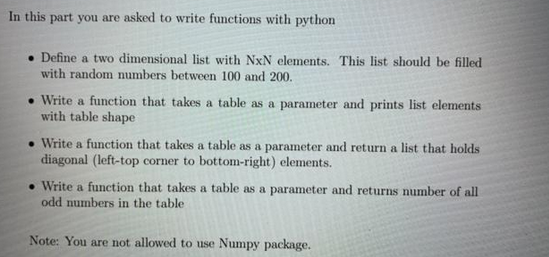
In this part you are asked to write functions with python • Define a two dimensional list with NxN elements. This list should be filled with random numbers between 100 and 200. .Write a function that takes a table as a parameter and prints list elements with table shape .Write a function that takes a table as a parameter and return a list that holds diagonal (left-top corner to bottom-right) elements. • Write a function that takes a table as a parameter and returns number of all odd numbers in the table Note: You are not allowed to use Numpy package.
Q: What software category do compilers and editors belong under?
A: System software is required to manage computer resources and facilitate application program…
Q: What is Unpacked BCD Format?
A: The answer is given below step.
Q: During the design of the crete framework for binary-level concolic testing, what are design goals…
A: During the design of the crete framework for binary-level concolic testing, we have identified the…
Q: What are the benefits of automating server deployment and configuration? Consider the drawbacks of…
A: Given - What benefits can automated server provisioning and configuration offer? What negative…
Q: X. Consider the following C functions and assembly code Assume that int is 32 bits, short is 16…
A: Here we have given the correct option with suitable code. You can find the solution in step 2.
Q: What benefit does Linux partitioning provide an operating system?
A: The answer of the question is given below
Q: What are the benefits of providing and configuring servers automatically? Which of the following are…
A: given - What benefits do servers that are provisioned and configured automatically offer? What…
Q: Exists a substantial drawback to a two-tier architecture? How can a client–server design with many…
A: Two-tiered client-server architecture: The Client-Server concept is the basis for the two-tier…
Q: How knowledgeable are you about computer networking? List the many types of computer networks
A: Computer networking refers to interconnected computing devices that can exchange data and share…
Q: How is service-oriented architecture (SOA) deployed?
A: Introduction: The service-oriented design used in software development is the root of the issue.
Q: Describe some methods for seizing control of a session. What preventative actions might you employ?
A: Explanation: Depending on their location and vector, attackers have many ways for hijacking a user's…
Q: What connects all Agile frameworks? Following that, click Submit. A set number of cycles…
A: Given: Work may be planned, managed, and carried out according to a certain methodology known as an…
Q: How far has technology advanced over the last many decades, and what kind of technological systems…
A: Introduction Technology Advancement is a process that evolves constantly over the course of time.
Q: Is 2n = O(3n)? I need solution on why or why not.
A: Answer: The exponentials with different bases are not of the same order.
Q: This is partially due to the tremendous powers of contemporary computers. Exists proof from the past…
A: Introduction: The value of computers in our educational system must be emphasised, as well as their…
Q: What does it mean in the context of programming to "resist the impulse to code"?
A: Introduction: Software engineers should understand the problem, develop a solution, and then code.…
Q: Define XLAT instruction used in 8086.
A: XLAT instruction is Used to translate a byte of AL register using It Locates the byte entry in a…
Q: 3-2 Relative asymptotic growths Indicate, for each pair of expressions (A, B) in the table below,…
A: Please refer to the below table for the solution A B O 0 Ω ω Θ a) lgk n nε Yes Yes No No…
Q: Machine Language is a straightforward notion that may be expressed in a few words. In addition, why…
A: To Be Done: Describe machine language. Answer: Computer Language: Machine language is a collection…
Q: What is the difference between a Domain and a Workgroup?
A: Domain Computers in a domain have a centralized database. The domain is primarily used to transfer…
Q: What are the pros and downsides of global connection in cloud computing?
A: Pros of cloud: cost reduction: It helps in providing more profit for less money. so when it comes…
Q: xist examples of virtual servers being used in a classroom settin
A: Answer is in next step
Q: What are the prerequisites for computer science study?
A: The academic field of computer science focuses on understanding computers and other computational…
Q: What principles did computer pioneer Ada Lovelace develop?
A: The first computer programmer is thought to have been English mathematician Augusta Ada King,…
Q: How knowledgeable are you about computer networking? List the many types of computer networks
A: Computer networking refers to the interconnected devices of a computer that will exchange…
Q: Provide a short explanation of each kernel component before listing the components.
A: NOTE :- Below i explain the answer in my own words by which you understand it well. The Kernel…
Q: Is the transfer from on-premise servers to an IaaS architecture accompanied by any governance…
A: Given: Is migrating from on-premise servers to IaaS architecture governed Charity management employs…
Q: How does MVC fit into the broader web application framework? What are the advantages of an MVC…
A: MVC is made up of three components: model, view, and controller. The Model component of the MVC, as…
Q: How to get rid of global variables gl_args and gl_hashType, while preserving all the functionality…
A: Python which refers to the high-level, general purpose programming language. Its design which…
Q: Describe briefly the three primary phases involved in physical design. Database recovery management…
A: Physical design is the process of determining the data storage organization and access…
Q: Compare and contrast secondary solid-state storage technologies with secondary magnetic storage…
A: Solid-State Storage : Data storage that uses integrated circuit devices rather than moving magnetic…
Q: The many sorts of programming languages are as follows: Describe each of them briefly.
A: The history of programming languages actually dates back further than you might think. Early…
Q: RAM and Register refer to two different types of memory.
A: RAM Stands For Random Access Memory.
Q: What functions do compilers provide in computer scienc
A: compiler, computer software that translates (compiles) source code written in a high-level language…
Q: Rerouting malicious traffic across VLANs is one way to get access to a network. Recognize the…
A: A virtual local area network (VLAN) shares the physical network while simultaneously establishing…
Q: What are the prerequisites for computer science study?
A: Computer science is the academic discipline that focuses on studying computers and other…
Q: How does the Dogpile Effect operate and what is it? Can you do anything to prevent this from…
A: Introduction: The dogpile effect occurs when a cache is allowed to get stale, which causes several…
Q: Exist classroom or educational institution deployments of virtual servers?
A: Introduction: A dedicated physical server's capabilities are a recreated by a virtual server.…
Q: Which port is utilized to provide electricity to the Raspberry Pi? Is it an HDMI port, a Macro USB…
A: Answer:-
Q: What are the four fundamental capabilities of a computer system? employ an example to illustrate
A: A computer is an electrical digital machine that can do any mathematical and logical activity…
Q: A. What bit pattern does mask have, as a function of x? B. What numerical value does mask have, as a…
A: Note: As per our company guidelines we are supposed to answer only 3 sub-parts. Kindly repost other…
Q: computer Which principles did Ada Lovelace expressly develop?
A: Introduction: Ada Byron was the sole biological child of mathematician Lady Byron and poet Lord…
Q: Define Inter segment Indirect addressing mode
A: let us see the answer:- Introduction:- This type of addressing involves including the address of the…
Q: tems to the cloud, where should you check for governance c
A: What are some of the management issues to be aware of when moving from on-premises servers to an…
Q: Is there a connected planar graph with an odd number of faces where every vertex has degree 6? Prove…
A: A connected planar graph with an odd number of faces where every vertex has degree 6 is:
Q: How exactly does virtualization function within the context of cloud computing?
A: What is Virtualization ? The process of producing a virtual copy of anything rather than a real…
Q: Which are the most significant drawbacks of a two-tier system? What about a client–server design…
A: Introduction Client Tier and Database are the two layers that make up a two-tier architecture (Data…
Q: What language is used to create PHP websites?
A: Definition: Hypertext Preprocessor is referred to as PHP. It is a server side scripting language…
Q: Is the internet a useful resource for those with physical or mental disabilities? What new…
A: Inspection: The internet is helpful for those who are blind. They have access to the following…
Q: How do network architecture and application architecture differ?
