - We need to get a function for the printing of a list and we need to find the complexity of the…
Q: Create a C++ program that include the Fees to be paid The book was returned on time (Yes/No)…
A: C++: C++ is a general purpose,high level object oriented programming language. It was developed by…
Q: Provide code to run the calcShipping() function when the value of the state field in the…
A: Answer
Q: Give an explanation for what the word "firewall" means in terms of network security, and describe…
A: A firewall is a type of equipment used to filter network traffic in the context of cybersecurity.…
Q: 4. Point out TRUE/ FALSE of the following statements: (a) A CLR(1) grammar can guarantee there is no…
A: For a) and b) i)LALR can have shift-reduce conflicts only if CLR has a shift-reduce conflictii)LALR…
Q: The difference between an interpreter and a compiler should be discussed.
A: Interpreter translates just one statement of the program at a time into machine code.
Q: Code a private method called days0fTheWeek that takes in a parameter day as a String. Based on the…
A: Program: public class Main { // This method returns the corresponding day for that Number.…
Q: Consider the below integer array which is already sorted { 1, 2, 3, 4, 4, 6, 6, 6 } program in Java…
A: import java.util.*;class GFG { // function to find repeating elements static void…
Q: cyber security Aims of the project
A: Cyber security awareness is very important. The aims of Cyber security awareness are as follows:…
Q: 5. Additional Credits - List all control signals for executing MAR + X, including P0 ~~ P5, MR AND…
A:
Q: Make a list of the databases that have information about you. What method is used to acquire data in…
A: Database : A list of databases available in your nation may be found online. Each database collects…
Q: What are the program's similarities and differences?
A: Project and programme similarities It’s good for project and programme managers to understand the…
Q: Java program to evaluate the given post-fix expression in O( n) time and with O(n) space complexity.…
A: We will create SolvePostFixExpr Class and in main method we will define our logic. We can use stack…
Q: unding box reve
A: At first, while beginning a new visual basic project,
Q: • The Emerging Manufacturing Company has decided to use its new computer for payroll. • You have…
A: Java Program: import java.util.*; import java.io.*; class Employee { private String id;…
Q: The command x followed by p, given in vim, places the cursor on the first letter of the word.…
A: To install the latest VIM package available in the repository: Vim is a text editor that works with…
Q: 1. Describe an iterative algorithm that takes as input a list of n distinct integers and counts how…
A: As per our policy I have given answer to only first question.
Q: For what reasons does an operating system normally offer specific calls for accessing directory…
A: There are a number of operations that can be carried: The working directory should be changed.You…
Q: Compile a summary of JAD and RAD. Describe how they vary from typical fact-gathering techniques.…
A: JAD and RAD: The characteristics and intended aims of the target project are described in system…
Q: Determine a function T(n) that relates input sizen to number of runtime steps and the Big-O Time…
A: Big O notation is a maths notation which helps in describing the limiting behaviour of a given…
Q: b, Σ X2 W
A: The answer is
Q: When creating a huge system's architecture, explain why you decided to use a range of architectural…
A: Normally, when we design the architecture for a large system, various architectural patterns are…
Q: Explain what the word "firewall" means in terms of network security and how it is employed in…
A: Firewall is a packet filter that prevents malicious contents from getting inside our network or…
Q: How am I to determine what a MAC file is?
A: Macintosh File System: Apple Computer established the Macintosh File System (MFS) as a volume format…
Q: 4. Let A = {a, b, c, d}, B = {a, y} and C = {m, n, 0, p}. Find a. A × B = b. В2 — |A x B x C| = с.
A:
Q: The owner of a file named linux.txt belongs to a group that has all permissions on it. Describe the…
A: Linux is a multiuser operating system, which means that several users may execute their jobs…
Q: se to preview a pie
A: Here we are expected to make sense of what text qualities a reader might utilize to get a sneak look…
Q: A Label control's text may be changed using what property?
A: Please refer below for your reference: Follow the steps in VBA: 1) Click on visual basic on left top…
Q: The command x followed by p, given in vim, places the cursor on the first letter of the word.…
A:
Q: 2. Draw a recursive tree for callMyself(4). What is its return value? public static int…
A: Below I have drawn a recursive tree of the given question:
Q: The Course class The modifications you will apply to the Course class are shown in the following UML…
A: Course.java import java.util.Arrays; import java.util.Scanner; public class Course {…
Q: in Python Create the logic for a program that call calls a function that computes the final price…
A: Python program: def calculatePrice(price, com_rate, dis_rate): # Add the salesperson…
Q: 2. Create matrix contain of 2 row and 2 column. Find elements in row 2 and columns from 1 to 2. The…
A: In this problem, we need to create a program in Matlab to create a matrix and access its data.…
Q: Calculate the perceptron network if there are 3 inputs x,-1.7, x,-5.9, x,-3 and b- -1.8.
A: The answer is
Q: The owner of a file named linux.txt belongs to a group that has all permissions on it. Describe the…
A: Command: A command is defined as an order or the authority to command. A dog owner instructing their…
Q: In terms of firewall management, what are some best practises? Explain.
A: Firewall management: The act of establishing and monitoring a firewall in order to maintain a secure…
Q: Make use of the following structure while creating your mobile application's test cases (black box…
A: Black box analysis Black box testing is the process of testing a system with no prior knowledge of…
Q: 2.12. For each of the following languages, draw an FA accepting it. d. (bbb, baa}* (a) e. (a}U…
A: Given: For the following language draw an Finite automata accepting it . As per the Company…
Q: Using the Collections framework (ArrayList or LinkedList), create and add a queue of 5 names and…
A: Java is one of the languages, which is considerably used in many sectors of Computer. In older…
Q: What is Post Office Protocol's compressed representation on a computer?
A: Post office Protocol (POP) is a kind of PC systems administration and Internet standard convention…
Q: ΡΥTHON Determine a function T(n) that relates input size n to number of runtime steps and the Big-O…
A: Solution: Given,
Q: How critical is the RNC (Radio Network Controller) in 3G cellular data networks?
A: Radio Network Controller: The RNC (Radio Network Controller) is a component of the overall structure…
Q: What is the underlying cause of diskthrashing? What steps can you take to mitigate effects?
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Disk…
Q: Q2- Write a program to read a number (n). Then print all numbers from 0 to n that are not equal to 1…
A: I give code in Matlab as well as in python along with output and code screenshot
Q: Collision domains broadcast domains is a Cisco switch command that can be used to debug VLAN trunk…
A: Can use the display interface trunk command to determine whether the local and peer-native VLANs are…
Q: Describe an algorithm (in words or pseudo code) for the following computational problem: Input: A…
A: Here is the algorithm for your problem- Find the minimum spanning tree cost of the entire graph,…
Q: Let E = {a,b}. Prove the equivalence: b+ e*bab((ab)*)* = b(ab)*.
A: The complete solution is below:
Q: Quantum computing can be defined as follows:
A: Quantum is a Latin word which means "amount". According to dictionary it is any of the small…
Q: Python has the following syntax: In order to print each item in a list, create a function called…
A: Python program to solve the given problem is below.
Q: What is the ultimate purpose of Artificial Intelligence (Al)? Give an overview of the many domains…
A: AI's goal: Artificial intelligence use technologies such as machine learning and deep learning to…
Step by step
Solved in 3 steps with 3 images

- JAVA, PLEASE THE PROGRAM SHOULD USE THE INITIAL ARRAYLIST AND TO EDIT IT NOT TO CREATE A NEW ONE Create a class called OurArrayList and implement the following methods. Do NOT createany auxiliary memory.Include a main method and test all your methods with appropriate examples.a. Write a method called scaleByK() that takes an ArrayList of integers as aparameter and replaces every integer of value K with K copies of itself. Forexample, if the list stores the values (4, 1 , 2, 0 ,3) before the method is called, itshould store the values (4, 4, 4, 4, 1, 2, 2, 3, 3, 3) after the method finishesexecuting. Zeroes and negative numbers should be removed from the list by thismethodDesign and implement a getLastHalf() method for the MyLinkedList class. The method should return the last half of the list as a new list leaving the original list intact. If the list has an uneven number of elements the extra one element must be in the list returned. Example : [1,3,5,4] return [5,4] and [1,6,9] return [6,9]. Follow the three step method for designing the method Develop the java code for the method Create a test program to test the method thoroughly using the Integer wrapper class.Design and implement a getLastHalf() method for the MyLinkedList class. The method should return the last half of the list as a new list leaving the original list intact. If the list has an uneven number of elements the extra one element must be in the list returned. Example : [1,3,5,4] return [5,4] and [1,6,9] return [6,9]. Follow the three step method for designing the method Develop the java code for the method Create a test program to test the method thoroughly using the Integer wrapper class. public class MyLinkedList<E> { private Node<E> head, tail; public MyLinkedList() { head = null; tail = null; } /** Return the head element in the list */ public E getFirst() { if (head == null) { return null; } else { return head.element; } } /** Return the last element in the list */ public E getLast() { if (head==null) { return null; } else { return tail.element; } } /** Add an element to the beginning of the list */ public void prepend(E e) { Node<E> newNode = new…
- Question: What is the length of the array in MyArrayList after executing the following statements? MyArrayList<Double> list = new MyArrayList<>(); list.add(25.4); list.trimToSize(); list.add(15.4); list.add(35.4); list.add(17.4); list.add(7.4); public class MyArrayList<E> implements MyList<E> { public static final int INITIAL_CAPACITY = 16; private E[] data = (E[])new Object[INITIAL_CAPACITY]; private int size = 0; // Number of elements in the list /** Create an empty list */ public MyArrayList() { } /** Create a list from an array of objects */ public MyArrayList(E[] objects) { for (int i = 0; i < objects.length; i++) add(objects[i]); // Warning: don’t use super(objects)! } @Override /** Add a new element at the specified index */ public void add(int index, E e) { ensureCapacity(); // Move the elements to the right after the specified index for (int…JAVA, NOTE: PLEASE THE METHOD SHOULD USE THE INITIAL ARRAYLIST AND TO EDIT IT NOT TO CREATE A NEW ONE Create a class called OurArrayList and implement the following methods. Do NOT createany auxiliary memory.Include a main method and test all your methods with appropriate examples.a. Write a method called scaleByK() that takes an ArrayList of integers as aparameter and replaces every integer of value K with K copies of itself. Forexample, if the list stores the values (4, 1 , 2, 0 ,3) before the method is called, itshould store the values (4, 4, 4, 4, 1, 2, 2, 3, 3, 3) after the method finishesexecuting. Zeroes and negative numbers should be removed from the list by thismethodgetListRowIndices Method public static java.util.ArrayList<java.lang.Integer> getListRowIndices(int[][] array, int rowLength) This method returns an ArrayList with the indices of rows of the two-dimensional having a length that corresponds to rowLength. You may only use one auxiliary method. The method should create an ArrayList that is passed to the auxiliary in order to place the indices (if any). If no indices are found, an empty (size of 0) ArrayList will be returned. You can assume the array parameter will not be null and every row of the two-dimensional array has an array with a size of at least 0. Your implementation must be recursive and you may not use any loop construct. Do not use ++ or -- in any recursive call argument. It may lead to an infinite recursion. For example, use index + 1, instead of index++. Parameters: array - rowLength - Returns: ArrayList<Integer>
