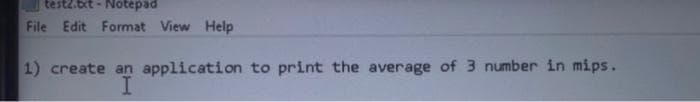
create an application to print the average of 3 number in mips.
Q: 149. Write a C# Sharp program to create a new list from a given list of integers removing those valu...
A: C#: C# is a simple and powerful object oriented programming language. It is developed by Microsoft a...
Q: Describe the processing of a C++ Program from editor to execution.
A: What is the editor? Editors are software programs that are used by the user to create and edit text ...
Q: Can you convert this to basic c language? The output must be like the one on the photo #include ...
A: As given, we need to convert the given C++ code into basic C language. I have provided the code in C...
Q: Damon Davis was putting the finishing touches on the Drano Plumbing Company's spreadsheet when we me...
A: Answer: The $50,000 was put on the debit side instead of the credit side. Retained earnings should ...
Q: 149. Write a C# Sharp program to create a new list from a given list of integers removing those valu...
A: The above C# pogram is answered in next step here we take the sample input array and find the outp...
Q: Implement constructors for each of the three subclasses. Each constructor should call the superclass...
A: three sub class of the main class and constructor of each subclass is call on the super class
Q: Create a Java program that asks the user to enter three (3) first names then display the following: ...
A: Algorithm: Start Read 3 names and store them in an array named names Declare a string array uname o...
Q: Why is it possible to do several different actions on a same stream by using a publish-subscribe sys...
A: Introduction: An operation is saved in a topic in the publish-subscribe system. Unlike a point-to-p...
Q: In C Language please.. Let's make a simple program that mirrors this beautiful idea where we ask ...
A: #include <stdio.h> void slowDisplay(int, int);int main(void){ int start, nextCount; ...
Q: A-System.out.print(Math.floor(5.7);
A: In Java, we have Math.floor(double x) which returns the nearest mathematical integer value that is ...
Q: Consider the Case study and answer the question below. Scenario: The Ministry of Health is planning ...
A: Answer-'d' There are lots of methods for software testing but for this model the best type of testin...
Q: Explain the seven phases of the Systems Development Life
A: SDLC stands for software development life cycle, it is a method of developing high quality software....
Q: In a royal casino, there is a lottery at 134 number card. If a person is playing that game, find the...
A: Java Code import java.util.*; // importing the required modules using the * operatorpublic class Ma...
Q: fo/0 192.168.1.10/24 PC-1 f0/0 Google 150.150.150.2/2 fo/1 ISP Sw R1 150.150.150.1/28 fo/0 100.100.1...
A: Introduction: NAT is an abbreviation for network address translation. It's a method of mapping numer...
Q: Please enter all answers as strings of 0's and 1's. Consider the 64 bit DES block below. 001000000...
A:
Q: E-R model is an acronym for this. Encircle the correct choice. a. Entity reference model b. Event re...
A: According to the information given:- We have to choose the correct option to satisfy the statement
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in ...
A: Given : To write a php program to convert temperature in Fahrenheit from the degree celsius.
Q: Use C sharp language and code must get compiled in visual studio. ---------------------------------...
A: Here are some points to note exceptions can be caught by using try and catch block try block is u...
Q: When the ME Reset vector Interrupt vector General purpose Flag regietoro
A: When the MPU starts up for the first time it goes to the and begins executing. Reset vector Interru...
Q: Many firms are now implementing big data initiatives. Discuss it, as well as how and why it is used ...
A: Introduction: Big data is a collection of unstructured, semi-structured, and structured data gathere...
Q: endent 4 swi
A: Independent 4 switch table
Q: An action is taken if the condition is true, otherwise the control goes to the next statement. * O I...
A: If statement: This statement is used to executed block of statement if the condition is true. Do whi...
Q: Using your favourite sport as an example, describe how predictive mining methods may be employed by ...
A: Answer: A cricket sports team may gather a lot of data regarding the event.Some team members perform...
Q: Let E = {0, 1} and A, B be the list of three strings each. Verify below PCP has a solution or not? L...
A: The Answer is in below Steps
Q: Create the following table in your database with the following schema: Table: orders | Column Name 1...
A: Here are all the queries:
Q: Instruction: Based on your readings about the primary sources and secondary sources in acquiring his...
A: Lets see the solution in the next steps
Q: Convert to LEGV8 int main() int set1[5]; int set2[5]; int total=0; set1[0] = 1; for(int i=1; i<5; i+...
A: check further steps for the answer :
Q: Create a Java program that asks the user to enter three (3) first names then display the following 1...
A: 1)Read first names from user 2)use for loop concatenate to one first name with other 3)print the a...
Q: A-System.out.print(Math.floor(5.7);
A: Here, I have to provide an answer to the above question.
Q: s may contain a lot of properties in certain applications, with the majority of them being null. Is ...
A: Lets see the solution.
Q: What additional fundamental parts are found in the central processing unit (CPU)?
A: CPU stands for Central Processing Unit it is also known as the brain of the computer. CPU receives t...
Q: chis true? D Yes!
A: given - msh7 . c can be terminated with exit , but mshs. c cannot.Is this true? Yes!NO!
Q: Say you are given a hash function that produces a 224-bit digest, along with a message digest d. Usi...
A: In both math and cryptography, given a capacity H from set A to set B, and a component b in B, a pre...
Q: computer Ada Lovelace came up with what ideas.
A: Ada Lovelace realized that a computer could be programmed to obey a set of instructions, which she c...
Q: What level(s) of input/output manipulation can an assembly language programme perform?
A: Introduction: An assembly language statement is a line of text that translates into a single machine...
Q: Write a python program to find the median of two lists when the lists are merged into a single list....
A: logic:- iterate for each element in lst1 and append it to lst3. End loop Iterate from i=0 to i<...
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in ...
A: Here is your php code with an output :-
Q: An alternate approach would be to store shared structures in the local memory of a specific process ...
A: Introduction: Local memory, in the context of a computer with several processors, refers to memory t...
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in ...
A: logic:- read degree Celsius from user. Multiply it by 9 and divide it by 5. Add 32 at last. Displ...
Q: A short history of evolution and computer systems in terms of technology and trends should be given
A: A short history of evolution and computer systems in terms of technology and trends should be given
Q: Write a JAVA program in which the user enters the initial velocity u, time of travel t, and the acce...
A:
Q: Machine learning/deeplearning in additive manufacturing how to find projects or examples to learn t...
A: Lets see the solution.
Q: Moore's law has a big impact on super computing, grid computing, and cluster computing, so we'll loo...
A: Moore’s law: Moore’s law is the law which precepted about the chip of transistors. It stated that in...
Q: What is the hexadecimal and decimal representation of the ASCII capital B character?
A: ASCII represents American Standard Code for Information Interchange and is frequently involved desig...
Q: Draw the shape used in the object-based logical model of the following. a. Attributes b. Entity sets...
A: a. An attribute defines the characteristic/property of an attribute The shape of the attribute in th...
Q: Who made the first microprocessor?
A: Computers in the Beginning: The early electrical computers were colossal in size. ENIAC, for example...
Q: 1. Does deleting row [C002] in CUSTOMER affect referential integrity? Why or why not? Limit your ans...
A:
Q: Write a JAVA program in which the user enters the initial velocity u, time of travel t, and the acce...
A: Required:- Write a JAVA program in which the user enters the initial velocity u, time of travel t, a...
Q: In JAVA language, write a program to input the x and y coordinate of a point in the first quadrant a...
A: Code: import java.util.Scanner; public class Main{ public static void main(String[] args) { bool...
Q: For WriteString, describe what it does
A: Introduction: First, we'll look at the WriteString function. It is necessary to write into the blo...
Step by step
Solved in 2 steps with 1 images

- Python- Write a script that uses the hashlib module to hash a user entered password and then write the hashed password to a file. Use the input function to prompt the user for the password Hash the password using the hashlib md5 function. Use utf-8 encoding. Include the new line (\n) character when you write the hashed password to the file.3 please Find equivalent mutant and paste the code segment here pleasePlease use javascript to write the function. write the code for the edit() function. This function prompts the user for a unique code. If the entered unique code is matched with the random-generated unique code for the respective user, store the user index and reason index to the local storage with their relevant key. Then redirect the user to the edit page. Otherwise, if the unique code cannot match with the user’s random-generated unique code, alert the user by mentioning that incorrect unique code.
- Fill in the blank question- Only answer needed without explanation Q. /dev represents_____________files.Question 9 nag.A text file contains: aaaabcc aabbbbc aacc a ats bart cube Write a regular expression that will match only lines 1, 2, and 3. Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line// Ex 7-1.cpp in this exercise you will use what you learned about opening a file and reading input //Read and follow the comments submit your code through the Exercise one quiz #include <fstream> #include <iostream> #include <string> using namespace std; int main() { //this is the code for exercise 7-1 ofstream data_in; //find and fix the error in this line data_in.open(myDVDFile.dat); //find and fix the error in this line string dvdName, dvdPrice, dvdShelf; data_in >> dvdShelf; data_in >> dvdPrice; data_in >> dvdName; /* use notepad to create a datafile named myDVDFile.dat that contains the following data Fargo 8.00 1A Amadaus 2.00 2C Casino 7.50 3B */ //add print statements to output dvdShelf, dvdPrice, dvdName record the values in your workbooks // there is a problem with the values fix it } // End of main function
- Create a brief code segment that moves the file pointer 50 bytes from the file's start. Assume the file is already open and BX has the file handle.'373. File operation used with random access files to first position pointer to a specific place in a file, is known to be a. Pointer b. Cursor c. Current locator d. SeekCode in C language. Please provide code for 3 different files. One header file and two .C files. I need the code for each file. Please provide photos of the output and source code for each file (3). Please follow All instructions in the photo provided. Use the provided input.txt file provided below. A1, A2 20294 Lorenzana Dr Woodland Hills, CA 91364 B1, B2 19831 Henshaw St Culver City, CA 94023 C1, C2 5142 Dumont Pl Azusa, CA 91112 D1, D2 20636 De Forest St Woodland Hills, CA 91364 A1, A2 20294 Lorenzana Dr Woodland Hills, CA 91364 E1, E2 4851 Poe Ave Woodland Hills, CA 91364 F1, F2 20225 Lorenzana Dr Los Angeles, CA 91111 G1, G2 20253 Lorenzana Dr Los Angeles, CA 90005 H1, H2 5241 Del Moreno Dr Los Angeles, CA 91110 I1, I2 5332 Felice Pl Stevenson Ranch, CA 94135 J1, J2 5135 Quakertown Ave Thousand Oaks, CA 91362 K1, K2 720 Eucalyptus Ave 105 Inglewood, CA 89030 L1, L2 5021 Dumont Pl Woodland Hills, CA 91364 M1, M2 4819 Quedo Pl Westlake Village, CA 91362 I1, I2 5332 Felice Pl…
- The "-t" flag to "ls" sorts the listing by modification time. Write a BASH line which will write the name of file with the oldest modification time into a file called "lastfile".COMPLETE TO DO's (do not copy other responses to this question if you do ill downvote) recv.cpp #include <stdio.h>#include <stdlib.h>#include <string.h>#include <fcntl.h>#include <mqueue.h>#include <sys/stat.h>#include <sys/types.h>#include <sys/mman.h>#include <unistd.h>#include <signal.h> // The name of the shared memory segment#define MSQ_NAME "/cpsc351queue" // The name of the file where to save the received file#define RECV_FILE_NAME "file__recv" #define MQ_MSGSIZE 4096 /*** Receive the file from the message queue*/void recvFile(){ // TODO: Define a data structure // of type mq_attr to specify a // queue that can hold up to 10 // messages with the maximum message // size being 4096 bytes // The buffer used to store the message copied // copied from the shared memory char buff[MQ_MSGSIZE]; // The total number of bytes written int totalBytesWritten = 0; // The number of bytes written int…Function ________repositions the file position pointer to a specific location in the file



