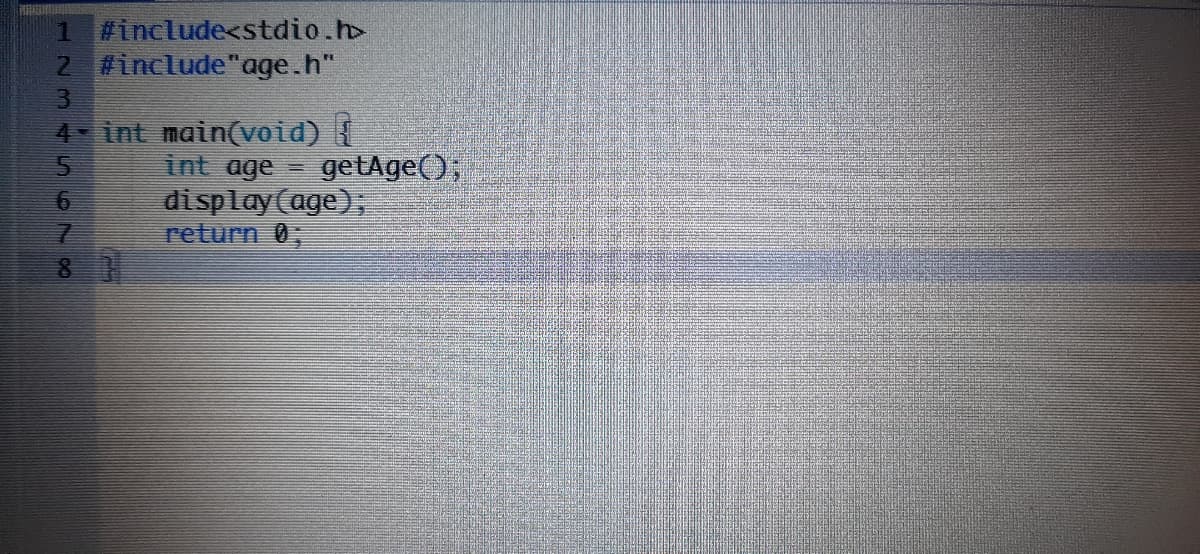
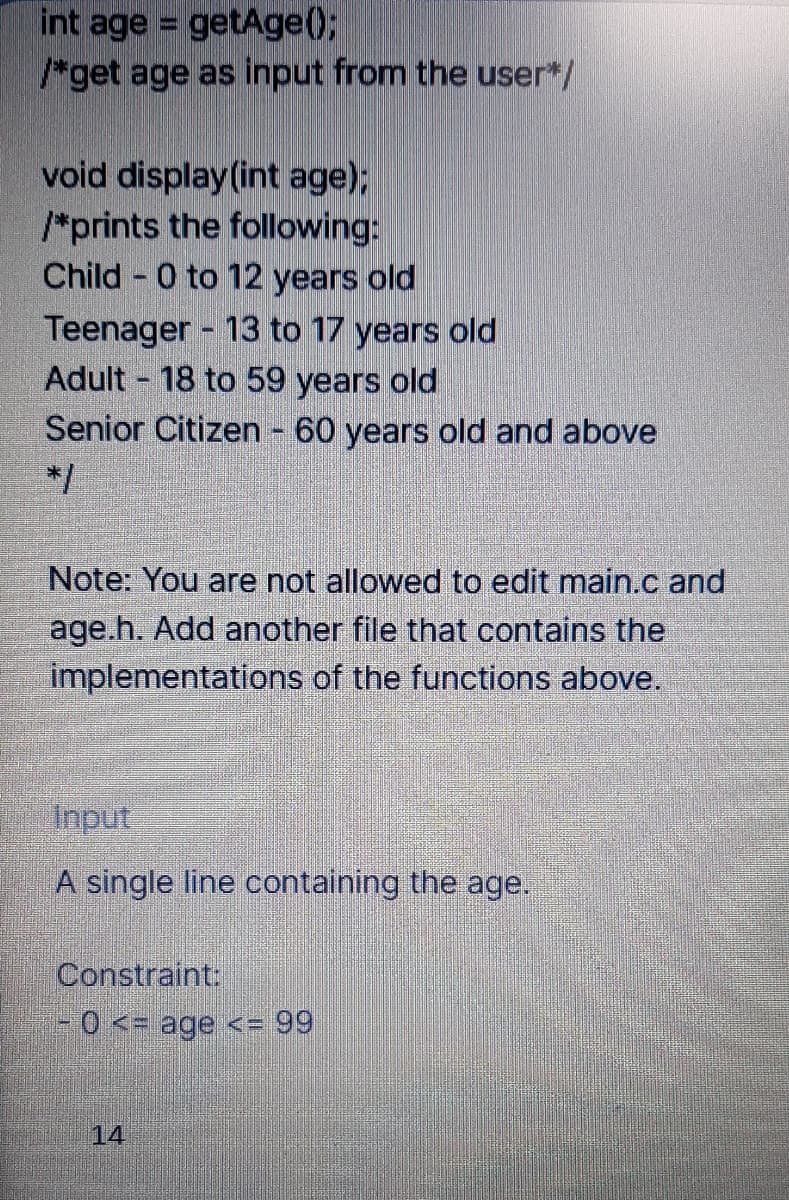
int age = getAge(); /*get age as input from the user*/ void display (int age); /*prints the following: Child 0 to 12 years old Teenager 13 to 17 years old Adult 18 to 59 years old Senior Citizen 60 years old and above %3D */
Q: When is it more advantageous for a user to utilize a time-sharing system rathe than a PC or single-u...
A: Introduction: It is a high-performance computer system that is primarily intended for a single user ...
Q: How can a smart phone's video capability be utilized to collect data?
A: The data captured or recorded using smartphones can be transferred or shared by MMS, Bluetooth, USSD...
Q: LWC Assignment: Create a LWC component to display the output. When we click on the checkbox it will ...
A: Lightning Web Components uses core Web Components standards and provides only what’s necessary to pe...
Q: Who is accountable for computer user training in an organization? What role does the DBA play during...
A: Answer: Data set administrator(DBA)is an individual controlling and planning the data set administra...
Q: Other than SSL or TLS, which protocol is used to secure communication between a web browser and a we...
A: The answer to the following question
Q: MicroStrategy employs Intelligent Cube Technology in what ways?
A: INTRODUCTION: Cube Technology is a provider of comprehensive information technology solutions. We su...