A: The phrase "network architecture" refers to the process of communication being segmented into…
Step by step
Solved in 4 steps with 3 images

- Write a function MedianWithoutHL(ScoreList) that takes an unsorted list of n numbers as a parameter, discards the highest and the lowest numbers and return the median. You can assume the number of items in the list is between 0.0 and 9.9. To find the median from a list of items, you have tosort the list and find out the value of the item in the middle.Note: If the list has an odd number of items, the median is the value of the middle item. If the list has an even number of items, the median is the average of the two middle items.Sample Run #1:scoreList1 = [9.0, 9.0, 7.5, 8.0, 9.5, 6.5, 5.0, 7.0, 7.5, 8.5]print("The Original ScoreList: ", scoreList1)print(MedianWithoutHL(scoreList1))Output of Sample Run #1:The Original ScoreList: [9.0, 9.0, 7.5, 8.0, 9.5, 6.5, 5.0, 7.0, 7.5, 8.5]The List after sorting: [5.0, 6.5, 7.0, 7.5, 7.5, 8.0, 8.5, 9.0, 9.0, 9.5]Without the High & Low: [6.5, 7.0, 7.5, 7.5, 8.0, 8.5, 9.0, 9.0]7.75Write in C++ Now, what if Sam wants to insert Eevee after Pikachu but he doesn't know where Pikachu is located in his list. Let's help him search for a Pokemon by its name and insert another Pokemon directly after it. Write a function secondPlace() that takes six parameters and inserts a new Pokemon into a list right after another specified pokemon. Once you find the specified Pokemon, use the insertAfter() function from the previous sub-question to add the new Pokemon. The function should return the new number of strings in the array. Note The same Pokemon may appear in the list multiple times (Sam has a bad memory). Assume that Sam wants every instance of the Pokemon he is searching for to be followed by the Pokemon he is attempting to insert. If the array is already full or if the number of strings that are going to be added to the array plus the current number of strings exceeds the total size of the array, the array should remain unchanged. Assume all inputs are lowercase…Given a list called L. I am to write a function in python that will return two lists, one list with all the elements that are even, and the other list with all the elements that are odd. L = [1,2,3,4,5,6,7,8,9,0]
- this code should be in python: write a function that receives a list as its only parameter. Inside the function remove all the duplicate items from the list and returns a new list. For Example: If we call the function with [“dad”, “aunt”, “mom”, “sister”, “mom”] as its input, the returned value should be [“dad”, “aunt”, “mom”, “sister”]. The order of the items inside the returned list does not matter.In python, create a function wherein you transfer elements from a list into different lists. If a certain element has been encountered, continue the listing in a new list. Continue doing so until this certain element has been encountered two times. Disregard the succeeding elements after the second certain element. Once you have your 2 lists, return them both as a tuple. Example: element_stop = ‘a’ original_list = [‘b’, ‘c’, ‘d’, ‘d’, ‘f’, ‘a’, ‘e’, ‘t’, ‘d’, ‘g’, ‘f’, ‘t’, ‘a’, ‘b’, ‘e’] The output should be: ([‘b’, ‘c’, ‘d’, ‘d’, ‘f’], [‘e’, ‘t’, ‘d’, ‘g’, ‘f’, ‘t’])Write a function that gets a linked list of ints, and reverses it. For example - on input 1 -> 2 -> 3 -> 4, after the function finishes the execution, the list becomes 4 -> 3 -> 2 -> 1 - If the list has one element, then it doesn’t change - If the list is empty, then it doesn’t change You may use the data fields in the struct and the functions provided in LL.h and LL.c. // reverses a linked list void LL_reverse(LL_t* list); Test for the Function: void test_q3() { LL_t* lst = LLcreate(); LL_add_to_tail(lst, 1); LL_add_to_tail(lst, 3); LL_add_to_tail(lst, 8); LL_add_to_tail(lst, 4); LL_add_to_tail(lst, 3); LL_reverse(lst); intcorrect[] = {3,4,8,3,1}; inti; node_t* n = lst->head; for(i=0;i<5;i++) { if (n==NULL) { printf("Q3 ERROR: node %d==NULL unexpected\n", i); return; } if (n->data != correct[i]) { printf("Q3 ERROR: node%d->data==%d, expected %d\n", i, n->data, correct[i]); return; } n = n->next; } if (n==NULL) printf("Q3 ok\n"); } Support…
- Write a function that gets a linked list of ints, and reverses it. For example - on input 1 -> 2 -> 3 -> 4, after the function finishes the execution, the list becomes 4 -> 3 -> 2 -> 1 - If the list has one element, then it doesn’t change - If the list is empty, then it doesn’t change You may use the data fields in the struct and the functions provided in LL.h and LL.c. // reverses a linked list void LL_reverse(LL_t* list); Test for the Function; void test_q3() { LL_t* lst = LLcreate(); LL_add_to_tail(lst, 1); LL_add_to_tail(lst, 3); LL_add_to_tail(lst, 8); LL_add_to_tail(lst, 4); LL_add_to_tail(lst, 3); LL_reverse(lst); intcorrect[] = {3,4,8,3,1}; inti; node_t* n = lst->head; for(i=0;i<5;i++) { if (n==NULL) { printf("Q3 ERROR: node %d==NULL unexpected\n", i); return; } if (n->data != correct[i]) { printf("Q3 ERROR: node%d->data==%d, expected %d\n", i, n->data, correct[i]); return; } n = n->next; } if (n==NULL) printf("Q3 ok\n"); } Support File…1.Given the argument passed to the function is a list containing integer values, what does the function return def mystery1(someListOfValues: list):total = 0for value in someListOfValues:total += valuereturn total/len(someListOfValues) 2. The function below is to find the largest value in a list passed by parameter. Does it work as intened (yes or no)? If not give an example of an argument it would not work for. def maxValue(someListOfValues:list):"""returns the largest value the list passed by parameter"""value = 0for num in someListOfValues:if num > value:value = numreturn value 3.Write a function called loadNames() that will open a file called names.txt and build a list of its contents and return it. Function Call: names = loadNames()print(names) Sample ouput: ['Nolan Rafaj\n', 'Brandon Brzuszkiewicz\n', 'Amanda Vozari\n', 'Chase Harper\n', 'Bryce Conner']Please answer it in Python Write a function min_odd that takes a list as an argument and returns the smallest even integer contained in the list. If the list contains no even integers, the function will return None. For Example : min_odd([45, 62, 19, 22, 26, 18, 3, 5, 14])Expected answer is 14 min_odd([])Expected answer is None Write a function index_of that takes as an argument an integer (supposedly even) and a list, and returns the index to which this integer appears in the list. If the integer does not appear, the function will return None. It is assumed here for simplicity that the integer searched for does not appear several times in the list. Hint: if the for e in list loop doesn't suit you, remember that you can make a for + range or a while. .. For Example: index_of(34, [3, 67, 62, 34, 19, 24])Expected answer is 3 index_of(16, [2, 6, 104, 5, 25, 18, 50, 16])Expected answer is 7
- Please answer it in Python Write a function insere_milieu that takes as an argument a list l and an element elem and returns the list obtained from l by adding elem "in the middle" of l, that is: If the length of l is even, the item is added once, in the middle of the list. If the length of l is odd: the element is added on either side of the central element. Example: insere_milieu([4, 7, 12, 3], 0) is [4, 7, 0, 12,3] insere_milieu([9, 3, 5, 6, 2], 1) is [9, 3, 1, 5, 1, 6, 2].4. Modify the bracketsBalance function so that the caller can supply the brackets to match as arguments to this function. The second argument should be a list of beginning brackets, and the third argument should be a list of ending brackets. The pairs of brackets at each position in the two lists should match; that is, position 0 in the two lists might have [ and], respectively. You should be able to modify the code for the function so that it does not reference literal bracket symbols, but just uses the list arguments. (Hint: The method index returns the position of an item in a list.) the bracketsBalance function: def bracketsBalance(exp):"""exp is a string that represents the expression""" stk = LinkedStack() for ch in exp: if ch in [’[’, ’(’]: stk.push(ch) elif ch in [’]’, ’)’]: if stk.isEmpty(): # Create a new stack # Scan across the expression # Push an opening bracket # Process a closing bracket# Not balanced return FalsechFromStack = stk.pop()# Brackets must be of…You are given the pointer to the head node of a linked list and an integer to add to the list. Create a new node with the given integer. Insert this node at the tail of the linked list and return the head node of the linked list formed after inserting this new node. The given head pointer may be null, meaning that the initial list is empty. Function Description Complete the insertNodeAtTail function in the editor below. insertNodeAtTail has the following parameters: SinglyLinkedListNode pointer head: a reference to the head of a list int data: the data value for the node to insert Returns SinglyLinkedListNode pointer: reference to the head of the modified linked list Input Format The first line contains an integer , the number of elements in the linked list.The next lines contain an integer each, the value that needs to be inserted at tail. Constraints Sample Input STDIN Function ----- -------- 5 size of linked list n = 5 141 linked list data values…

