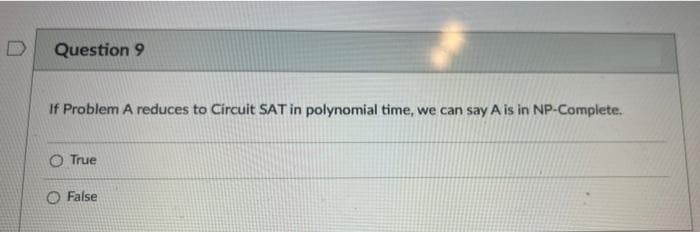
If Problem A reduces to Circuit SAT in polynomial time, we can say A is in NP-Complete.
Q: Consider the LFSR represented by the polynomial x^4+x^3+1 What are the tap bits of the LFSR? Please ...
A: The bits in the LFSR state that influence the input are called taps.
Q: What is the evaluation of Erlang in these 4 criteria: readability, writability, reliability, and cos...
A: Ans: Evaluation of Erlang in these 4 criteria: readability, writability, reliability, and cost are b...
Q: What are the implications of a distributed cloud for "Systems Analysis and Design"
A: What is distributed cloud? A distributed cloud is an architecture where multiple clouds are used to ...
Q: F H J M R S V 1 3 4 5 7 8. 9 10 11 12 low, middle, and high indices for each pass when using binary ...
A: Pass 1 Low : 0 Mid : 0+13/2 =6 High: 13 ----------------------------------- Pass 2 Low : 7 Mid : 7...
Q: at are the relevent details of a trap? Users with special logins that have administrator privilege a...
A: Correct answer is option (C)
Q: What is Activity Circle Diagram (ACD)? What are the dead and active states? What are the Event Sched...
A: What is Activity Circle Diagram (ACD)? What are the Event Scheduling? Algorithm steps of Event Sche...
Q: Which one of the following attributes are used to expand the width of a widget to the width of the p...
A: Let us see the answer below,
Q: Using C program. Create an array named NUMBERS with 10 cells. You are to initialize all of the cells...
A: PROGRAM INTRODUCTION: Include the required header files. Declare the array to store ten values. Use...
Q: Which XXX should replace the missing statement in the following BSTReplaceChild algorithm? ESTReplac...
A: The question is to fill the missing statement in BSTReplaceChild algorithm.
Q: Write a java program to reverse a user entered array in groups. Take the size of group from the user...
A: Hi Dear!! Please Upvote!! Your positive feedback will be more valuable!! ---------------------------...
Q: As the CISO, you're in charge of developing an information security programme that's backed up by a ...
A: Introduction: Program of security measures: Unified threat management (UTM) refers to the process of...
Q: Look for an example of a cost overrun in an information systems development project by browsing the ...
A: He supplied information on an example of an information systems development project with cost overru...
Q: What are the different models for software requirements, and their advantages and disadvantages in r...
A: Advantages and disadvantages of different software models Thesoftware model is an abstract represent...
Q: 1. Write a console application that uses at least five (5) different methods of Math class. Provide ...
A: Find the required code in Java given as below and output:
Q: Critically analyze the various search tools available and how they are used to perform basic searche...
A: There are many tools are available for business search like and they are very much helpful in this ...
Q: 5. Define a A-term called or such that or is a binary logical or function for Church booleans. Also,...
A: The creator of the lambda calculus, realised this and consequently set about to make a series of enc...
Q: What do you think the boundaries of an organization's information security are? When security rules ...
A: Introduction: Organizations may use information security to secure both digital and analog data (Inf...
Q: Given a string, write a method that returns the number of occurrences of substrings "baba" or "mama"...
A: Since no programming language is mentioned, I am using python. Algorithm: Start Implement a method ...
Q: Which of the following encoding systems can handle both traditional and simplified Chinese writing s...
A: The encoding system that can handle both traditional and simplified Chinese writing systems is Unico...
Q: Consider the following multithreaded algorithm for performing pairwise multiplication on n-element a...
A: Algorithm: SUM-ARRAYS'(A, B, C) n = A. Length grain-size = ? // to be determined r = ...
Q: Create a read function and a print function
A: Question is to implement two functions read and print. It is given in next step.
Q: Use the following expression to create an expression tree: 6 - 5 * 4 + 3 / 2 + 1 - 0
A: Given: We Have to create a Expression Tree in the Following Expression: 6 - 5 * 4 + 3 / 2 + 1 - 0...
Q: Why CyberSecurity is Important? Explain
A: Cybersecurity is very important because it protect your all sensitive data from threats and damage. ...
Q: What is the ArrayList list's starting size?
A: Actually, ArrayList list = new ArrayList();
Q: What are the main advantages of virtual memory? And Describe three advantages of virtual memory and ...
A: Virtual memory is a memory space in the operating system which is acts as a main memory to the secon...
Q: One of the disadvantages of the Bus topology that you should mention is the difficulty in reconnecti...
A: Introduction One of the disadvantages of the Bus topology that you should mention is the difficulty ...
Q: Suppose that a manufacturing company builds n different types of robots, say robots 1, 2, . . . , n....
A: We call this a canvassing because it is not a representative, randomized survey. Its finding emerge ...
Q: Prove the statement above. (Big-theta notation).
A: Not at all like Big-O notations, which addresses just upper bound of the running time for some algor...
Q: What is the significance of the von Neumann bottleneck?
A: Introduction the question is about the significance of the von Neumann bottleneck and here is the s...
Q: Write a program C++ to read a sequence of integers (n), then print the number of the positive and ne...
A: For this program, we will be performing the following actions: Asking user how many numbers he woul...