Q: HTML, CSS, JavaScript Integration This assignment involves integrating HTML, CSS and JavaScript. The...
A: Below is the implementation of program using js,css and html. NOTE: Whenever a button is clicked, th...
Q: What is the distinction between a subsystem and a logical subdivision, and why does it matter?
A: Subsystem Work is processed on the system in the subsystems. A subsystem is a single, predetermined...
Q: 6.30 LAB: Flip a coin Write a program that simulates flipping a coin to make decisions. The input is...
A: NOTE - This is a Java question, so I have written the code in the Java programming language. Here I ...
Q: Why is it necessary to utilize APIS rather than system calls?
A: Introduction: There are four leading causes for this:
Q: Computer Science Objective: To create a JSON for Population census with objects and arrays Scenar...
A: The generic structure of a JSON object is: { a:a1, b:[b1,b2,b3], c:{ c1:c11, c2:[c...
Q: 1- A) What kind of books -------ike reading? B) Horror stories and science fiction. 2- A) What --the...
A: 1A) What kind of books do you like reading? 2A)What is the teacher doing?
Q: Distinguish the three layers of data modeling.
A: Distinguish the three layers of data modeling.
Q: Before sending it to the lecturer for review, I'd like to submit a PowerPoint presentation for doubl...
A: Introduction: Despite the fact that the American Psychological Association's guide does not include ...
Q: Using the Pigeonhole Principle, determine how many cards you’d have to pull from a deck in order to ...
A: Below im explaining the it:
Q: How far have robots come, and how intelligent do you believe they will become in the future?
A: Introduction: Some experts believe that by 2045, robots will outsmart humans. Others believe it will...
Q: What's the difference between uncertainty and risk?
A: In step 2, I have provided difference between uncertainty and risk----
Q: Each software application is based on a distinct architectural basis. Describe the different archite...
A: There are five different architectural style are available
Q: Identify all of the following graphs that are traversable given that each graph only has 5 vertices ...
A: Option C:- A,D
Q: What are some of the drawbacks of utilizing public WiFi?
A: Secure is public Wi-Fi: The typical public Wi-Fi connection isn't safe. Just because you have to log...
Q: The amount of information accessible at the moment is vast and varied. Forms are discussed in relati...
A: Introduction: The term "data transfer" refers to any information moved from one place to another by ...
Q: What Linux is used for and how it works on mobile phones
A: Introduction: Everyone's attention is now focused on Android, which has become one of the most popul...
Q: What is the difference between a homogeneous and heterogeneous relational database management system...
A: What is Relational Database: A relational database is a digital database based on E. F. Codd's relat...
Q: What does having an embedded computer of the future entail?
A:
Q: What are the advantages of MATLAB over other programming languages for solving Computational Geometr...
A: INTRODUCTION: MATLAB MATLAB is a programming platform created specifically for engineers, trainees, ...
Q: The concept of Mutual Exclusion (ME) is described in length as a fundamental mechanism for the smoot...
A: Just a single process can execute its basic segments whenever. No different process can be executed ...
Q: What happens when an array is sorted using a selection sort
A: Introduction: The smallest element in an unsorted array is brought to the front of the selection sor...
Q: Q9) Write about IA-32 Architecture microprocessors. Explain about IA-32 Registers.
A: IA-32 is the 32-bit version of the x86 instruction set architecture, designed by Intel.
Q: If a programmer or systems analyst has less than two years of experience or has a grade of average o...
A: Introduction: A systems analyst is a person who utilizes information technology to address business ...
Q: Q5/ A- Write the equation for the following abbreviation with diagram and truth table? X=(A OB)(COD)
A: Introduction
Q: 4 A combinational circuit is defined by the following three Boolean functions: F1(x,y,z)=x'y'z'+xz F...
A:
Q: Write a function in C language that takes student number as a value and adds the numbers in each dig...
A: The answer to the following question:-
Q: Which sorting method is said to be the fastest? Why?
A: A sorting algorithm is an algorithm that puts elements of a list into an order. The most frequently ...
Q: What are the four types of records used in SSL protocols? What are their implications?
A: Four different types of records in SSL protocols: SSL record protocol Handshake protocol Change-cip...
Q: Refer to the WORKERS table: WORKERS Empno Empname Job Mgr HireDate Sal Comm Deptno 24000 2.405 17000...
A: Given :
Q: What is the shortest possible size for a genuine ethernet frame?
A: Introduction: The sum of the Ethernet header (14 bytes), the payload (IP packet, generally 1,500 byt...
Q: A _______ LAN allows several LANs to be connected. a. backbone b. wireless c. wired Computer ne...
A: Introduction: A _______ LAN allows several LANs to be connected. a. backbone b. wireless c. wired C...
Q: When is it more advantageous for a user to utilize a time-sharing system rather than a PC or single-...
A: We need to explain when is it more advantageous for a user to utilise a time-sharing system rather t...
Q: When is it more advantageous for a user to utilize a time-sharing system rathe than a PC or single-u...
A: Introduction: A time shared operating system makes use of CPU scheduling and multi-programming to gi...
Q: Cache memory is a modest but critical component of modern computers. Justify the existence of cache ...
A: Introduction: Cache memory stores frequently used instructions/data that the CPU may demand next, an...
Q: Define and explain what is Data Science?
A: Let's see what is data science
Q: The phases of the computer machine's life cycle should be described and illustrated with examples.
A: The life cycle of a computer is similar to the life cycle of any machine, except that a computer has...
Q: Identify and describe the four distinct kinds of data warehouse schemas (Star, Snowflake, Galaxy, an...
A: Schema is a logical description of the database as a whole, Every kind of record, as well as the acc...
Q: How many possible colors do we have for each pixel if we utilize direct RGB value coding with ten bi...
A: Let's see the solution below
Q: Explain wireless networking in terms of standards, topologies, and trends.
A: Wireless networking: Wireless local network is an unassumingly efficient to acquaint and is proper w...
Q: What is the distinction between a subsystem and a logical subdivision, and why does it matter?
A: Subsystem: The subsystem of computer science is a branch of computer science that pertains to the ...
Q: Where is the object's supertype stored?
A: Introduction: A super type is a type of generic object that is related to one or more subtypes. A su...
Q: Is there a restriction on the use of MST for TSP? How is the temporal complexity of MST calculated?
A: Tree with the Fewest Nodes: A subgraph with minimal weight edges links all vertices in a connected, ...
Q: Is there a connection between an individual's educational process and his or her physical and cultur...
A: Introduction: When attempting to understand human nature and ability, sociocultural, evolutionary, a...
Q: Distinguish the three layers of data modeling.
A: - They three steps of data modelling must be highlighted. - The distinctions: - Data modelling is d...
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 2 images

- 13. Write function quote() that takes as input the name of a file (as a string) and anindex i (as an integer). The file will contain quotes, one per line. The function shouldopen the file, read the file, close the file, and return the i-th quote (i.e. the i-th line in thefile), assuming that the quote numbering starts at 0. Test your solution onfile Wilde_Quotes.txt.>>> quote("Wilde_Quotes.txt", 5)'At twilight, nature is not without loveliness, thoughperhaps its chief use is to illustrate quotations from thepoets.\n'>>> quote("Wilde_Quotes.txt", 0)'A little sincerity is a dangerous thing, and a great dealof it is absolutely fatal.\n'>>> quote("Wilde_Quotes.txt", 23)'Patriotism is the virtue of the vicious. \n'>>>Write a function void saveByDept(char *fileName, char *deptName , student allStudents[], int size) that will save the information of all students who belong to the department with name pointed to by deptNameinto a text file. The name of the file is given as an input parameter, fileNamePlease answer it in Python Below are the first 4 lines of such a file whose number of lines is not known a priori: Bella 91.0 18.5 19.5 19.5 19.0 19.5 (91 is a dist note) Azhar 83.0 19.0 18.5 18.5 18.5 19.0 Clara 91.0 17.5 17.5 17.5 18.5 19.0 Dalton 92.5 17.0 18.5 18.5 17.5 18.0 Write a function import_result that takes as an argument the name of the file that contains the results file_name and reads it to make the list of results. Each item in this result list is a dictionary corresponding to a competitor. The keys to this dictionary are: • 'name' with the competitor's name associated • 'note_dist' with which is associated the score obtained by the competitor for the length of his jump. It is known from the question. • 'notes_style' to which is associated the list of 5 marks obtained by the competitor for the style of his jump. Thus, if the file passed as an argument consists only of the 4 lines given as an example previously, the function will return: [{'name': 'Bella',…
- (5) Write a function called copy_even_lines() that takes two strings (filenames) as input parameters and copies every other line from the first file into the second. That is, counting from 0, it copies the 0th line, the 2nd line, the 4th line, etc. from the first file to the second file. You may assume that both files exist. (6) Write a python program that asks the user for two filenames and calls your function copy_even_lines() from (5) using those two filenames. If one or more files do not exist, your program must handle the exception by repeating the prompts until valid filenames are entered.please code in pythonRead in and return a list of review dates. The function should ask the user to enter some review dates This should be entered in the format mm/dd/yyyy (same as that in the file) where dd is two-digit day, mm is two digit month and