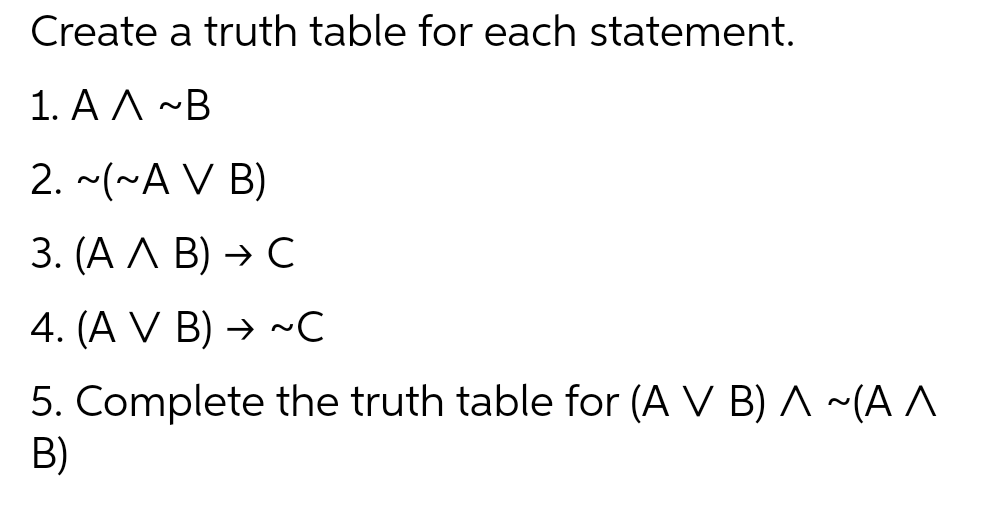
Create a truth table for each statement. 1. AA ~B 2. ~(~A V B) 3. (A A B) → C 4. (A V B)→ ~C 5. Complete the truth table for (A V B) A ~(A^ B)
Q: The implementation and maintenance of a web application involves a variety of challenges.
A: Intro: Here are some of the things that went into setting up and maintaining the web application.…
Q: Methods Java Write the appropriate method headings using the provided method name for the following…
A: Step-1: StartStep-2: Call function printArea and pass 4.5 as an argumentStep-3: Call fucntion…
Q: Define and discuss single and double buffering, and identify some of the issues they are attempting…
A: Buffering is used to efficiently handle speed disparities between the producer and the consumer in…
Q: Solving Differential Equation by Laplace Transform My Solutions > Solve the following initial value…
A: 1. Code: syms t s Y y(t) Dy = diff(y,t); D2y = diff(Dy,t); D3Y = diff(D2y,t);…
Q: Verion, release, and baseline are instances of software.
A: Introduction: Every single piece of software goes through a progression of steps before it is at…
Q: Network maintenance is an important task in organizations today who entirely rely on their network…
A: Part-a There are essentially two methods for network maintenance: Internal IT staff: With support…
Q: how would the diagram for question 2 look like.
A: Here we have given explanation with suitable diagram. You can find the solution in step 2.
Q: What is the main function of router?
A: The answer of the question is given below
Q: The characteristics that are inherently present in wireless networks give rise to a diverse set of…
A: Given: There are several difficulties brought on by the characteristics of wireless networks. Give…
Q: What printers can be allocated an IP address, and which ones can't?
A: Almost every printer can print a network setup page, which provides the printer's IP address. If…
Q: Explain the distinctions between open source and proprietary software by providing examples of both.…
A: Computer software Application software is a computer program that carries out specific academic,…
Q: In order for a sniffer attack to be regarded effective, what kind of actions are expected by the…
A: Data thefts known as sniffing attacks occur when packet sniffers are used to illegally access and…
Q: Write a program that prompts the user to enter two words. The program prints "true" if the two words…
A: Below I have provided Java Programming. Also, I have attached the screenshot of the code and output…
Q: There are many different kinds of digital memory that may be used, such as cache memory, hard disk…
A: Definition: There are numerous digital memory standards, so it would be beneficial if there were…
Q: The many stages of development for an information system are referred to together as the progression…
A: Information system An information system is a collection of various elements or entities that are…
Q: What is the main function of router?
A: Introduction: Routers are computer networking devices used to transport data packets from one…
Q: What is the main function of router?
A: Definition: A router is a network hardware device that enables communication between the Internet…
Q: How does an operating system's main memory become allocated to all of its many applications if it…
A: In this question we have to understand how an operating system main memory become allocated to all…
Q: Find at least three firms that provide free or shareware CASE tools on the Internet. Give an…
A: CASE Tools: A CASE tool is a piece of software used to model, evaluate, and record business…
Q: hat is code optimization? with relevant examples,explain the difference between machine dependent…
A: Optimization of code is necessary because non-optimized code take a lot of resources and is not…
Q: It would be helpful to include both an example and a description of a real-world SQL database.
A: The Answer start from step-2.
Q: When using the waterfall process, why is there a limit set on the total number of iterations that…
A: The waterfall approach uses a linear strategy called a software development sequence. The project is…
Q: An advanced UML diagram for a booking system with classes such as online booking site, reservation,…
A: We have to create UML diagram for the boking system.
Q: Testing at the unit level, testing at the integration level, and testing at the system level are all…
A: A unit test is a little piece of code that may be evaluated to ensure that your program functions as…
Q: The characteristics that are inherently present in wireless networks give rise to a diverse set of…
A: Given: There are several difficulties brought on by the characteristics of wireless networks. Give…
Q: Which mobile operating system works with the iPhone? Which mobile operating system was developed by…
A: The operating system which helps to execute application program software on the mobile devices is…
Q: What does the word "kernel mode" signify in terms of operating systems?
A: Introduction: Kernel mode: Kernel mode and system mode are the two working modes of the central…
Q: In order for a device to be able to physically connect to a network, what hardware component is…
A: Definition: When users log in to their computers and visit the networks page, they see a virtual…
Q: When it comes to the process of sending and receiving email over the internet, what are the most…
A: ANSWER:-
Q: in the position 0 through 3 of the register AL, while passing through the bits in the position 4…
A: The answer is given below step with an explanation :
Q: With non-systems analyses, it might be advantageous to use structured English to describe techniques…
A: utilize structured English to describe procesess unrelated to systems analysis will be discussed.…
Q: When it comes to the design of the operating system's microkernel, what type of philosophy is behind…
A: Introduction: The microkernel an operating system is built on the idea of the reducing the kernel to…
Q: Give an example of the meaning of the Visual Basic term Dim. Using visual basic, explain how to…
A: According to the question, we have to explain the Visual Basic term Dim with an example. And then…
Q: Look for methods to describe processes that aren't part of a systems analysis using Structured…
A: Given: The act of studying a procedure or business to discover its aim and purposes and build…
Q: The responsibility of the transport layer on the Internet is to ensure that data may be sent from…
A: Introduction: The transport layer is the fourth layer of network connections in the OSI model. As…
Q: What precisely does a Demilitarized Zone, which is more often referred to as a DMZ, bring to the…
A: Demilitarized Zone: An region that has been designated as a "demilitarize zone" by the parties to an…
Q: When the CMP instruction sequence is executed, what is the final value for AL register ? MOV AL, 25h…
A: Introduction: CMP instruction is used to compare the two operands. It does so by subtraction one…
Q: Installing software on a PC, a mobile device, or even a web browser involves the same basic…
A: Introduction: A software programme that may be transferred from one computer to another is referred…
Q: For this project, you will create a class for an elementary school that will allow a teacher to…
A: Java Code : - " Do this code in jdoodle"
Q: The next step, which follows the development of a list of the six components that make up an…
A: (IS) Information System: A system for organizing, storing, collecting, and sharing information is…
Q: ElGamal Digital Signatures: How do you make and validate them?
A: Introduction: ElGamal signature system is one of the digital signature generating mechanisms that is…
Q: Take into account the importance of wireless networks in countries that are still developing. Why do…
A: Introduction: Families with many electronic a devices, including PCs, laptops, and other mobile…
Q: When utilizing a WYSIWYG editor, what are the pros and drawbacks to be aware of?
A: We need to mention the pros and cons of utilising a WYSIWYG editor.
Q: What precisely does a Demilitarized Zone, which is more often referred to as a DMZ, bring to the…
A: A Demilitarized Zone: A "demilitarize zone" is an agreed-upon territory between the parties to an…
Q: e answer to this question is a resounding yesan IT infrastructure probl
A: Introduction: Below describe the resounding yes an IT infrastructure problem at the company
Q: What is the term for the protocol(s) used to deliver broadband data over the home network? (Choose 2…
A: The Internet Protocol is the organization layer correspondences convention in the Internet…
Q: How does this works in computer graphics, more specific in WebGL?
A: Here's the solution:
Q: Verion, release, and baseline are instances of software.
A: Examples of software releases, versions, and baselines: software releases Every piece of software…
Q: A device that stores MPEG formatted files called assets on hard or solid state drives to be viewed…
A: Complete answer is given below:
Q: printers can be allocated an IP address, and whic
A: Introduction: A network configuration page, which includes the printer's IP address, may be printed…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Can you please complete this code and explain every line please.3 please Find equivalent mutant and paste the code segment here please(b) Using IF function, write a formula in cell range D24 to display your recommendation. Hint: IF the Weighted Score of VDI is more than DaaS, then VDI should be recommended, else DaaS should be recommended. Thanks screenshot attached thanks thankz
- Please follow the step Please Use SUBLIME TEXT THANKSemail validation, use regular expression to check javascript format is <p>@<domain1>.<domain2>, it needs to follow the format and check <p> <domain1><domai> should have at least one character. also1.0Write a PHP echo statement to find out the user who owns the current script being run. 2.Complete the following code such that it determines when a script was last changed. echo date('g:i a, j M Y',___);
- (e) In cell E37, write a formula to compute Total Actual Visitors, copy the formula to cell E38. (f) Compute the percent increase in the Total Actual Visitors as compared to Expected mobile website visitors, write the formula in cell G37 and copy to cell G38. (g) In cell H37, Use the IF Function to create a formula to print "Yes" if the App Launch was beneficial to the firm; else, the formula should print "No". Copy the formula to cell H38.Hint: If the Percent increase is positive, then the launch is beneficial; else, it is not beneficial. SCREENSHOT ATTACHED THNAKSMake a School Fee Calculator using formula and Function in Excel. Provide your formula on the blank black cells. The specifications of the formula can be read from the comments, in each black cell. The white cells are the user-input elements. LABORATORY Year Level 4 #Comp. Lab: 0 Total Units 24 Rate/Comp Lab: 1,657.13 Rate Per Unit #Non-comp Lab: 0 Rate/Non-comp Lab: 750.00 Tuition Laboratory TYPES OF DISCOUNT Miscellaneous 3,125.25 Free-All TOTAL CHARGES Free Tuition Fee Downpayment 75% Discount Discount 50% Discount 1 NET CHARGES 25% Discount 10% Discount RATE BASED ON YR. LEVEL First Year 500.00 Prelim Balance Second Year 450.00 Midterm Balance Third Year 400.00 Semifinal Balance Fourth Year 350.00 Final Balance Fifth Year 300.00(b) Using IF function, write a formula in cell range D24 to display your recommendation. Hint: IF the Weighted Score of VDI is more than DaaS, then VDI should be recommended, else DaaS should be recommended. Screenshot attached thanks
- (i) Using the IF function, write a formula in cell L24 to determine if the number of hours rented for the given server is more than the average. Copy the formula from K25 to K41. (j) Using the IF function, write a formula in cell M24 to determine if the number of hours rented for the given server is more than the average. Copy the formula to M25 to M41. Screenshots attached below thank you!Analyze each statement whether it is true of false. Choose the appropriate letter from the options below. A if the first statement is true, but the second statement is false; B if the first statement is false, but the second statement is true; C if both statements are true; and D if both statements are false. 1. (1) Intrusion prevention is a reactive security measure.(2) Intrusion prevention uses an intrusion prevention system to preemptively block application attacks. 2. (1) Role Based Access Control is a discretionary access control which means that access is granted to roles defined on the systems.(2) It means that end users are assigned to roles so they can access assets needed for their jobs. 3. (1) Task Based Access Control is referred as the most complex model.(2) It means that the rules can change which role a user is assigned to. 4. (1) Hybrid VPN uses both methods of trusted and secured VPN.(2) It typically over several hops to the target network. 5. (1) Intrusion detection…The following code would include: SELECT P_DESCRIPT, P_PRICE FROM PRODUCT WHERE P_PRICE < ANY ( SELECT P_PRICE FROM PRODUCT WHERE LOWER(P_DESCRIPT) LIKE '%blade%'); A) Products that are less costly than all of the blades. B) Products that are less costly than the most expensive blade. C) An error message. D) Products that are less costly than the least expensive blade.