- Question 4: Task 1: Create a generic method named sum() that accepts a generic ArrayList reference and returns the sum of the elements in the ArrayList argument. The generic type is bound to the Number class. The method will throw a NullPointerException is the input argument is null. public static ______________________sum(____________________) { } Task 2: i) Create an ArrayList of 100 random integers taking values between 0 and 1000. ii) Use the sum() method to find the sum in the integer ArrayList. iii) Create an ArrayList of 200 random real numbers taking values between -50.0 and +50.0. iv) Use the sum() method to find the sum in the ArrayList of real numbers. public static void main(String[] args){ } Task 3: Create a recursive method named dec2bin() that takes an integer argument (in decimal format) and returns the binary representation of the input argument as a String. Make sure that the input argument is not negative! public static String…Java Create an ArrayList of strings to store the names of celebrities or athletes. Add five names to the list. Process the list with a for loop and the get() method to display the names, one name per line. Pass the list to a void method. Inside the method, Insert another name at index 2 and remove the name at index 4. Use a foreach loop to display the arraylist again, all names on one line separated by asterisks. After the method call in main, create an iterator for the arraylist and use it to display the list one more time. See Sample Output. SAMPLE OUTPUT Here is the list Lionel Messi Drake Adele Dwayne Johnson Beyonce Here is the new list * Lionel Messi * Drake * Taylor Swift * Adele * Beyonce Using an iterator, here is the list Lionel Messi Drake Taylor Swift Adele BeyonceWrite a Java application CountryList. In the main method, do the following:1. Create an array list of Strings called countries.2. Add "Canada", "India", "Mexico", "Peru" in that order.3. Use the enhanced for loop to print all countries in the array list, one per line.4. Add "Spain" at index 15. Replace the element at index 2 with "Vietnam". You must use the set method.6. Replace the next to the last element with "Brazil". You must use the set method. You willlose one point if you use 3 in the set method. Do this in a manner that would replace thenext to the last element, no matter the size of the array list.7. Remove the object "Canada" Do not remove at an index. Your code should work if"Canada" was at a different location. There is a version of remove method that willremove a specific object.8. Get and print the first element followed by "***"9. Call method toString() on countries to print all elements on one line.10. Use the enhanced for loop to print all countries in the array list,…
- I need to write changeArrayLength(int m) – void method; I already have the code (attached below) but it needs debugging... This method creates a new student table for this course; this new table has the given length m; the method moves all registered students to this table. This method creates a new array of SLinkedList<Student>, moves all the registered students into these linked lists, and changes this course’s studentTable field so it references this new table instead. Each student in the current table will be moved to the new table. This will require in most cases that the student is moved to a different array slot index. The slot index for the SLinkedList<Student> that they are moved to is id % m, where m is the new length of the array (the parameter of the method). The motivation for increasing the capacity of the array is that it keeps the average lengths of the linkedlists below 1, which tends to mean a fast traversal of each linked list. public class Course {…I need to write changeArrayLength(int m) – void method; I already have the code (attached below) but it needs debugging... This method creates a new student table for this course; this new table has the given length m; the method moves all registered students to this table. This method creates a new array of SLinkedList<Student>, moves all the registered students into these linked lists, and changes this course’s studentTable field so it references this new table instead. Each student in the current table will be moved to the new table. This will require in most cases that the student is moved to a different array slot index. The slot index for the SLinkedList<Student> that they are moved to is id % m, where m is the new length of the array (the parameter of the method). The motivation for increasing the capacity of the array is that it keeps the average lengths of the linkedlists below 1, which tends to mean a fast traversal of each linked list.Import the ArrayList and List classes from the java.util package to create a list of phone numbers and also import the HashSet and Set classes from the java.util package to create a set of unique prefixes. Create a class called PhoneNumberPrefix with a main method that will contain the code to find the unique prefixes. Create a List called phoneNumbers and use the add method to add several phone numbers to the list. List<String> phoneNumbers = new ArrayList<>(); phoneNumbers.add("555-555-1234"); phoneNumbers.add("555-555-2345"); phoneNumbers.add("555-555-3456"); phoneNumbers.add("444-444-1234"); phoneNumbers.add("333-333-1234"); Create a Set called prefixes and use a for-each loop to iterate over the phoneNumbers list. For each phone number, we use the substring method to extract the first 7 characters, which represent the prefix, and add it to the prefixes set using the add method. Finally, use the println method to print the prefixes set, which will contain all of…

