My assignment want me to come up with a code in C++ that would remove any non-alphebet character from a input string using loop. I have not getting the full answer I was expecting and seems like my loop is cutting short. I have attached a screenshot of the code I come up with. example input: -Hello, 1 world$! expected output: Helloworld
My assignment want me to come up with a code in C++ that would remove any non-alphebet character from a input string using loop. I have not getting the full answer I was expecting and seems like my loop is cutting short. I have attached a screenshot of the code I come up with. example input: -Hello, 1 world$! expected output: Helloworld
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter17: Linked Lists
Section: Chapter Questions
Problem 5PE
Related questions
Question
My assignment want me to come up with a code in C++ that would remove any non-alphebet character from a input string using loop. I have not getting the full answer I was expecting and seems like my loop is cutting short. I have attached a screenshot of the code I come up with.
example input: -Hello, 1 world$!
expected output: Helloworld
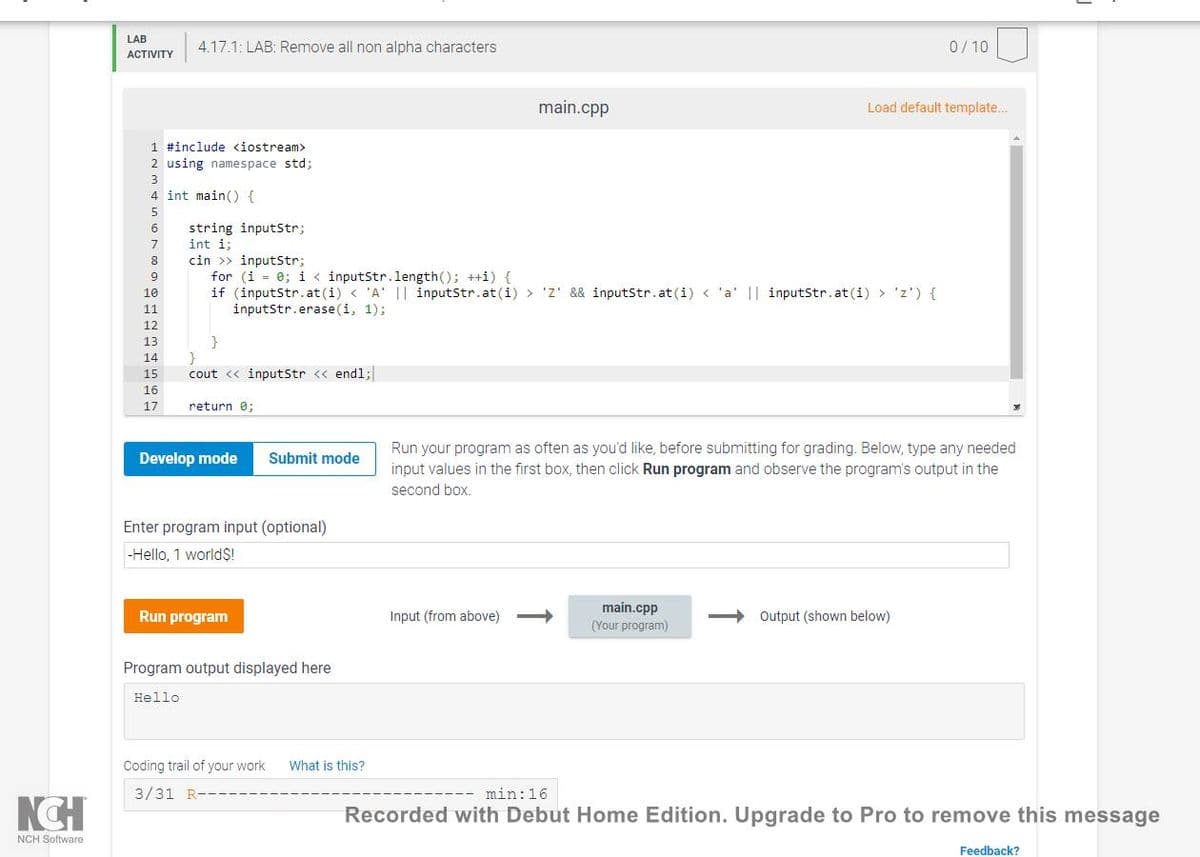
Transcribed Image Text:LAB
4.17.1: LAB: Remove all non alpha characters
0/10
ACTIVITY
main.cpp
Load default template.
1 #include <iostream>
2 using namespace std;
3
4 int main() {
5
string inputStr;
int i;
cin >> inputStr;
for (i = 0; i < inputStr.length(); ++i) {
if (inputStr.at (i) < 'A' || inputStr.at (i) > 'z' && inputStr.at(i) < 'a' || inputstr.at (i) > 'z') {
inputstr.erase(i, 1);
6
7.
8
9.
10
11
12
13
}
cout << inputStr <« endl;
14
15
16
17
return e;
Run your program as often as you'd like, before submitting for grading. Below, type any needed
input values in the first box, then click Run program and observe the program's output in the
Develop mode
Submit mode
second box.
Enter program input (optional)
-Hello, 1 world$!
main.cpp
Run program
Input (from above)
Output (shown below)
(Your program)
Program output displayed here
Hello
Coding trail of your work
What is this?
3/31 R-
min:16
Recorded with Debut Home Edition. Upgrade to Pro to remove this message
NCH Software
Feedback?
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning