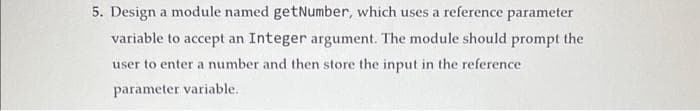
Design a module named getNumber, which uses a reference parameter variable to accept an Integer argument. The module should prompt the user to enter a number and then store the input in the reference parameter variable.
Q: Provide concrete examples of data manipulation, forgeries, and web jacking.
A: We have to explain what is data manipulation, forgeries, and web jacking. also we have to provide…
Q: Show the results of inserting the keys: F, L, O, R, I, D, A, U, N, V, M, Y, C, S in order into an…
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: 1. Given the following dennition of fun, what will be output by the call funi (4): void fun1(int n)…
A: We have toi explain that what is the output of the function when we call fun(4). void fun1(int n)…
Q: orm solution for the well-known mathematical puzzle, the Towers of Hanoi, is: Hn = 2Hn−1 + 1, n ≥ 2,…
A: To prove the correctness of the closed-form solution for the Towers of Hanoi puzzle, we will use…
Q: It is up to you to determine what steps to take in response to criminal activity online. What are…
A: Answer: Conclusion. Cyber security is one of the most important aspects of today's rapidly…
Q: What Kind of Conceptual Framework Does Cybercrime Analysis Have? When you respond, try to be as…
A: Cybercrime analysis involves the systematic study and investigation of cybercrimes, their motives,…
Q: When you look at the properties of a file, what kinds of information can you learn about that file?
A: When you look at the characteristics of a file, what information can you find out about it? By…
Q: The class will begin with: public abstract class Airplane { Include at least 4 private…
A: Sample abstract class for an airplane in java is as follows: public abstract class Airplane {…
Q: When deciding how to approach a problem, is it better to work alone or in a group?
A: One of the elements that determines whether one person or more is required is the intricacy of the…
Q: Developing a conceptual framework for comprehending online criminal activity. Please offer evidence…
A: Introduction: Online criminal activity has become an increasing concern in recent years due to the…
Q: The bulk of the code base is distributed on the web in tarball format. Does this assertion hold true…
A: The tar ball format is the one of the oldest formats available, and it may be used for archiving…
Q: Write a report (EC1_Document.pdf) comparing the efficiency of multilevel array and multi-…
A: Report: Efficiency Comparison of Multilevel Array and Multi-Dimensional Array
Q: putting up a conceptual structure for the purpose of analysing cybercrime. If you make statements,…
A: Introduction: Cybercrime is a growing problem in the modern world, with advancements in technology…
Q: Explain each of the following ideas using both common language and the language of computers:…
A: Problem-solving: Issues involve articulating a problem, discovering its cause, finding,…
Q: In the context of the healthcare business, please provide an explanation of the primary tasks and…
A: Introduction: The CIO (chief information officer) is an executive at a healthcare organization that…
Q: Workers who break the security policy of a corporation run the danger of having the following…
A: The sanctions that workers who break the security policy of a corporation may face can vary…
Q: Question 1: Using static analysis study the following code snippets to determine the developer…
A: A)From a static analysis of the code snippet, we can identify the following developer error/fault:…
Q: a) Assuming a Carry skip adder with the following stages: Stage 1 3 4 # of bits 4 6 2 5 7 5 5 b)…
A: a) Assuming a Carry skip adder with the following stages: Stage 1 2 3 4 5 6 7 8 # of bits 4 5 6 7 5…
Q: 7. Give a big-O estimate for f(x) = (x + 1) log(x² + 1) + 3x².
A: Answer the above question are as follows
Q: Answer these: 1. Encode the binary number as even parity Hamming codes: 1011100101011011 2. What…
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: The acronym "USB" stands for "Universal Serial Bus," which is what it refers to.
A: Please find the answer in next step
Q: WPA2 should be your wireless connection of choice if you want to stay secure. What makes this choice…
A: WPA2 (Wi-Fi Protected Access II) is a wireless security protocol that was introduced as an upgrade…
Q: Just what does it imply when something is said to be operating on the.NET Framework?
A: According to the question, the NET framework is the instrument that developers used to create…
Q: In this lab, you will create a backend class called SortableSet. A set, in computer science, is an…
A: Here's an implementation of the SortableSet class that meets the requirements you've described.…
Q: A number of content providers have launched their own own social networks. Provide a high-level…
A: Answer is
Q: Do in-depth analysis on the application that has object-oriented design (OO)
A: Introduction: Object-oriented design (OO) is a programming paradigm that revolves around the concept…
Q: What is the single most essential thing that one should keep in mind while dealing with prototypes…
A: We'll comprehend the fundamental idea behind using the prototype technique while creating software.…
Q: The signal is modulated in which stage: O a. Channel O b. Transmitter O c. Receiver
A: We have to explain that the signal is modulated in which stage we have to also explain every stages…
Q: Please offer the names and brief explanations of three different methodologies for evaluating the…
A: Threat modeling is a methodology for identifying and analyzing potential security threats by…
Q: of Conceptual Framework Does Cybercrime A en you respond, try to be as specific as possi
A: Introduction: Cybercrime analysis involves the systematic study and investigation of cybercrimes,…
Q: Answer the given question with a proper explanation and step-by-step solution. The base class Pet…
A: Note :- You have not mention the language of the program so, I'm answering your question in Java…
Q: If you're worried about the security of your human resources information system, here are 10…
A: Human Resources Information System: The HRIS, also referred to as the human resources information…
Q: Use python to write different codes that show from 1999-2016 in US adults a. The estimated energy…
A: Python code snippets that demonstrate the different trends described: a. Code: import numpy as…
Q: Add: (2g^(3)+4h)+(8g^(3)+3h) Enter the correct answer.
A: Addition is a mathematical operation that involves combining two or more numbers or quantities to…
Q: How can I determine whether or not a given command includes the extended indication?
A: To determine whether a given command includes the extended indication, you will need to provide more…
Q: To what end specifically does the use of formal techniques aim to be successful? It is strongly…
A: To what end specifically does the use of formal techniques aim to be successful? I
Q: cks to using a more formal methodology? At least four different considerations make the use of…
A: Given : Are there some benefits as well as drawbacks to using a more formal methodology? At least…
Q: The conversion from RGB to HIS colors is broken down into its component parts and discussed in…
A: Color conversion from RGB to HIS 1. Use the 'imread' function to read the RGB picture. 2. Each RGB…
Q: It is important that the Assistant Managers at Telenor get training on the subject of employee…
A: According to the supplied information: Telenor need a Training Program for Assistant Managers on…
Q: Let R be an equivalence relation on A = {0, 5, 7,9} and R = {(0, 9), (0, 5), (7, 7), (9,5), (5, 9),…
A: Since R is an equivalence relation, it partitions A into equivalence classes. An equivalence class…
Q: Is it possible to explain cost and costing, as well as the significance of accurately estimating…
A: Introduction: Cost and costing are essential concepts in product management, as they help businesses…
Q: a) AlgorithmX(n) 1. xfl 2. for i 1 to n² 3. x←max(x,i) 4. for j1 to n² 5. x←max(x.j) 6. return x b)…
A: a) Answer: The Big O analysis for the given code snippet is O(n^2), which means that the time…
Q: Members of Set A = {Monday, Tuesday, Wednesday, Friday, Saturday, Sunday} What is the cardinality…
A: Cardinality of a set is:
Q: It is essential to do an analysis of the characteristics of a "good" requirements document rather of…
A: The answer to the question is given below:
Q: For example, I am a security officer for an organization. I am tasked to create a security policy…
A: As a security officer, you should implement a comprehensive security policy that includes the…
Q: Kevin plans to use a Boolean operator to look for data on two different topics. Which Boolean…
A: Solution In order to look for the necessary information The AND boolean operator is used on both of…
Q: How strongly does he stress the need of having an efficient cyber defense strategy throughout his…
A: The importance of cyber security lies in the fact that it guards against the loss of all types of…
Q: Throughout the process of designing software, a variety of models are used, and the utility of each…
A: It's crucial to take into account the numerous processes needed for the project's ultimate release…
Q: Describe in detail giving examples the concept of Abstraction, Encapsulation, Inheritance and…
A: Answer is
Q: While deciding on a method of wireless connection for your house, it is important to think about…
A: The answer is given in the below step
Question 17 mammi
.PSEUDOCODE
Full explain this question and text typing work only
We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line
Step by step
Solved in 2 steps

- Which of the following is false?a. A function can return one or more values to the statement that invoked it.b. A function can accept one or more items of data passed to it.c. The parameterList in a function header is optional.d. At times, a memory location inside the computer’s internal memory may have more than one name.Which of the following is not a step in the function-calling process?a) The calling program suspends.b) The formal parameters are assigned the value of the actual parameters.c) The body of the function executes.d) Control returns to the point just before the function was called.Create a void function, “displayMenu”, for the menu that is used forselecting the options. The function declaration is void displayMenu(); Create a function “callExponentialFunction”. The function body containsall code for getting user input and returning the value of the call of thepredefined “exp” library function. The function declaration is below.double callExponentialFunction(); Create a function “callLogarithmFunction”. The function body contains allcode for getting user input and returning the value of the call of thepredefined “log10” library function. The function declaration is below.double callLogarithmFunction(); Create a function “callMaximumFunction”. The function body contains allcode for getting user input and returning the value of the call of thepredefined “fmax” library function. The function declaration is below.double callMaximumFunction(); Create a function “callMinimumFunction”. The function body contains allcode for getting user input and returning the value of…
- Design a program using Flowgorithm that will accept a number representing a class and then displays the name of the class. Continue modifying the program so that the numeric class request can only enter continuously until a sentinel value is entered. Then display each class number, name, and a count of the number of request for each class.Write a function named “endingWithSlashSlash” that accepts the same parameters as command line arguments (argc and argv). It returns true if at least one of the arguments have a “//” at the end and false otherwise. This function also returns the number of arguments that have “//” at the end. For example, “//” will return true and 1 “one// two three// four” will return true and 2 “one” will return false and 0 “one two” will return false and 0 Please note that for question #5, you cannot refer or use string class, string methods such length() or size() or any string function such as strlen(), strcmp or strstr(). Please use only array notation, pointer to character, and/or pointer arithmetic and make use of the fact that this is a C-string.A student imports a module called dnautil in Python using the following command: import dnautil What does the following call to the dir function do? dir(dnautil) Lists the gc and has_stop_codon functions Prints all the documentation associated with the function dir Lists all the attributes of the dnautil module Lists all the functions in the dnautil module
- parameter list can also contain the data type of the output of function : true/false a function declared int addition (int a and b) is capable of returning one value back to the main loop : true/false main () is a void function: true / false the address returned by the reference pointer is always the same regardless of operating system: true/false a function declares as int addition (int a, int b) has a and b as output arguments : true/ falseAssignment #2 Instructions: Through this programming assignment, the students will learn to do the following: Learn to work with command line options and arguments Gain more experience with Makefiles Gain more experience with Unix Learn to use some of the available math functions available with C Usage: mortgagepmt [-s] -r rate [-d downpayment] price In this assignment, you are asked to perform a mortgage payment calculation. All information needed for this will be passed to the program on the command line. There will be no user input during the execution of the program You will need a few pieces of information. The price of the home and the amount of the down payment. You will also need to know the interest rate and the term of the mortgage. To figure your mortgage payment, start by converting your annual interest rate to a monthly interest rate by dividing by 12. Next, add 1 to the monthly rate. Third, multiply the number of years in the term of the mortgage by 12 to calculate the…C ++ - Create a program that calculates the distance an object travels in meters on Earth for a specific number of seconds. Also calculate the distance traveled on the moon, also in meters, for a specific number of seconds. Do not include any global variables Your program must have the main function and, at least, the following four additional functions. The signatures for these functions must be as follows: double readSeconds() double calculateEarthDistance(double seconds) double calculateMoonDistance(double seconds) void displayResults(double seconds, double earthDistance, double moonDistance) The readSeconds function will be an input function that will read in a double value from cin and return that value back to main. The calculateEarthDistance function will calculate the distance an object falls (on Earth) during the specified number of seconds. The calculateMoonDistance function will calculate the distance an object falls (on the Moon) during the specified number of seconds. The…
- Which statement is incorrect about virtual function? a. Each virtual function declaration starts with the virtual keyword b. All of these options are correct c. They are used to achieve runtime polymorphism d. They are used to hide objects Clear my choiceI have two codes. One is validator and another is main code. Please make the main code follow requirement of validator like assertation. requirenment. Validator:--------- @points(5)def test_flour_sack():"""Testing flour_sack"""module = import_file("pizza.py")_test_ingredient(module.flour_sack, "flour") @points(5)def test_yeast_jar():"""Testing yeast_jar"""module = import_file("pizza.py")_test_ingredient(module.yeast_jar, "yeast") @points(5)def test_salt_shaker():"""Testing salt_shaker"""module = import_file("pizza.py")_test_ingredient(module.salt_shaker, "salt") Main code:------ from time import time def flour_sack(capacity=10):for i in range(capacity):yield 'flour ' def yeast_jar(capacity=20):for i in range(capacity):yield 'yeast ' def salt_shaker(capacity=100):for i in range(capacity):yield 'salt ' def water_faucet():while True:yield 'water' if __name__ == "__main__":passCreate a C++ application that will allow you to build two functions for multiplication as well as modulus. The two numbers must be passed to the function as an argument from the main function. Within the functions, the outcomes are displayed.







