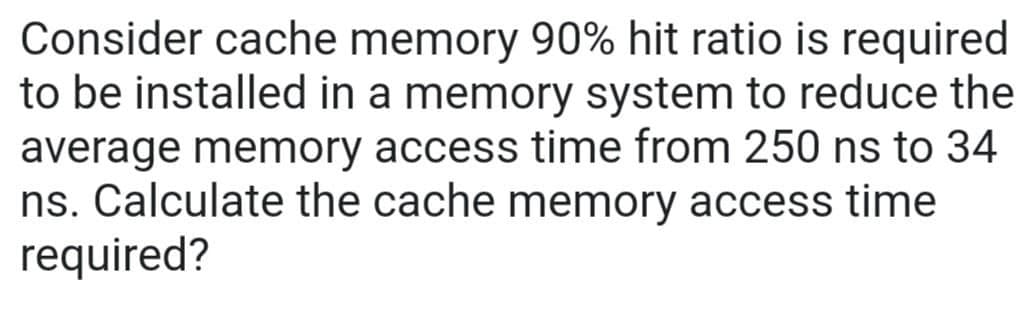
Consider cache memory 90% hit ratio is required to be installed in a memory system to reduce the average memory access time from 250 ns to 34 ns. Calculate the cache memory access time required?
Q: Why aren't the most important concepts of the subject being used in software engineering?
A: Concepts of the subject being used in software engineering: When faced with a new topic, look into…
Q: What will you add to 9 to become 6?
A: Answer -3
Q: The study of computers Explain the dilemma of the dining philosophers and how it relates to…
A: Operating systems: The operating system is the most important piece of software that a computer may…
Q: It is recommended that you offer a more in-depth description of the metrics that are involved in the…
A: Programming: Make software without coding. It needs an idea and no-code, customizable UI. No-code…
Q: What is IP spoofing, and how does it work? If so, how does it compromise security?
A: Answer in step 2
Q: We have a circuit that counts from 1 to 14. This circuit output (1,2,4,6,7) will light up red, when…
A: int pin1=11; int pin2=10; int pin3=9; int pin4=8; int timr=1000; int i=0; void setup() {…
Q: Discover how information systems are put to use in a range of different fields.
A: Major sectors of the Economy: Primary sector — raw material extraction – mining, fishing, and…
Q: Consider three intensive processes, which requires 10,20 and 30 units of time and arrive at times…
A: Let three process be A0, A1 and A2 with arrival times 0, 2 and 6 respectively and CPU burst times…
Q: What would you do if a virus invaded your mobile device, such as a smartphone or tablet? Determine…
A: Mobile Phone Virus A cellular phone virus is malicious computer software that targets cellular…
Q: When a file is read from a disk block, operating systems attempt to keep succeeding blocks in the…
A: Given: This topic discusses how operating systems try to retain successive blocks of a file on the…
Q: What is the role of operating system in computer?
A: Operating system In our computer, we have two kinds of software that is application software(like…
Q: explain the importance of a Work Breakdown Structure. While directing a traditional software…
A: Given: We must explain why the Work Breakdown Structure is vital in this section. Is your preferred…
Q: When a line ends, which of the following is most likely to be omitted? What's the rationale for its…
A: Given: In order to keep just the essential data and avoid unneeded whitespaces, programmers must…
Q: mechanical), class 3 should insert engineering name. Friend function should diagnose error a display…
A: // I hope my solution is helpful #include <bits/stdc++.h> using namespace std; class…
Q: Computer Science write a complete C++ code for Cricket tournament scheduling aspect of the…
A: Please find the answer below :
Q: What is the reserved word used to define a function? O a. function O b. func O C. def O d. method O…
A: keywords are the reserved words that cant be used for defining variable names
Q: Many businesses store all of their critical data on cloud storage providers. What makes you believe…
A: Benefits Cloud storage saves money. Sсаlе economies. Cloud vendors acquire storage and pass the…
Q: Where did the concept of the internet of things come from, and how is it being implemented in…
A: Internet of things: IoT is a network of interconnected computing devices, mechanical and…
Q: Why is it beneficial for your online company to make advantage of cloud computing? What are the…
A: Cloud computing for e-commerce: Businesses spend a lot on software to improve operations. Cloud…
Q: Question What is the computational (time) complexity of the following piece of an algorithm? while…
A: Answer - While calculating the time complexity of any program or algorithm. Need to know the time…
Q: Explanation of It's possible that web caching may speed up the delivery of a requested item. Are all…
A: What is Web Caching? Cache (memory) is memory that is stored very close to the CPU, say on the same…
Q: What is the fundamental idea that underpins the quality assurance process for software, and how does…
A: You will get the whole answer to your inquiry in the steps that follow: An engineering process is…
Q: 1. What are the specific limitations of a computer system that provides no operating system? What…
A: It is defined as a software that acts as an interface between computer hardware components and the…
Q: 6-) Find binary representation of (33.625)10- 7-) Find binary representation of 3.21. (Stop after…
A:
Q: How to keep your network safe from phishing assaults What can we do to prevent another attack of…
A: Intro: => Phishing tricks are one of the most widely recognized strategies for assault you…
Q: Which of these two scenarios best describes your experience while attempting to delete software?
A: What are two potential causes for your inability to remove the software?
Q: What are the advantages and disadvantages of utilizing the cloud for data storage? A list of…
A: Given: Basic cloud storage is a cloud computing strategy in which data is stored on the Internet…
Q: Provide an explanation as to why businesses have started using cloud computing.
A: Cloud computing is availability of resources over internet to offer flexible use of resources. It…
Q: Q1/ Write C++ program to detect patient state. the program should have class 1 insert patient (name…
A: As per the question statement, We need to write c++ program.
Q: What, if any, influence has cloud computing had on the effectiveness of human interaction and…
A: Cloud computing is the technology that is an emerging new computing paradigm for delivering the…
Q: 3-) Find a,b,c. a) 2.5 GB in MB? b) 32 x 2¹0 bits in KB? c) 3.5 MB in bits?
A: your question is about find a,b,c let's find all of that
Q: Based on the given class diagram, create a class implementation using C++.
A: As per the question statement, We need to write c++ program.
Q: What does the phrase "interdependence" represent in terms of system ideas, and how does it vary from…
A: The correct answer of the question is given below
Q: Write a python program for the following pattern using while loop [code & output screenshots are…
A: Code: n = 8 # Upper pyramid# number of spacesk = 0# outer loop to handle number of rowsfor i in…
Q: How does the process of manually testing software compare to other approaches, and what are the…
A: The testing is done by hand: One sort of software testing is known as "manual testing," and it is…
Q: The total number of distinct operator and operand occurrences is utilized as a measurement in order…
A: please find the solution in next step
Q: Use the network address 192.168.10.0 to answer the following: a) Subnet mask? b) How many subnets?…
A: Please refer to the following step for the complete solution of the problem above.
Q: What are the most significant issues, both technical and nontechnical, that prevent software reuse?…
A:
Q: There are some key differences between online transaction processing systems and business…
A: There are some significant points of differentiation between business intelligence systems and…
Q: write a function that performs this array manipulation with the given parameters. array…
A: here in given question ask for c++ program.
Q: In what ways do customers and developers work together to create software?
A: your question is about what ways do customers and developer work together to create software , let's…
Q: What aspects of an organization's computing infrastructure could make a virus more likely to spread…
A: Virus: One of the most well-known dangers to computers and networks is a programme known as a virus.…
Q: me of the Benefits and Drawbacks of Using the Cloud to Store Your Company's Data for a Small…
A: Cloud Storage Benefits for a small scale business :Many modern enterprises understand the value of…
Q: Excel: What does the "subtotal" function accomplish and how do I use it?
A: Subtotal function: You will be able to automatically generate groups with the aid of the Subtotal…
Q: In addition to participating in the Comm Center, please upload your discussion response here for…
A: The question has been solved in step2 successfully.
Q: Identify the several design models that we use throughout the analysis phase of the software…
A: Software development: Software development include the creation, design, implementation, and…
Q: Knowing which programming paradigms a language supports is of what importance? Add to it,
A: If you know which programming paradigm a language supports, you can figure out how to write code in…
Q: •1. How can we calculate the address of "a[2][3]” in "int a[5][10]" ?
A: here in the given question ask for address .
Q: Program in c++. Given an unsorted array, find the least difference between the element pairs.…
A: The code is given below. #include<iostream.h> #include <limits.h> // for INT_MAX…
Q: What exactly is online analytical processing (OLAP), and how does the technology behind it work?
A:
Step by step
Solved in 2 steps

- Assume a cache memory hit ratio is 93% and the hit time is one cycle, but the miss penalty is 40 cycles. Then, Compute the average memory access time (AMAT)If memory read cycle takes 100 ns and a cache read cycle takes 20 ns, then for four continuous references, the first one brings the main memory contents to cache and the next three from cache. Find the time taken for the Read cycle with and without Cache? What is the Percentage speedup obtained?Consider a memory system with a cache access time of 100ns and a memory access timeof 1200ns. If the effective access time is 10% greater than the cache access time, what is thehit ratio H?
- Consider a system with 4GB of memory address space. Assuming a write-back policy and block size of 32 bytes, find the space overhead when it uses a (a) 64 KB direct mapped cache(b) fully associative cache (c) eight-way set-associative cacheWhy SRAM is preferred over DRAM for constructing Cache Memory. Justify your answer by mentioningat least three points.A 32-bit computer has a memory of 256 KB and a cache line size of 64 bytes. The memory cache access time is 5ns. This cache is 4-way associative and use LRU as a replacement algorithm. a) What is the number of lines and sets of this memory cache? b) What is the block size transferred between the cache memory and the main memory? c) If the time to transfer a line to cache memory is 200 ns, what is the hit ratio needed to obtain an average access time of 20 ns?
- Consider a system with 20 requests and out of 20 , 4 requests are already in cache memory. What will be the hit ratioSuppose you have a processor with a base CPI 1.0, assuming all references hit in theprimary cache (L1), and a clock rate of 3 GHz. Assume that you have two caches (L1and L2). L2 cache access time is 10 ns and main memory access time is 200 ns,including all the miss handling. Suppose the miss rate per instruction at the L1 cache is10%, L2 cache is 5%.a) What is the effective CPI?b) What will be the effective CPI if we add a new cache (L3) that has 50 nsaccess time and reduce the miss rate to main memory to 1%?Show work and type answer please. Suppose a computer using fully associate cache has 2G Bytes of main memory and a cache of 256 Blocks, where each cache Block has 8 Words, and the Word Size is 2 Bytes. a. How many blocks of main memory? b. What is the format of a memory address as seen by the cache? c. To which cache block will the memory reference 00001C4A in Hex?
- Suppose a 1 MiB L1 cache has an access time of 1 clock cycle, the 16 MiB L2 has an access time of 4 clock cycles, and the 8 GiB DRAM has an average access time of 40 clock cycles. 80% of memory reads are satisfied by the L1 cache. Only 10% have to go to main memory. (a) What is the AMAT following a miss on L1? (b) What is the AMAT for memory overall?You are given the following data about a virtual memory system:(a) The TLB can hold 512 entries and can be accessed in 1 clock cycle (1nsec).(b) A page table entry can be found in 100 clock cycles or 100 nsec.(c) The average page replacement time is 9 msec.If page references are handled by the TLB 99% of the time, and only 0.01%lead to a page fault, what is the effective address-translation time?Draw the mapping cache memory for this system and view the details of the connection between cache memory and main memory with this parameter ? Cache is divide into two memories (one for data and another for instruction) Cache size 16 bytes (8 for data 8 for instruction) Block line size 16bytes Main memory size is 16Mbytes and each byte addressing to 24 bit address Cache design 2-way set associative

