Given the class definitions of MPoint and Named Point below, which of the constructors would be valid class? (Select all that apply) class MPoint { private int myX; // coordinates private int myY; public MPoint() { myX= 0; myY= 0; } public MPoint(int a, int b) myx = a; myY = b; } } // ... other methods not shown } public class NamedPoint extends MPoint private String myName; // constructors go here // ... other methods not shown Opublic NamedPoint(int d1, int d2, String name) { myx = d1; myy=d2; myName = name; } Opublic NamedPoint() { myName = ""; } Opublic NamedPoint(int d1, int d2, String name) { super(d1, d2); myName = name; }
Given the class definitions of MPoint and Named Point below, which of the constructors would be valid class? (Select all that apply) class MPoint { private int myX; // coordinates private int myY; public MPoint() { myX= 0; myY= 0; } public MPoint(int a, int b) myx = a; myY = b; } } // ... other methods not shown } public class NamedPoint extends MPoint private String myName; // constructors go here // ... other methods not shown Opublic NamedPoint(int d1, int d2, String name) { myx = d1; myy=d2; myName = name; } Opublic NamedPoint() { myName = ""; } Opublic NamedPoint(int d1, int d2, String name) { super(d1, d2); myName = name; }
Chapter10: Introduction To Inheritance
Section: Chapter Questions
Problem 6RQ
Related questions
Question
25
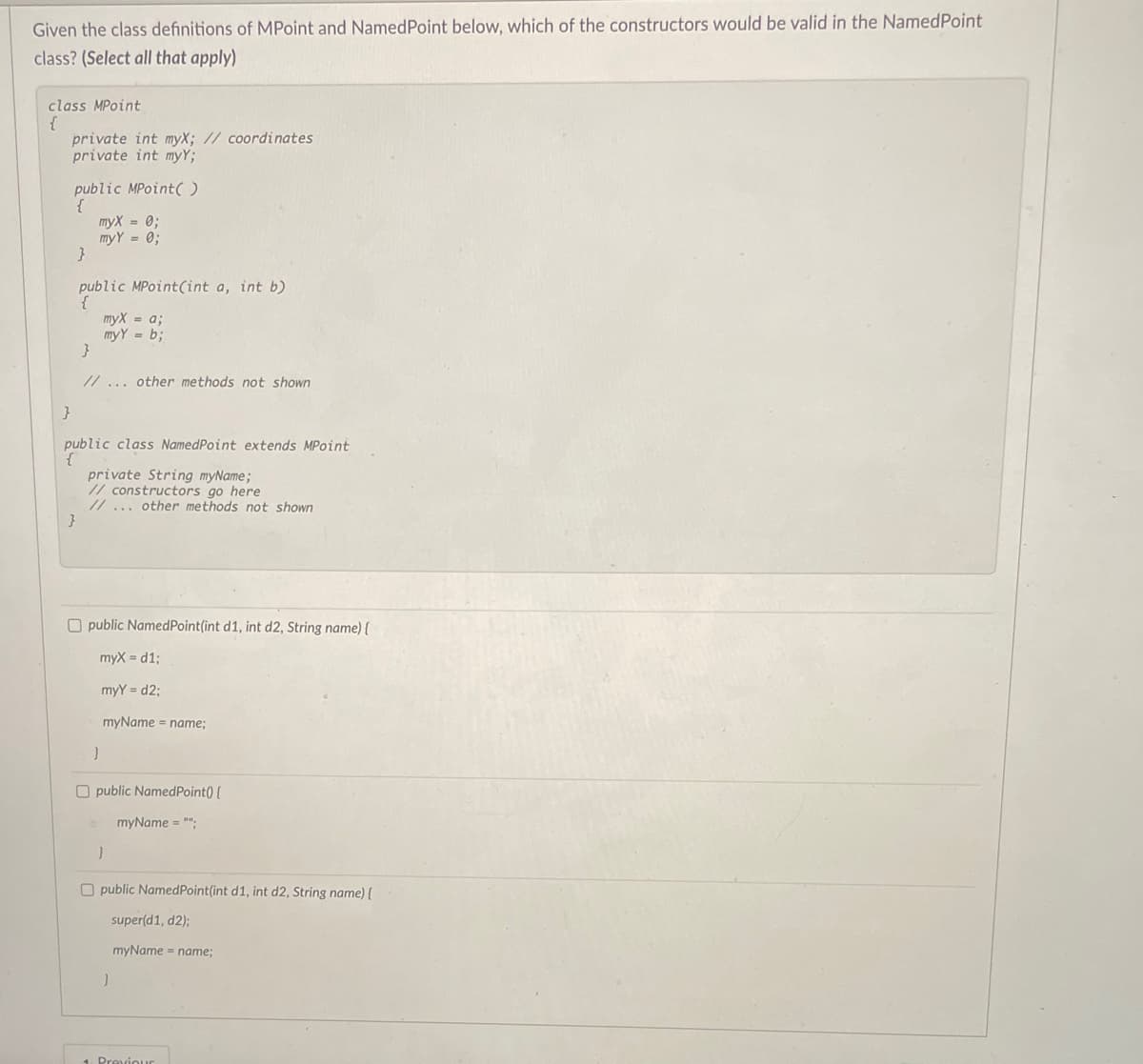
Transcribed Image Text:Given the class definitions of MPoint and Named Point below, which of the constructors would be valid in the NamedPoint
class? (Select all that apply)
class MPoint
{
private int myX; // coordinates
private int myY;
public MPoint()
myx = 0;
my Y = 0;
}
public MPoint(int a, int b)
myX = a;
myY= b;
}
}
// ... other methods not shown
}
public
public
private String myName;
// constructors go here
// ... other methods not shown
class NamedPoint extends MPoint
Opublic NamedPoint(int d1, int d2, String name) {
myX=d1;
myy=d2;
myName = name;
}
Opublic NamedPoint() {
myName = "";
}
Opublic Named Point(int d1, int d2, String name) {
super(d1, d2);
myName = name;
}
1 Previour
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT