Display only the products (name and ID) that have a quantity greater than the average quantity of all products.
Display only the products (name and ID) that have a quantity greater than the average quantity of all products.
Database Systems: Design, Implementation, & Management
12th Edition
ISBN:9781305627482
Author:Carlos Coronel, Steven Morris
Publisher:Carlos Coronel, Steven Morris
Chapter3: The Relational Database Model
Section: Chapter Questions
Problem 25P: Create the ERD. (Hint: Look at the table contents. You will discover that an AIRCRAFT can fly many...
Related questions
Question
Display only the products (name and ID) that have a quantity greater than the average quantity of all products.
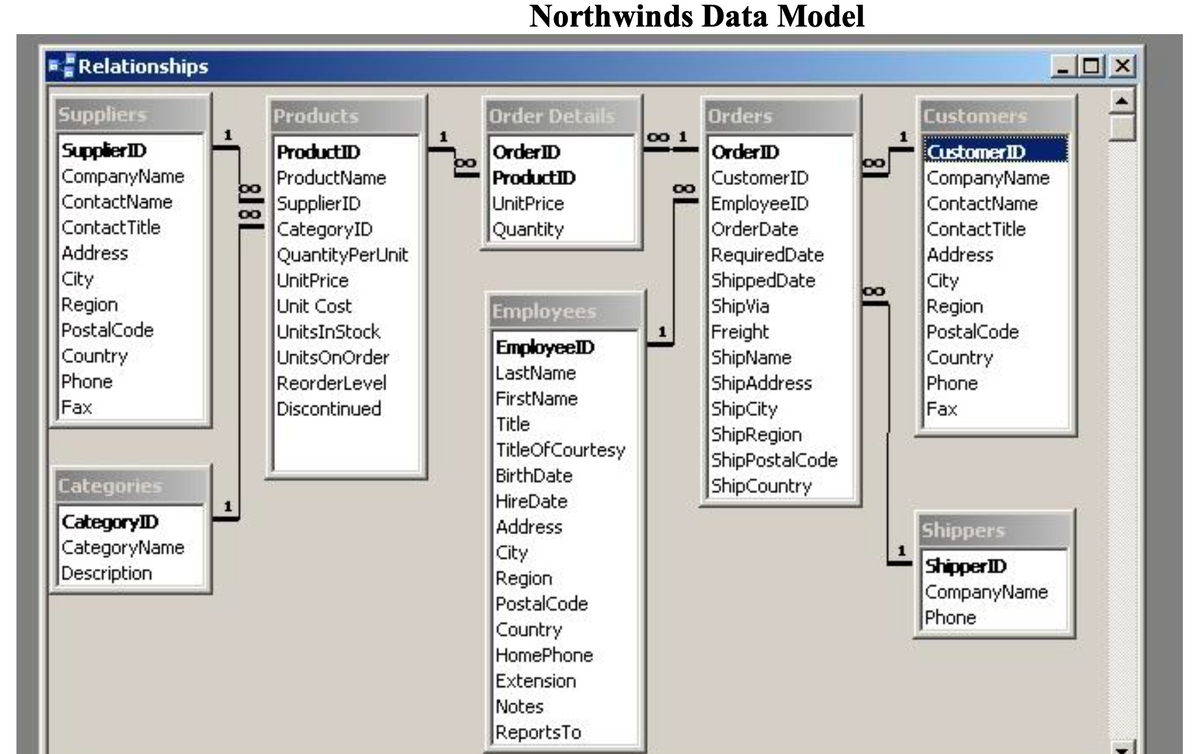
Transcribed Image Text:Relationships
Suppliers
Supplier ID
CompanyName
ContactName
Contact Title
Address
City
Region
PostalCode
Country
Phone
Fax
Categories
CategoryID
CategoryName
Description
8181
Products
ProductID
ProductName
Supplier ID
CategoryID
QuantityPerUnit
UnitPrice
Unit Cost
UnitsInStock
UnitsOnOrder
ReorderLevel
Discontinued
Northwinds Data Model
Order Details
Order ID
ProductID
UnitPrice
Quantity
Employees
EmployeeID
LastName
FirstName
Title
TitleOfCourtesy
BirthDate
HireDate
Address
City
Region
PostalCode
Country
HomePhone
Extension
Notes
Reports To
Orders
Order ID
Customer ID
EmployeeID
OrderDate
RequiredDate
ShippedDate
ShipVia
Freight
ShipName
ShipAddress
ShipCity
ShipRegion
ShipPostalCode
ShipCountry
8
Customers
Customer ID
CompanyName
ContactName
Contact Title
Address
City
Region
PostalCode
Country
Phone
Fax
Shippers
Shipper ID
CompanyName
Phone
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