Q: Building and using DNA Motifs Background Sequence motifs are short, recurring (meaning conserved) pa...
A: Apart from the conventional strings which start and end with a single quote in python. There is also...
Q: +b is O(x²)
A: 1) f(x) = ax+b is O(x2) 2) explain a condition where the code isn't O(x). also prove witness and gra...
Q: Refresh your C++ skill Using function with 2D array 1. Create a global variable 2 dimensional array ...
A: Step-1: StartStep-2: Declare a global variable of 2-D array of size [3][5]Step-3: Call function init...
Q: The determination to make a context switch is based on which of the follow O illegal operation O reb...
A: The determination to make a context switch is based on which of the following? (Select all that appl...
Q: Why is it that on today's Internet, audio and video traffic is frequently carried through TCP rather...
A: Introduction: UDP and TCP: The UDP is an abbreviation for "User Datagram Protocol," It is a protocol...
Q: Man-in-the-middle (MITM) attacks can be averted in several ways. Give a step-by-step respons
A: Actually, given question regarding Man-in-the-middle (MITM).
Q: Name the virtual machine that is used Android O a. Dalvik Virtual Machine
A: Name the virtual machine that is used inAndroidO a. Dalvik Virtual Machine O b. javacO c. dex compil...
Q: For this question you will be using a doubly linked list containing Strings and Node class which con...
A: I have answer this question in step 2.
Q: What does it mean to have "knowledge"? and how is "knowledge" represented in the realm of computers?...
A: What does it mean to have "knowledge "? and how is "knowledge" represented in the realm of computers...
Q: Which one of the following is the built-in database in android? O a. Java O b. MS Access O c. SQL O ...
A: I have answered all the 3 parts. First we will see which one is the built-in database in android.The...
Q: Give and answer a "how would you solve this problem?" (specific scenario related to the job offering...
A: If the question being asked in the interview stating that how would you solve hardware problem, then...
Q: Draw an ER Diagram for the following Business Situation: A bank has a phone call system in which th...
A: ER Diagram is shown below!!
Q: Write a C program to: Ask the user to enter 2 float numbers. Use increment operator to modify the f...
A: Black screen is nothing but a console and to print printf function is used ++ is increment operator ...
Q: Python :Using the Positional List, write a code that asks the user to enter the words, insert the wo...
A: import bisect print("Enter words for the list, \"exit\" to quit")lst = []while True: x = input()...
Q: The operation F(X, Y, Z) = (!X + !Y + !Z) can be implemented with a single input signals and one out...
A: Here in this question we have given a some boolean expression and we have asked to implement with si...
Q: Computer Science using this data data <- data.frame(no = seq(1,1000), offers = c(rep(0, 550), r...
A:
Q: Write code that outputs variable numBirds as follows. End with a newline. Ex: If the input is: 3 the...
A: The required Java program is in the next step with explanation given in code comments.
Q: PLEASE DRAW THE DIAGRAM ACCORDING TO THE QUESTION: 4. Company TeaLeaves has recently adopted a new o...
A: Let's see the solution in the next steps
Q: How using Well-connect could help you be successful as a student in personal health and wellness.
A: Solution: The Well-Connect program is offer the several subjects on the personal health and the well...
Q: What exactly is a MAN? What is the distinction between MAN and WAN?
A: Introduction: A metropolitan area network (MAN) is a computer network that links computers within a ...
explain
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Show that EPM is a special case of RPM2? Determining the number of all solutions, however, is an NP-hard problem.please give me the full answer of applying the Booth Algorithm on the following equation :(-6) x (-2) please explain and provide ca) Define the following and show the relationship among them:(i) Polynomial time problems(ii) NP Hard Problems(iii)NP-Completeness.b) Why Dijkastra’s Algorithm does not work with negative weight edges.
- Part(a): Explain Race Condition with example. Part(b): What are the conditions that need to hold to solve critical section problem? Explain. Part(c): What is the problem with the following algorithm?Use the Quine McCluskey algorithm to simplify the function:F(w, x, y, z) = Σ(2, 6, 9, 10, 11, 13, 14, 15)Show all work – no credit will be given for an answer without accompanying workTheory of Computation Prove that XY is undecidable XY = { ⟨M⟩ ∣ M is a TM where x∈L(M) and y∈L(M) } Prove this by reducing it from ATM which is proven to be undecidable
- we know that the DFA is equivalent with NFA and regular expression (RE). For the problem to determine whether a given DFA and RE are the same, C = {<D, R> | D is a DFA and R is a RE that L(D) = L (R)}, please prove that C is decidable.Write a Hilbert proof for the following theorem schema ⊢((p→q)∨(p∧(¬q)))A. 3-SAT to Hamiltonian CycleReduce 3-CNF Satisfiability problem to an instance of Hamiltonian Cycle problem in polynomial time.Note: Variables in red color are negated.1. Given: Variables: X1, X2, X3 Clause: (X1 v ¬X2 v X3) Ʌ (¬X1 v ¬X2 v ¬X3)2. Given: Variables: X1, X2, X3 Clause: (X1 ∨ X2 ∨ X3) ∧ (¬X1 ∨ ¬X2 ∨ ¬X3) ∧ (¬X1 ∨ X2 ∨ ¬X3)
- Algorithm for Computation of A∗ starting from A by the generalized “escalator” method (case where G(A) has no 0-absorbing circuit).In each case below, show using the pumping lemma that the givenlanguage is not a CFL.e. L = {x ∈ {a, b, c}∗ | na(x) = max {nb(x), nc(x)}}Prove the following theorem. If A * B * C, D * E * F, AB ≅ DE, and BC ≅ EF, then AC ≅ DF.