yyyy is a four digit year e.g. 01/22/2020 The function should return a list containing the specified review dates. :return: a list of review datesYou can take any review date as sample exampleYou are given a file consisting of students’ names in the following form: lastName, firstName, middleName. (Note that some students may not have middle names). Write a program that converts each name to the following form: firstName middleName lastName. Your program must read each student’s entire name in a variable and must consist of a function that takes input as a string, consists of student’s name, and returns the string consisting of the altered name. Use the string function find to find the index of the function length to find the length of the string; and function substr to extract the firstName, middleName, and lastName. Test your program with a file consisting of the following names: Miller, Jason Brian Blair, Lisa Maria Gupta, Anil Kumar Arora, Sumit Sahil Saleh, Rhonda Beth
- Write a function count_character(filename, character) that takes in a filename and a character, both as strings, and returns the total number of times the given character occurs in the file. Examples: Contents of hello.txt:HelloHELLOHelloHELLO count_character('hello.txt', 'L') returns 4count_character('hello.txt', 'H') returns 4count_character('hello.txt', 'e') returns 2 Requirements: Please use Python Programming only Show screenshot of your work.struct employee{int ID;char name[30];int age;float salary;}; (A) Using the given structure, Help me with a C program that asks for ten employees’ name, ID, age and salary from the user. Then, it writes the data in a file named out.txt (B) For the same structure, read the contents of the file out.txt and print the name of the highest salaried employee and youngest employee names name in the outputscreen.Code done in C Write a piece of code in a function called password that creates a file with a random password (it can be a number). In another function called check_password, the function must ask the user to input the password to login and it should match the password in the file. If it doesn't, it should keep asking the user to keep inputting the right password. Finally, just by passing in the two functions into the main, that would be fine. Ex. int main() { ....password(....); ....check_password(....); }
- In Programming Exercise 13 (Chapter 8), you are asked to write a program to calculate students’ average test scores and their grades. Improve this programming exercise by adding a function to sort students’ names so that students’ data is output into ascending order according to their name. The code is below, is there a way to implement a sort function perhaps? Right now it just outputs as shown in the picture attached. #include <iostream> #include <fstream> #include <string> #include <iomanip> using namespace std; void getData(ifstream& inf, string n[], double tstData[][6], int count); void calculateAverage(double tstData[][6], int count); void calculateGrade(double tstData[][6], char gr[], int count); void print(string n[], double tstData[][6], char gr[], int count); int main() { string names[10]; double testData[10][6]; char grade[10]; ifstream inFile; inFile.open("data.txt"); if (!inFile) { cout…C++ is my answer correct ? Write a function to convert a given string : Answer: #include <iostream> #include <string> using namespace std; void toUpper(string &str) { for (int i = 0; i < str.length(); i++) { str[i] = toupper(str[i]); } } void toLower(string &str) { for (int i = 0; i < str.length(); i++) { str[i] = tolower(str[i]); } } int main() { string str = "khaled"; toUpper(str); cout << str << endl; str = "MOHAMMED"; toLower(str); cout << str << endl; return 0; } Write a function to calculate the sum of the even number from 1 - 100. Answer: #include <iostream> using namespace std; int sumEven() { int sum = 0; for (int i = 1; i <= 100; i++) { if (i % 2 == 0) { sum += i; } } return sum; } int main() { cout << sumEven() << endl; return 0; }You are given a file consisting of students’ names in the following form: lastName, firstName middleName. (Note that a student may not have a middle name.) Write a program that converts each name to the following form: firstName middleName lastName. Your program must read each student’s entire name in a variable and must consist of a function that takes as input a string, consists of a student’s name, and returns the string consisting of the altered name. Use the string function find to find the index of ,; the function length to find the length of the string; and the function substr to extract the firstName, middleName, and lastName.



