Each of the four color buttons will display an image of an appropri colored jacket in the picture control whose name is picJacket. The different colored images are stored in the BlackJacket.png, BlueJacket.png, BrownJacket.png, and RedJacket.png files. • When the user clicks the Black button, the black jacket should app the picture control. The same thing for the remaining buttons.
Each of the four color buttons will display an image of an appropri colored jacket in the picture control whose name is picJacket. The different colored images are stored in the BlackJacket.png, BlueJacket.png, BrownJacket.png, and RedJacket.png files. • When the user clicks the Black button, the black jacket should app the picture control. The same thing for the remaining buttons.
Chapter16: Graphics
Section: Chapter Questions
Problem 2PE
Related questions
Question
Transcribed Image Text:Shee
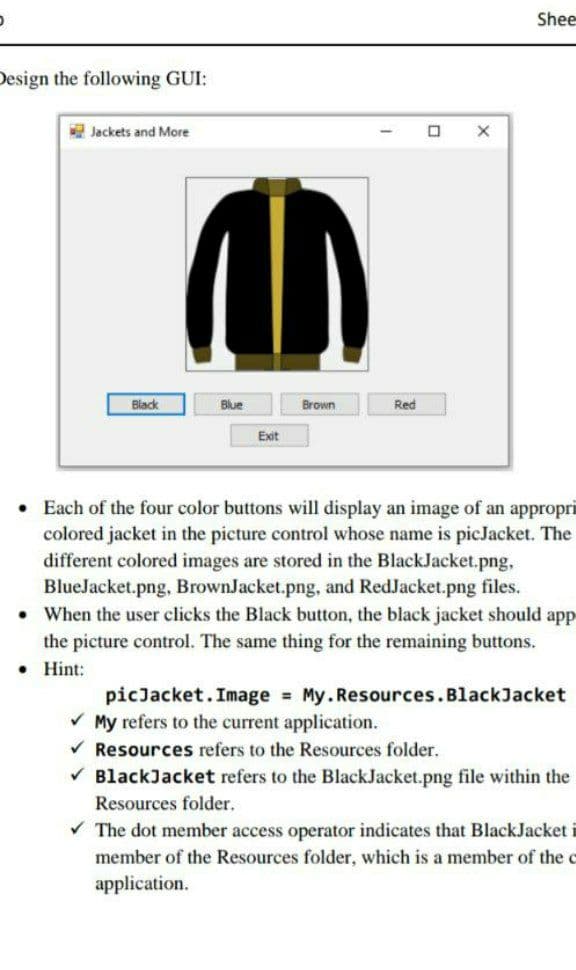
Design the following GUI:
Jackets and More
Black
Blue
Brown
Red
Exit
• Each of the four color buttons will display an image of an appropri
colored jacket in the picture control whose name is picJacket. The
different colored images are stored in the BlackJacket.png,
BlueJacket.png, BrownJacket.png, and RedJacket.png files.
• When the user clicks the Black button, the black jacket should app
the picture control. The same thing for the remaining buttons.
• Hint:
picJacket.Image My.Resources.BlackJacket
V My refers to the current application.
V Resources refers to the Resources folder.
V BlackJacket refers to the BlackJacket.png file within the
Resources folder.
V The dot member access operator indicates that BlackJacket
member of the Resources folder, which is a member of the c
application.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 7 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781305480537
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781305480537
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage