Is there a way if the previous code is plugged in the example below.
Q: 4. More asymptotic notation. For the following questions use the definitions of O, N, and e, not our…
A: - There are two equations we have to focus on. - We have to prove or disprove two of the equations.…
Q: In order to further assist your readers, it is suggested that you provide a more thorough…
A: Understanding the metrics used in the software development process is essential for measuring the…
Q: Solve these Pop and Push Push BX Where: B = 3691H SS = 1900H SP = 5C9DH Push BX Where: B = 1370H…
A: An assembly language is a programming language that communicates with the hardware of a computer…
Q: Write the function strend (s ,t ), which returns 1 if the string t occurs at the end of the string…
A: Here is a function called strend written in C that checks if the string t occurs at the end of the…
Q: Is having access to the internet beneficial or harmful?
A: The internet is a powerful tool that has revolutionized the way we communicate, work, learn, and…
Q: I was wondering, in your view, what features you'd want to see in the perfect programming language.
A: Here is your solution -
Q: What type of authentication method is displayed in this picture? Multi-Factor Authentication…
A: Multi-Factor Authentication is the correct answer. In the image sms code is being shown which is…
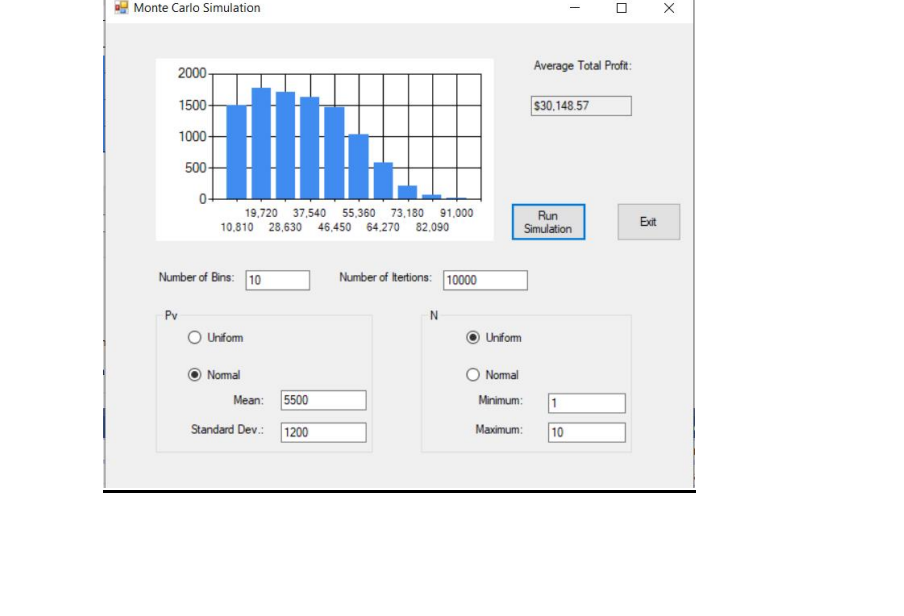
Q: Is the use of a computer really essential if one wishes to achieve realism in the outcomes of a…
A: Computers are essential for complex simulations because they provide the computing power and storage…
Q: and Wha
A: Introduction: Understanding addition, subtraction, multiplication and division. Know what is modulus…
Q: estion to Hi there straightforward checkbook balancer that would include a succession of stores…
A: The question is asking you to create a simple program that can balance a checkbook by tracking…
Q: What are the benefits of utilizing the Internet for healthcare over traditional methods? What…
A: Compared to conventional approaches, using the internet for medical purposes can provide a number of…
Q: Task 5: Complete the function validages that accepts a list of tuples containing (name, age), and…
A: We have to complete the given function validages that accepts a list of tuples containing (name,…
Q: During the analysis phase of software development, there are a wide variety of design models used.
A: The analysis phase of software development is the first stage in the software development life cycle…
Q: Linux is a piece of software that has its source code available to the public. Using just your own…
A: Open Source: Open source software is computer programs with their source code publicly available on…
Q: what does the abbreviated form of the interrupt service process
A: Interrupt Service Process (ISP) is a crucial component of the operating system that manages and…
Q: You need to have an understanding of the differences between parallel programming and serial…
A: Involves executing multiple operations simultaneously Divides a large task into smaller subtasks…
Q: PYTHON/ JUPYTER NOTEBOOKS a) Import the following reaction mechanism for acetaldehyde pyrolysis ,…
A: Introduction: In this question, we are asked to import and display a reaction mechanism for the…
Q: I'm curious as to what you think is the most effective language for programming.
A: There are several programming languages available for use in industry. What I should learn, though,…
Q: how to Generating random numbers using various density functions in R. write all of them with code
A: In statistics, probability density functions (PDFs) describe the likelihood of a random variable…
Q: 1.What sort of malware requires the user to pay to remove the malware? Adware Trojan horse…
A: Malware is defined as a program that is intentionally harmful to a computer network Examples: Worms,…
Q: A A E 0 B B True Bo Numeric 3 stop DE Amay 3 Bur False Which the following answers describes the…
A: While loop is used to execute a block of code repeatedly until a given condition is true. Syntax:…
Q: // prototype of DelOddCopEven of Assignment 5 Part 1 #endif // definition of DelOddCopEven of…
A: Linked List which refers to the one it is that each of its node contains a reference to the next…
Q: The SparseVector class should be extended to include a method sum() that accepts a SparseVector as…
A: The sum() method will take two SparseVectors as arguments and return a SparseVector that contains…
Q: Three simultaneous computer loop iterations bake a cake. Describe data-level and task-level…
A: Introduction: Cake-making is a complex process that involves multiple steps and variables, including…
Q: 1. Show the ListStackADT interface 2. Create a ListStackDataStrucClass with the following methods:…
A: Algorithm: Define a BaseNumber class to represent a number and its base. Define a ListStackADT…
Q: Even if a programmer knows a great deal about several different programming languages, the capacity…
A: Introduction: Each successive standard for the C programming language, ANSI C, ISO C, and Standard…
Q: In managing a database, what would you say are the three most important tasks?
A: Three primary responsibilities of database administrators: Storage: Information is stored when it is…
Q: In C++, what are linked lists about?
A: Dear Student, The detailed answer about linked list in C++ are given below -
Q: What do you think are the most fundamental concepts that CS majors should know?
A: Computer science studies computing and its theoretical and practical applications. Computer science…
Q: mple of when one of the four possible access ed. What distinguishes this option from other
A: Introduction: Only the owner and controller of access control controls will have access to this.This…
Q: Linux lets users share time and resources. Does this system protect well
A: LINUX is open source which means you can download it and use it for free. It is mostly used by…
Q: Even if a programmer knows a lot about a lot of different programming languages, it's still useful…
A: It's preferable to master language-independent programming ideas and then get familiarity with one…
Q: The Software Engineering Code of Ethics and Professional Practice (SE Code of Ethics and…
A: The question asks which of the Software Engineering Institute's eight principles is not followed.…
Q: Simply said, this is the bare bones of a piece of software. Just what is it, and could you explain…
A: The fundamental components of a piece of software are those that are necessary for it to run. These…
Q: Consider the matrix multiplication C = AB. A matrix W is called a witness matrix with the following…
A: Algorithm: Import the NumPy library. Define the Boolean matrices A and B with entries 0 and 1 using…
Q: What justifications are there for doing the authentication process? Study how the benefits and…
A: What is the purpose of the authentication procedure? Contrast and evaluate the benefits and…
Q: Please explain the most fundamental problems with software engineering. Explain?
A: Software engineering has made incredible progress in recent years, but several fundamental problems…
Q: How much log data can a log processing function access? The code below determines the average cache…
A: A log document is a record which keeps track of events that occur while the programme is running,…
Q: Whenever is the best moment to improve the network?
A: The best time to improve a network depends on a variety of factors, including the current…
Q: How may the many dangers to a reliable and secure online system be lessened?
A: A set of computers connected form a computer network. The use of a network allows computers to…
Q: How may an individual's use of the Internet help them fulfill their needs for medical care? What…
A: An Electronic Health Record is a computer-readable record of a person's health-related information.…
Q: The library functions strncpy, strncat, and strncmp, which only accept the first n characters of…
A: Please find the answer below :
Q: Which of the following is NOT a reason to be against using static routing? O. More resources, such…
A: Static routing is a type of routing protocol used in computer networks, where the routing table is…
Q: What two distinct categories of Internet-based services are available to users of mobile…
A: Two distinct categories of Internet-based services available to users of mobile applications are:
Q: 1.Which of the following is a security concern in cloud deployments? Authentication methods…
A: The answer of all 3 questions are given below with explanation
Q: Consider the matrix multiplication C = AB. A matrix W is called a witness matrix with the following…
A: Given data: Consider the matrix multiplication C = AB. A matrix W is called a witness matrix with…
Q: List four ways that white space can be added to an HTML webpage. Provide two that are HTML and two…
A: Here is your solution -
Q: In which of these circumstances is it advisable to use a POST request?
A: Dear Student, POST requests are used to send data to the server, which can then be used to update or…
Q: What do you consider to be the four most important factors while developing software? Please comment…
A: Given: Which four factors are the most important in software development? Please comment on the…
Q: How different are the concepts of computer architecture and organization from one another? Please…
A: Computers are electrical devices that do calculations and accept input and output. Indeed, there are…
Is there a way if the previous code is plugged in the example below.
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 2 images

- The language must be in python. Neural Network Units weights of [-1.2, -1.1, 3.3, -2.1] two training examples:Example 1: [0.9, 10.0, 3.1, 1]Example 2: [0.9, 2.1, 3.7, 1] Note that you don't have to explicitly include a threshold or bias since the examples include a last element of 1 which means that the last weight effectively operates as a threshold. Create a single ReLU unit and provide the outputs for those examples. Calculate the derivative of the sigmoid with respect to net input for both examples Calculate the derivative of the ReLU with respect to net input for both examplesplease try to simulate the probability of rolling a Die with Sample Space* S={1,2,3,4,5,6} and the probability of each sample point has a 1/6 chance of occurring, i.e., you need to verify that your simulation converges to 1/6 when you select one point of sample space. When X is a random variable for sample point of rolling a Die, Pr(X<=4)=2/3. Please verify this result by simulation. Please let me know how to make an Excel file as stated above.Suppose we use the following KB (where x,y,z are variables and r1, r2, r3, goal are constants) to determine whether a particular robot can score a) Open(x) ∧ HasBall(x) -> CanScore(x) b) Open(x) ∧ CanAssist(y,x) ∧ HasBall(y) -> CanScore(x) c) PathClear(x,y) -> CanAssist(x,y) d) PathClear(x,z) ∧ CanAssist(z,y) -> CanAssist(x,y) e) PathClear(x,goal) -> Open(x) f) PathClear(y,x) -> PathClear(x,y) g) HasBall(r3) h) PathClear(r1, goal) i) PathClear(r2, r1) j) PathClear(r3, r2) k) PathClear(r3, goal) Intuitively, CanScore(x) means x can score on goal. CanAssist(x,y) means there exists some series of passes that can get the ball from x to y. Open(x) means x can shoot on goal directly. And PathClear(x,y) means the path between x and y is clear. Provide a SLD-derivation for the query CanScore(x) in which the answer provided is r1. Provide a SLD-derivation for the query CanScore(x) in which the answer provided is r3. How many "distinct" derivations (i.e., involving different…
- Computer Science A way to avoid overfitting in Deep Neural Networks is to add an additional term R to the loss function L (for example L can be the cross entropy loss) as follows: L(w) + λR(w). (1) You know that one choice for R is the L2 norm, i.e. R(w) = ||w||2 2 . One friend of yours from the School of Maths told you however that there’s no need to use squares (i.e. powers of two) and that you can achieve the same effect by using absolute values, i.e. the L1 norm: R(w) = ||w||1. Would you agree with him? i.e. is the use of the L2 norm equivalent to using the L1 norm for regularization purposes? Justify your answerThe correct statements are: Group of answer choices Google’s pagerank values can be considered as long-term visit rates of pages from a random walker on the Internet graph. Markov models can be used to compute pagerank values. Markov models are stochastic finite state machines. Markov models can be used to generate random music.How make simulation Aquarium Automatic Care (AOC) system (incl. coding) with Arduino. AOC is simulated using Tinkercad based on below conditions? Conditions: 1. Water must be replaced when -Water level (T) < 41 mm -Discard water and fill 30% of Aquarium water volume when high Acidic pH (pH> 9)2. Fish food (pellets): 1 x 4.5 mL/day at 6am in the morning, the machine only contains 100 mL (warning on D-day is over)3. To save electricity, the aquarium lights are on at night (8 hours)
- Suppose we use the following KB (where x, y, z are variables and r1, r2, r3, goal are constants) to determine whether a particular robot can score. (a) Open(x) ∧ HasBall(x) → CanScore(x)(b) Open(x) ∧ CanAssist(y, x) ∧ HasBall(y) → CanScore(x) (c) PathClear(x,y) → CanAsist(x,y)(d) PathClear(x,z) ∧ CanAssist(z,y) → CanAssist(x,y) (e) PathClear(x,goal) → Open(x)(f) PathClear(y,x) → PathClear(x,y) (g) HasBall(r3)(h) PathClear(r1,goal) (i) PathClear(r2,r1) (j) PathClear(r3,r2) (k) PathClear(r3,goal)Suppose we use the following KB (where x, y, z are variables and r1, r2, r3, goal are constants) to determine whether a particular robot can score. (a) Open(x) ∧ HasBall(x) → CanScore(x)(b) Open(x) ∧ CanAssist(y, x) ∧ HasBall(y) → CanScore(x) (c) PathClear(x,y) → CanAsist(x,y)(d) PathClear(x,z) ∧ CanAssist(z,y) → CanAssist(x,y) (e) PathClear(x,goal) → Open(x)(f) PathClear(y,x) → PathClear(x,y) (g) HasBall(r3)(h) PathClear(r1,goal) (i) PathClear(r2,r1) (j) PathClear(r3,r2) (k) PathClear(r3,goal) Intuitively, CanScore(x) means x can score on goal. CanAssist(x, y) means there exists some series of passes that can get the ball from x to y. Open(x) means x can shoot on goal directly. And P athClear(x, y) means the path between x and y is clear. Provide a SLD-derivation for the query CanScore(x) in which the answer provided is r1. Provide a SLD-derivation for the query CanScore(x) in which the answer provided is r3. How many “distinct” derivations (i.e., involving different…MATLAB Project : Fuzzy Control of Air-conditioner • Use M a x -Min O p e r a tio n & S u g e n o’s Sim plifie d FI E • RoomTemperature ~ x, Outside Temperature ~ y Representative Values forx & y : [20 22.5 25 27.5 30 32.5 35] (oC) • Motor Speed forCompressor ~ z : [0 500 1000 1500 2000] (rpm) • Rule 1: IF (x is LOW [1.0 0.8 0.6 0.4 0.2 0 0]) AND (y is HIGH [00 0.2 0.4 0.6 0.8 1.0]) THEN (z is SLOW [0.6 1.0 0.6 0.2 0] ~ 500rpm) • Rule 2: IF (x is HIGH [0 0 0.2 0.4 0.6 0.8 1.0]) AND (y is LOW[1.0 0.8 0.6 0.4 0.2 0 0]) THEN (z is MEDIUM [0 0.5 1.0 0.5 0] ~1000 rpm) • Rule 3: IF (x is HIGH [0 0 0.2 0.4 0.6 0.8 1.0]) AND (y is HIGH[0 0 0.2 0.4 0.6 0.8 1.0]) THEN (z is FAST [0 0.2 0.6 1.0 0.6] ~1500 rpm) • Rule 4: IF (x is LOW [1.0 0.8 0.6 0.4 0.2 0 0]) AND (y is LOW[1.0 0.8 0.6 0.4 0.2 0 0]) THEN (z s STOP [1.0 0.6 0.2 0 0] ~ 0rpm) • Draw 3D plots for control surface z = f(x,y), andInterpolate x, y, z axes with 31, 31, 21 points, resp. • Outputs àM-Script file “your_program.m” and…
- By using neural network algorithm solve the XOR problem. Where X1 and X2 are inputs Y is the output. Learning rate is 0.5. Threshold is 1 if weighted sum >= 0.5 otherwise 0 and weights w1 and w2 = 0.9 Add 17 with learning rate and w1, w2 before start solving the question. X1 X2 Y 0 0 0 0 1 1 1 0 1 1 1 0Correct answer will be upvoted else downvoted. There are n focuses on an endless plane. The I-th point has facilitates (xi,yi) to such an extent that xi>0 and yi>0. The directions are not really integer. In one maneuver you play out the accompanying activities: pick two focuses an and b (a≠b); move point a from (xa,ya) to either (xa+1,ya) or (xa,ya+1); move point b from (xb,yb) to either (xb+1,yb) or (xb,yb+1); eliminate focuses an and b. Notwithstanding, the move must be performed if there exists a line that goes through the new organizes of, another directions of b and (0,0). If not, the move can't be performed and the focuses stay at their unique directions (xa,ya) and (xb,yb), individually. Input The main line contains a solitary integer n (1≤n≤2⋅105) — the number of focuses. The I-th of the following n lines contains four integers ai,bi,ci,di (1≤ai,bi,ci,di≤109). The directions of the I-th point are xi=aibi and yi=cidi. Output :In the primary…Correct answer will be upvoted else Multiple Downvoted. Don't submit random answer. Computer science. How about we consider a line with n shops. The shops are numbered with integers from 1 to n from left to right. The expense of a dinner in the I-th shop is equivalent to man-made intelligence. You should handle q questions of two sorts: 1 x y: for each shop 1≤i≤x set ai=max(ai,y). 2 x y: we should think about an eager man with y cash. He visits the shops from x-th shop to n-th and if he can purchase a feast in the current shop he gets one thing of it. Observe the number of dinners he will buy. The man can purchase a feast in the shop I in the event that he has essentially simulated intelligence cash, and after it his cash diminishes by man-made intelligence. Input The main line contains two integers n, q (1≤n,q≤2⋅105). The subsequent line contains n integers a1,a2,… ,an (1≤ai≤109) — the expenses of the suppers. It is ensured, that a1≥a2≥… ≥an. Every one of the…











