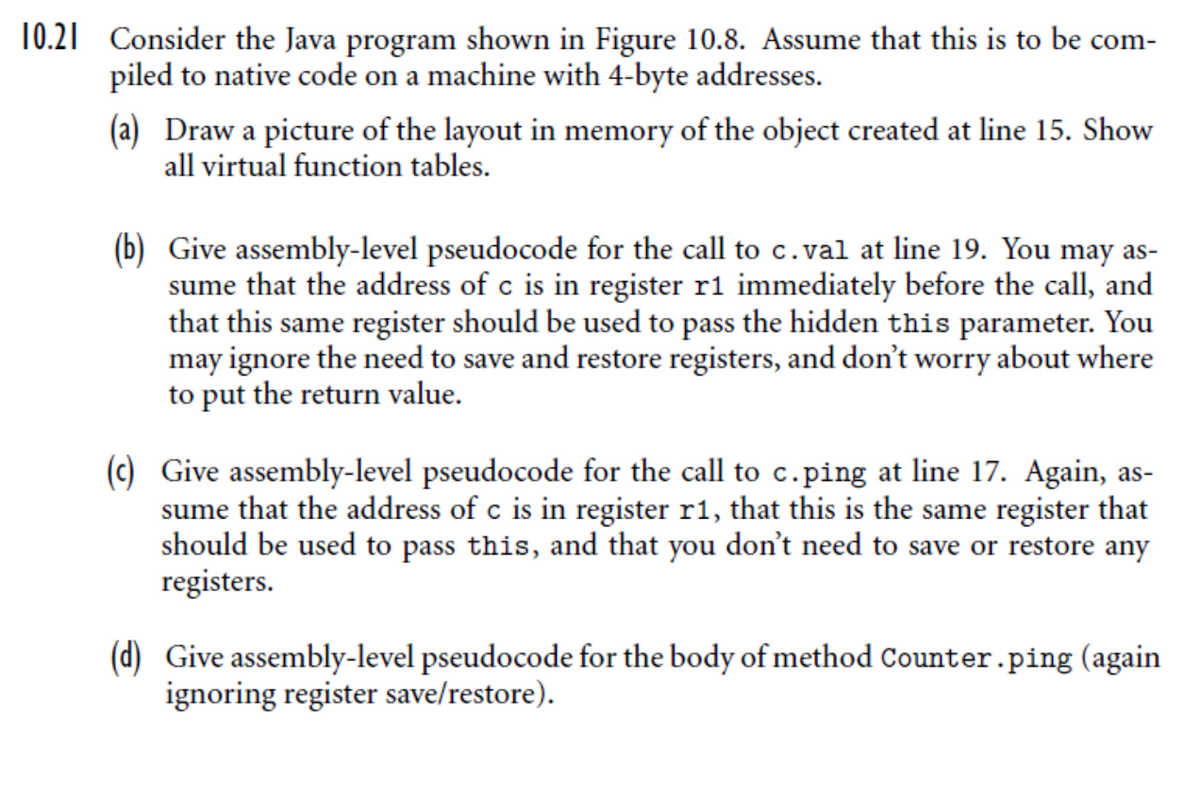
Consider the Java program shown in Figure 10.8. Assume that this is to be com- piled to native code on a machine with 4-byte addresses. (a) Draw a picture of the layout in memory of the object created at line 15. Show all virtual function tables.
Consider the Java program shown in Figure 10.8. Assume that this is to be com- piled to native code on a machine with 4-byte addresses. (a) Draw a picture of the layout in memory of the object created at line 15. Show all virtual function tables.
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter12: Points, Classes, Virtual Functions And Abstract Classes
Section: Chapter Questions
Problem 19SA
Related questions
Question
![interface Pingable {
public void ping();
1.
2.
3.
4.
class Counter implements Pingable {
int count =
public void ping() {
5.
0;
6.
7.
++count;
8.
}
9.
public int val() {
10.
return count;
11.
}
12.
public class Ping {
public static void main(String args []) {
Counter c = new Counter();
13.
14.
15.
c.ping();
c.ping();
int v = c.val();
System.out.println(v);
16.
17.
18.
19.
20.
21.
Figure 10.8 A simple program in Java.](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2F0eeffc8d-4542-4963-851c-14fc09a64fcf%2Fb22acb96-a27f-43a2-ad73-5b25babb3254%2F6idpp_processed.png&w=3840&q=75)
Transcribed Image Text:interface Pingable {
public void ping();
1.
2.
3.
4.
class Counter implements Pingable {
int count =
public void ping() {
5.
0;
6.
7.
++count;
8.
}
9.
public int val() {
10.
return count;
11.
}
12.
public class Ping {
public static void main(String args []) {
Counter c = new Counter();
13.
14.
15.
c.ping();
c.ping();
int v = c.val();
System.out.println(v);
16.
17.
18.
19.
20.
21.
Figure 10.8 A simple program in Java.
Transcribed Image Text:10.21 Consider the Java program shown in Figure 10.8. Assume that this is to be com-
piled to native code on a machine with 4-byte addresses.
(a) Draw a picture of the layout in memory of the object created at line 15. Show
all virtual function tables.
(b) Give assembly-level pseudocode for the call to c.val at line 19. You may as-
sume that the address of c is in register r1 immediately before the call, and
that this same register should be used to pass the hidden this parameter. You
may ignore the need to save and restore registers, and don't worry about where
to put the return value.
(c) Give assembly-level pseudocode for the call to c.ping at line 17. Again, as-
sume that the address of c is in register r1, that this is the same register that
should be used to pass this, and that you don't need to save or restore any
registers.
(d) Give assembly-level pseudocode for the body of method Counter.ping (again
ignoring register save/restore).
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning